Last week I blogged about the CVE-2011-2110 Adobe Flash vulnerability being actively exploited in the wild. Adobe released its patch exactly a week ago (Tuesday, June 14) ... I wanted to do a follow up to identify the patch rate within our enterprise customers.
Last week I blogged about the CVE-2011-2110 Adobe Flash vulnerability being actively exploited in the wild. Adobe released its patch exactly a week ago (Tuesday, June 14) ... I wanted to do a follow up to identify the patch rate within our enterprise customers.
Within our last
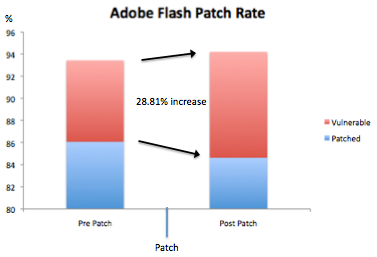
"State of the Web" quarterly report - we identified that only 4.5% of our customers running Flash were running an outdated, vulnerable version. (Java was the most out of date with 51.32% - good reason why this has become a favorite client-side application for attackers to exploit). Running the numbers for the week prior to and the week following the patch shows:
Week prior to CVE-2011-2110 patch:
About 93.43% of clients accessing the web through our cloud during this period had Flash installed. Of the clients that had Flash installed, 7.88% were running an out of date / vulnerable version.
Week following CVE-2011-2110 patch:
About 94.19% of the clients accessing the web through our cloud during this period had Flash installed. Of the clients that had Flash installed, 10.15% were running an out of date / vulnerable version - about a 28.81% percentage increase of vulnerable Flash instances. The overall vulnerable percentage rate is also more than double the rate that we noticed for Q1 2011 - showing that client-side application patching within the enterprise remains a problem. This is in spite of Adobe's auto-updating feature - which still requires action from the weakest-link (the user). "Windows users and users of Adobe Flash Player 10.3.181.16 or later for Macintosh can install the update via the auto-update mechanism within the product when prompted."
 Last week I blogged about the CVE-2011-2110 Adobe Flash vulnerability being actively exploited in the wild. Adobe released its patch exactly a week ago (Tuesday, June 14) ... I wanted to do a follow up to identify the patch rate within our enterprise customers.
Last week I blogged about the CVE-2011-2110 Adobe Flash vulnerability being actively exploited in the wild. Adobe released its patch exactly a week ago (Tuesday, June 14) ... I wanted to do a follow up to identify the patch rate within our enterprise customers.