For those unfamiliar, Bitcoin is a digital P2P currency (here's a more detailed video explanation if interested) - people interact with it using locally or hosted "wallet" software. It should not come as much of a surprise that malware has been designed to target abuse of this digital currency the same as any other (e.g., WoW Gold). Abuse can come in terms of theft and/or unauthorized Bitcoin mining - that is, solving computationally complex, "proof-of-work" problems ("solving blocks") to obtain a payout (based on an inflation algorithm).
For those unfamiliar, Bitcoin is a digital P2P currency (here's a more detailed video explanation if interested) - people interact with it using locally or hosted "wallet" software. It should not come as much of a surprise that malware has been designed to target abuse of this digital currency the same as any other (e.g., WoW Gold). Abuse can come in terms of theft and/or unauthorized Bitcoin mining - that is, solving computationally complex, "proof-of-work" problems ("solving blocks") to obtain a payout (based on an inflation algorithm).
A Bitcoin account can be compromised if a computer with a wallet file can be remotely accessed by hackers or becomes infected by a virus or trojan. The first malware specifically targeting Bitcoin wallets was discovered June 16, 2011. Current Bitcoin clients lack functionality for encrypting the wallet, however, the current development tree contains this feature and it will be available in the next release.[1]
Recently, Symantec released a report on
"Trojan.Badminer" - discovered 11 days ago, affecting most Windows systems that has the ability of running one of two Bitcoin mining programs depending on the infected host's configuration: Phoenix Miner (uses the system's GPU on graphics card) or RPC Miner -- the mined Bitcoins are then sent back to a location for the attacker to retrieve the generated currency. When you think about it, this type of revenue generation is perfect for a botnet.
It took me virtually no time at all to find a quick case study of such a malicious Bitcoin miner in our logs from yesterday. Here is a live sample of one that we blocked:
hxxp://img901.fileave.com/x8gp-on-59as.exe
MD5: 8941ECF2586690701F0E748CCC954BB7
Fortunately, it is detected by most A/V programs:
Virustotal Report (
26/44)
The corresponding ThreatExpert report shows the malware connecting to 78.47.124.250 (belongs to Hetzner netblock) on port 8332 -- HTTP listener, assuming Botcoin dropzone. Note: I doubt the ThreatExpert sandbox is able to process any of the code that would be designed to mine Bitcoins on the GPU.
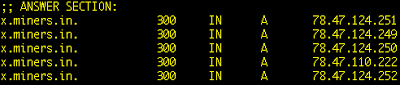
Further analysis of this particular sample shows that it makes its calls out to the domain: x.miners.in which does correspond to the previously mentioned IP in the ThreatExpert report. A round-robin has been setup as follows to handle receipt of the Bitcoins:
All of the IPs in the round-robin are to the Hetzner netblock - a great inexpensive hosting provider in Germany (sidenote: I recently tried to setup an account with them, and they required that I fax over a copy of my passport or drivers license for authenticity as part of their policy to prevent abuse - I did not want to share this and thus cancelled my account setup).
Attempts to HTTP GET access the Bitcoin drop site show authentication required (likely for an admin console):

Whereas, infected hosts do HTTP POST requests with the UserAgent strings like:
Ufasoft bitcoin-miner/0.20 (Windows NT XP 5.1.2600 Service Pack 3)
Ufasoft bitcoin-miner/0.20 (Windows NT 7 6.1.7600)
The Ufasoft Bitcoin Miner (
site) shows that it supports AMD/ATI, CUDA GPU (graphics card processor utilization)
Obvious fake domain registration information provided to Name.com for registration of the miners.in domain:
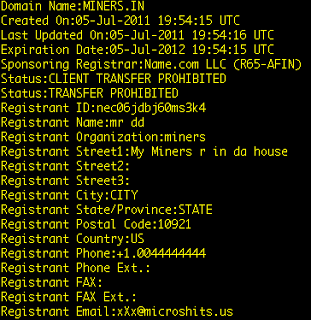
(microshits.us is a domain registered and hosted through gandi.net in France, registered to "Dennis Timony" in the US with billing to "Gemblous Kim" in Germany)
Under the same fileave.com profile there are two PE executables with jpeg file extensions, possibly used in the same malware campaign:
yavncc.jpeg
MD5: 291bfc99016ed4647862aeb896f741d1
IRC Malware / injector (VT:
37/43)
C2: 92.243.19.35 port: 1337
yap.jpeg
MD5: a9c88a209db76deb4fe9f1a9f8f47971
While IRC-based malware and Palevo are older malware families, it looks as though the attacker is padding their portfolio of malware to include this newer, Bitcoin miner, form of revenue generation from their victims.
Do a Google Search for Bitcoin miner in VirusTotal (
Google dork) and you will see an influx of these varieties in late July through present. If VirusTotal is any indicator, this certainly appears to be a growing trend (and convenient revenue stream for botherders).
 For those unfamiliar, Bitcoin is a digital P2P currency (here's a more detailed video explanation if interested) - people interact with it using locally or hosted "wallet" software. It should not come as much of a surprise that malware has been designed to target abuse of this digital currency the same as any other (e.g., WoW Gold). Abuse can come in terms of theft and/or unauthorized Bitcoin mining - that is, solving computationally complex, "proof-of-work" problems ("solving blocks") to obtain a payout (based on an inflation algorithm).
For those unfamiliar, Bitcoin is a digital P2P currency (here's a more detailed video explanation if interested) - people interact with it using locally or hosted "wallet" software. It should not come as much of a surprise that malware has been designed to target abuse of this digital currency the same as any other (e.g., WoW Gold). Abuse can come in terms of theft and/or unauthorized Bitcoin mining - that is, solving computationally complex, "proof-of-work" problems ("solving blocks") to obtain a payout (based on an inflation algorithm). (microshits.us is a domain registered and hosted through gandi.net in France, registered to "Dennis Timony" in the US with billing to "Gemblous Kim" in Germany)
(microshits.us is a domain registered and hosted through gandi.net in France, registered to "Dennis Timony" in the US with billing to "Gemblous Kim" in Germany)