To learn more about the top DNS threats facing organizations today (and what to do about them), check out the paper “Decoding Modern DNS Threats”
At Zscaler, our mission is to enable seamless, secure access to the internet and applications in every possible circumstance. That means any user, device, or workload, connecting to any resource, on any port or protocol, from anywhere in the world, at any time.
The DNS security features built into the Zscaler Zero Trust Exchange are critical to our fulfillment of that mission. As a cloud native proxy, the Zscaler Zero Trust Exchange delivers scalable inspection, advanced threat protection, and DNS resolution at more than 150 edge locations for optimal performance and security around the globe.
Today, Zscaler is excited to announce new innovations that further this promise. We’ve made enhancements to the security, availability, flexibility, and performance of our DNS security module, including:
- DNS encryption of plaintext traffic into DNS-over-HTTPS (DoH) for better privacy and security
- Availability improvements with enhanced failover capabilities that automatically redirect traffic to a secondary resolver if the primary fails
- DNS security enhancements including improved DNS tunnel protection to prevent data exfiltration, and enhanced DGA detection to block any command and control malware activities
- Protective DNS enablement, encrypting and sending all government agency traffic to protective DNS (PDNS) resolvers in alignment with mandates from the NSA, CISA, and the National Cyber Security Centre
- Better user experience with configurable DNS ECS to provide the best localized resolution based on the country, and to ensure users experience webpages with their local language, content, and currency
- Enhanced error handling and reporting to provide more control and visibility
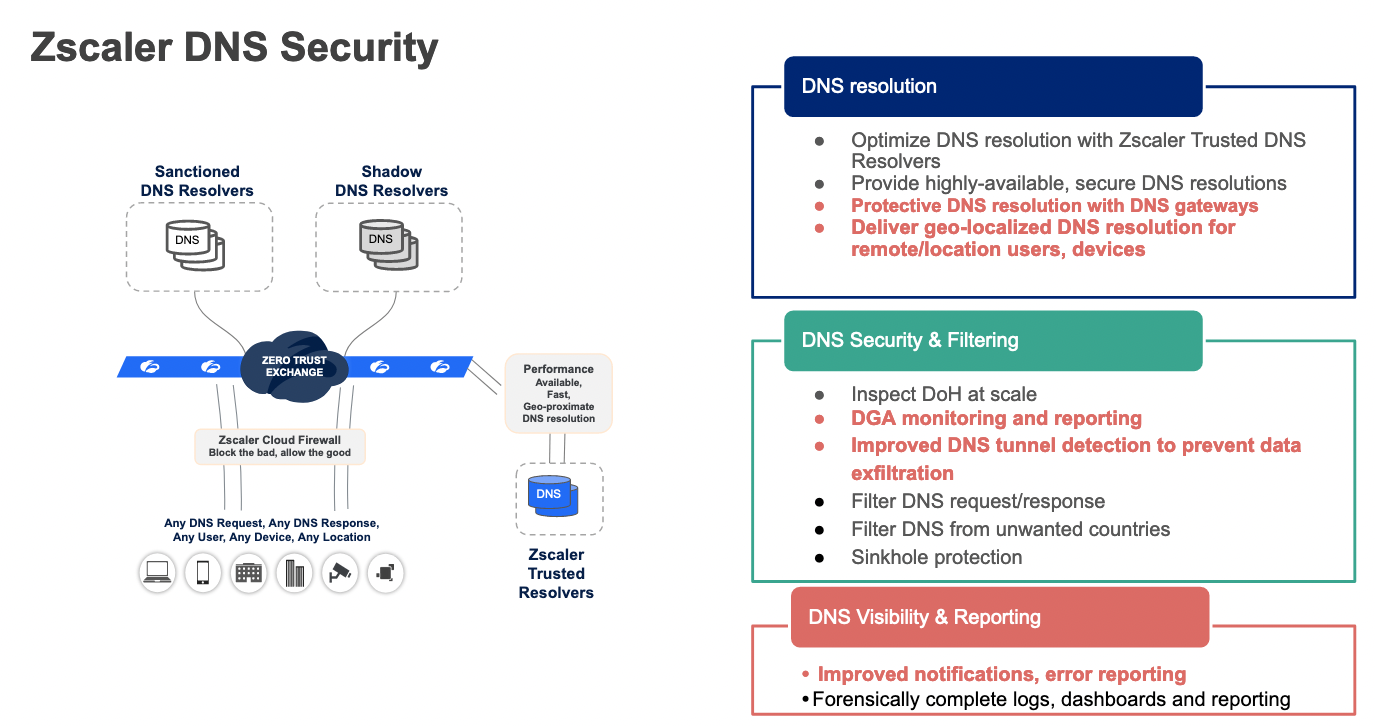
Figure 1: Zscaler DNS Security Overview
88% of companies suffer from DNS attacks
DNS is often referred to as the phone book of the internet. DNS’ job is to translate web addresses, which people use, into IP addresses, which machines use. But, DNS was not designed with security in mind. And even though companies have invested incredible amounts of money into their security stack, their DNS traffic often goes unmonitored.
This has only gotten worse with the adoption of encrypted DNS, known as DNS-over-HTTPS (DoH), which has grown annually since its introduction in late 2018. Organizations end up with little to no visibility over what’s happening with these DNS queries, and attackers can exploit that in various ways. IDC's 2022 Global DNS Threat Report revealed that 88% of organizations interviewed had suffered DNS-related attacks over the previous year, primarily phishing, malware, and DDoS attacks. 70% had experienced application downtime as a result.
Organizations need better DNS security. They need it with a cloud native solution that can scale to inspect both encrypted and unencrypted traffic, and they need it delivered with speed and performance regardless of where their users, devices, and applications are located around the world.
The latest in DNS protection and resolution
For years, Zscaler has been proud to partner with our customers to tackle this problem with a differentiated approach to DNS resolution and security. Zscaler is the only security vendor that combines optimal DNS resolution closest to the user with best-of-breed DNS filtering, security, horizontally scalable DoH inspection, and data exfiltration protection.
Below is a deep dive into the new features that further enhance all of these benefits:
DNS Gateway for better availability
Organizations handle DNS resolution in one of two ways: they either build their own DNS resolvers into their data centers, or they work with third-party providers. In 2016, cybercriminals used the Mirai botnet to wage a DDoS attack against a leading DNS provider, causing massive website and application outages. This made it clear that no one is immune to attacks, and highlighted the risk of relying exclusively on one DNS provider.
Zscaler’s DNS Gateway reduces this risk by providing automatic failover to secondary resolvers if the primary resolver fails.
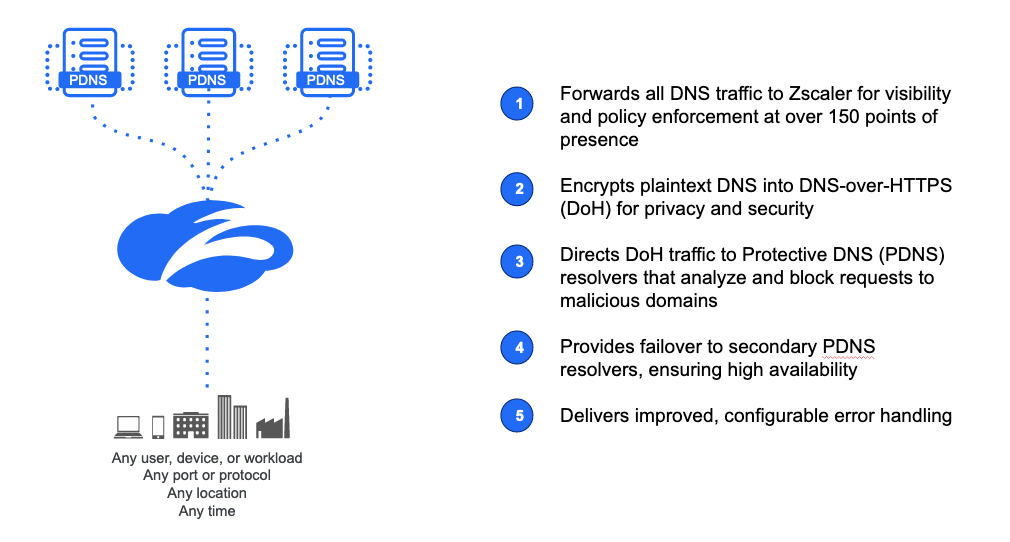
Figure 2: DNS Gateway features
Increased security (and PDNS compliance) with DoH translation
The DNS gateway also has the ability to translate plaintext DNS into DNS-over-HTTPS (DoH). This is a differentiated capability that ensures any traffic, regardless of source and destination, gets the privacy and security benefits of encryption.
For federal agencies, this feature may be of particular importance: DoH translation means that Zscaler can send all traffic to protective DNS (PDNS) resolvers. PDNS resolvers are government-sanctioned, security-focused DNS resolvers that are available (and in some cases mandated) to use by any US organization that has access to United States Department of Defense (DoD) information, as well as to a range of public services in the UK.
DNS tunneling and DGA detection
Some DNS-based attacks can be particularly difficult to stop. Luckily, Zscaler has the world’s largest inline security cloud, which processes 300 billion requests per day and stops over 8 billion threats. This tremendous amount of data not only means that a threat stopped for one customer immediately improves protections for customers everywhere, but it also feeds into our AI and machine learning models to detect new and evasive threats.
DNS tunneling
One of the most popular DNS threats is DNS tunneling, in which threat actors take advantage of the flexible nature of DNS queries to hide communications to command-and-control servers, download malware, or exfiltrate data. This is challenging to detect both due to the broad nature of DNS queries (a website can be called pretty much anything so a DNS query can be pretty much anything), and due to IT visibility gaps, particularly when it comes to encrypted traffic.
Zscaler’s machine learning algorithms uncover DNS tunneling by examining key data such as variations in the amount of data, the volume and distribution of domain and subdomain requests, and the reputation and co-occurrence of various domains and subdomains. If we discover malicious activity attempted anywhere, we immediately update our protections for all customers.
DGA detection
Attackers frequently use domain generation algorithms (DGA)—programs that can rapidly generate thousands of new domain names—to allow them to bypass DNS block lists.
Zscaler analyzes the domains and the traffic itself to detect and block attacks using DGA. These domains can also be blocked, isolated, or cautioned at the policy level using URL and/or DNS filtering categories for miscellaneous/unknown and newly registered domains. Finally, all files traversing the Zscaler Zero Trust Exchange undergo analysis by our advanced threat protection engine and inline sandbox in order to ensure that no malware makes it to the client.
Improved user experience with DNS ECS
Third-party DNS resolvers typically lack user context when a request comes via an intermediary. If a user in Argentina is connecting to a resolver in Brazil, the Brazilian resolver won’t know where the request is coming from, and may route the request to a content delivery network (CDN) that is far from the user, causing latency. Even worse – the user may receive web content in the wrong language and currency, i.e., Portuguese and Brazilian reals rather than Spanish and pesos.
With DNS ECS, third-party resolvers get the context that they need to improve this user experience. The resolvers deliver content using the closest CDN, and with the correct language and currency. This is fully optional and configurable subject to privacy requirements.
Error handling and reporting improvements
DNS Security gives admins superior visibility and control over their DNS traffic, irrespective of the protocol or the type of encryption used. This includes forensically complete logging, dashboarding, and the ability to define rules to control requests and responses. With this launch, organizations have even more flexible and granular control over error handling and even better reporting on both an ad-hoc and quarterly basis, with answers to questions such as:
- Who are the top DNS talkers?
- What DNS protocols are being used?
- What categories are my users hitting?
- Who are my top blocked users?
- What were the attempted DNS tunnel data exfiltrations?
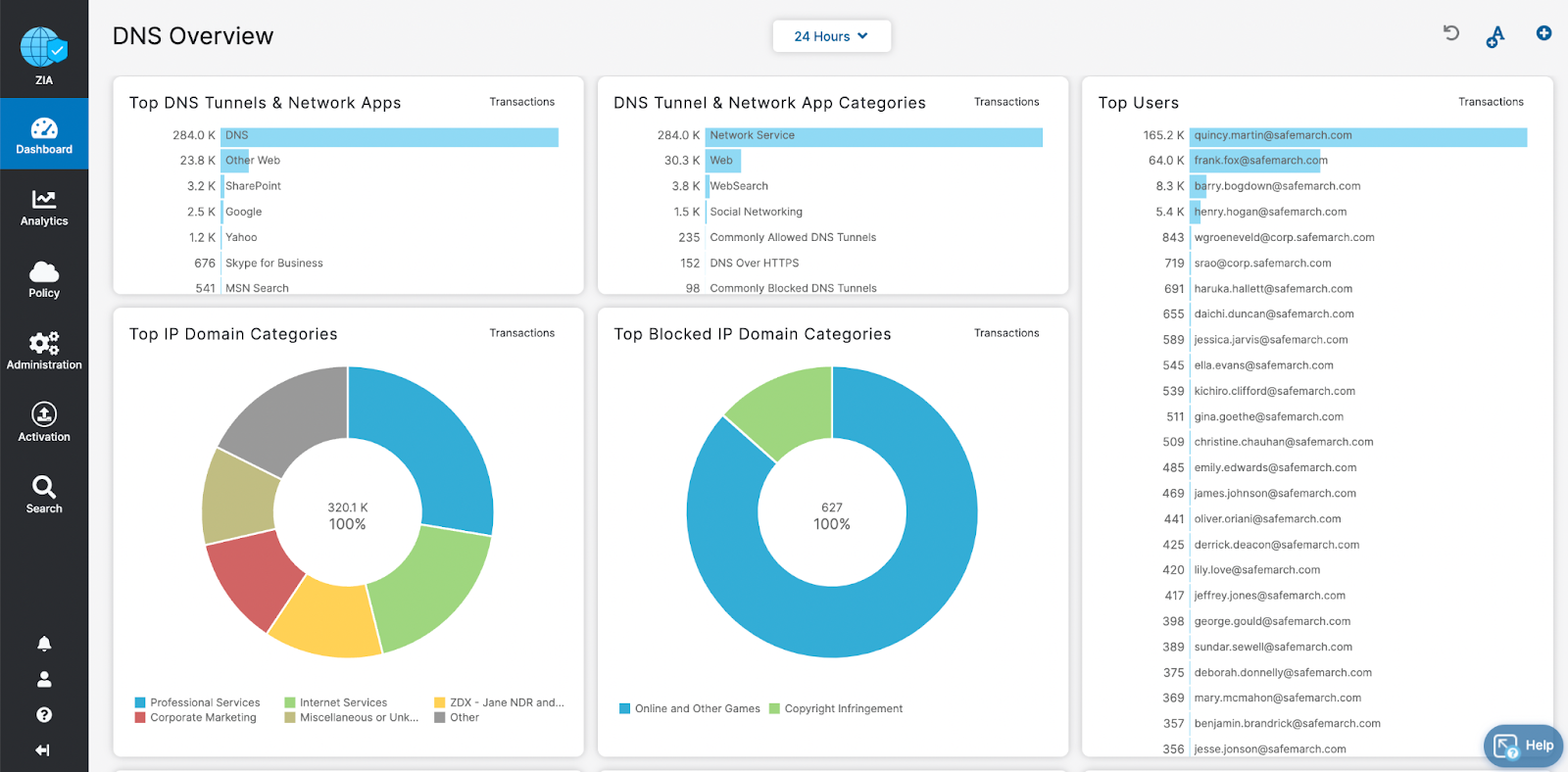
Figure 3: DNS Security reporting dashboard
Part of the world’s leading zero trust solution
DNS Security is just one of many capabilities of the Zscaler Zero Trust Exchange, which helps organizations reduce business risk while enabling and simplifying digital transformation. We consistently strive to provide better value, security, and performance across our platform, and are proud to offer these new benefits to our customers everywhere.
To learn more about DNS Security, visit our website.





