Zscaler Blog
Get the latest Zscaler blog updates in your inbox
The IT War Room Survival Guide: Ending the "Blame Game" with Correlated Data in 5 Minutes
The "War Room" is a familiar but costly necessity. When a business-critical SaaS application like Microsoft 365 or Salesforce slows down, the clock starts ticking on lost productivity.
The traditional response—gathering representatives from the Service Desk, Network, and Security teams into a single meeting—often leads to a "Blame Game" where teams spend more time proving it isn't their fault than finding the root cause. For Network Operations (NetOps) teams, the "network is slow" complaint is a daily occurrence. For Security teams, the suspicion often falls on SSL inspection or CASB policies. Without visibility into the user’s browser, IT teams are "flying blind."
This guide outlines how to exit that cycle in under five minutes by leveraging Zscaler Digital Experience (ZDX) Real User Monitoring (RUM) to monitor 100% of real user traffic for critical SaaS and internal applications, reducing your Mean Time to Detection (MTTD) and Resolution (MTTR).
The Problem: The Visibility Gap in a "Work-from-Anywhere" World
The primary reason War Rooms last for hours is a lack of alignment between what the system says and what the user actually sees. In a distributed workforce, traditional tools end at the corporate edge, leaving a massive blind spot in the "last mile" home Wi-Fi, regional ISPs, and local device health.
While synthetic monitoring is proactive and essential for baseline testing, it cannot account for every unique user variable. In a typical War Room:
- The Network Team sees a healthy WAN link, so "everything is green."
- The Security Team insists their DLP and SSL inspection policies aren't adding overhead, but they lack the data to prove it.
- The User still sees a loading page or spinning wheel.
Without data from the user's actual session, you are "flying blind" against variables you don't control, such as unstable home Wi-Fi, regional ISP outages, or bloated browser extensions.
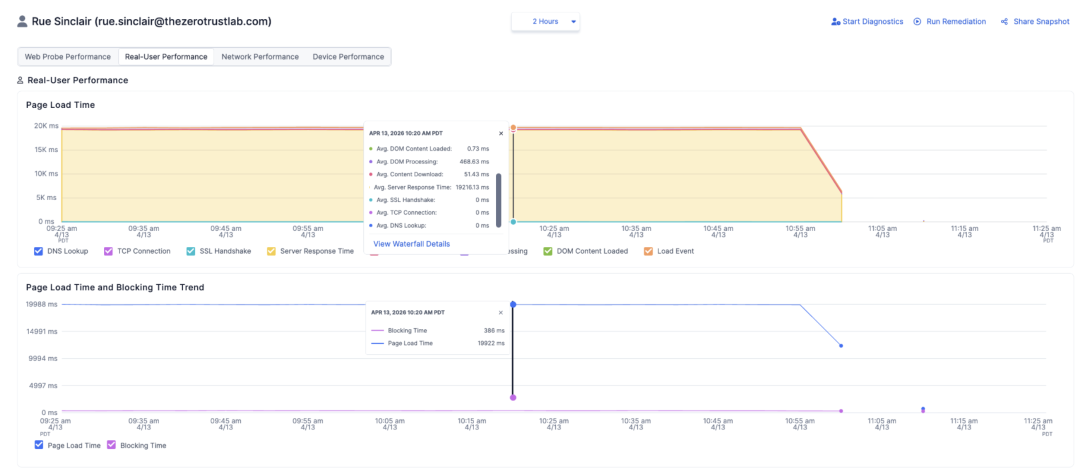
Step 1: Identifying the Symptoms (The First 60 Seconds)
For the Service Desk, the first minute is about "One-Click Triage." Instead of manual back-and-forth with a frustrated user, Service Desk can immediately access full session context on the user level. ZDX RUM utilizes lightweight browser extensions for Chrome and Microsoft Edge to track user sessions and application load behavior in near real-time.
Within the first minute of an investigation, a Service Desk admin can:
- Instant Ticket Triage: Determine if the issue is widespread (regional ISP/SaaS backbone) or localized to a specific workstation, outdated browser version, or poor home Wi-Fi signal.
- Baseline Performance: Establish accurate performance baselines across all users to identify significant trend shifts.
- Check High-Level Metrics: View real user session data alongside active synthetic monitoring and cloud path probes all from a single unified dashboard.
By gaining this "last mile" visibility, the Service Desk can stop the flood of vague tickets and ensure only valid, data-backed issues are escalated to specialized teams.
Step 2: Dismantling the Blame Game (Minutes 2–3)
To end the finger-pointing, you need to correlate what the user reports with what the data actually shows. ZDX provides a unified view that breaks down the user experience into three distinct pillars, allowing NetOps and Security to achieve "Mean Time to Innocence" almost instantly.
- Device Health: Monitor device type, CPU/Memory spikes, and even the impact of security endpoint tools that might be blocking the browser's main thread.
- Network Path: Identify bottlenecks in the "Last Mile," including DNS lookup, TCP connect time, and SSL/TLS handshake timings.
- Application Performance: Distinguish between server response time (Time to First Byte) and client-side rendering time.
This is where Security teams can shine. By monitoring SSL negotiation times and comparing the performance of internal apps accessed via ZPA versus direct connections, they can definitively prove that security is performing as it should and is not a bottleneck. If a new decryption policy is deployed, the data will show immediately if it's causing latency or if the problem lies elsewhere.
Step 3: The 5-Minute Resolution with Waterfall Charts
Now on to resolution. NetOps can use deep-dive waterfall analyses to provide a granular, moment-by-moment breakdown of the page load process to pinpoint the exact element degrading performance.
In minutes, an admin can drill down into a specific session to identify:
- Network vs. Security Timings: Pinpoint if the delay is in the DNS lookup, an inefficient SSL handshake, or a regional ISP bottleneck.
- Backend vs. Frontend: Use Time to First Byte (TTFB) to prove if the application backend is slow, or if the delay is in the browser rendering.
- Resource & API Bottlenecks: Identify if stricter CASB or firewall rules are blocking critical background API calls (XHR errors) or if oversized images and third-party scripts are the culprit.
- Web Vitals: Track Largest Contentful Paint (LCP) and Cumulative Layout Shift (CLS) to understand why key content is slow to appear.
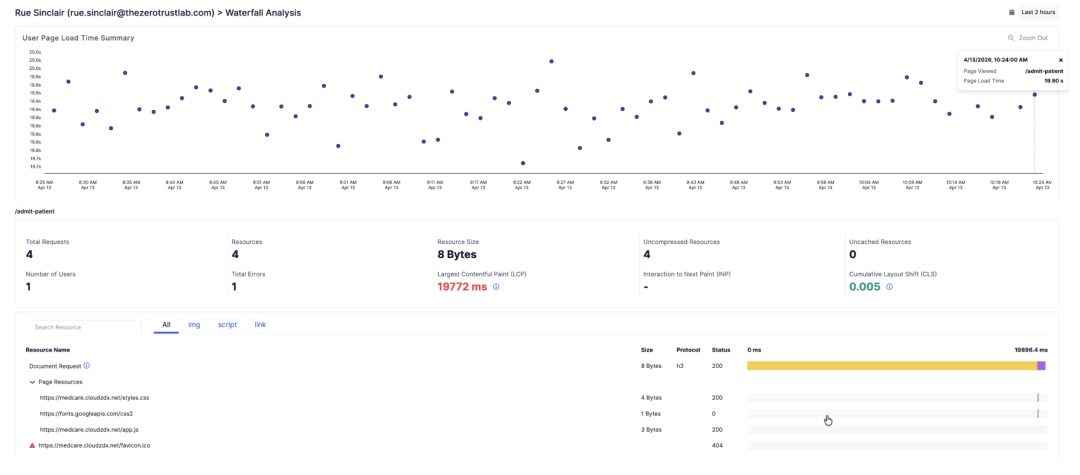
This allows you to drastically reduce MTTR. You can stop wasting time trying to replicate user issues and instead go directly to the user's session data to find the root cause.
Conclusion: From Firefighting to Strategic Management
The goal of this guide isn't just to survive the War Room, it’s to make it obsolete. By shifting from reactive firefighting to proactive assurance, IT teams, from the Service Desk to Network Security, can identify poor-performing applications or regional ISP outages before users even create a ticket.
ZDX’s native integration into the Zscaler Zero Trust Exchange means you get this unparalleled context without adding operational complexity. When you have the data to prove exactly where a bottleneck resides, you don't need a War Room. You just need a resolution.
Was this post useful?
Disclaimer: This blog post has been created by Zscaler for informational purposes only and is provided "as is" without any guarantees of accuracy, completeness or reliability. Zscaler assumes no responsibility for any errors or omissions or for any actions taken based on the information provided. Any third-party websites or resources linked in this blog post are provided for convenience only, and Zscaler is not responsible for their content or practices. All content is subject to change without notice. By accessing this blog, you agree to these terms and acknowledge your sole responsibility to verify and use the information as appropriate for your needs.
Get the latest Zscaler blog updates in your inbox
By submitting the form, you are agreeing to our privacy policy.




