There are numerous tools available to help individuals create new, exciting webpages. And, there seem to be just as many hackers looking to exploit these tools for their own gain.
Recently, the Zscaler ThreatLabz Team came across various phishing campaigns that leverage the StackBlitz tool, using the preboot library functionality that helps ease the transition of the hosted webpage immediately from the server side to the client side.
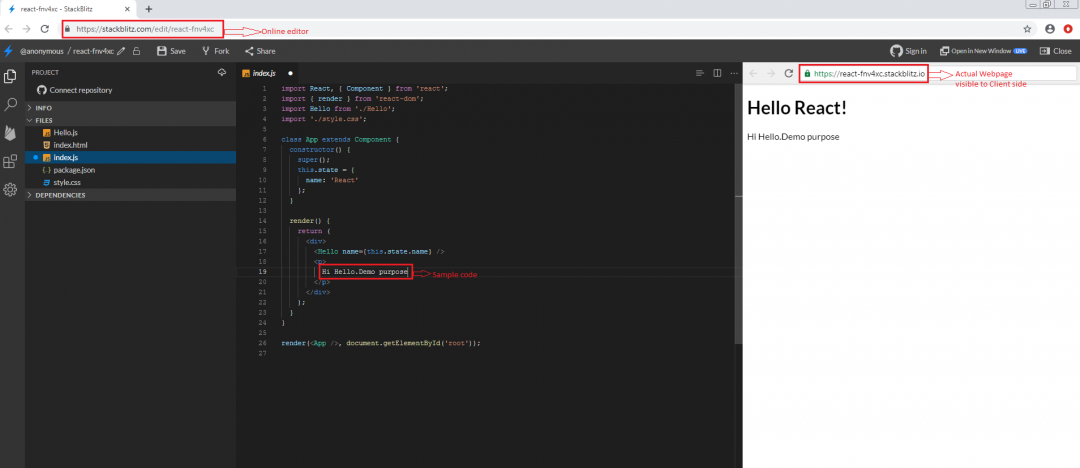
StackBlitz is an online integrated development environment (IDE) where anyone can create Angular JavaScript and React TypeScript projects that are immediately posted online. Attackers have targeted this method to host phishing pages. The purpose of the preboot library function is to help manage the transition of state from a server-generated web view to a client-generated web view.
Figure 1 shows the working flow of the StackBlitz tool.
Figure 1: A demonstration workflow of the StackBlitz tool.
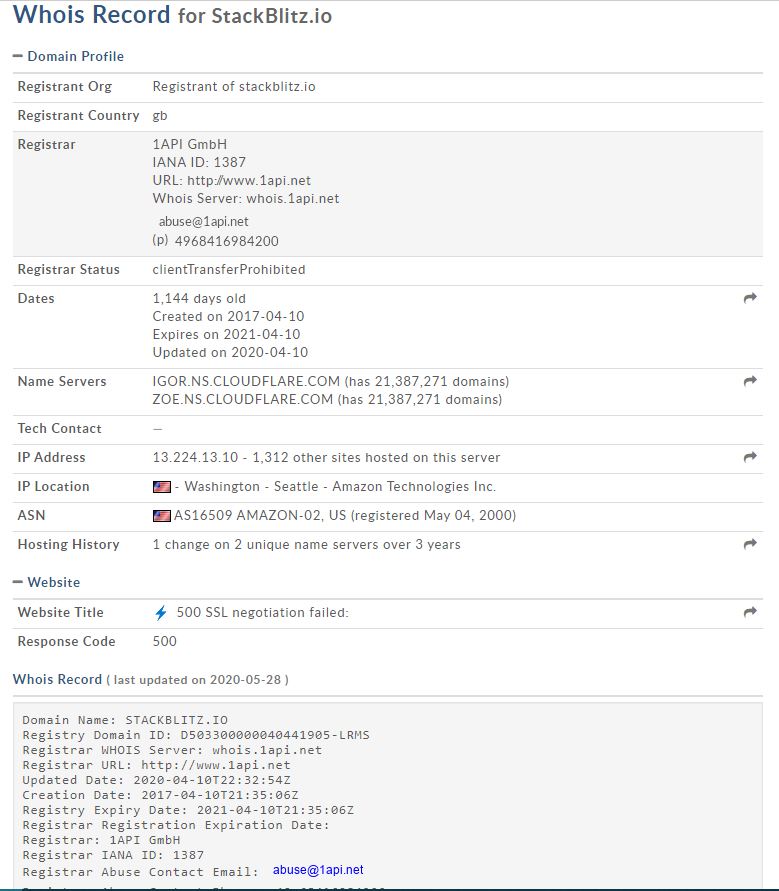
Figure 2: This is the Whois lookup info for the domain StackBlitz.io.
In this blog, we will describe the phishing attacks hosted using the StackBlitz tool and its delivery vector in detail. We found these phishing URLs through our Threat Intelligence collection framework as well as online submissions to ThreatLabZ team for review.
Spam method 1
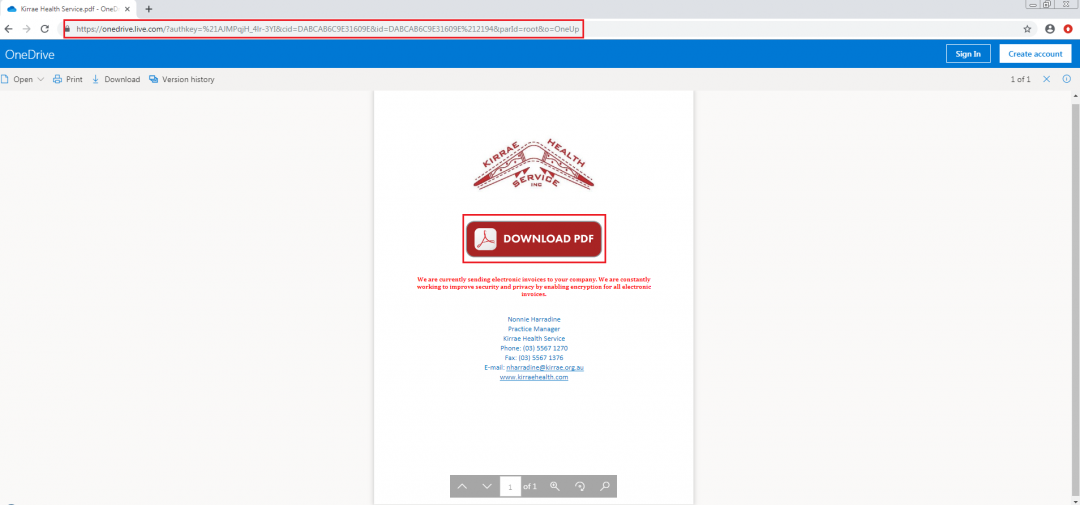
In this case, the spam link will be delivered via Microsoft’s OneDrive shareware service, pretending to be a document shared by a particular health organization.
Once the user clicks the download link, it redirects the user to the Outlook phishing page.
Figure 3: The spam campaign with the phishing link.
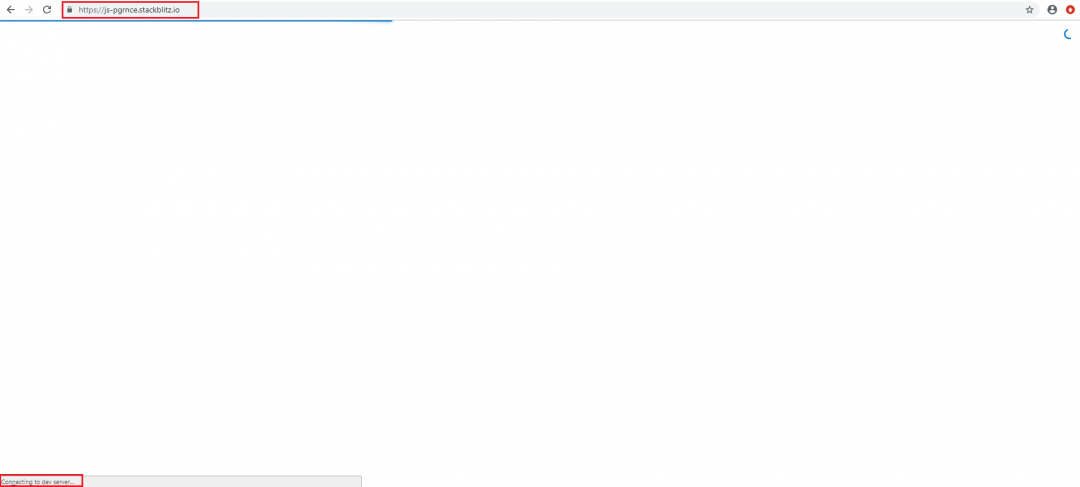
Figure 4 shows the page after the user clicks on the download button. It takes a little bit of time to fetch the web page from the StackBlitz development server.
Figure 4: Fetching data from the dev server.
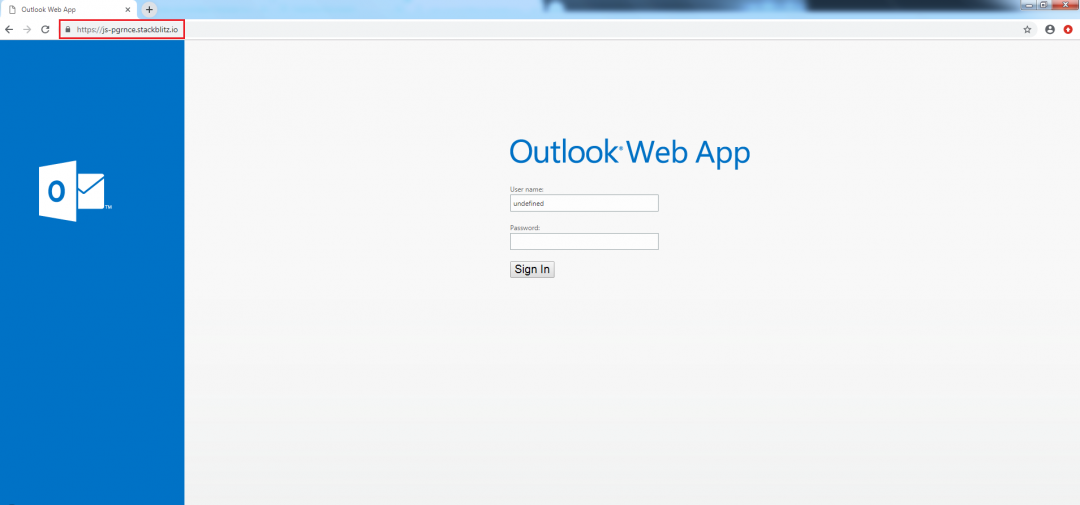
Finally, it lands to the Outlook phishing campaign, as shown in Figure 5.
Figure 5: The Outlook login phishing page.
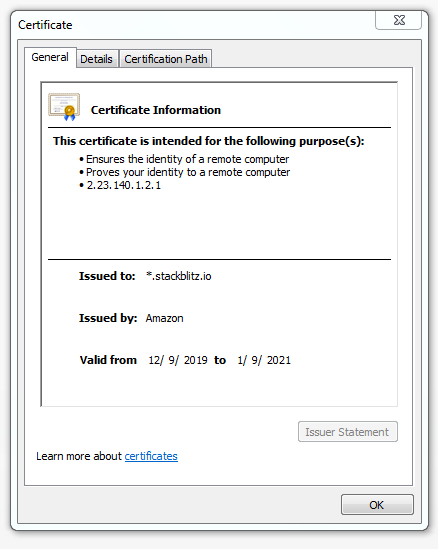
The SSL certificate of the hosted domain is shown in Figure 6.
Figure 6: Wildcard SSL certificate applies to all subdomains
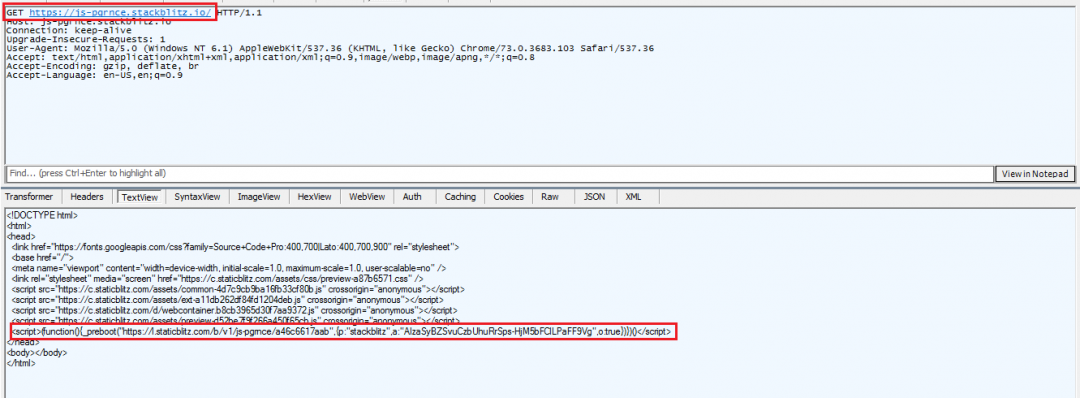
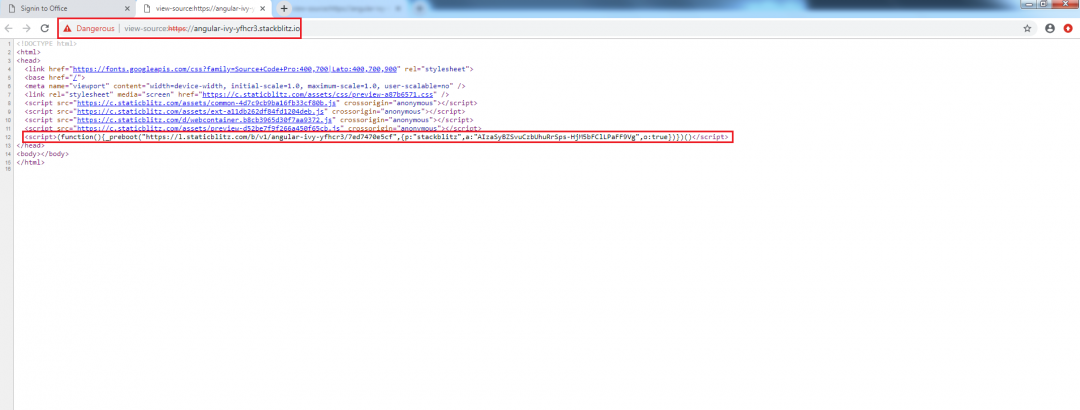
Figure 7 shows the source code of the hosted phishing page with the preboot library functionality. As mentioned earlier, this library manages the user experience from the time when a server view is visible until the client view takes over control of the page.
Figure 7: The source code of the Outlook phishing page.
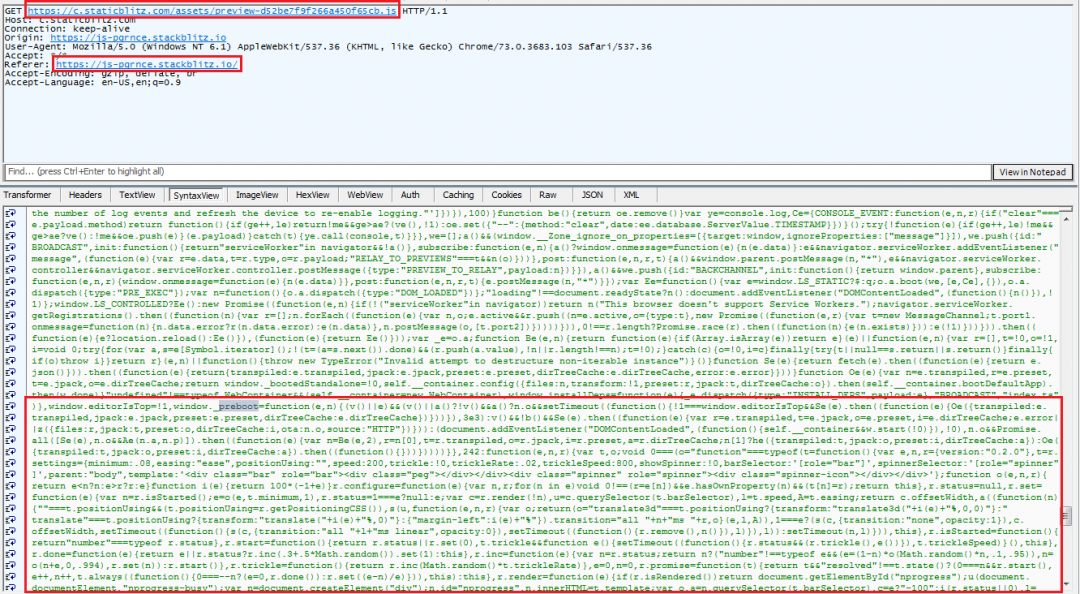
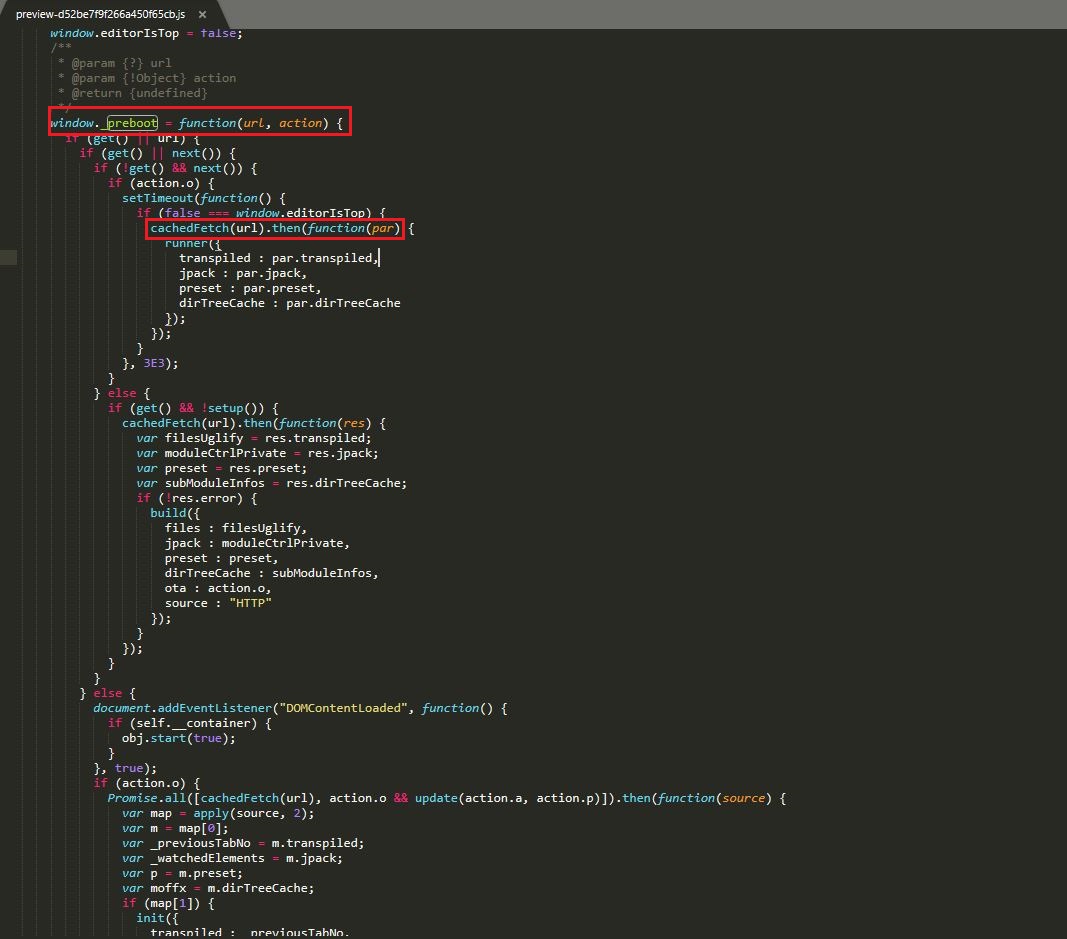
The function will be invoked from the (preview-d52be7f9f266a450f65cb.js) JavaScript. Figure 8 shows the source code of the preview JavaScript.
Figure: 8: The (preview-d52be7f9f266a450f65cb) script invokes the preboot function.
While analyzing the preboot function, we also identified that the preboot library functionality uses the CachedFetch() module to check if a cached copy of the page is available or not.
Figure 9: The preboot functionality with CachedFetch().
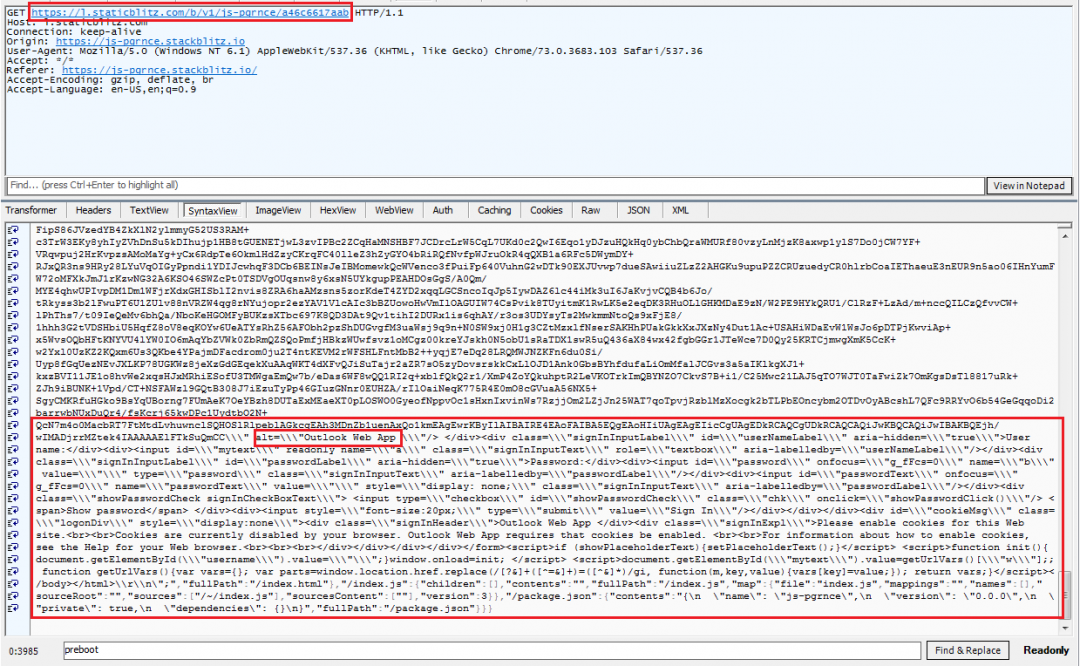
The preboot function returns the hosted webpage as a JSON file as shown in Figure 10.
Figure 10: The original source code of the hosted webpage in JSON format.
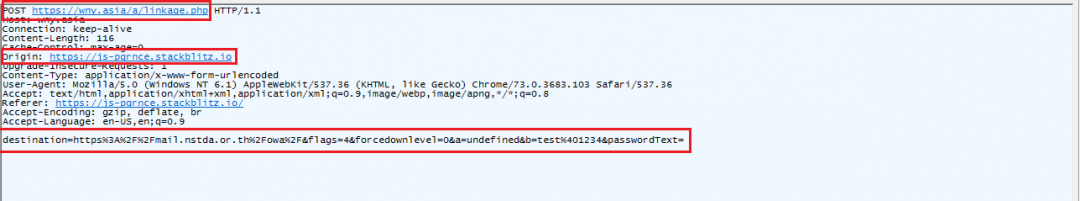
Figure 11: The post-infection web traffic that is sent to the cybercriminals.
Figure 12: Fiddler capture of the Outlook phishing campaign.
Spam method 2:
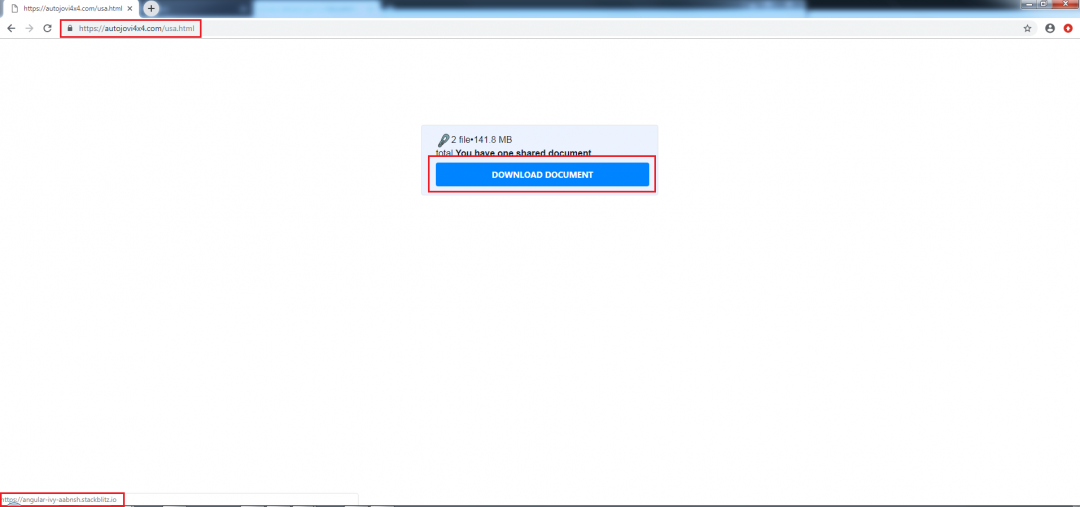
In this case, the spam link will host a web page with a message stating that you received a shared document with the associated document download link. Once the user clicks the download link, it redirects them to the OneDrive phishing campaign.
Figure 13: The spam campaign with phishing link.
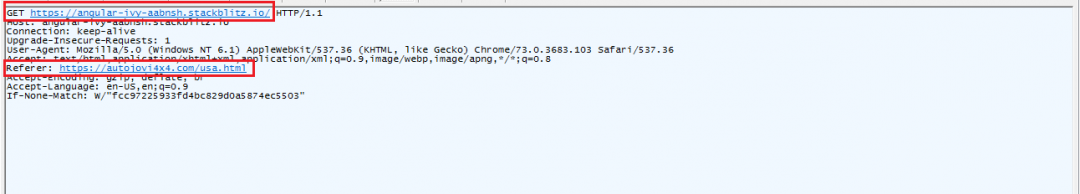
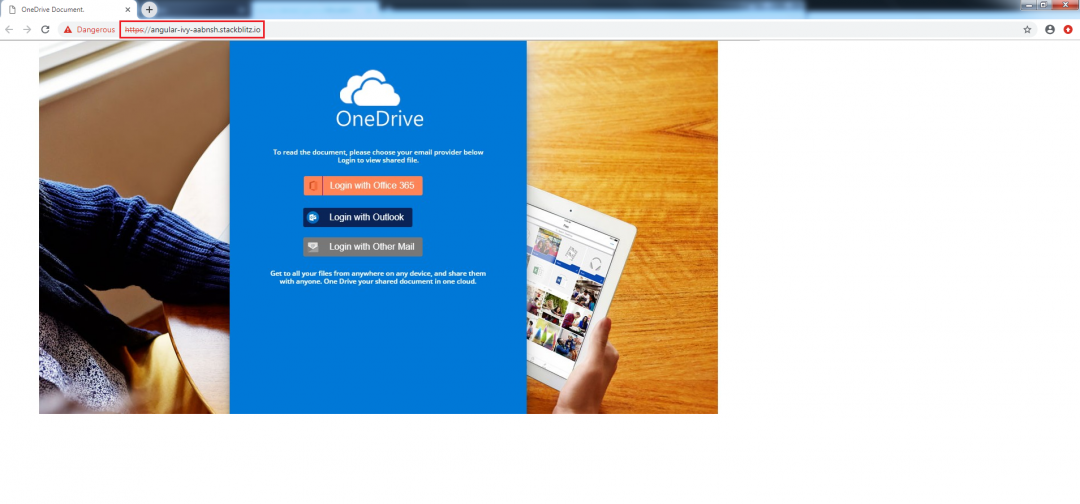
If the user clicks the download document button, it will redirect the user to the OneDrive login phishing page (angular-ivy-aabnsh(.)stackblitz(.)io).
Figure 14: The redirection traffic of the spam link.
Figure 15: The OneDrive login page for the phishing campaign.
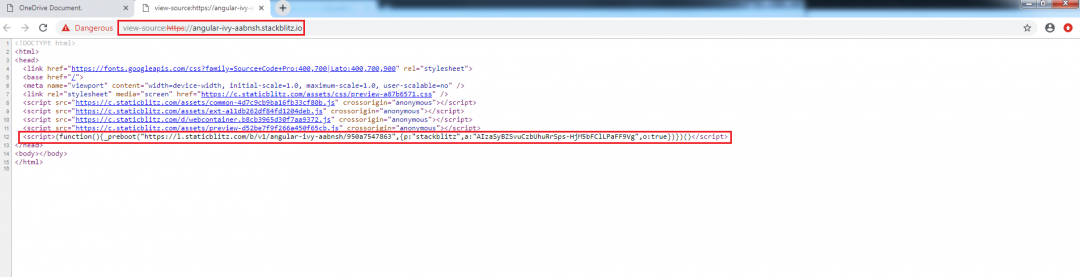
Figure 16 shows the source code of the hosted phishing campaign with the preboot library functionality.
Figure 16: The source code of the hosted phishing page.
If the user unknowingly clicks any of the phishing login methods to view the document, it will redirect the user to relevant phishing page.
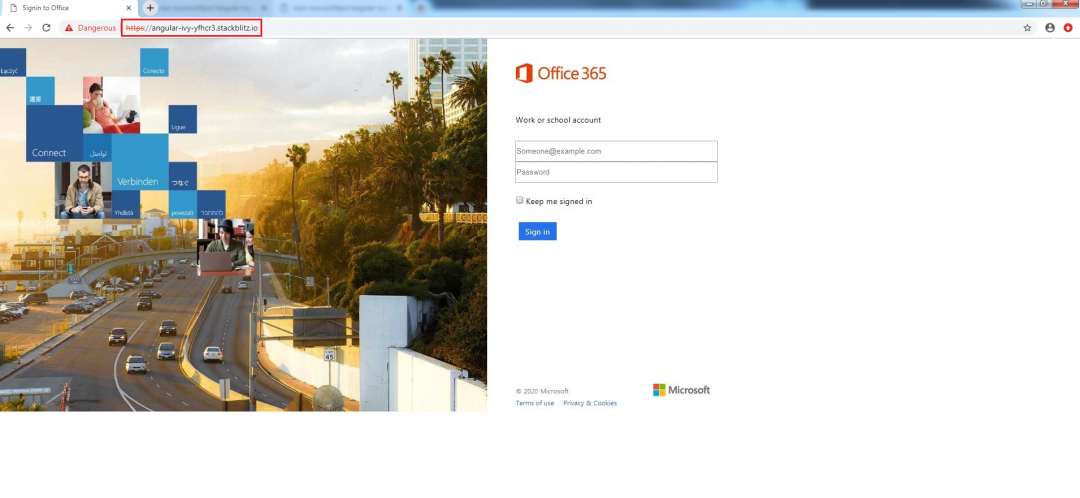
Here, we clicked on the Office365 login method to view the document, which redirected us to a webpage that looks exactly like a legit Office365 site.
Figure 17: The Office365 login phishing campaign.
As we mentioned earlier, the source code of the webpage will be common to all the websites hosted using the StackBlitz tool, except for the URL link, which is passed as parameter for the preboot function.
Figure 18: The source code of the Office365 login phishing page.
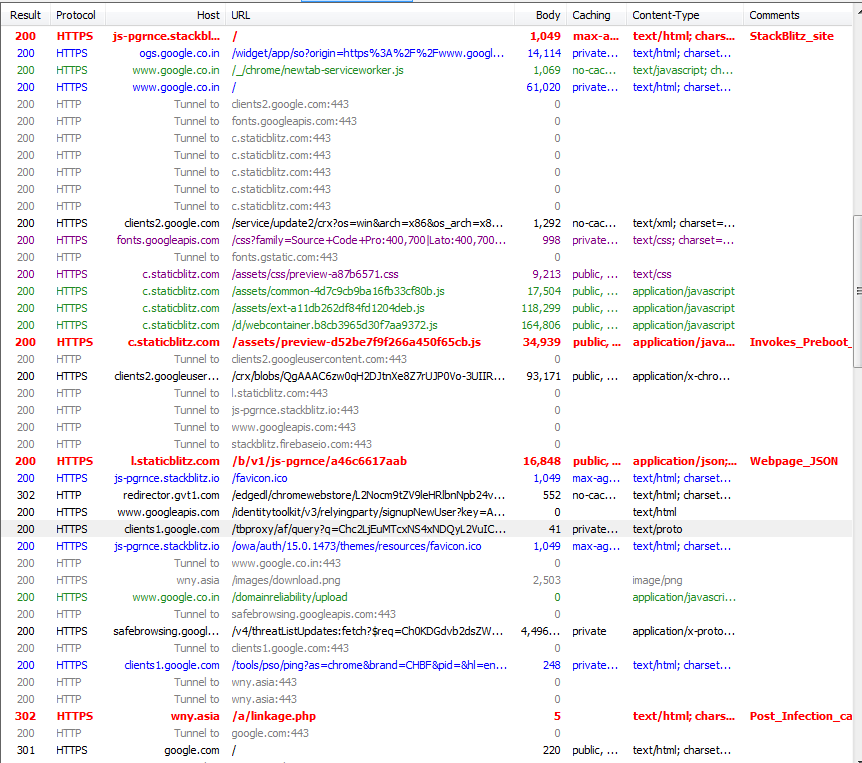
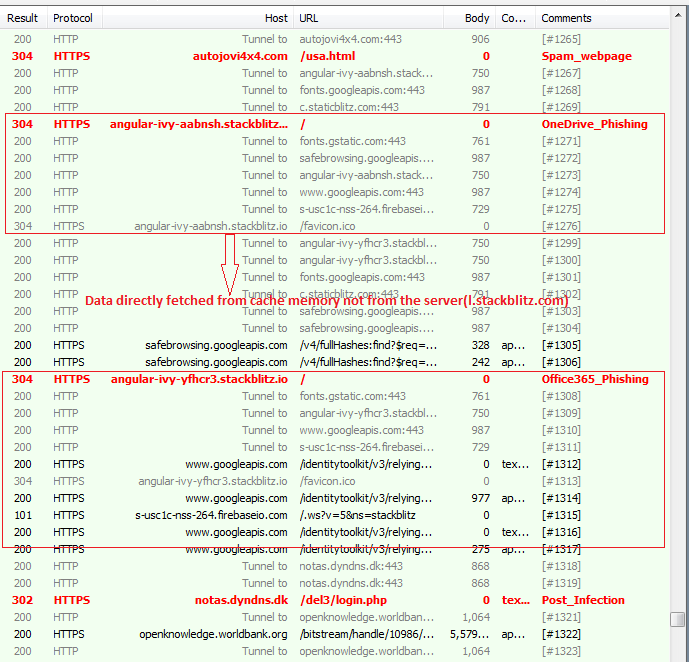
Here, we have accessed the hosted phishing campaign a second time to showcase the working functionality of the CachedFetch() and observe the overall web traffic.
Figure 19: The overall traffic of the phishing campaign captured in the Fiddler tool.
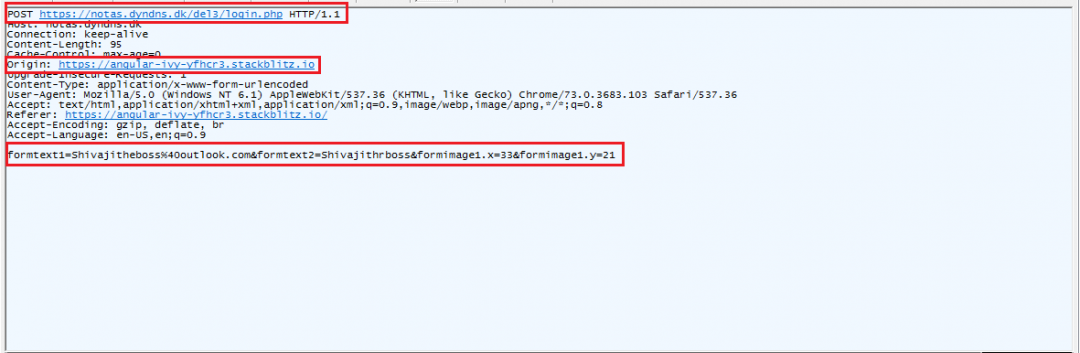
Once the login information has been entered by the user, the form will post the user’s credential details to malicious sites that are operated by the cybercriminals.
Figure 20: The post-infection web traffic.
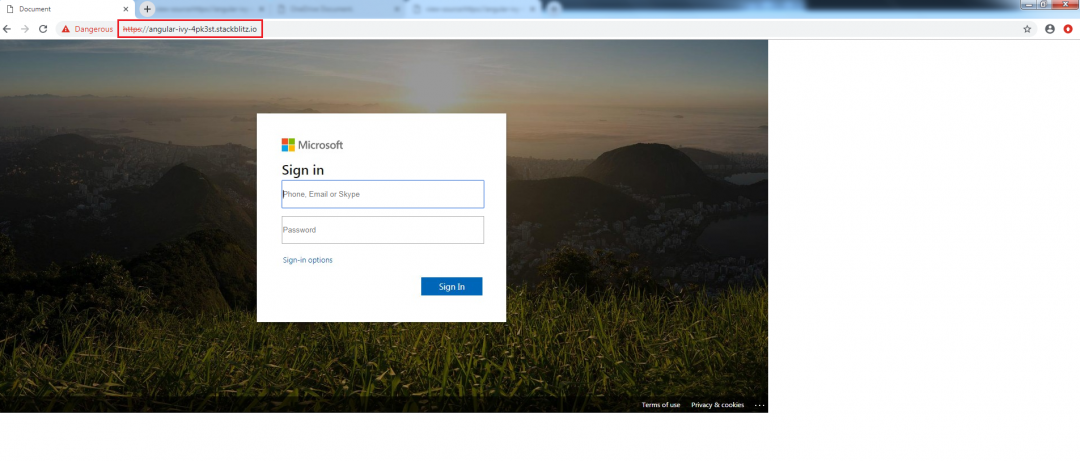
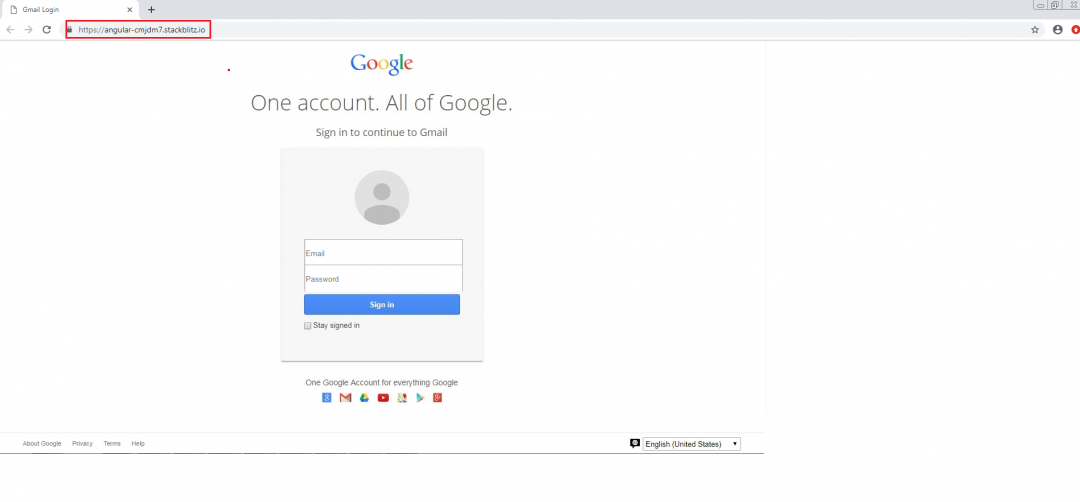
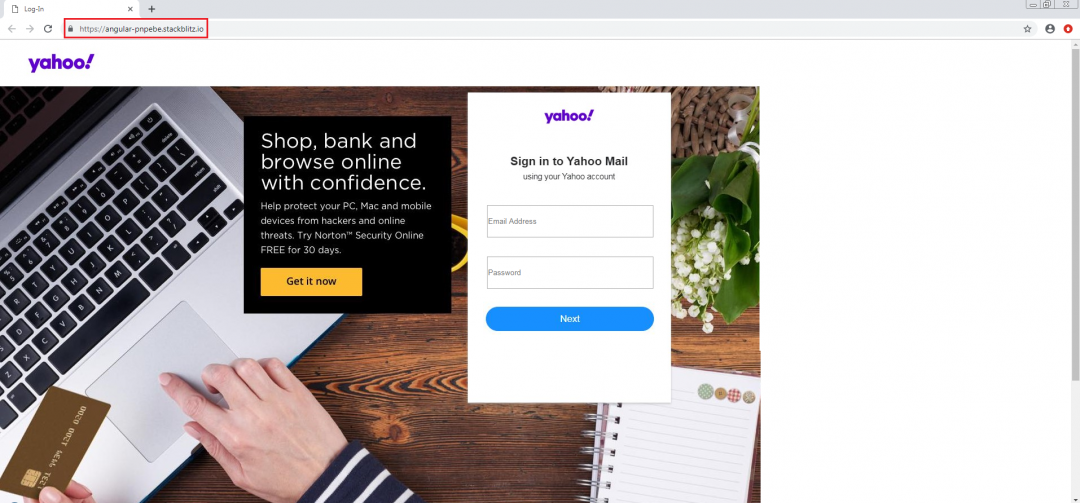
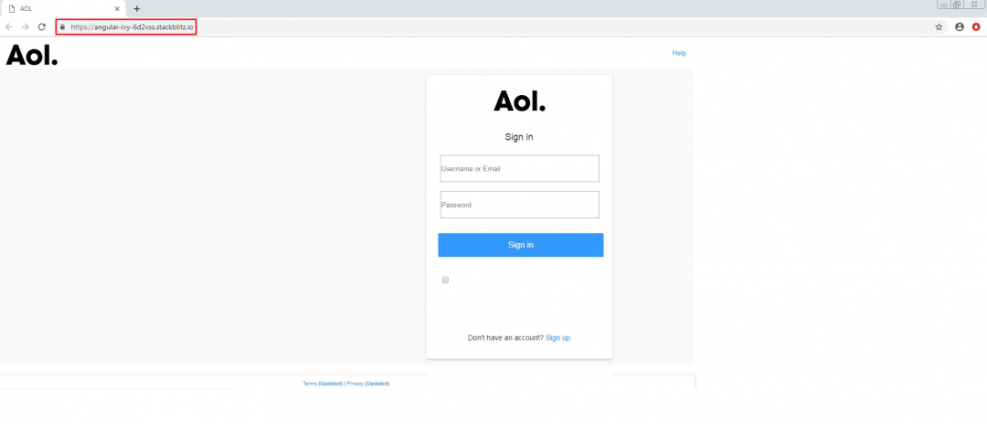
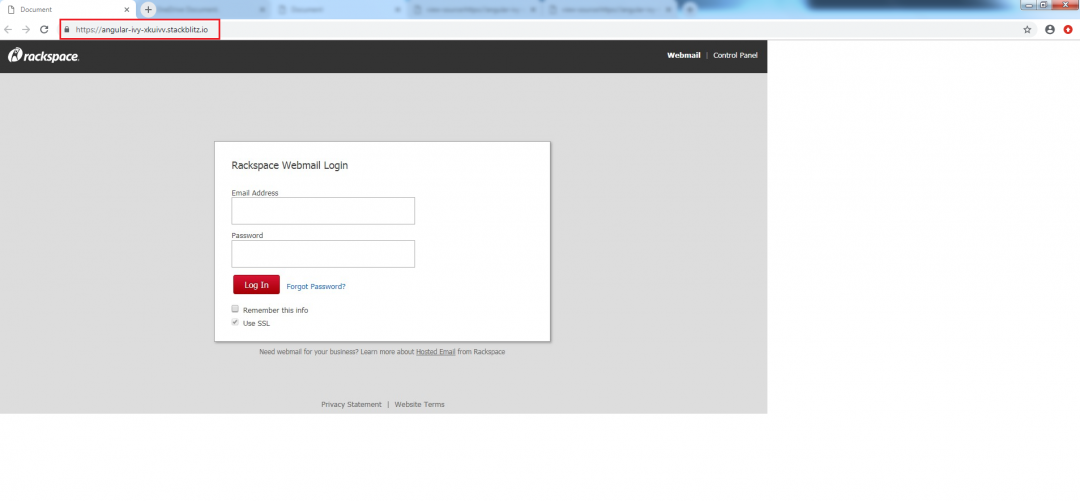
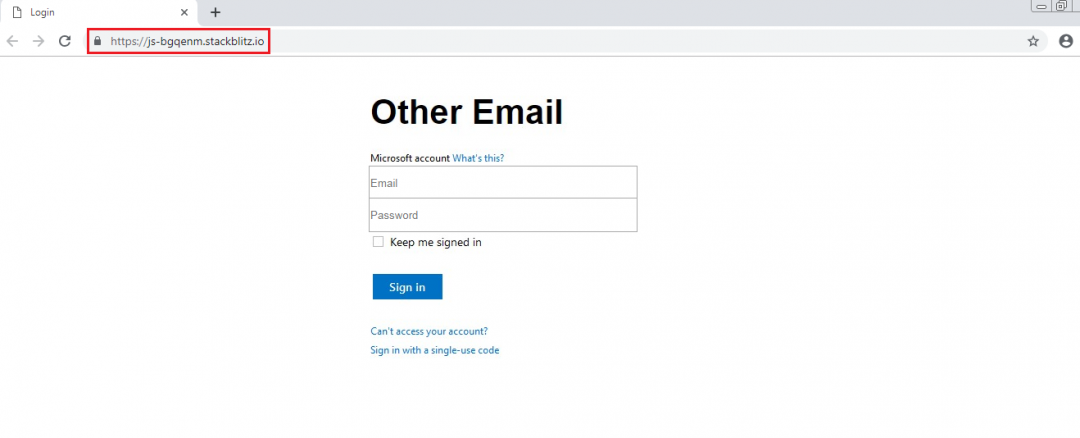
Figure 21-26 shows different phishing pages that are hosted using the StackBlitz tool (StackBlitz.io).
Figure 21: The Microsoft login phishing campaign.
Figure 22: The Gmail login phishing campaign.
Figure 23: The Yahoo login phishing campaign.
Figure 24: The AOL login phishing campaign.
Figure 25: The Rackspace login phishing campaign.
Figure 26: The Other Email login phishing campaign.
Conclusion
Cybercriminals use tools, such as StackBlitz, to come up with smarter ways to start phishing campaigns and make it harder for security vendors to detect such campaigns. The Zscaler ThreatLabZ team is actively tracking these kinds of phishing attacks to ensure coverage for and to keep our customer safe.
IOC:
Spam 1
js-pgrnce(.)stackblitz(.)io
wny(.)asia/a/linkage(.)php
Spam 2
autojovi4x4(.)com/usa(.)html
angular-ivy-aabnsh(.)stackblitz(.)io
angular-ivy-yfhcr3(.)stackblitz(.)io
notas(.)dyndns(.)dk/del3/login(.)php
Other phishing domains observed:
1nxbcc-hedxe8(.)stackblitz(.)io
2podk-ff4mtn(.)stackblitz(.)io
6eyyd-zjrnne(.)stackblitz(.)io
7djnd-jzc89e(.)stackblitz(.)io
angualar-ivy-aabnsh(.)stackblitz(.)io
angula-ivy-epksfd(.)stackblitz(.)io
angular-4ulsja(.)stackblitz(.)io
angular-4vjbos(.)stackblitz(.)io
angular-9gejbd(.)stackblitz(.)io
angular-c8ebxa(.)stackblitz(.)io
angular-e9ebhj(.)stackblitz(.)io
angular-e9hqf9(.)stackblitz(.)io
angular-emu4e4(.)stackblitz(.)io
angular-exrste(.)stackblitz(.)io
angular-f6xehy(.)stackblitz(.)io
angular-ivy-1tsaka(.)stackblitz(.)io
angular-ivy-2nghsv(.)stackblitz(.)io
angular-ivy-3etd9y(.)stackblitz(.)io
angular-ivy-4pk3st(.)stackblitz(.)io
angular-ivy-62mfgk(.)stackblitz(.)io
angular-ivy-8vrqfq(.)stackblitz(.)io
angular-ivy-aabnsh(.)stackblitz(.)io
angular-ivy-ayzk51(.)stackblitz(.)io
angular-ivy-bkvyy7(.)stackblitz(.)io
angular-ivy-c8ebrc(.)stackblitz(.)io
angular-ivy-d55uqm(.)stackblitz(.)io
angular-ivy-dug3fr(.)stackblitz(.)io
angular-ivy-epksfd(.)stackblitz(.)io
angular-ivy-feppa5(.)stackblitz(.)io
angular-ivy-ikp1nd(.)stackblitz(.)io
angular-ivy-jtatnb(.)stackblitz(.)io
angular-ivy-jxxbb8(.)stackblitz(.)io
angular-ivy-kxyakr(.)stackblitz(.)io
angular-ivy-rsphh3(.)stackblitz(.)io
angular-ivy-rv7qqo(.)stackblitz(.)io
angular-ivy-tphvml(.)stackblitz(.)io
angular-ivy-uvhyey(.)stackblitz(.)io
angular-ivy-wwnxei(.)stackblitz(.)io
angular-ivy-xkuivv(.)stackblitz(.)io
angular-ivy-yfhcr3(.)stackblitz(.)io
angular-ivy-zbaxnt(.)stackblitz(.)io
angular-ivy-zff34d(.)stackblitz(.)io
angular-jwnijt(.)stackblitz(.)io
angular-kc1uhi(.)stackblitz(.)io
angular-lcj5yi(.)stackblitz(.)io
angular-lvy-bkvyy7(.)stackblitz(.)io
angular-n21op8(.)stackblitz(.)io
angular-nujspf(.)stackblitz(.)io
angular-nvavzw(.)stackblitz(.)io
angular-ojbaxu(.)stackblitz(.)io
angular-pcn7ny(.)stackblitz(.)io
angular-qx5ttm(.)stackblitz(.)io
angular-soswe4(.)stackblitz(.)io
angular-tjrwpf(.)stackblitz(.)io
angular-vdwkgy(.)stackblitz(.)io
angular-vv96yb(.)stackblitz(.)io
angular-xeqzqy(.)stackblitz(.)io
angular-xm7khp(.)stackblitz(.)io
angular-zinz3v(.)stackblitz(.)io
angular-zpsmud(.)stackblitz(.)io
angular-zxmgsz(.)stackblitz(.)io
angular-zzrtvx(.)stackblitz(.)io
angular-vv96yb(.)stackblitz(.)io
angular-pnpebe(.)stackblitz(.)io
angular-cmjdm7(.)stackblitz(.)io
angular-ivy-6d2vss(.)stackblitz(.)io
hjgjhjn-csg4mf(.)stackblitz(.)io
js-1withj(.)stackblitz(.)io
js-2dfx8svt(.)stackblitz(.)io
js-3jeoen(.)stackblitz(.)io
js-6jce4b(.)stackblitz(.)io
js-7tkbpg(.)stackblitz(.)io
js-8j8wbj(.)stackblitz(.)io
js-azirnd(.)stackblitz(.)io
js-bfwssp(.)stackblitz(.)io
js-bgqenm(.)stackblitz(.)io
js-fx8svt(.)stackblitz(.)io
js-iqgiwv(.)stackblitz(.)io
js-iqqiwv(.)stackblitz(.)io
js-kfkbak(.)stackblitz(.)io
js-mdurny(.)stackblitz(.)io
js-pgrnce(.)stackblitz(.)io
js-pihxqe(.)stackblitz(.)io
js-rzhdtg(.)stackblitz(.)io
js-tk13zi(.)stackblitz(.)io
js-v4zgeb(.)stackblitz(.)io
js-xerqcn(.)stackblitz(.)io
officeloginaccount(.)stackblitz(.)io
react-ba2roi(.)stackblitz(.)io
rxjs-lv18nb(.)stackblitz(.)io
typescript-byr97k(.)stackblitz(.)io
typescript-dbnwsw(.)stackblitz(.)io
typescript-nxgptb(.)stackblitz(.)io
typescript-qeklm1(.)stackblitz(.)io
typescript-qgtbfk(.)stackblitz(.)io