Zscalerのブログ
Zscalerの最新ブログ情報を受信
Zero trust illustrated: Secure cloud migration
Editor’s note: This is the third in a three-part series on popular use cases for zero trust transformations
As applications are migrated to the cloud or built as cloud-native, there is protection for how their workloads communicate with other workloads and the internet, and how they are entitled and configured. Providing strong posture control, secure workload configuration, and safe workload communications is an important aspect of a holistic ZTA.
Posture control
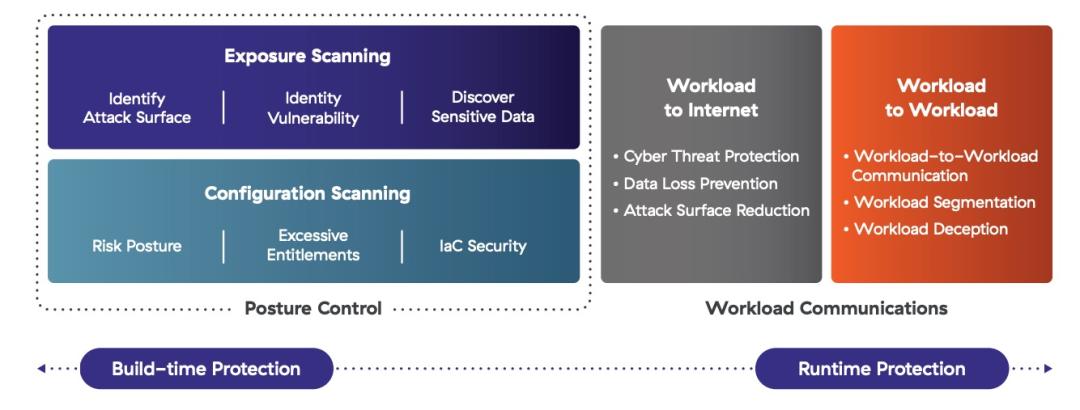
Posture control for cloud applications falls into two categories: exposure scanning and configuration scanning. Exposure scanning, leveraged through API integration with common IaaS and SaaS vendors, can identify an attack surface, find identity vulnerabilities, and discover sensitive data.
Configuration scanning uses similar API integration to identify the risk posture of a cloud application, excessive entitlements, and the security of infrastructure-as-code scripts. This capability is commonly called CNAPP (Cloud Native Application Protection Platform).
CNAPP is agentless and uses ML to correlate hidden risks caused by misconfigurations, threats, and vulnerabilities across the cloud stack. Security, development, and DevOps teams should prioritize and remediate risks in cloud-native and VM-based apps as early as possible in the software development life cycle (SDLC), both at build-time and runtime. CNAPP gives professionals the visibility they need to “shift left” security practices during the SDLC, and fix small problems before they become costly disasters.
Workload communications
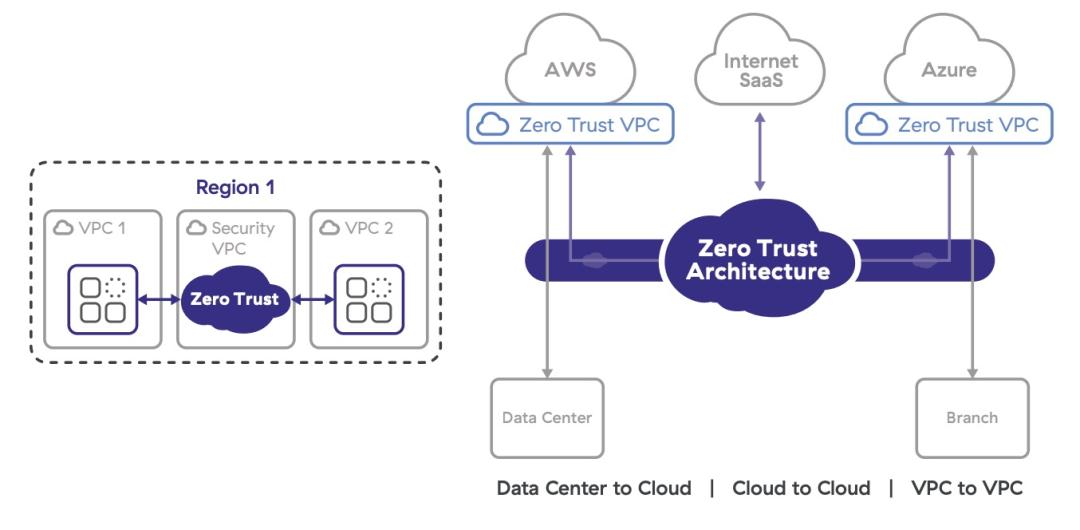
Previous articles discussed private application access and cyberthreat and data protection from users accessing internal and external applications. Secure workload communication extends these same protections to workloads talking to other workloads or to the internet by using zero trust cloud connectivity. Customer-defined policies specify which workload can communicate with another regardless of region, cloud provider, or network path, in hybrid and multicloud environments alike.
Zero trust architecture(ZTA) provides a scalable, secure solution that allows cloud applications to access any internet or SaaS destination, such as third-party APIs and software updates. It inspects all transactions while applying advanced threat protection and data loss prevention controls. Workloads in one public cloud can securely communicate with any cloud, public or private, with support for communications across VPCs, zones, and regions on the same cloud. ZTA eliminates lateral movement, internet attack surface, VPNs, and the complexities of bespoke cloud routing.
In today’s business environment, securing workloads is an important part of ZTA. Often zero trust proponents only focus on how users are identified and access to resources is earned. While these things are important, it is imperative organizations consider the many transactions in their environment that do not involve users at all. For a business to achieve robust zero trust protection, the security of apps and workloads must be assured as well.
What to read next
From code to cloud, the case for cloud-native app protection
このブログは役に立ちましたか?
免責事項:このブログは、Zscalerが情報提供のみを目的として作成したものであり、「現状のまま」提供されています。記載された内容の正確性、完全性、信頼性については一切保証されません。Zscalerは、ブログ内の情報の誤りや欠如、またはその情報に基づいて行われるいかなる行為に関して一切の責任を負いません。また、ブログ内でリンクされているサードパーティーのWebサイトおよびリソースは、利便性のみを目的として提供されており、その内容や運用についても一切の責任を負いません。すべての内容は予告なく変更される場合があります。このブログにアクセスすることで、これらの条件に同意し、情報の確認および使用は自己責任で行うことを理解したものとみなされます。



