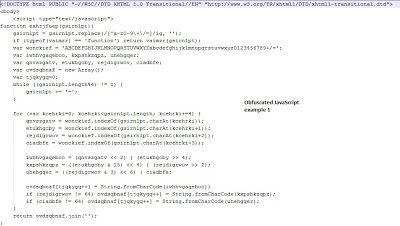
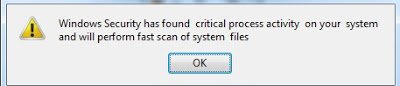
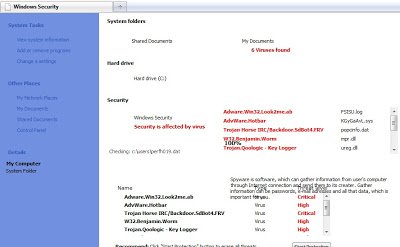
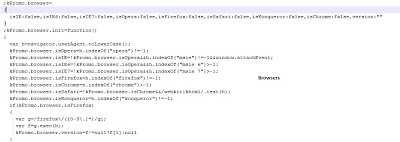
 Looking at the above images, you can see that the structure of code remains the same and only the variable names are randomized. Even the source of the page contains only a body tag and the malicious JavaScript. When this page loads, it starts creating animations that deliver security warnings to scare the victim. Here is one example:
Looking at the above images, you can see that the structure of code remains the same and only the variable names are randomized. Even the source of the page contains only a body tag and the malicious JavaScript. When this page loads, it starts creating animations that deliver security warnings to scare the victim. Here is one example:
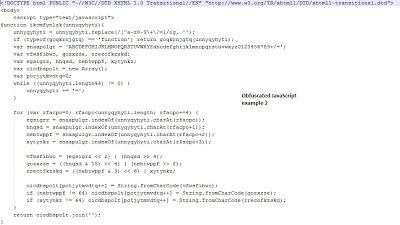
 As I mentioned in the earlier blog post, these are fake security attempting to coerce the victim into downloading fake antivirus software that will download additional malware onto the system. The code for doing these animations and initiating the download of malicious binaries is hidden inside the malicious script. Let’s decode the main script. The malicious JavaScript code has two functions defined and three lines of code to decode the content. Here is how they look:
As I mentioned in the earlier blog post, these are fake security attempting to coerce the victim into downloading fake antivirus software that will download additional malware onto the system. The code for doing these animations and initiating the download of malicious binaries is hidden inside the malicious script. Let’s decode the main script. The malicious JavaScript code has two functions defined and three lines of code to decode the content. Here is how they look:
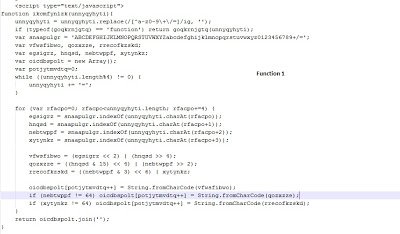
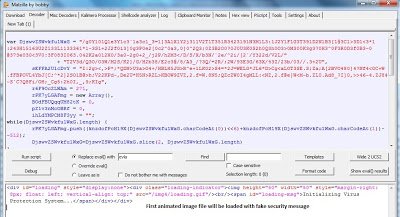
 The variable “euqbvulz” is passed in the first iteration to the decoding function “ikcmfynlzk()”. The decoded content is then stored in a variable called “wfuaydtmd”. The “wfuaydtmd” variable is again passed to in a second iteration to a second function called “fiyctdv()” with a “document.write()” function call. So the code will go through two iterations of the decoding. Let’s decode this code using Malzilla.
The variable “euqbvulz” is passed in the first iteration to the decoding function “ikcmfynlzk()”. The decoded content is then stored in a variable called “wfuaydtmd”. The “wfuaydtmd” variable is again passed to in a second iteration to a second function called “fiyctdv()” with a “document.write()” function call. So the code will go through two iterations of the decoding. Let’s decode this code using Malzilla.
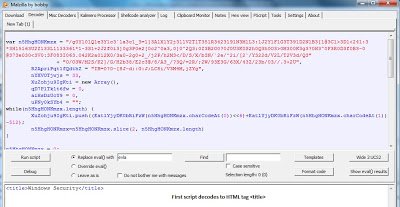
Malzilla successfully decoded the contents. But the decoded results contain another three heavily obfuscated JavaScript snippets and some HTML code. Let’s decode them one by one. Here is first one:
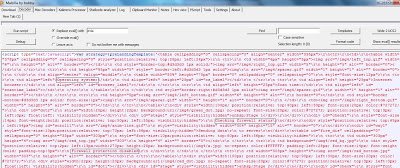
The first malicious JavaScript snippet decodes to the HTML “title” tag, which will be displayed as the title of the webpage, claiming it is a legitimate Windows security website. This means the HTML code displaying warnings and animation is hidden in the remaining malicious scripts. Here is second one:
The above script code will load the animated images with message “Initializing virus Protection System…”. Here is the third one:
If you look at the above image, you will notice some strings related to security, which suggests that this JavaScript code actually loads the animation. The first variable is declared as “strategy” so the strategy used by the attacker is to load the variable with JavaScript code in a CSS format. Here are some of the screenshots of that CSS code:
 So, the code displaying the security warnings and messages are obfuscated multiple times by the attacker. You will notice the strings used by the attacker are displayed in warning images mentioned in the first few images. Due to the heavy obfuscation used, the detection rate remains very poor for legitimate antivirus vendors when scanning this HTML file.
So, the code displaying the security warnings and messages are obfuscated multiple times by the attacker. You will notice the strings used by the attacker are displayed in warning images mentioned in the first few images. Due to the heavy obfuscation used, the detection rate remains very poor for legitimate antivirus vendors when scanning this HTML file.
Umesh