Blog Zscaler
Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
Zscaler CXO Monthly Roundup | April 2026
Introduction
The CXO Monthly Roundup provides the latest Zscaler ThreatLabz research, alongside insights into other cyber-related subjects that matter to technology executives. This month’s roundup includes my thoughts on powerful AI frontier models, new linkages in the ransomware ecosystem (including Payouts King activity tied to former BlackBasta affiliates), fake software downloads that install remote access tooling like ScreenConnect, and nation-state campaigns that abuse trusted platforms like GitHub for command-and-control (C2).
My Thoughts on Enterprise Security Readiness Against Powerful AI Frontier Model (Mythos, GPT 5.5, and more)-Driven Attacks
CEO Jay Chaudhry recently posted about Zscaler’s partnership with Project Glasswing, giving us early access to Claude Mythos Preview to harden our platform and applications.
Mythos hasn’t changed the threat chain itself. Attackers will continue to find what’s exposed, break in through a weak point, move laterally, and steal data. What’s changed is the expertise required, speed, and scale. Anthropic has already reported what it described as the world’s first AI-orchestrated cyberattack. In another case, a threat actor allegedly used Claude and ChatGPT APIs to accelerate exploitation and automate breach workflows, compromising nine government agencies in Mexico.
Key observations:
- Within the next three months we’ll be looking at multiple frontier models with GPT5.5 and Mythos-like capabilities. They will be available to both defenders and attackers, making zero day exploits very common.
- The risk spans first-party code, third-party code (including open-source libraries), supply chain tooling, and more.
- Keeping up with these high fidelity findings will be critical and will require reimagining security tooling in your secure SDLC program that must be powered by these powerful frontier models.
- Patching alone can’t keep up when AI can find flaws and help build attacks at machine speed, especially when most security teams are already buried under a long list of vulnerability fixes.
Zero Trust Architecture adoption is the most critical defense in a world where Zero Day exploits are a commodity.
This is where we came up with the following high-impact recommendations that go beyond active vulnerability management to start reducing your risks today:
- Minimize your external attack surface: Reduce your external exposure by moving your applications behind a Zero Trust Architecture like Zscaler Private Access—you can’t attack what you can’t see.
- Understand your assets and associated risks: Establish complete visibility across exposed and internal assets and prioritize remediation using business context risk. This is where we help our customers with Exposure Management capabilities like Asset Exposure Management, External Attack Surface Management, and Unified Vulnerability Management, powered by AI.
- Prioritize deploying proactive defense with Deception: AI will use multiple paths to get to the action-on-objective stage and, in the process, inadvertently trigger carefully planted decoys in the environment. Zscaler customers are able to auto-contain the asset or identity from accessing all real applications while capturing full activity in the decoy environment for both AI and human adversaries using Zscaler Deception.
- AI red teaming & guardrails for your production models: Treat your production AI like a real attack surface. Protect it from prompt injection, toxic content, hallucinations, and model drift over time.
- Prioritize Zero Trust everywhere architecture: Apply Zero Trust consistently across remote and on-prem environments. Enforce user-to-application segmentation to prevent lateral propagation and reduce the blast radius from AI-driven attacks.
- AI-Powered Exposure Management: Prioritize remediation and patching using Zscaler Exposure Management Remediation Agent for high risk areas (applicable to both external and internal assets).
Zscaler has shared guidance in our webinar on how to protect your organization from attackers leveraging these powerful frontier models. In addition, I recommend visiting this article written by the Cloud Security Alliance with the contributions of several peer CXOs, which offers recommendations on building a risk register and timeline-driven action items.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception, Zscaler Private Access (AI Segmentation), Zscaler Exposure Management (Asset Exposure Management, External Attack Surface Management, Unified Vulnerability Management)
Payouts King Ransomware Linked to Former BlackBasta Affiliates
ThreatLabz has published a technical analysis of recent ransomware activity tied to a relatively obscure group known as Payouts King. The group appears to have ties to initial access brokers who previously collaborated with BlackBasta, a group that ceased operations in February 2025 following the leak of its internal chat logs. BlackBasta primarily relied on initial access brokers to carry out attacks on organizations, stealing sensitive data and encrypting files. Although BlackBasta has disbanded, its former affiliates have continued launching attacks, deploying various ransomware strains such as Cactus and now Payouts King.
The attack flow that Payouts King follows is shown below:
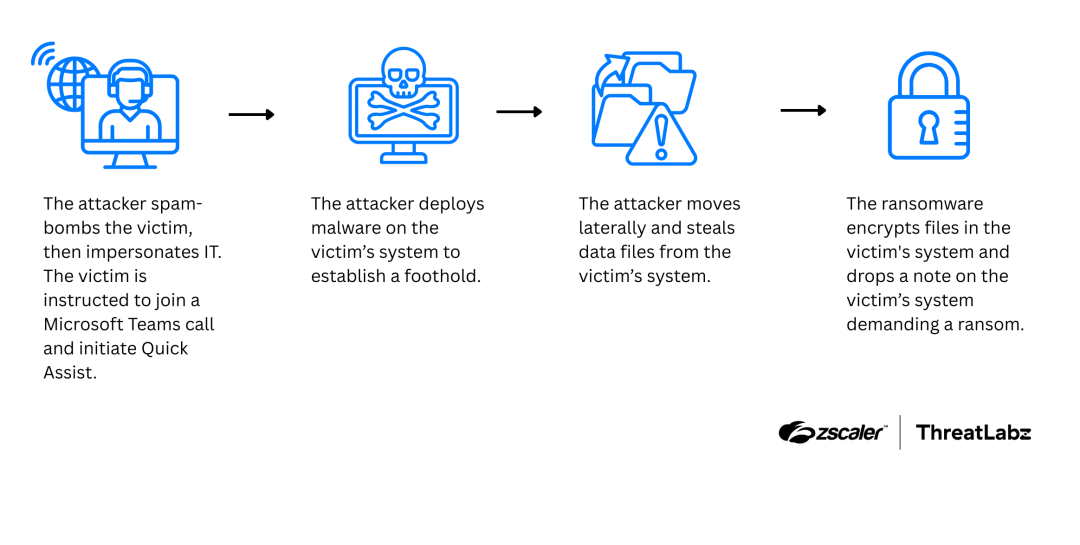
Figure 1: The Payouts King attack flow.
Payouts King attacks often begin with the threat actor spamming their target with emails and then pretending to be IT or helpdesk staff. They ask the victim to join a Microsoft Teams call and install a tool like Quick Assist so they can help “fix” the issue. Once they have access, the attacker installs tools on the system to gain control and start operating, using methods similar to BlackBasta.
The Payouts King ransomware employs techniques designed to evade detection by malware sandboxes, antivirus programs, and endpoint detection and response (EDR) tools.
During execution, the ransomware encrypts files and then takes steps to make recovery harder (for example, removing common Windows recovery artifacts and clearing traces). Victims may also find a ransom note (shown below) directing them to contact the attackers through encrypted channels.
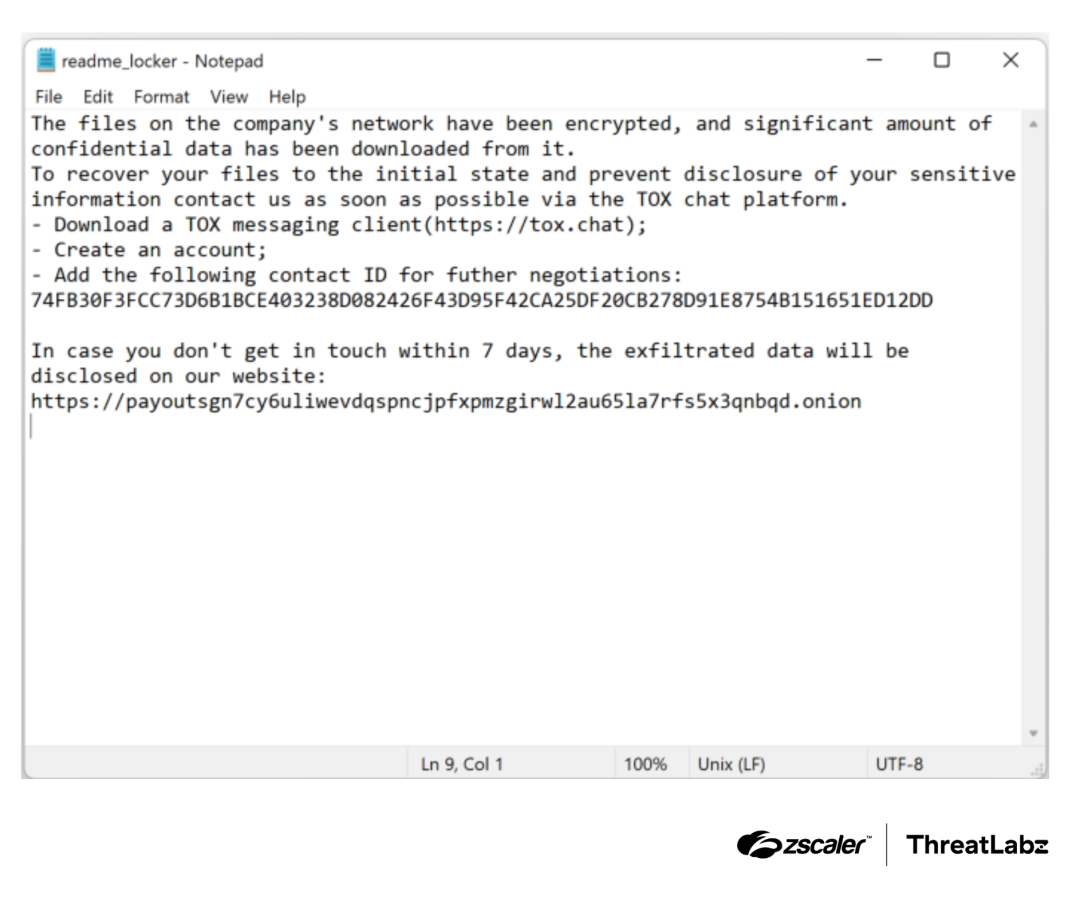
Figure 2: Example of Payouts King ransomware note.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
Fake Adobe Download Leads to ScreenConnect Remote Access
ThreatLabz published a technical analysis of a multi-stage attack chain that lures victims with a fake Adobe Acrobat Reader download and ultimately installs a legitimate remote access tool often abused by attackers—ScreenConnect, in this instance. The chain emphasizes heavy obfuscation and fileless/in-memory execution to reduce disk artifacts and hinder detection and analysis.
The attack chain is shown below:
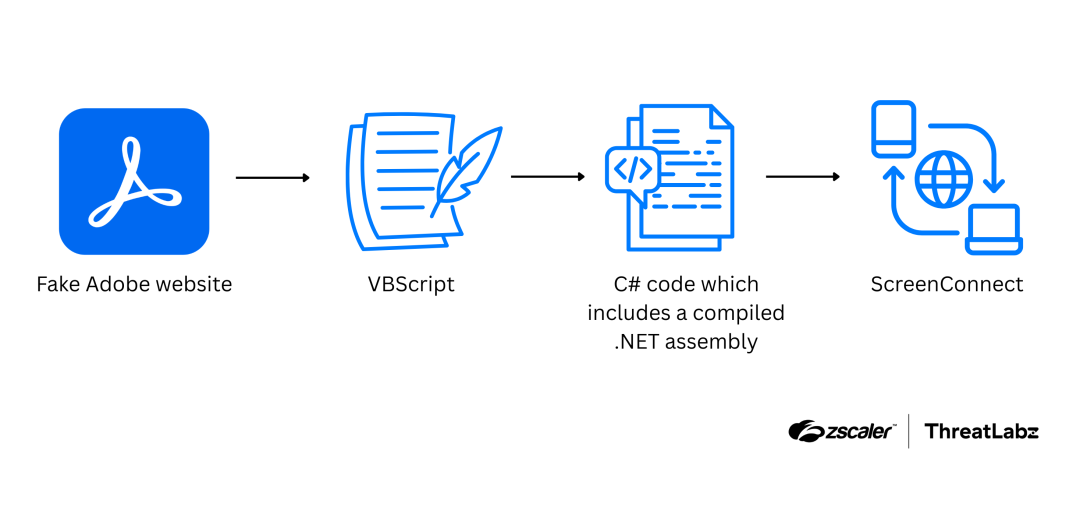
Figure 3: Attack chain for the ScreenConnect deployment.
The attack begins with a fake Adobe website that tricks users into downloading a hidden script. This script runs PowerShell with special settings to avoid restrictions, creates a temporary folder, downloads code from Google Drive, and runs a .NET loader directly in-memory without saving anything to the computer.
The attack tries to stay under the radar by tweaking process details so it looks like a normal Windows process, which can make it harder for some user‑mode/EDR tools to spot. It also bypasses security prompts to gain higher permissions without alerting the user. In the final step, PowerShell downloads and installs ScreenConnect, which gives attackers remote control over the victim's system.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
Tropic Trooper Abuses GitHub to Control Backdoor (AdaptixC2)
ThreatLabz identified a malicious ZIP file containing military-themed documents aimed at Chinese-speaking individuals. Our technical analysis revealed an attack involving a modified PDF reader that installs a backdoor agent, eventually enabling remote access. The campaign appeared to target Chinese-speaking individuals in Taiwan, and individuals in South Korea and Japan.
Based on the observed methods and patterns, ThreatLabz confidently attributed this activity to a group known as Tropic Trooper.
The overall attack process is outlined below:
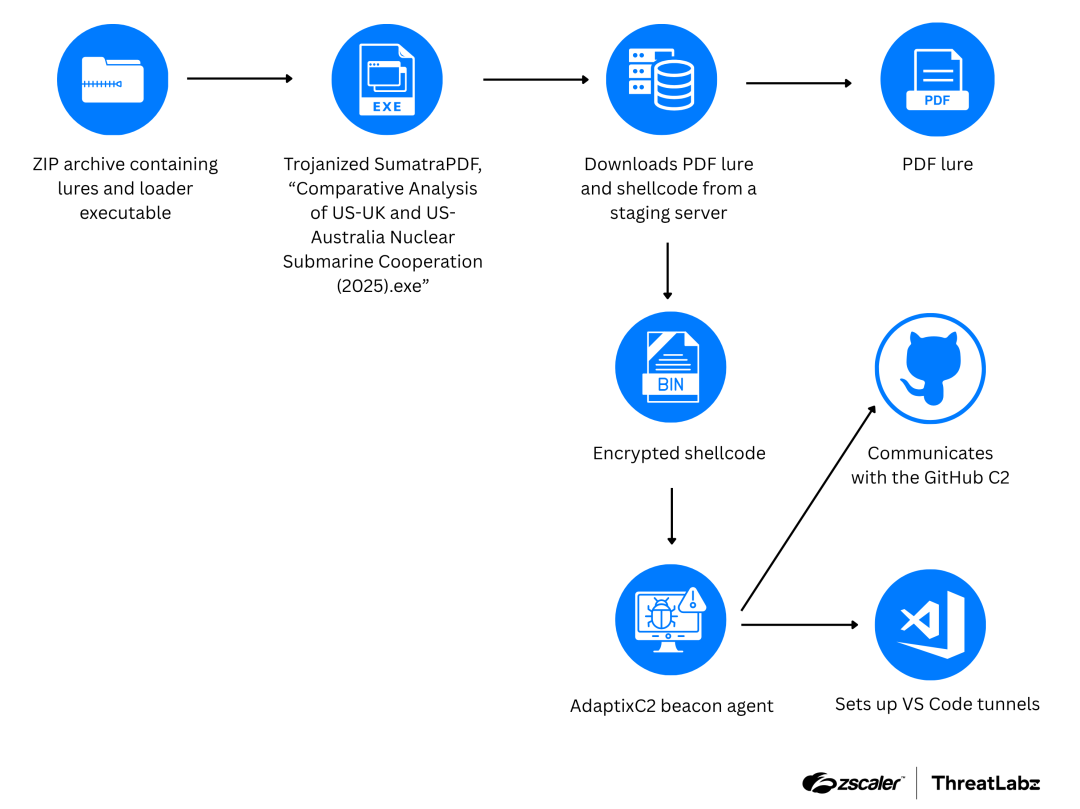
Figure 4: Tropic Trooper attack chain leading to the deployment of an AdaptixC2 Beacon and VS Code tunnels.
The attack starts with a trojanized SumatraPDF reader that executes malicious code. This code sets up key configurations, retrieves a decoy PDF to display, and downloads additional malicious components. The PDF lure is shown below:
Figure 5: Tropic Trooper military-themed PDF lure.
These components are decrypted and executed in-memory and then deliver a backdoor agent, AdaptixC2 Beacon.
The AdaptixC2 Beacon agent incorporates a customized Beacon Listener and uses GitHub as its communication channel.
ThreatLabz observed that the attackers primarily used the AdaptixC2 Beacon agent for initial access and reconnaissance. If a target was considered valuable, the attackers deployed additional tools for remote access such as Visual Studio (VS) Code. In some cases, the attackers installed modified applications to blend in with the victim's regular software usage.
Zscaler Zero Trust Exchange Coverage – Zscaler Internet Access (Advanced Cloud Sandbox, Advanced Threat Protection, Advanced Cloud Firewall, SSL Inspection), Deception
Threat Updates
- Malicious PyPI packages distributing RATs: ThreatLabz uncovered two campaigns distributing malware through Python Package Index (PyPI) packages. One group of packages shares a common codebase, features layered obfuscation and a staged execution process, and distributes a RAT that uses Telegram for C2 communication. In addition, ThreatLabz discovered another package that downloads a Python-based RAT from Google Drive. Visit our post for more information on package names, hashes, and author details.
- Anatsa: ThreatLabz discovered another fake document reader on the Google Play Store that had over 10,000 downloads and delivered the Anatsa Android trojan. Visit our post for indicators of compromise.
Conclusion
Powerful frontier AI models aren’t rewriting the defender and attacker playbooks—they’re accelerating it, making sophisticated attacks easier to execute at scale and harder to stay ahead of with patching alone. The threats highlighted in this newsletter, from ransomware operations to fileless malware and trusted-platform abuse, show how quickly adversaries can blend social engineering, stealth, and legitimate tools to reach their objectives. The most practical path forward is to reduce what’s exposed, assume compromise, and limit blast radius with Zero Trust, segmentation, and strong identity controls. Pair that with AI-powered exposure management, proactive deception, and dedicated red teaming and guardrails for your own AI systems. The organizations that act now will be the ones that keep zero days from becoming business disruptions.
Cet article a-t-il été utile ?
Clause de non-responsabilité : Cet article de blog a été créé par Zscaler à des fins d’information uniquement et est fourni « en l’état » sans aucune garantie d’exactitude, d’exhaustivité ou de fiabilité. Zscaler n’assume aucune responsabilité pour toute erreur ou omission ou pour toute action prise sur la base des informations fournies. Tous les sites Web ou ressources de tiers liés à cet article de blog sont fournis pour des raisons de commodité uniquement, et Zscaler n’est pas responsable de leur contenu ni de leurs pratiques. Tout le contenu peut être modifié sans préavis. En accédant à ce blog, vous acceptez ces conditions et reconnaissez qu’il est de votre responsabilité de vérifier et d’utiliser les informations en fonction de vos besoins.
Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
En envoyant le formulaire, vous acceptez notre politique de confidentialité.




