The Greek philosopher Heraclitus once said, “Change is the only constant in life.” This statement certainly applies to the modern workplace. Your users, data, and applications were once relegated to the corporate office and data center. But, today, 50 percent of all corporate data is stored in the cloud, and 70 percent of the applications used by businesses are SaaS-based. And no one can ignore the fact that, while already in motion, the global pandemic rapidly accelerated the shift to remote work. Overnight, organizations saw a 300 percent increase in the percentage of total employees that are remote workers.
While the numbers may adjust to some extent when we eventually emerge on the other side of the pandemic, the reality is this forward momentum will not reverse. Remote work is here to stay, at minimum in the form of a hybrid workplace. Data will become even more distributed across clouds, applications, and user devices spread around the globe. And, businesses will continue to take advantage of the benefits of moving applications out of the data center and into public clouds and SaaS.
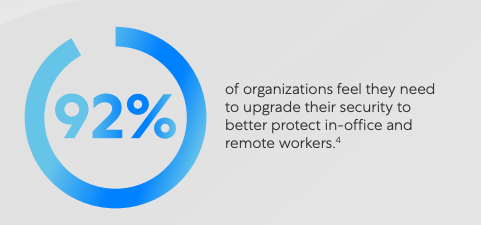
These shifts demand change beyond what can be seen upon first glance. Organizations embracing digital transformation quickly realize that the old ways of protecting the perimeter and trusting everything inside of it may have worked in the past, but just don’t cut it in their new reality. There is no perimeter anymore. So, how can you stake your security on firewalls and perimeter-based tactics? Ninety-two percent of organizations realize you can’t, and recognize the need to upgrade their security to better protect this new hybrid-workforce reality.
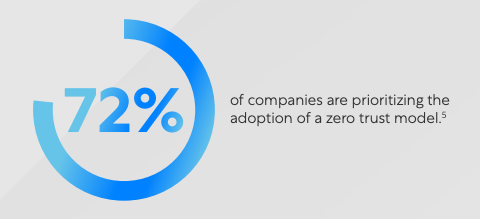
But the question remains: how do you achieve this? According to Cybersecurity Insiders, 72 percent of organizations are prioritizing the adoption of a zero trust model. Zero trust is a strategy—a foundation for your security ecosystem—based upon the principle of least-privileged access, combined with the idea that users should not be inherently trusted.
Organizations are quickly coming to the realization that you can’t do zero trust with firewalls and VPNs. In fact, 47 percent of organizations don’t have confidence that their existing technologies will help them achieve zero trust. Unfortunately, the other 53 percent will place users on the corporate network, mistakenly trusting their existing technologies.
Connecting users to the corporate network creates significant challenges to achieving zero trust. VPN gateways have an open inbound listener to allow remote users to connect. Unfortunately, this also makes it easy for attackers to discover and gain access to the network. Once on the network, the inherent trust placed in the user makes it easy for threats and attackers to move laterally across the network to locate and exploit valuable assets and data.
To avoid connecting users to the network, organizations will sometimes choose to publish applications on the Internet instead, exposing IP addresses to make applications easier for your employees to find and access. But this is just moving the attack surface from the connectivity infrastructure to the application itself - not an improvement, and often carrying even more risk.
Inspection of encrypted traffic is more critical than ever as attacks over encrypted channels increased 314 percent in the last year. But, solutions leveraging passthrough firewalls have limited ability to inspect encrypted traffic inline and at scale. Even if they could inspect traffic, the passthrough approach allows content to reach its destination before analysis is complete, only signaling a problem after it has occurred and potentially spread across your entire network.
So, if your firewalls and VPNs aren’t fit for zero trust, what can you do? According to Socrates, “The secret of change is to focus all of your energy not on fighting the old, but on building the new.” As such, zero trust requires a fundamentally different approach. Instead of blind trust and complex network segmentation—the hallmarks of firewall-based solutions—zero trust authorizes connections using identity and context, where context is based upon business policy and dynamically reassessed as conditions change.
Zero trust requires an inline platform possessing three critical capabilities. First, it must be able to eliminate the lateral movement of threats by connecting users directly and only to the applications they need to do their job, while never placing users on the corporate network. Second, it must minimize the attack surface by making users and applications invisible to the internet because you cannot attack what you cannot see. Finally, it must stop threats and data loss, and that means full inspection of all traffic—including encrypted traffic—without choking application performance.
“Change is the law of life. And those who look only to the past or present are certain to miss the future.” - John F. Kennedy
To successfully achieve digital transformation, organizations must adopt a new approach to networking and security, one that enables true zero trust. Every day, the Zscaler Zero Trust Exchange helps IT teams embrace zero trust on their transformation journey. The zero trust exchange secures over 200 billion transactions and prevents more than 7 billion security incidents and policy violations every day, all while processing over 200 thousand unique security updates to ensure your organization is secure.
To find out more about how Zscaler can help you transform securely using zero trust, download our complimentary whitepaper, “The Top Five Risks of Perimeter Firewalls and the One Way to Overcome Them All” and register for our webinar, “Why Firewalls Cannot Do Zero Trust.”





