Earlier today, a large DDoS attack disrupted a significant portion of Internet traffic, starting on the US East Coast, spreading to the West Coast and ultimately Europe. This attack was particularly damaging as it wasn't focused on a specific domain, but rather a popular DNS provider (Dyn). Many major Internet properties leverage Dyn for DNS services and were impacted as a result. A quick visit to downdetector.com will show you the many popular sites impacted.
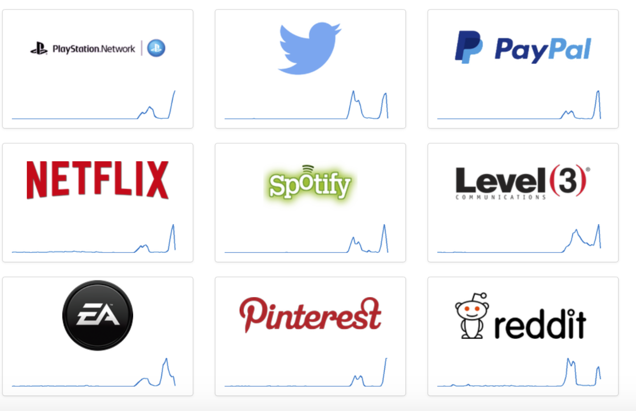
Fig. 1 – DownDetector.com screenshot 10/21/16
DDoS attacks against DNS providers are generally more challenging to accomplish, given the redundant nature of the services, which suggests that this attack came with significant firepower. DNS attacks, when successful are however more damaging as they impact any Internet properties relying on that particular DNS provider.
In today's world, DNS is a fundamental part of critical infrastructure. DNS provides the translation between human friendly domain names and machine readable IP addresses. In short, without DNS services, users are unable to reach websites, even though the sites themselves may be running just fine. Given the amount of commerce done over the Internet today, it is not surprising that the US Department of Homeland Security is already investigating the attack.
DDoS attacks have been in the spotlight recently after popular security journalist Brian Krebs had his site taken offline by what at the time was the largest DDoS attack ever recorded by traffic volume. That particular attack was eye opening, not just due to its size, but because it was powered by thousands of insecure IoT devices. It's no secret that Internet-connected devices have for years been sold with weak to nonexistent security and known default passwords that are never changed. This was, however, a moment where the risk posed by such devices was on clear display.
The Mirai source code from the KrebsOnSecurity DDoS attack was leaked online after that attack and, not surprisingly, it appears that the Dyn DDoS attack was powered at least in part by the same Mirai code and vulnerable IoT devices, including webcams and DVRs. What was the motivation for the attack on Dyn? Retaliation for Dyn researcher Doug Madory's recent talk on DDoS attacks likely played a role, much as Brian Krebs was targeted after he reported on vDOS, a DDoS-for-hire service.
The power of recent attacks, the damage done, and the fact that such attacks can be conducted by small teams of adversaries or even determined individuals should serve as a wakeup call to enterprises everywhere. Companies often mistakenly assume that their Internet infrastructure is "too big to fail." They’ve purchased significant amounts of bandwidth, rarely coming anywhere near peak capacity, and they leverage service providers that can deliver more as needed. Yet the reality of a DDoS attack exceeding 620 Gbps, as was the case in the KrebsOnSecurity attack, is that any site would struggle to stay afloat. Bandwidth alone isn’t enough.
Enterprises require proactive DDoS defense services to mitigate the attacks as they emerge. The fact that such attacks were driven by insecure IoT devices, which are trivially easy to identify and exploit, is deeply concerning as it exposes tremendous firepower to even small, unsophisticated groups of attackers. The CodeRed and Nimda worms launched in 2001 turned out to be the tipping point that led to the release of Bill Gates' famed Trustworthy Computing memo in January 2002. That was a seminal moment for software security. It was the moment that software vendors turned the corner and began "baking security in" as opposed to "brushing it on." The massive IoT-powered DDoS attacks against krebsonsecurity and Dyn need to serve as a wakeup call for hardware vendors. This needs to be the seminal moment that leads hardware vendors to turn the corner on security.





