A Google search for "Dad walks in on Daughter.. EMBARRASSING!" shows hundreds of spam pages. They are mostly new domains, set up just for the purpose of scamming users.
 |
| Google search shows spam pages |
Some of the domains identified are:
- the-ping.org
- t401.org
- ectoplax.info
- 20yearstimephoto.info
- 20yearsphoto.info
- apps.facebook.com/cooljoysole/
- apps.facebook.com/dadwalksin/
- apps.facebook.com/fgdfhgdfgdf/
- www.facebook.com/pages/Dad-walks-in-on-Daughter-Embarrassing/217239648303953
Besides being wide spread, this spam is interesting because it shows the wide variety of scams and spam associated with Facebook. Here are a few.
Like-Jacking
A very common technique used with Facebook spam involves likejacking. The spammer entices users to click on a link or image, often on the premise of watching a funny video. However, the page contains a hidden Like button that is unknowingly triggered by the user. The Like button is placed in a hidden iFrame or hidden DIV tag that follows the mouse.
This technique is used to spread the spam page via Facebook profiles to get more users to visit the page. This likejacking technique can be found, for example, on gadgetera.net or t401.org.
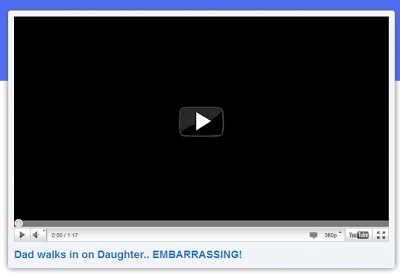 |
| Fake video layer hiding a Like button |
On these pages, the likejacking technique used is somewhat unique: 23 Like Buttons are placed in the center of the video, below what looks like the play button. The opacity is set to 0, meaning these buttons are totally transparent and cannot be seen. When a user believes he is clicking on the play button, he is actually clicking on one of the like buttons.
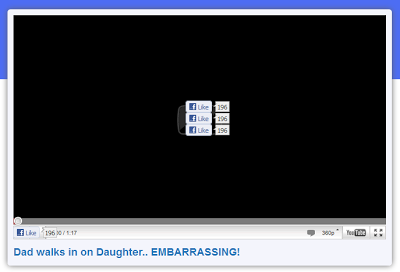 |
| Like buttons rendered visible |
You can check the details in this video:
Script injection
This second example is much more harmful. The attackers ask users to copy and paste Javascript code into their Browser URL bar. The Javavascript has full access to contents in the open browser tab. It can grab the user session cookie and send it to the attacker. This gives the attacker full access to and control of your Facebook account.
 |
| Script injection |
These types of script injection used to be done through cross-site scripting (XSS), or other vulnerabilities. Now unfortunately, attackers are finding that they can bypass security protections as users are willing to do anything, including willingly executing malicious code!
Comment-Jacking
Instead of using a Like button to spread a page, spammers can also use comments. On hxxp://kingsoz.org/, the user is asked to enter a captcha to access the video. The result is actually entered into a Facebook comment box (you can see the "comment" button).
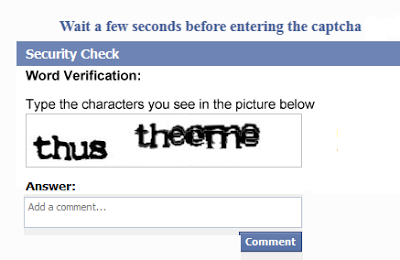 |
| User asked for a Captcha |
 |
| Spam link on my user profile after visiting hxxp://kingsoz.org/ |
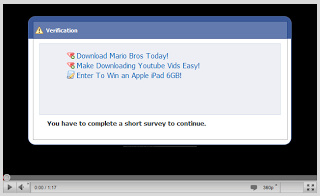
Survey, Software Installation
Getting the spam page hosted in a victim's Facebook profile is only the first step for a scammer. Ultimately, they want to make a few bucks from each visitor. A common technique used involves asking visitors to fill out a survey, install software, or to click on advertising to verify that they are in fact a human and not an automated script. The spammers get paid for each action.
After getting 5 spam pages added to my profile, filling out 3 surveys and getting my Facebook account stolen, I was still not able to watch this video :-)
-- Julien