Zscalerのブログ
Zscalerの最新ブログ情報を受信
Stop “Patient Zero” Threats: Why Traditional Sandboxes Fail and How Zscaler Advanced Cloud Sandbox Changes the Outcome
Security teams don’t lose sleep over known malware. They worry about the first time a brand new threat shows up with no signature, no IOC, and an easy path to execution by the attacker.
That’s the patient zero moment: the first encounter with an unknown file.
In many organizations, risk comes from a common pattern: deliver then detonate. A file reaches the inbox or endpoint, endpoint tools classify it as unknown (or low prevalence), and then submit it for sandbox analysis while everyone waits for a verdict. Even if the file hasn’t been executed yet, it’s now present—and one mistaken click, share, or re-download can turn “unknown” into an incident.
The real enemy: The verdict gap
In many environments, sandboxing is triggered only after the file has already reached the endpoint, often because the Endpoint security solution flags it as unknown or low prevalence and submits it for detonation.
That creates a timing problem:
- A user downloads a file to the device
- The file lands on the endpoint (now one click away from execution)
- EDR identifies it as unknown and submits it to a sandbox
- The sandbox analyzes the file
- A verdict returns (benign/suspicious/malicious)
That delay between “file on the endpoint” and “sandbox verdict” is the verdict gap. With ~450,000 new malicious programs per day (AV-TEST.org), the gap isn’t occasional; rather, it becomes a repeating exposure window. Patient zero threats live in that gap because the attacker only needs one successful execution to trigger credential theft, persistence, or ransomware staging.
Endpoint detection and response is essential, and endpoint sandboxing is useful, but both operate after files reach the device. The goal is to reduce how often unknown files get that far in the first place.
Inline sandboxing helps reduce how often that happens by stopping unknown threats earlier in the attack chain, lowering the number of endpoint alerts and investigation workload.
Other common sandboxing pitfalls
The verdict gap is not the only problem with traditional sandboxing approaches. Many sandboxes, especially basic or standard versions, still leave coverage and timing gaps that attackers exploit.
These limitations include:
- Limited file-type coverage (primarily executables), while modern campaigns use archives, scripts, Office/PDF files, installers, and mixed-content packages
- Restrictive file-size limits that exclude realistic payloads and multi-stage droppers
- Blind spots on large payloads (50 MB+) increasingly used as installers, disk images, archives, and bundled droppers
Many organizations start with standard sandbox protection to inspect suspicious files. This provides valuable visibility, but as attackers evolve, security teams often find they need broader inspection and faster decisions to reduce patient zero risk.
What patient zero defense actually means
Patient zero defense isn’t a promise that malware will never appear. It’s a security posture:
- Unknown files don’t get a free pass
- Suspicious content is stopped upstream
- A verdict is reached quickly
- Only then does content reach the device
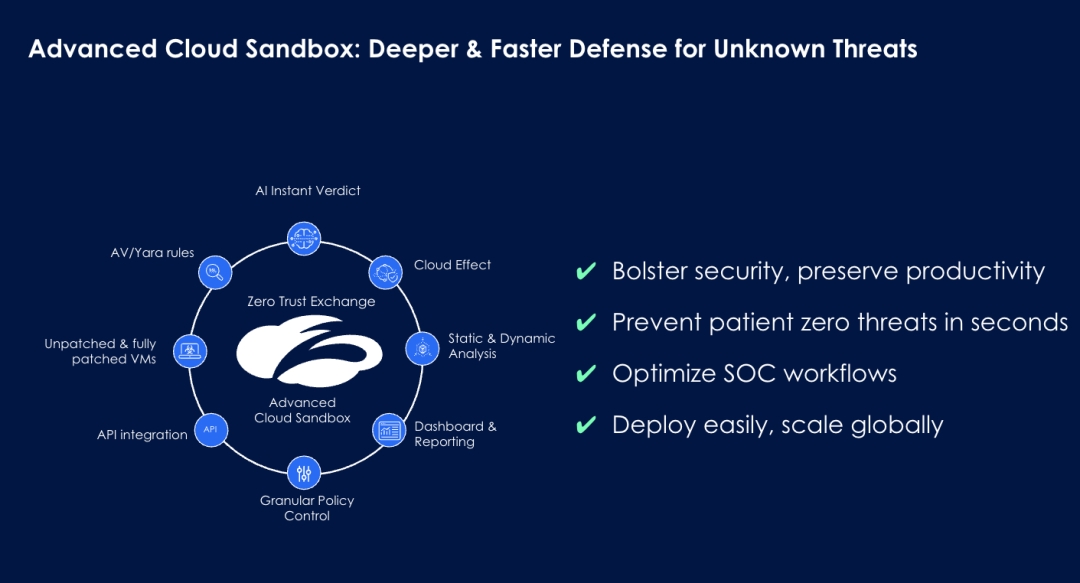
This is the approach behind Zscaler Advanced Cloud Sandbox, delivered inline through the Zscaler Zero Trust Exchange.
Zscaler Advanced Cloud Sandbox
Advanced Cloud Sandbox helps close the verdict gap with capabilities designed for modern attack techniques. It’s delivered through the Zscaler Zero Trust Exchange, which processes 500 B+ transactions per day, and Zscaler achieved 100% effectiveness in the CyberRatings SSE Threat Protection Test for two consecutive years (AAA rating).
Unlimited inline prevention: Hold it at the door
Instead of “deliver then detonate,” Advanced Cloud Sandbox can quarantine unknown files upstream so they never land on the endpoint while analysis occurs.
AI Instant Verdict: Stop unknown file-based threats in seconds
Block unknowns too aggressively and productivity suffers. Allow them through and you risk incident response later.
AI Instant Verdict delivers a high-confidence verdict in seconds, enabling organizations to stop unknown threats without weakening policy or slowing down users.
Patched VM analysis: Expose evasive malware
Patched VM environments help uncover threats designed to evade or “sleep through” standard sandbox environments.
API-driven analysis: Extend protection to more workflows
API-driven out-of-band analysis enables detection of hidden threats in third-party files, acquired environments, and other workflows outside traditional traffic inspection.
Zero Trust Browser integration: Maintain productivity during analysis
Users can safely interact with files during sandbox inspection through browser isolation.
If malicious behavior is detected, files can be flattened into PDFs or disarmed to remove harmful content.
Three ways to consume Zscaler Advanced Cloud Sandbox
- Inline deployment: Stop patient zero attacks before they land. Inspect files in line and quarantine unknown threats upstream while a verdict is reached. Best for stopping ransomware and other malware before it ever reaches the endpoint.
- Offline analysis (Endpoint Sandbox): Neutralize threats introduced offline. Analyze files introduced outside normal network paths (USB, Bluetooth) before execution to prevent offline “patient zero” attacks.
- API/SOC workflows: Inspect third-party and business-critical files. Submit files out-of-band for rapid inspection from third parties, or M&A workflows—and equip SOC teams with actionable reports and MITRE ATT&CK–mapped insights to speed triage and response.
Why stepping up to Advanced Cloud Sandbox changes the outcome
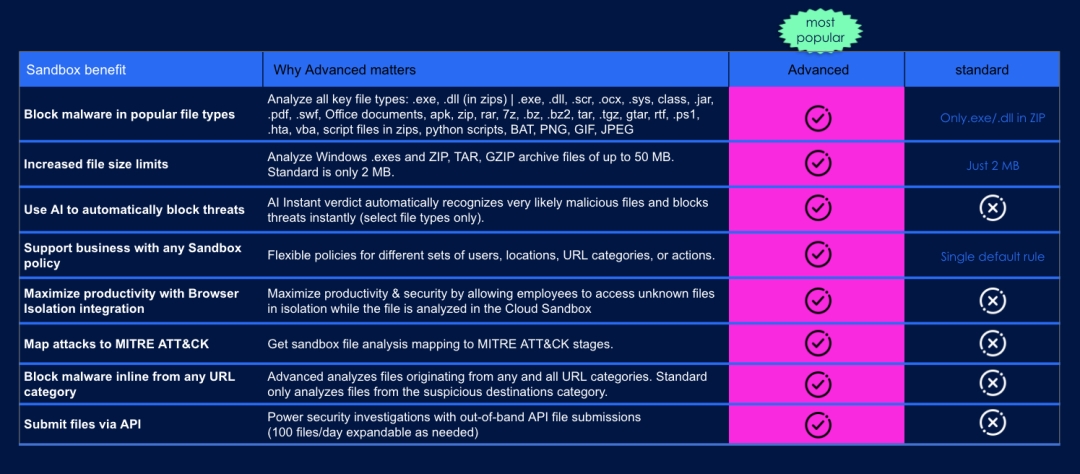
Zscaler provides standard sandbox protection as part of the platform, while Advanced Cloud Sandbox extends that protection with deeper inspection, broader coverage, and faster decisions as threats evolve. This allows organizations to start with foundational protection and step up their defenses as threat complexity grows.
At a glance, here’s what’s included in a standard sandbox vs. what you gain with Advanced Cloud Sandbox:
Budget reality: What you’re really buying
When evaluating sandbox protection, it helps to step back and consider the bigger picture. Organizations don’t invest in sandboxing to generate detonation reports—they invest in risk reduction.
A single ransomware incident can quickly lead to downtime, incident response costs, recovery efforts, and reputational damage. Those losses often exceed the incremental cost of upgrading traditional sandboxing or adding Advanced Cloud Sandbox prevention alongside endpoint protection.
Advanced Cloud Sandbox helps reduce those risks by delivering:
- Upstream quarantine of unknown files
- Fast AI-driven verdicts
- Coverage aligned with modern attack techniques
- Operational efficiency through API-driven workflows
A simple evaluation checklist
When evaluating sandbox protection for unknown files, consider the following:
- Can unknown files be quarantined upstream until a verdict is reached?
- How quickly can the sandbox deliver a high-confidence decision?
- Does the sandbox support the file types and sizes attackers commonly use?
- Does the sandbox help simplify SOC workflows by reducing alerts and investigation effort?
Next step
Patient zero attacks thrive in the verdict gap—when unknown files can reach endpoints before a decision is made.
If your organization currently relies on standard or traditional sandbox or an endpoint protection, this may be a good time to evaluate whether your coverage matches today’s threat landscape.
Talk to your Zscaler accounts team to see how Advanced Cloud Sandbox can help stop unknown file-based threats in seconds without compromising productivity.
このブログは役に立ちましたか?
免責事項:このブログは、Zscalerが情報提供のみを目的として作成したものであり、「現状のまま」提供されています。記載された内容の正確性、完全性、信頼性については一切保証されません。Zscalerは、ブログ内の情報の誤りや欠如、またはその情報に基づいて行われるいかなる行為に関して一切の責任を負いません。また、ブログ内でリンクされているサードパーティーのWebサイトおよびリソースは、利便性のみを目的として提供されており、その内容や運用についても一切の責任を負いません。すべての内容は予告なく変更される場合があります。このブログにアクセスすることで、これらの条件に同意し、情報の確認および使用は自己責任で行うことを理解したものとみなされます。



