This article originally appeared on Medium.
Props to Chris Wloch at Zscaler for this definition of Zero Trust…
“If a thief gets into your house they have full access to every room, unless you lock all the doors inside as well.
Lock every door and require fingerprint verification for access. That’s how I explain Zero Trust to my Grandparents. “
We are now in year two of “The Digital Decade.” Many traditional industries, capabilities, products, and services have moved online, either as part of enterprise digital evolution, or because new operational needs imposed by COVID over the last twelve months. Businesses in every industry (Government, Textile, Pottery, Insurance, Finance, and every vertical in between) are going digital. And that puts the topic of security and privacy front and center in the minds of senior executives.
Higher customer (and end-user!) expectations have driven businesses to change to adopt a digital experience. Security and privacy are undergoing a similar evolution, and that's where Zero Trust security philosophy, platforms, and services can impact your business service delivery, and change the way you design your brand, customer experience, speed of driving change, ease of doing business, and even reputation.
Network and security architectures from the post dot-com boom era were designed for stability, rigidity, and control, and not the agility needed to support rapid business evolution. They are -- by their very nature -- the epitome of inflexibility. Increases in data require increases in bandwidth. Is traffic spiking? Add more boxes. Pivot to work from home? Add more boxes. (Oh, and VPN procurement is probably backlogged, so delivery will be delayed.) For enterprises running duplicated stacks of security appliances, the ideals of operational accuracy, performance optimization, and business agility remain pipe dreams.
The “patching lag”: Putting enterprises at unnecessary risk of attack
Change is hard. IT department “box-hugging” is easy: the nearby hardware stack down the hall offers an illusion of control, of infrastructure within arms’ reach. Plus, it’s easy to “go with what you know,” and an IT organization’s existing security certifications can understandably bias decision-making toward older, hardware-based technologies.
But that complexity kills. Running changes—e.g., security patches, new regulatory or compliance workflows -- through an environment burdened with stacks and stacks of hardware requires extensive global coordination...extensive manual global coordination. That leads to errors, and ultimately, to greater risk exposure.
So just what is zero trust?
A zero trust architecture (ZTA) is the cloud-based evolution of the legacy network security model. Progressive enterprises are digitally transforming IT operations to adopt ZTA. In a ZTA enterprise, security is immediate, delivered inline from the cloud edge, between user and internet (via web proxy), or between user and application. Performance is optimized because data-travel is minimized. Connections are direct, ephemeral, and secured, whether those connections connect user to app, app to app, or system to system. There is no boundary to breach, and because systems are not visible to the open internet, attackable surface is diminished. There is no conceptual moat, no exposed metaphorical castle (or neighboring castles) for adversaries to ransack (in east-west fashion).
What’s the business justification for zero trust?
In two words, secure agility! ZTA allows security to shift focus to shared business objectives. In this way, ZTA can transform IT from “The Ministry of ‘No’” to the “Ministry of ‘This is How We Get Things Done.'”
Enterprise secure digital transformation using Zero Trust architecture seems an easy choice for an enterprise IT organization: better security, better resilience, faster performance, and lower cost.
When it comes to digital competition, speed matters, and driving change at warp speed is required. In traditional environments, making any change to legacy DMZ firewall infrastructure is a cumbersome process, restricted to lower-traffic, weekend-only scheduling. Cloud-based ZTA is dynamic, with policy-based security that can be adapted on-the-fly. You can’t afford to be able to change once a month when your evolving digital challengers can deliver change twenty times a day.
Efficiency, savings, time: Charting the indirect impacts of ZTA
Cloud-based ZTA delivers the next evolution of enterprise security. But that simple fact should not obscure its tangible impact on a customer enterprise: ZTA is a business solution that delivers business benefits. Let’s compare two examples, National Oilwell Varco and “Company A.”
One hundred laptops. That's how many machines CIO Alex Philips' IT team at National Oilwell Varco (NOV) had to re-image each month. Occasionally, the need for the fix would be technical. But most often, the machine had been infected with malware. Each laptop had to be shipped to headquarters, wiped, then completely reconfigured. And 100 laptops was an average: In some months between 2013 and 2016, as many as 200 machines needed disinfecting.
From a business standpoint, malware's impact on NOV was costly. Re-imaging is an understandably manual process, and each individual laptop required some level of individual attention. From downtime, to coordinating loaners, to replacing machines, every stage of the process to clean up an infected laptop impacted NOV in a measurable way: Data would be lost, productivity would dip, costs would be incurred, and effort would be expended, all to get a functioning laptop back in an employee's hands as quickly and possible. Philips envisioned a world in which it didn't have to be that way. And after August 2016, it wasn't.
Company A relies on legacy network and security infrastructure to protect its enterprise data traffic. Company A's IT team employs a stack of legacy hardware appliances in its headquarters to secure its corporate network perimeter. Each single-function machine in that stack is replicated in its 30 regional offices around the globe.
Each individual Company A DMZ includes 12 different products in its hardware stack, each appliance fulfilling a discrete networking or security purpose. (Sample functions/appliances include firewall, URL-filtering, antivirus, DLP, SSL inspection, load-balancing, DDoS protection, VPN-concentration, sandboxing, and more.) Each of Company A’s 30 DMZs require two full-time staff to maintain and operate the networking and security hardware infrastructure. Each individual appliance in each location must be maintained, with security patches updated manually (and instantly). Provisioning such equipment requires vendor and product assessments, procurement workflows, cross-division administrative support, and extensive upfront planning.
Company A's CTO manages more than 60 employees and oversees the purchase, maintenance, and operations of 360 individual network and security hardware appliances. The CTO's annual line-item budget measures in the tens of millions of U.S. dollars.
What does the Company A CTO’s massive budget buy? Certainly not better security. Certainly not peace of mind. Instead, it puts the CTO on a hamster wheel of futility, reacting to each latest threat, hardware flaw, or metaphorical fire, all just to keep up with hackers poised to attack. (Those hackers, by the way, are well-funded, sometimes state-sponsored, growing more savvy in method over time, and growing more destructive in intent.)
“So…why are you in the network security business?”
Enterprise leaders that cling to (or tacitly allow their IT departments to cling to) outdated security models do so at their own peril, at great risk to their livelihood, and at great risk to their organization. In doing so, they limit organizational agility, incur unnecessary overhead, hinder growth, and complicate operational management.
Preserving a legacy of antiquated hardware also places an enterprise IT organization squarely in the business of network security, with a CTO committed to operating a NOC and infrastructure intended to counter a growing wave of adversaries.
Enterprise leaders that sustain insecure, antiquated infrastructure have a responsibility to either justify outdated practices or modernize: Why is the organization in the network security business? Can it secure its enterprise data, users, assets, and resources better than a cloud-edge service provider with thousands or security experts working 24/7 to block the latest adversarial threats? Can it anticipate the next supply-chain threat? Can it patch instantly? (Really, really instantly?)
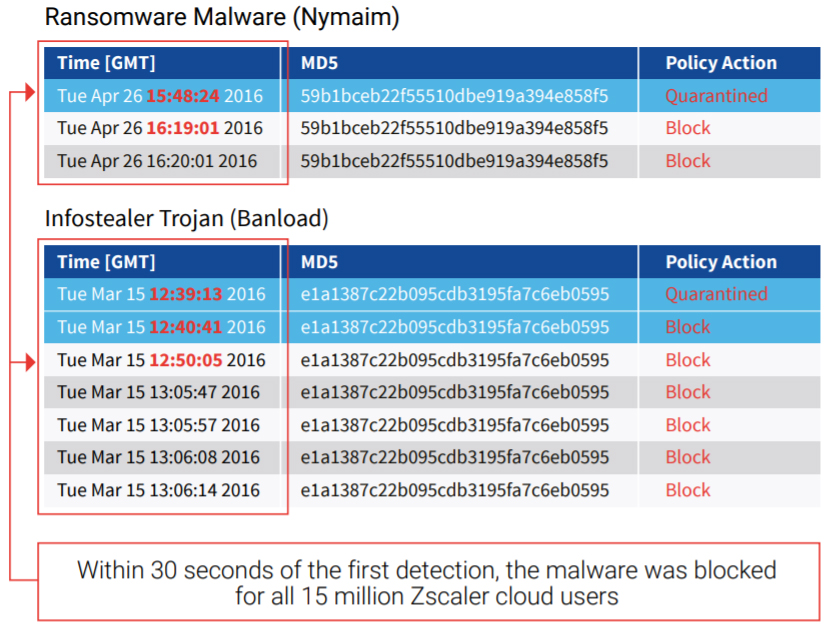
Figure 1. In March, 2016, hackers targeted a Zscaler customer that had a zero trust architecture. Zscaler Cloud Sandbox analyzed the threats and, in a matter of 30 seconds, blocked them for that customer and for all the millions of users on the cloud-based Zscaler Zero Trust Exchange around the world.
The Zero Trust Architecture: The new (reduced) cost of doing business
NOV CIO Alex Philips knows the practical impact a Zero Trust Architecture delivers. He led NOV’s secure digital transformation, adopting a Zero Trust model in August 2016. Shifting to security delivered via edge-computing web proxy, NOV eliminated its DMZs entirely. By reducing its reliance on MPLS networks and hardware-based security, NOV “slashed tens of millions of dollars from [its IT] budget.” NOV employees now enjoy better (read: faster) connectivity performance, improved security (with full SSL/TLS inspection), and better mobile-device access (which was particularly valuable when the company shifted to remote work last year). Since Philips and NOV adopted a Zero Trust Architecture, his IT team re-images only one or two laptops per month, freeing staff to concentrate on strategic, business-critical objectives.
As the past year has shown, ability to pivot is an essential enterprise competitive advantage. In every industry, new players use agility to disrupt. A Zero Trust Architecture delivers agility. And better security. And better performance. Stakeholders must demand more from business leaders: If those business leaders were to design operational infrastructure, workflows, and operations from scratch, would they look like they do now? And if those leaders could employ a Zero Trust Architecture to deliver better security, greater agility, significantly reduced costs, and significantly-reduced risk, why wouldn’t they?




