Zscalerのブログ
Zscalerの最新ブログ情報を受信
Secure SAP S/4HANA Migration: Top 4 Challenges Companies Must Address
Mainstream support for legacy SAP ERP platforms ends on Dec. 31, 2027. After that, SAP ECC 6.0 (and older ERP versions) will face increasing risk without routine patches and updates along with increased maintenance expense via “Extended Support: December 31, 2030 (available for SAP ECC EHP 6-8 at additional cost)”. This isn’t a “side IT project”—it impacts core ECC functions that support the business, such as Financial Accounting and Controlling (FICO), Sales Distribution (SD), Materials Management (MM), Human Capital Management (HCM), Production Planning (PP), Plant Maintenance (PM), and Quality Management (QM). Leading companies won’t take the risk; they have already embarked (or will soon embark) on the journey to modernize their SAP ERP through RISE with SAP program.
Complex Hybrid Infrastructure of SAP S/4HANA
S/4HANA migrations typically span multiple years. During this period, SAP ECC and SAP BW often remain on‑premises while S/4HANA is implemented in parallel. All systems must interoperate—sharing data and business processes across on‑prem and cloud environments. At the same time, connectivity requirements explode. S/4HANA connects to the internet and SaaS, external business partners, printers in the factories and manufacturing shop‑floors. The result is a highly interconnected, complex hybrid infrastructure.
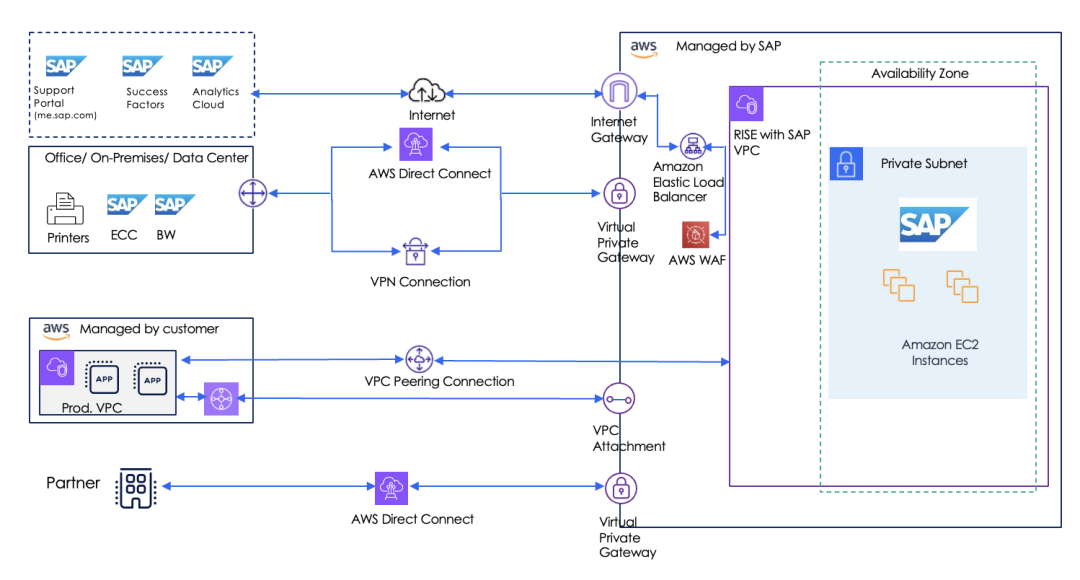
Figure1: Reference architecture featuring hybrid infrastructure of SAP S/4HANA
Top 4 Security Challenges in SAP S/4HANA migration
Extensive connectivity to the internet, SaaS platforms, and third-party partners significantly expands the attack surface, creating more entry points and accelerating the potential blast radius in the event of a compromise. Legacy security architecture that relies on firewalls and VPNs struggle to scale in a hybrid environment, resulting in policy sprawl, and inconsistent controls. Meanwhile, insecure data migration across cloud and on-premises environments increases risk of sensitive data exfiltration.
As a result, many companies face significant challenges because they overlook the need to modernize their security architecture alongside their SAP ERP transformation. Let’s walk through the top four key challenges they encounter.
Challenge #1: Provide secure access to partners without exposing S/4HANA
Providing SAP S/4HANA access to external business partners (such as suppliers, vendors, customers, and logistics providers) is important because it shifts B2B interactions from manual, siloed processes to real-time, collaborative, and automated digital workflows. This improves supply chain visibility, speeds up transaction processing, and increases operational efficiency.
Many companies directly manage this connectivity with business partners. The access to SAP S/4HANA is provided over dedicated private networks, with firewalls deployed at both ends. However, this approach increases the risk of exposing S/4HANA if either firewall is compromised. Companies need secure partner connectivity without placing S/4HANA behind publicly reachable IPs, partner-routed networks, or flat trust zones—and without creating a new maze of firewall exceptions.
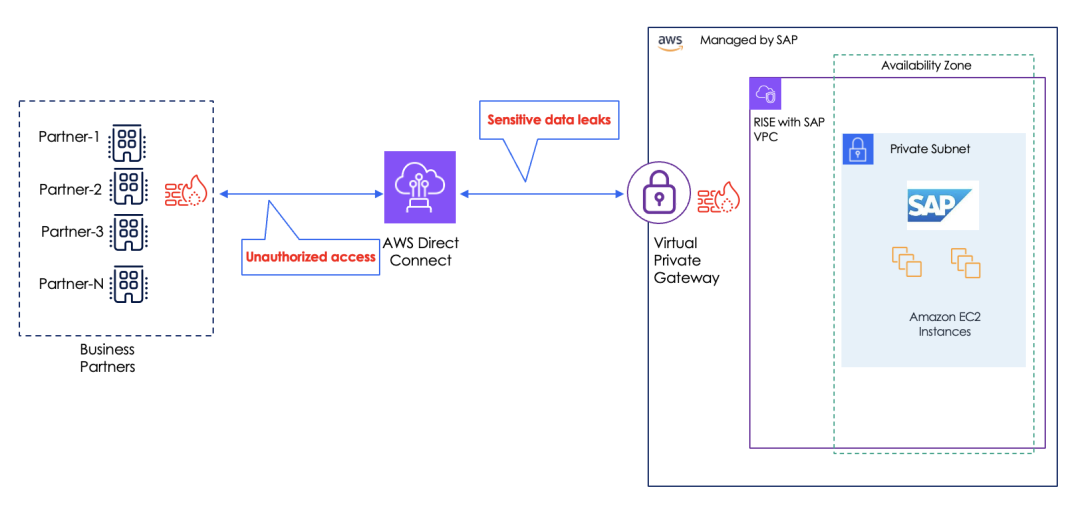
Figure 2: Insecure connectivity between business partners and SAP S/4HANA
Challenge #2: Protecting data exfiltration during SAP S/4HANA migration
An SAP S/4HANA migration introduces high-volume movement of sensitive data (financials, HR data, customer records, and IP) across on-premises and cloud environments. Security controls differ across these environments, and encryption can reduce visibility if inspection isn’t designed to operate at scale. This is when the risk of data exfiltration spikes, especially due to compromised accounts, rogue admin tools, misrouted transfers, or unmanaged endpoints that can quietly siphon sensitive data without detection. Companies require consistent, inline controls across the entire migration flow.
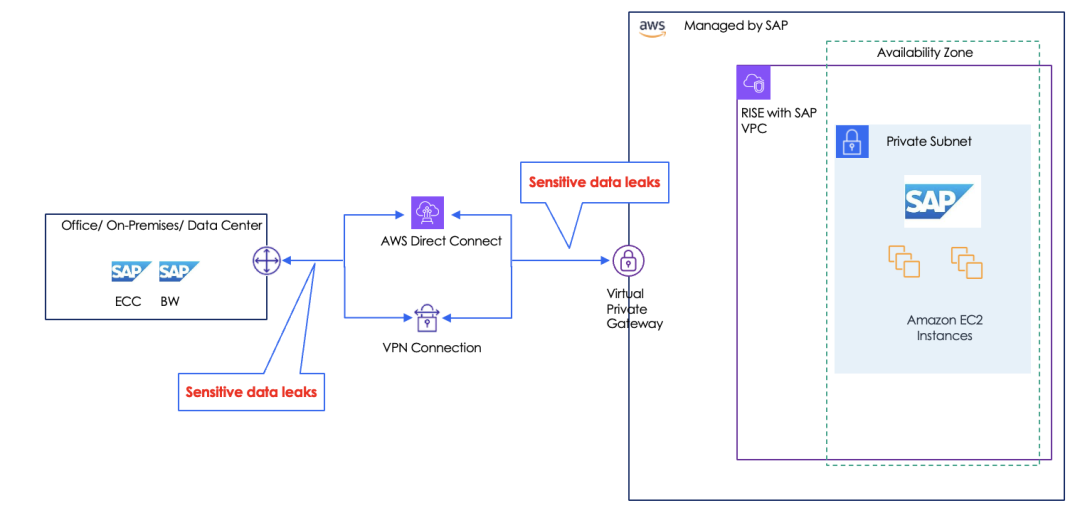
Figure 3: Insecure connectivity between on-prem and cloud during data migration
Challenge #3: Secure the connectivity between S/4HANA and manufacturing floors
SAP S/4HANA requires connectivity to manufacturing floors to bridge the gap between high-level business planning and physical, real-time shop-floor execution. This hybrid approach allows companies to leverage the speed and innovation of the cloud while maintaining control over sensitive, real-time production data.
Relying on private networks, site-to-site VPNs, or firewalls to secure this connectivity can enable lateral threat movement from a compromised device to SAP-connected services. Companies need to enforce one-to-one, least-privileged connectivity without disrupting production.
Consider the risk introduced by a seemingly benign device, such as a networked printer on the factory floor. While these devices require connectivity to SAP S/4HANA to facilitate real-time production labeling and reporting, they are often notorious for unpatched vulnerabilities and weak security controls. When connected via traditional site-to-site VPNs or legacy firewalls, the printer is typically placed on a trusted network segment. If an attacker compromises this printer, the broad, network-level access provided by the VPN acts as an open corridor, allowing the threat to move laterally from the shop floor directly into the core SAP environment. This vulnerability highlights why organizations can no longer rely on 'flat' network connectivity; instead, they must enforce one-to-one, application-level, least-privileged access that ensures a compromise at the edge cannot jeopardize critical business operations.
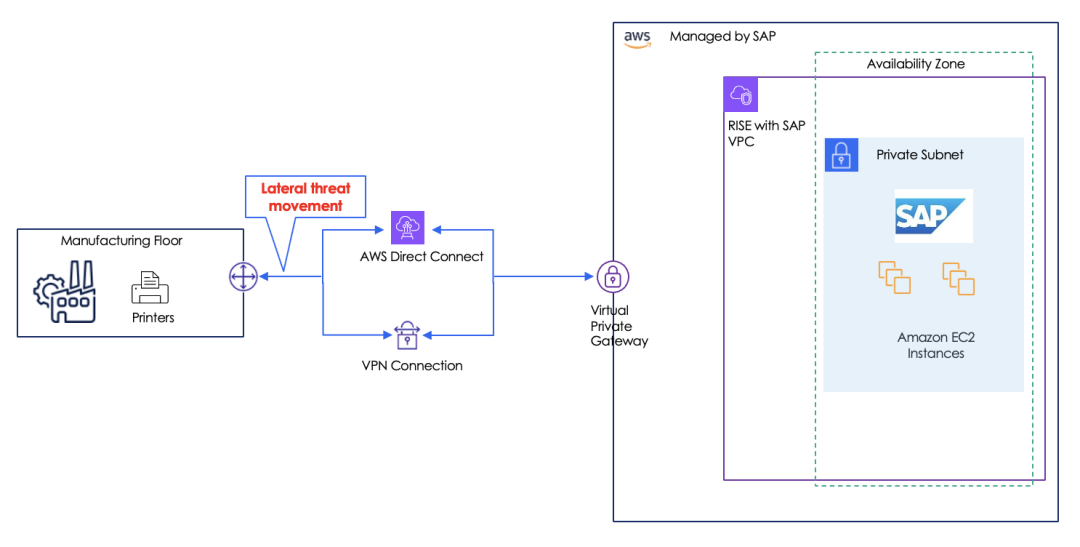
Figure 4: Unreliable connectivity between SAP S/4HANA and manufacturing floors
Challenge #4: Securing S/4HANA outbound traffic to SaaS without exposure
S/4HANA doesn’t operate in isolation—it increasingly connects to SaaS over the internet for downloading security patches, analytics, HR ecosystems, and collaboration. Outbound connectivity is where data leakage happens: uploads, API calls, file sync, and user-driven exports. If outbound traffic bypasses consistent inspection, blind spots grow—especially with encrypted traffic. At the same time, routing outbound traffic “backhaul-style” can add latency and complexity. Companies require secure, scalable inspection and data controls for internet/SaaS without reopening network exposure.
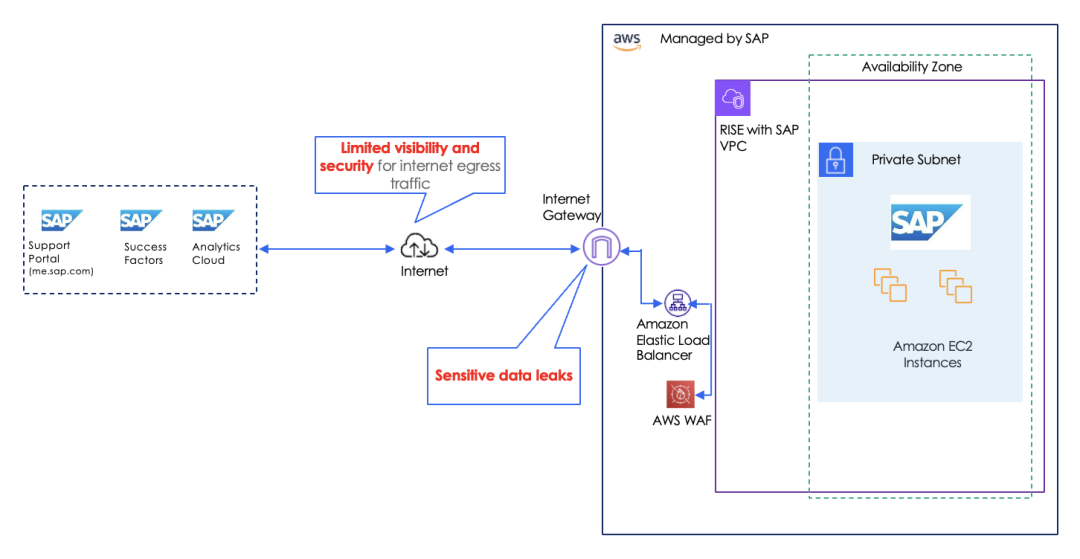
Figure 5: Lack of visibility of egress traffic to SaaS
Secure the journey with Zscaler Zero Trust Cloud
Zscaler Zero Trust Cloud —powered by the Zscaler Zero Trust Exchange, including ZIA and ZPA—replaces network-centric access with granular, identity- and policy-based controls. It secures SAP in a cloud-first environment by making S/4HANA undiscoverable and accessible only through verified, least-privilege access. It enables secure access for business partners. It protects SAP data in motion throughout the migration journey. It also secures SAP integration with the manufacturing floor, including print-job environments.
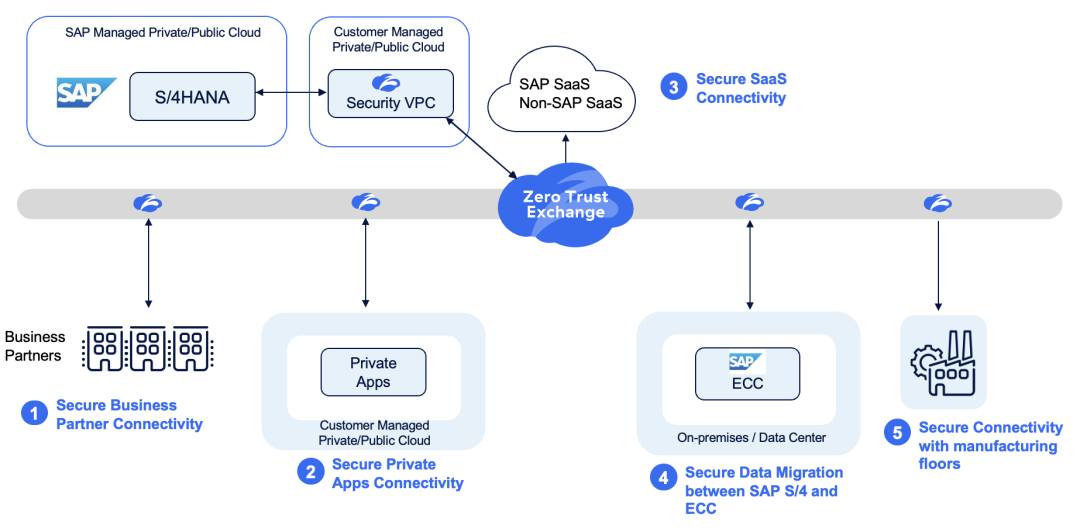
Figure 6: Secure SAP S/4HANA Migration with Zscaler Zero Trust Cloud
Next Steps
In our next blog, we will cover in detail how customers can provide secure access to business partners with a zero-trust approach leveraging Zscaler Zero Trust Cloud. Stay tuned!
このブログは役に立ちましたか?
免責事項:このブログは、Zscalerが情報提供のみを目的として作成したものであり、「現状のまま」提供されています。記載された内容の正確性、完全性、信頼性については一切保証されません。Zscalerは、ブログ内の情報の誤りや欠如、またはその情報に基づいて行われるいかなる行為に関して一切の責任を負いません。また、ブログ内でリンクされているサードパーティーのWebサイトおよびリソースは、利便性のみを目的として提供されており、その内容や運用についても一切の責任を負いません。すべての内容は予告なく変更される場合があります。このブログにアクセスすることで、これらの条件に同意し、情報の確認および使用は自己責任で行うことを理解したものとみなされます。




