Based on a comment, I modified the title to be 66.220.17.200 versus DNSMADEEASY. Let me explain:
- DNSMADEEASY provides the resolution / name services for the domains in question
- Hurricane Electric / C2 Media provides the hosting / IP space (66.220.17.200)
- Tucows is the registrar for the registered domain names
Update 2:
Also, after I published the post, I checked and found that the hostname portion of the domain does not seem to matter / affect the ability to download the binary payload. For example,
hxxp://garbage.nb.host192-168-1-2.com/bins/int/9kgen_up.int
let's you download the binary (where "garbage" can be anything). It is likely that the hostname is used for tracking purposes to identify which sites / trojan packages are most successful. The listed fully-qualified domain names below are what was seen in the wild.
Post:
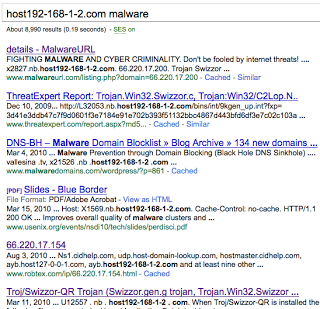
This may not be news for some of you, all it takes is a simple Google for something like host192-168-1-2.com malware. You’ll see a rich history of abuse from Trojan Swizzor ranging from 2009 to today:
host192-168-1-2.com is registered through Tucows and has resolution / name services provided through DNSMADEEASY. This robtex report shows the other related domains, each having a varying degree of abuse related to Swizzor:
adserver5.com
cidhelp.com
dns-look-up.com
host-domain-lookup.com
host127-0-0-1.com
host192-168-1-2.com
host255-255-255-0.com
lop.com
netbios-local.com
netbios-wait.com
range159-195.com
zone-media.com
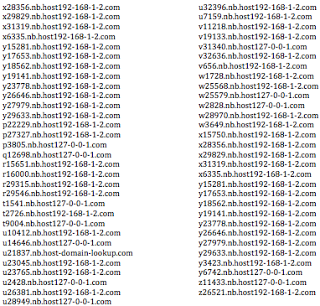
Below is a brief list of recent domains used to host Trojan Swizzor payloads. Note the domains used / listed here include: host127-0-0-1.com, host192-168-1-2.com, host-domain-lookup.com, and host255-255-255-0.com:
All resolve to the Hurricane Electric IP: 66.220.17.200
Note, the above active/live list we provide is much more extensive that what is listed on MalwareURL for example. The URL paths to the malware within the above domains include:
/bins/int/9kgen_up.int
/bins/int/upd_admn.int
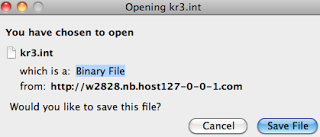
/bins/int/kr3.int
/bins/int/tp_map16.int
While they all have an "int" file extension, they are all PE32 executable files.
9kgen_up.int (Swizzor variant)
MD5: c79cd77012c848f93e0a8dfc28dee992
V/T (20/41)
upd_admn.int (Swizzor variant)
MD5: 43edfa7f55d4331ad2d3f5ca1bb4b999
V/T (22/42)
kr3.int (Swizzor variant)
MD5: ff7d4cbb6aa30bbf58d945e182700fb7
V/T (22/41)
tp_map16.int (Swizzor variant)
MD5: 599ebaed9e147ef8a0b6967dba2da040
V/T (24/42)
Swizzor is a Trojan that is typically installed via drive-by download or social engineering. It has the ability to interact with Internet Explorer through Browser Helper Objects (BHOs) to inject ads and to download/install other threats (for additional information see Microsoft's threat entry for Swizzor). In the particular variants that I downloaded, I saw C&C update activity to other related domains, e.g.,
hxxp://upd.host255-255-255-0.com/upd/check?version=0.1unk&fxp=614a69d6edf1b0f55a0a07bfd613edb3cceeefa1b7223878206dc7870f0307bf6e496e69
IP: 66.220.17.200
hxxp://ayb.host127-0-0-1.com/abt?udata=WWW_9WWW:5.60www:%20140445784:United%20States:program_started:1cb20aef0c84a243
IP: 66.220.17.154
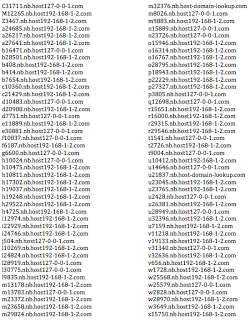
I’m in the process of sending something along to Hurricane Electric / Tucows/ DNSMADEEASY now, but you may want to check the logs in your environment for systems connecting to the mentioned domains. Here's a continuation of the above list of recent Swizzor domains: