The above page is largely identical to a legitimate Gmail login page but there are a couple of important differences to be noted. The address of the website is not “www.gmail.com” but rather points to “hxxp://kphb2040.110mb.com/Photosnewmine.htm”. Additionally, the copyright notice is out of date.
If you enter your username and password, the entered data will be sent to a malicious server and you will then be redirected to the legitimate Gmail website. The attacker has done this intentionally so that a victim will assume that the initial login wasn’t successful and they must then re-enter their login credentials.
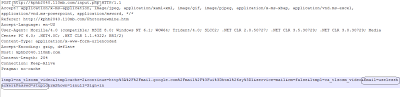
Even if you enter fake information, you will be redirected to legitimate Gmail site. For testing purposes, we have entered fake account information. The following packet capture illustrates the POST request:
The victim’s email address and password has been sent to “input.php” and they are then redirected to the real “mail.gogle.com” website. There are plenty of such websites are present on the Internet and users should be cautious any time they are entering login credentials. Always check URL address before entering any sensitive information on a webpage. Instead of clicking on links, when possible manually enter the website address in the address bar.
Careful…
Umesh