
CXO Monthly Roundup, February 2026: Middle East conflict–themed threat activity, Iran-nexus APT Dust Specter, APT28 Operation Neusploit (CVE-2026-21509), APT37 Ruby Jumper air-gap capabilities, analysis of GuLoader and Marco Stealer, and more
Mar 9, 2026
Highlights from the Zscaler ThreatLabz team's February 2026 research.
The CXO Monthly Roundup provides the latest Zscaler ThreatLabz research, alongside insights into other cyber-related subjects that matter to technology executives. This monthly roundup highlights findings from a surge in cybercriminal activity capitalizing on the elevated political climate in the Middle East, Dust Specter (Iran-nexus) activity targeting government officials in Iraq, APT28’s Operation Neusploit leveraging CVE-2026-21509, APT37’s Ruby Jumper campaign adding air-gapped network capabilities, malware analysis of GuLoader and Marco Stealer, and threat updates on Anatsa.
Middle East conflict fuels opportunistic cyber attacks
Zscaler ThreatLabz is diligently monitoring and reporting on the increase in cybercriminal activity occurring in the elevated political climate in the Middle East. This increased malicious activity includes discoveries that are directly tied to the ongoing conflict, alongside other related findings.
The ThreatLabz team identified over 8,000 newly registered domains with keywords tied to the Middle East political situation and conflict-themed events. Most of these domains currently have no content but they may be weaponized or used in threat campaigns in the near future. Analysis of the active domains revealed several trends, including conflict monitoring sites, conflict-themed meme-coins, storefronts selling conflict-related merchandise, general blogs and conflict-themed games, and scam or betting-related Progressive Web Apps (PWAs). The ThreatLabz team will continue monitoring newly registered domains and currently inactive domains for emerging threat campaigns.
The figure below shows a decoy PDF file used in an attack. The Arabic text in the PDF translates to “Iranian missile strikes against US base in Bahrain”.
Figure 1: PDF lure referencing Iranian missile strikes against a US base in Bahrain.
In our blog post, ThreatLabz examines multiple cases, including a conflict-themed lure designed to look like a PDF about missile strikes in Bahrain (mentioned above), a malware chain that uses a conflict-themed lure to deliver the LOTUSLITE backdoor via DLL sideloading, and a fake news blog campaign that redirects users to StealC malware. We also detail fake government and payment phishing sites designed to collect victim data, donation and online storefront scams that route payments to suspicious destinations, and meme-coin promotions consistent with pump-and-dump schemes.
Our blog post also includes best practices and recommendations for keeping organizations safe amid these rising threat campaigns.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
Advanced persistent threat (APT) activity
New Iran-nexus group, Dust Specter, targets government officials in Iraq
In January 2025, ThreatLabz discovered activity by a suspected new Iran-nexus advanced persistent threat (APT) actor group that we named Dust Specter. Dust Specter targets government officials in Iraq with phishing surveys by impersonating Iraq’s Ministry of Foreign Affairs. ThreatLabz has published a technical report where we examine several malware tools used by Dust Specter that were previously undocumented and the attack chains they facilitate.
In this campaign, ThreatLabz identified two separate attack chains. The first attack chain includes SPLITDROP, a .NET-based dropper that drops TWINTASK and TWINTALK to continue the next stage of the attack. The second attack chain uses GHOSTFORM, a .NET-based RAT that consolidates all the functionality of the first attack chain into one binary and uses in-memory PowerShell script execution.
The first attack chain starts with a password-protected archive that drops a small set of components onto the victim’s machine and then blends in by launching legitimate applications (VLC and WingetUI). The malware is split into two roles: one component executes threat actor commands on the endpoint, while a second component handles command-and-control (C2) communications. The two coordinate through local files, one for incoming tasking and one for output, allowing the operator to issue commands, receive results, and move files while maintaining persistence through standard Windows startup mechanisms. The figure below shows the attack flow.

Figure 2: The first attack chain that delivers SPLITDROP, TWINTASK, and TWINTALK.
The second attack chain delivers the same core capabilities as the first attack chain, but with less complexity by streamlining the operation into a single remote access trojan (RAT) that performs both C2 and its own execution without relying on multiple dropped modules or file-based coordination. The second attack uses a Google Form (shown below) lure for social engineering, adds execution delays, and runs threat actor-provided commands in-memory.

Figure 3: Google Form displayed by GHOSTFORM to the victim as a social engineering lure.
The figure below shows the attack flow.
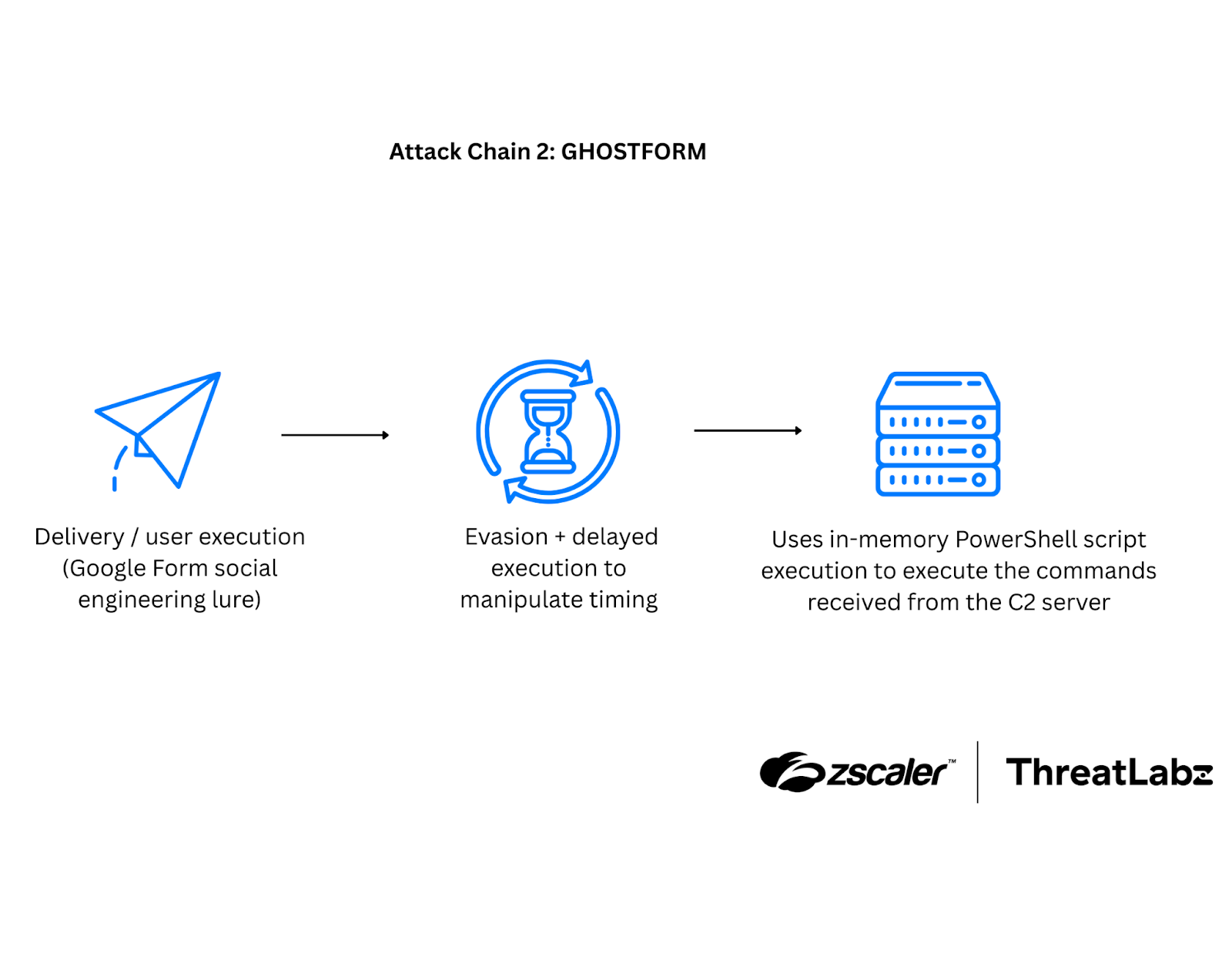
Figure 4: The second attack chain that delivers GHOSTFORM.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, SSL Inspection), Deception
APT28 Leverages CVE-2026-21509 in Operation Neusploit
In January 2026, ThreatLabz identified a new campaign in-the-wild, tracked as Operation Neusploit, targeting countries in the Central and Eastern European region. In our technical analysis, we cover how the threat actor leveraged specially crafted Microsoft RTF files to exploit CVE-2026-21509 and deliver malicious backdoors in a multi-stage infection chain, including the weaponized RTF exploit, staged payload delivery, and the execution chain.
The campaign has two main infection variants. Variant 1 drops MiniDoor, a malicious Outlook VBA project designed to steal emails by forwarding existing and newly received messages to threat actor-controlled email accounts, while also modifying registry settings and ensuring the payload loads on Outlook startup. Variant 2 deploys PixyNetLoader, which establishes persistence via COM object hijacking and a scheduled task, then uses a malicious DLL to extract shellcode hidden inside a PNG file (LSB steganography). That shellcode hosts the .NET CLR in memory to execute a Covenant Grunt implant. The figure below shows the attack flow.
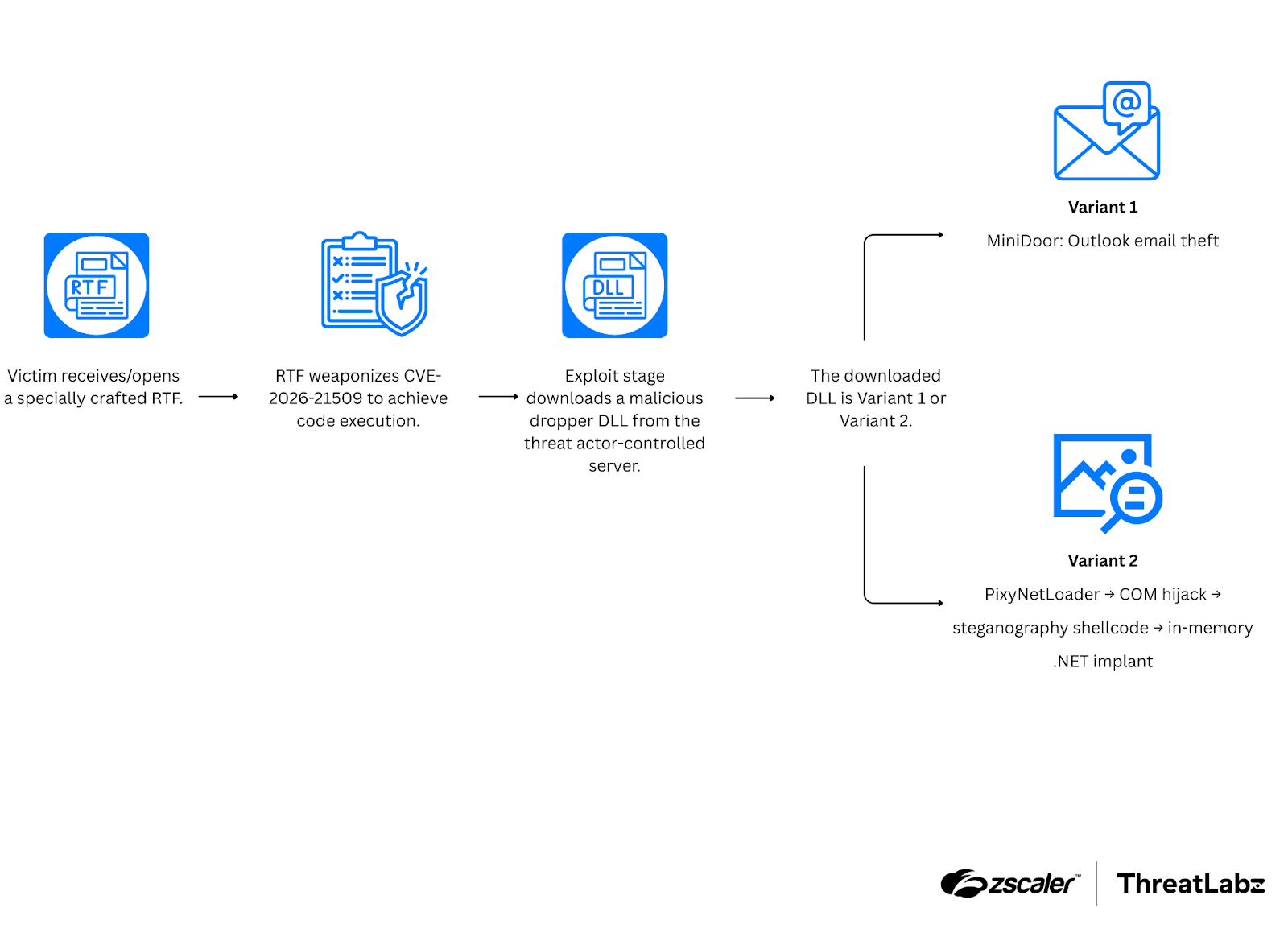
Figure 5: Attack flow for Operation Neusploit.
Operation Neusploit relies on the threat actor’s infrastructure to serve dropper DLLs only under specific conditions, including geographic targeting and expected HTTP User-Agent values. In Variant 1, MiniDoor exfiltrates by forwarding stolen emails to hardcoded recipient addresses. In Variant 2, the Covenant Grunt communicates over HTTPS and abuses the Filen API as a C2 bridge, using the legitimate web service to relay tasks and responses between the implant and the operator’s Covenant server.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
APT37 Adds New Capabilities for Air-Gapped Networks
ThreatLabz published a technical analysis of APT37’s new air-gap capability. APT37 (also known as ScarCruft, Ruby Sleet, and Velvet Chollima) is a DPRK-backed threat group that has been observed since 2012. During analysis, ThreatLabz identified several previously undocumented tools, including RESTLEAF, SNAKEDROPPER, VIRUSTASK, THUMBSBD, and FOOTWINE.
Tracked as Ruby Jumper, this campaign is a multi-stage chain that begins when a victim opens a malicious Windows shortcut (LNK), which launches PowerShell to extract and run embedded shellcode in-memory. That initial activity deploys RESTLEAF to retrieve additional payloads (including via abused cloud services such as Zoho WorkDrive), followed by SNAKEDROPPER, which installs a disguised Ruby runtime and sets persistence so later-stage components run automatically. The campaign then uses THUMBSBD and VIRUSTASK to weaponize removable media, enabling malware propagation and a bidirectional command/data relay that can bridge air-gapped systems.
The Ruby Jumper campaign attack flow is shown in the figure below.
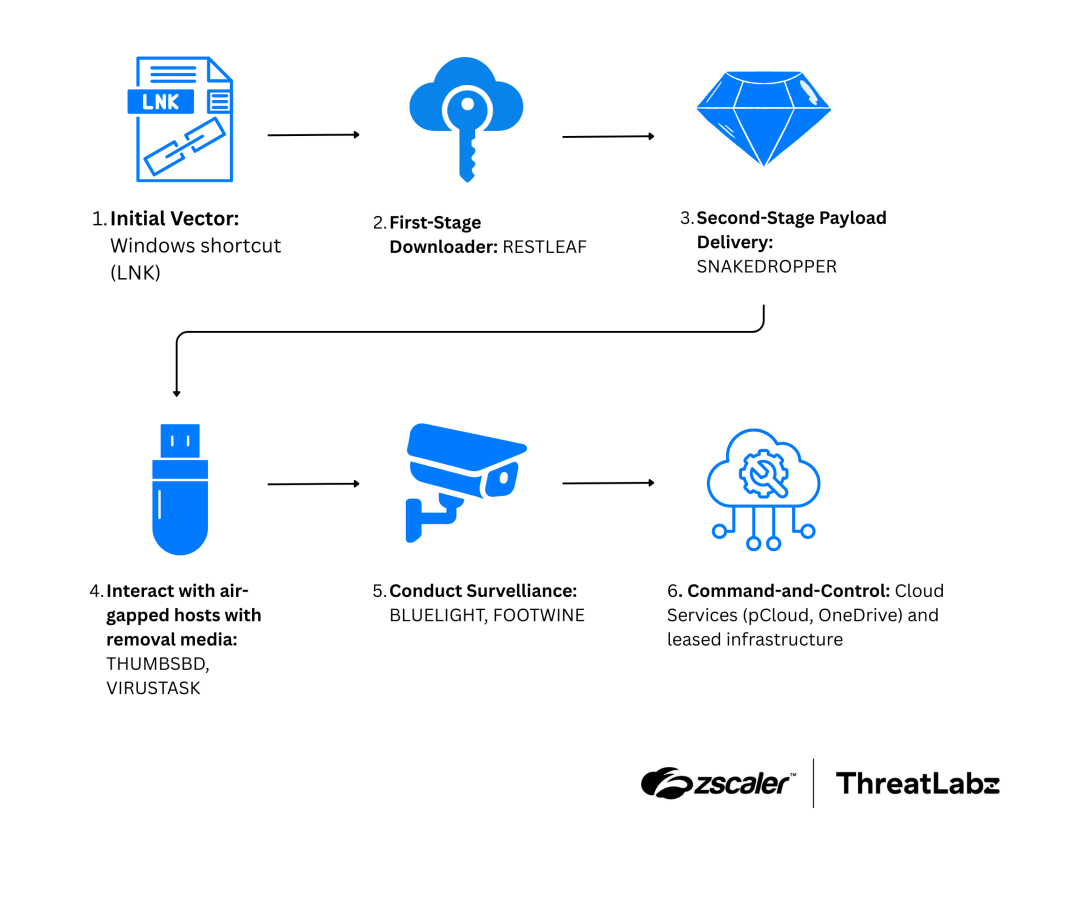
Figure 6: APT37 Ruby Jumper campaign attack flow.
Ultimately, Ruby Jumper delivers full-featured backdoors such as FOOTWINE and BLUELIGHT to support surveillance and remote control, including data theft and monitoring capabilities like keylogging and audio/video capture. FOOTWINE uses a custom XOR-based key exchange protocol to establish an encrypted communication channel with the C2 server.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
Malware Activity
GuLoader
ThreatLabz published technical analysis of GuLoader (also known as CloudEye) an obfuscated malware family that was first observed in December 2019.
GuLoader is a downloader for RATs and information stealers, which are delivered to compromised systems. To hinder analysis and signature-based detection, GuLoader relies on polymorphic code for dynamic constant/string construction and exception-driven control-flow redirection. This technique makes the malware's execution flow extremely difficult for automated analysis tools to trace. The table below outlines the exception types that GuLoader actively handles across different versions.
Table 1: Exception types handled by GuLoader across different versions.
GuLoader’s network communication is its payload retrieval infrastructure. GuLoader stores its download URLs/domains as XOR-encrypted strings, decrypts them during execution, and then fetches an encrypted next-stage payload, often from legitimate cloud hosting platforms like Google Drive or OneDrive to blend in and bypass reputation-based controls. After download, it uses an embedded XOR key buffer (a large binary blob) to decrypt the payload locally before handing off execution.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, SSL Inspection), Deception
Marco Stealer
ThreatLabz published a technical analysis of Marco Stealer, an information stealer that targets sensitive data and files stored in the victim’s system.
Marco Stealer’s capabilities include profiling infected systems, stealing browser credentials and other browser data (including decrypting Chromium-protected stores), harvesting cryptocurrency wallet extension data and sensitive local/cloud-synced files from services like Dropbox and Google Drive, capturing clipboard content and screenshots, and using anti-analysis techniques plus named-pipe communication between components. The attack chain below shows how a campaign may deliver Marco Stealer to a victim’s system.
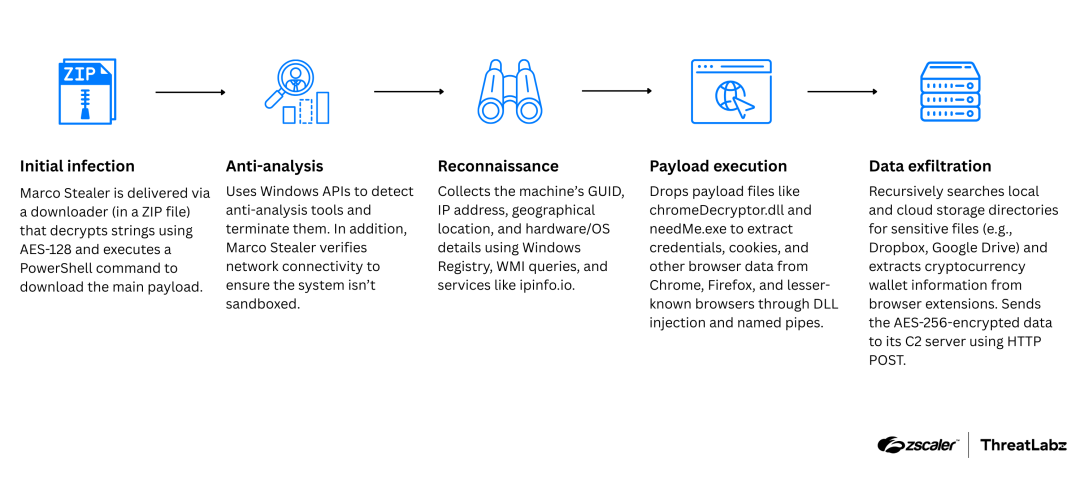
Figure 7: Attack chain depicting the execution flow in campaigns delivering Marco Stealer.
Marco Stealer communicates with its C2 infrastructure over HTTP, encrypting stolen data with AES-256 (CBC) prior to exfiltration. It derives a repeatable encryption key by hashing a hardcoded value (SHA-256) and using Windows cryptographic functions to generate the AES key material, then transmits the encrypted payload via HTTP POST requests to a predefined endpoint. Exfiltrated data is packaged with victim-identifying fields (such as a client ID, hardware ID, and IP address) and sent in separate posts as collection proceeds, helping the operator track infections while keeping the contents protected in transit.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, SSL Inspection), Deception
Threat Updates
Recommended
