Blog Zscaler
Ricevi gli ultimi aggiornamenti dal blog di Zscaler nella tua casella di posta
Zero Trust Purdue Model: How to Modernize OT Security
For decades, the Purdue Model has been the foundation of operational technology (OT) architecture. It provides a clear structure for how factory systems are organized from sensors and programmable logic controllers (PLCs) to enterprise applications.
In the past IT and OT in factories were airgapped. But in recent years the air gap has largely disappeared. Even if OT systems do not directly connect to the cloud, there are plenty of systems on the factory floor that are connected to enterprise IT or cloud for physical security, production analytics, industrial printing, and other functions that support a factory. Connectivity has become essential to modern manufacturing.
What no longer works are the security assumptions that grew around it. Many of those assumptions were built when access to OT was rarely available or granted. That world has disappeared, leaving a growing gap between how factories operate and how they are protected.
The Purdue Model Still Matters
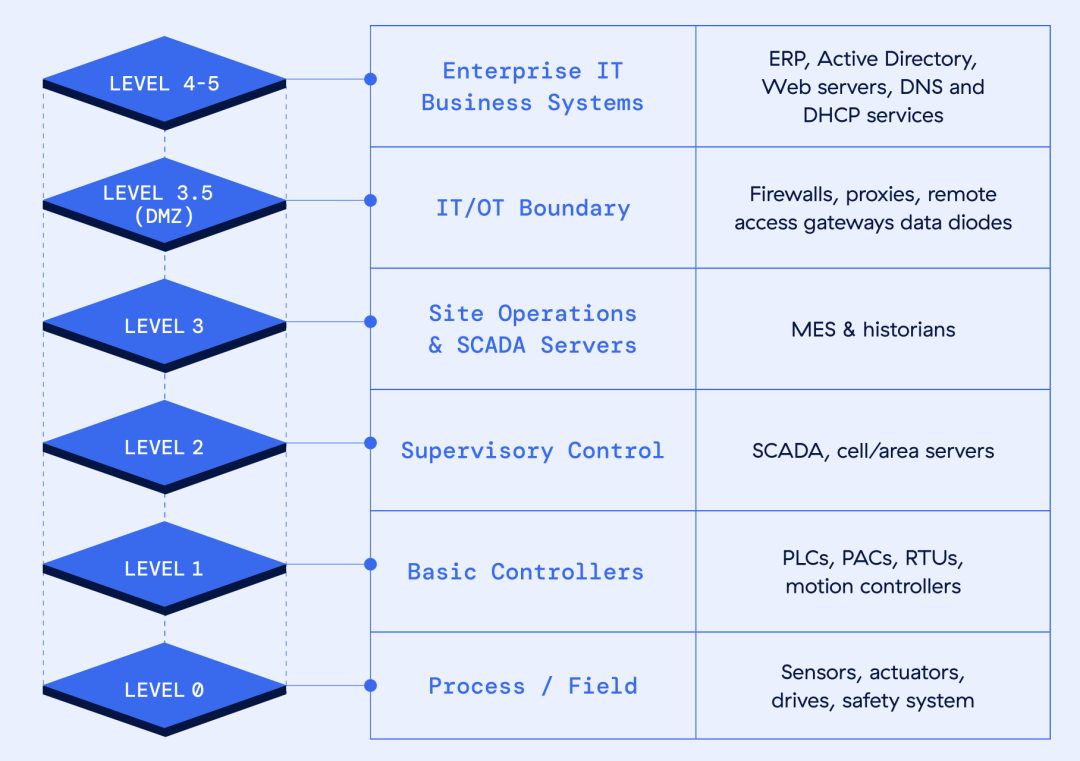
Despite predictions that the Purdue Model would eventually become obsolete, it remains deeply relevant for industrial organizations. It provides a shared framework for how OT teams design and operate manufacturing environments, organizing systems into layers that range from physical processes at the plant floor to enterprise applications in corporate networks.
It also works because it mirrors how industrial systems actually function. Sensors communicate with controllers, controllers interact with supervisory systems, and operational systems exchange data with enterprise platforms. The layered model provides clarity and operational consistency. A simple and effective structure looks something like this:
- Level 0–1: Physical processes and sensors
- Level 2: Control systems such as PLCs and HMIs
- Level 3: Operations management
- Level 4–5: Enterprise IT systems
Why Traditional OT Security Controls Fall Short
Many factories rely on familiar tools such as firewalls, VLAN segmentation, and network access control to secure their environments. These technologies still play a role, but they were never designed for the level of connectivity seen in modern manufacturing.
Firewalls
Firewalls, for example, are primarily designed to control north–south traffic communication entering or leaving the plant network. While they remain effective at that boundary, they provide limited visibility into the east–west communication that occurs inside the factory itself. Many attacks today spread laterally between systems once an attacker gains a foothold, which is exactly where traditional firewall architectures struggle.
VLAN Segmentation
VLAN segmentation attempts to address this challenge, but in many factories VLANs contain large numbers of devices with very different risk profiles. A single VLAN may include PLCs, HMIs, SCADA systems, engineering workstations, and even contractor laptops. If malware infects one device, it can often move laterally across the entire segment with little resistance.
NAC Solutions
Network access control (NAC) solutions face their own challenges in OT environments. Many industrial systems are decades old and cannot support modern agents or posture checks. In practice, organizations often fall back to maintaining allow lists based on MAC addresses, which are complex to manage and provide limited protection against sophisticated attackers. These approaches were designed for factories that were mostly isolated. Today’s connected industrial environments require a different security model.
AI Presents Additional Challenges
Industrial organizations are also facing a new reality: AI is accelerating cyberattacks.
Tasks that once required weeks of reconnaissance can now be automated:
- Faster vulnerability discovery
- Rapid network enumeration
- Automated lateral movement
- Faster data exfiltration
What once took attackers months can now occur in hours. Factories need security models that assume compromise and minimize the blast radius of an attack. Check out this report by Anthropic on an AI-orchestrated cyber espionage campaign.
Bringing Zero Trust to the Purdue Model
Zero Trust does not replace the Purdue Model. Instead, it modernizes how security is applied across the architecture.
The core idea behind Zero Trust is simple: never assume trust based on network location. Every connection must be verified, access must be limited to what is strictly necessary, and systems should never expose more of the network than required.
Applying these principles to industrial environments results in what many organizations now describe as the Zero Trust Purdue Model. This approach preserves the layered structure of Purdue while introducing controls that prevent lateral movement, restrict access to specific systems, and remove unnecessary network exposure.
How Zscaler Enables the Zero Trust Purdue Model
Zscaler helps enable this architecture through its Zero Trust Branch, typically deployed around Level 3 or 3.5 of the Purdue Model, where operational systems connect to enterprise IT and external services.
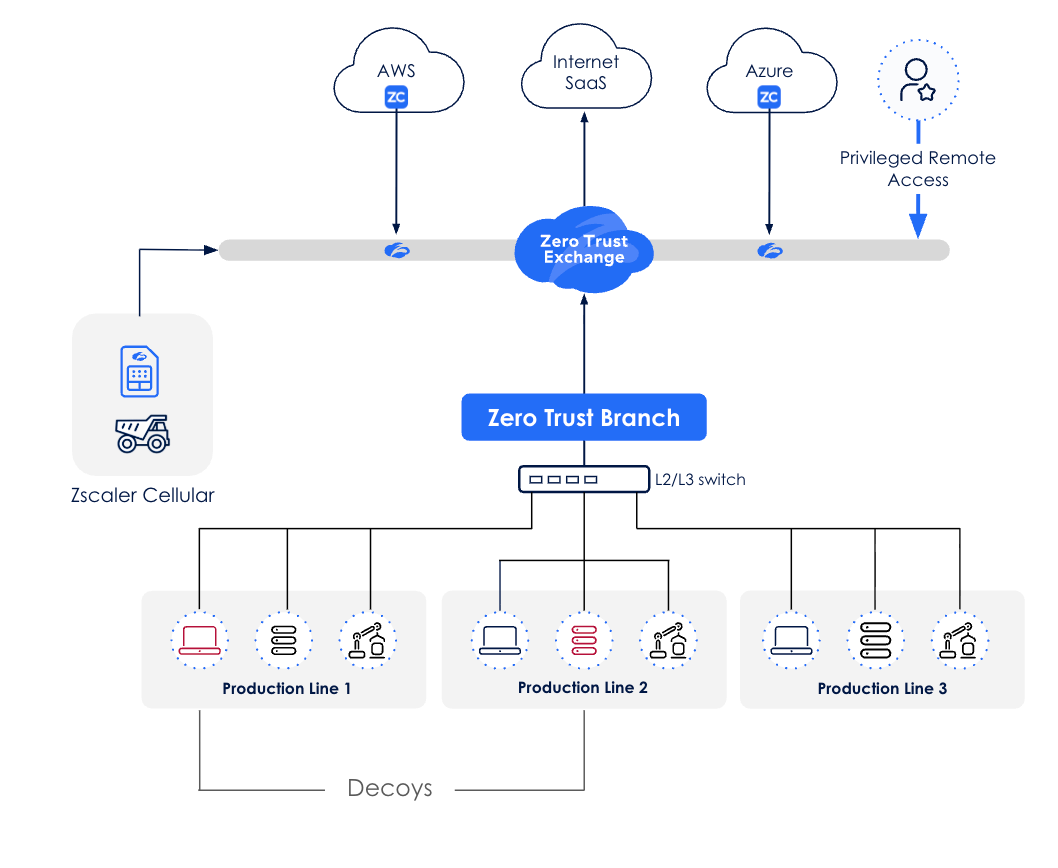
One of the most important capabilities is segmentation that operates at the level of individual assets rather than networks. Instead of relying on VLANs or firewall zones, organizations can control communication between specific devices. This prevents malware from spreading laterally if a system becomes compromised and significantly reduces the potential blast radius of an attack.
Zscaler also replaces traditional VPN-based remote access with a browser-based privileged access model. Contractors can connect directly to the machines they are authorized to maintain without exposing the broader factory network. This eliminates one of the most common entry points attackers exploit in industrial environments.
As factories increasingly connect to cloud platforms and enterprise systems, the architecture also secures outbound communications, allowing organizations to apply consistent security policies across both IT and OT traffic.
Finally, Zscaler incorporates deception technologies that deploy decoy systems inside the environment. These decoys mimic real OT assets, and any interaction with them immediately generates high-confidence alerts that allow security teams to detect attackers early in the attack lifecycle.
A reference architecture for Zero Trust Purdue Model is available here.
The Future of Factory Security
Factories will continue to become more connected, automated, and data-driven. The Purdue Model remains a useful architectural framework for organizing these environments, but securing them requires a modern approach.
By combining the structure of the Purdue Model with Zero Trust principles, organizations can protect their industrial systems while enabling the connectivity and analytics that modern manufacturing demands.
Questo post è stato utile?
Esclusione di responsabilità: questo articolo del blog è stato creato da Zscaler esclusivamente a scopo informativo ed è fornito "così com'è", senza alcuna garanzia circa l'accuratezza, la completezza o l'affidabilità dei contenuti. Zscaler declina ogni responsabilità per eventuali errori o omissioni, così come per le eventuali azioni intraprese sulla base delle informazioni fornite. Eventuali link a siti web o risorse di terze parti sono offerti unicamente per praticità, e Zscaler non è responsabile del relativo contenuto, né delle pratiche adottate. Tutti i contenuti sono soggetti a modifiche senza preavviso. Accedendo a questo blog, l'utente accetta le presenti condizioni e riconosce di essere l'unico responsabile della verifica e dell'uso delle informazioni secondo quanto appropriato per rispondere alle proprie esigenze.
Ricevi gli ultimi aggiornamenti dal blog di Zscaler nella tua casella di posta
Inviando il modulo, si accetta la nostra Informativa sulla privacy.




