I posted a few of these mal-spam incidents on our Scrapbook blog ... this sort of mal-spam has been on-going, but there has been a recent uptick since early June. The NACHA, Federal Reserve, and now IRS mal-spam sites have all favored the MelbourneIT/Yahoo netblocks/domain services.
I posted a few of these mal-spam incidents on our Scrapbook blog ... this sort of mal-spam has been on-going, but there has been a recent uptick since early June. The NACHA, Federal Reserve, and now IRS mal-spam sites have all favored the MelbourneIT/Yahoo netblocks/domain services.
This is one of those cases of using Uncle-Sam, which relates to any US citizen, for social engineering spam recipients into falling victim to an attack.
Recently the straight up spam-to-malicious URL exe scenario changed to a more complex multi-stage, multi-pronged attack scenario: spam to URL shortener which redirects to another URL shortener and/or site containing an exploit kit (Blackhole) and drop or social network to malicious Zeus-ish malicious executable to sites like:
hxxp:// irs-report.com/TAX6538001.pdf.exe
Fortunately, the IRS and security researchers alike were all over this to have these sites removed as quickly as possible. Regardless the spam was widespread through the
Cutwail/Pushdo botnet and impacted a lot of Internet users. Here are a few of the details (posted with permission from co-handler of this incident)...
Here is an example of one of the shorteners:
hxxp://shortn.me/iACt
Here is an example of one of the second-stage shorteners:
hxxp://ur.ly/MJu0
All-in-all a handful of shortener services were abused for this campaign to the tune of thousands of shortened URLs (perhaps a different shortened URL per spam message to avoid detection from groups like
SURBL). Some of the services abused include: 3cm.kz, bizz.cc, linkzip.net, omf.gd, ptiturl.com, tiny.tw, 0845.com as well as the previously mentioned shortn.me and ur.ly services.
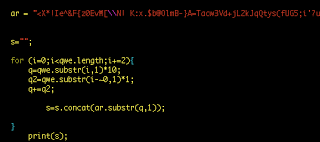
From my example, the second-stage shortener linked to content that was pretty well obfuscated ... it "abused" JavaScript (such that my command-line interpreter, CLI, couldn't render) and it also did the standard leveraging of HTML DOM objects: specifically through, getElementsByTagName, innerHTML, as well as some creative uses of document creation with createTextNode, appendChild, and related. Because of these, it made the second-stage redirect a bit challenging to deobfuscate ... in the end, it helped to modify the script to suite what my CLI JS could understand. All of the obfuscated content was numbers within HTML div tags that was looped through with this (modified) JS:
Deobfuscating the content, returns the exploit scripts as well as redirects to the previously mentioned irs-report site.
Example drop:
MD5 : 8a5bf0dd71a1b8ea8155963b252e2105
V/T
report: 13/42 now (seen
Remember the IRS does not contact the taxpayer through email! (
reference)
 I posted a few of these mal-spam incidents on our Scrapbook blog ... this sort of mal-spam has been on-going, but there has been a recent uptick since early June. The NACHA, Federal Reserve, and now IRS mal-spam sites have all favored the MelbourneIT/Yahoo netblocks/domain services.
I posted a few of these mal-spam incidents on our Scrapbook blog ... this sort of mal-spam has been on-going, but there has been a recent uptick since early June. The NACHA, Federal Reserve, and now IRS mal-spam sites have all favored the MelbourneIT/Yahoo netblocks/domain services.