Last week, the Zscaler ThreatLabZ research team did an analysis of phishing attacks we’ve come across in our cloud leading up to Black Friday and Cyber Monday. The team had been seeing an increase in a variety of phishing activities, with targeted attacks and faked login pages designed to steal the credentials of unsuspecting shoppers. (You can read their informative report here.)
With Black Friday and Cyber Monday behind us, we decided to take another look at the data to determine the volume of shopping activity across our cloud and the expected rise in threat activity that coincides with major online events.
What we found was that Cyber Monday was, indeed, the biggest shopping day of the year on our cloud and elsewhere. According to the National Retail Federation, 50 million people shopped online in the U.S. alone. Amazon reported that Cyber Monday was its biggest shopping day in history, and over the five days from Thanksgiving through Monday, Amazon customers bought more than 180 million items.
What we saw more than a billion times
We can attest to the high volume of shopping activity. On Cyber Monday, the Zscaler cloud processed 1.35 billion internet requests on shopping sites, with the highest volume by far on Amazon, at 372,824,847 requests. While Monday’s shopping traffic only represented 2.18 percent of traffic overall on our cloud, it was 72 percent higher than shopping traffic on a typical day.
Cyber Monday top five shopping sites on the Zscaler cloud:
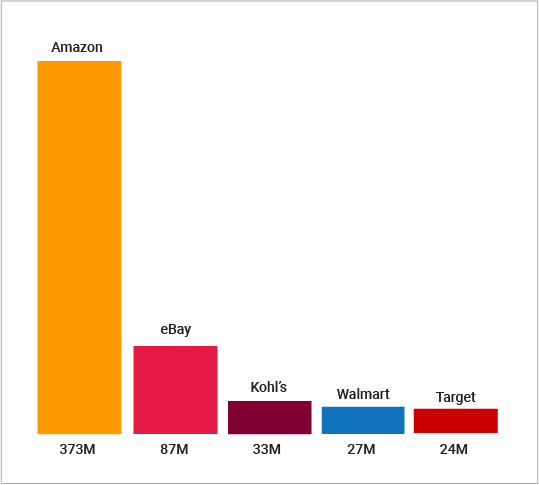
Number of requests we processed on Cyber Monday's top shopping sites.
With so much shopping activity, you might think that Black Friday and Cyber Monday would be the days that cybercriminals would crank up the volume, launching phishing attacks and spreading malware to online shoppers. But the traffic patterns on our cloud show otherwise.
Phishing attacks are planned and executed with precision
On Cyber Monday, we blocked a total of 2,337,537 phishing attempts. That’s significant, but that number was actually down from the days before Black Friday, and this decrease is consistent with patterns we’ve seen. Attacks peak in the days leading up to major events or shopping days. Attackers plan their phishing campaigns for the days when potential victims are looking for deals, aligning their attacks with mainstream advertising campaigns. On the “big day,” when shoppers have already decided what sites to visit, the attacks drop off accordingly.
On the three days before Thanksgiving, we blocked the highest numbers of phishing attempts, with a peak of 4.4 million on Wednesday. By Black Friday, attacks had dropped by nearly 30% from the high. They continued to decrease in volume through Monday when attacks were down 46% from Wednesday.
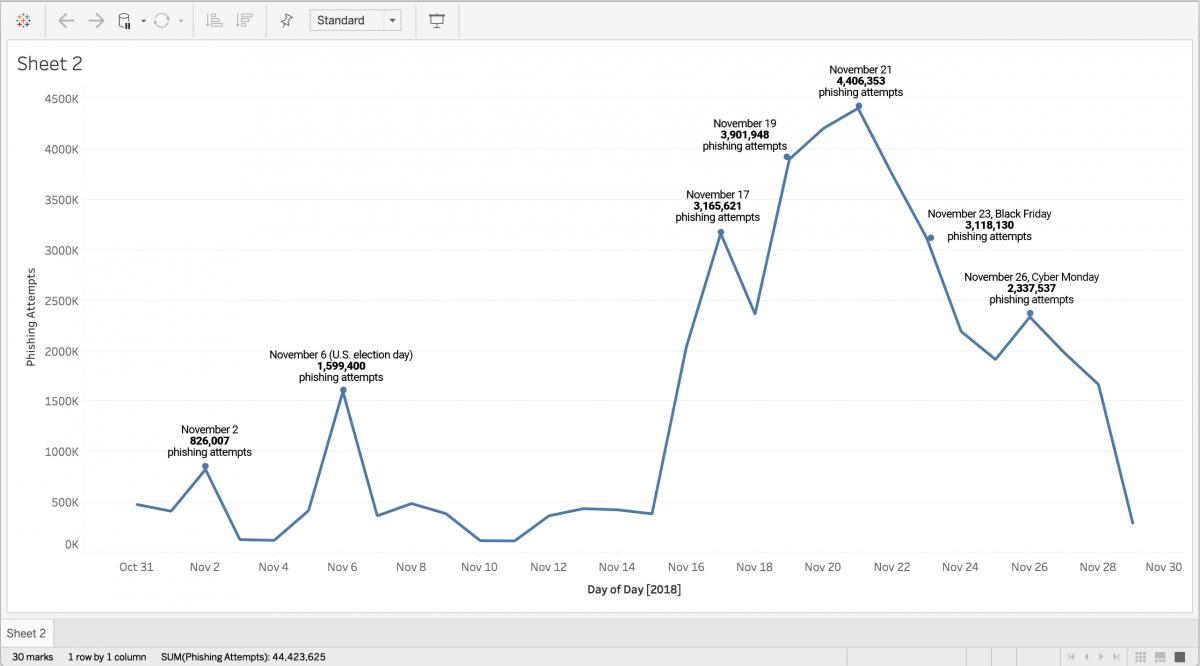 November graph shows daily phishing attempts on the Zscaler cloud
November graph shows daily phishing attempts on the Zscaler cloud
Why did attacks drop on Cyber Monday?
It’s been a long time since hackers could be stereotyped as nerds in the basement using their programming skills to bootleg videos. Today’s criminals are sophisticated in their technical execution and in their understanding of market drivers and user behavior. They operate their campaigns like big businesses—because they are. They know when you’re most likely to be online and when you’ll be sifting through the most email (Monday is the most popular day for phishing attacks). They know you’re more likely to open tracking slips or invoices than an unknown attachment. And they exploit the trust you have in brands like Amazon, Kohl’s, Bank of America, and many others, by creating fake websites that look just like the real thing.
Consumers must change their online behavior accordingly, approaching each online interaction with an awareness of its potential risk. You can’t assume that attachments are safe, even if you recognize the name of the sender; spoofing names is practically effortless. You can’t assume that text messages are safe either, due to the rise in SMS phishing. So-called “SMiShing” links can take you to compromised websites, just as infected email attachments can. E-commerce websites can be compromised in a variety of ways. Hackers can inject JavaScript into a site and the script sends data collected in the input fields to the hacker’s remote server. A favorite tactic is creating sites that look like legitimate sites but are designed to steal your personal information.
Can you tell the difference between these two Amazon login screens?
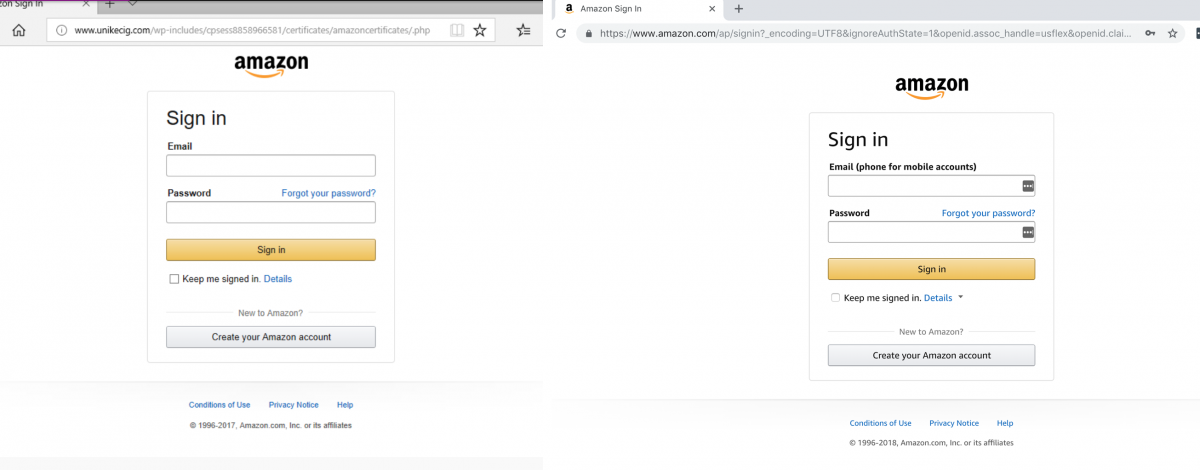
The screen on the left is a login for a phishing site that will collect your personal information, including credit card number, and you’ll think you’re on the Amazon site the whole time. The one on the right is a real Amazon login screen. The only difference is in the address bar. Be sure the site you are on matches the URL address.
We also know, as we stated earlier, that today’s cybercriminals plan their campaigns with a marketer’s precision. It’s wise to take extra precautions leading up to and during big events or news days (another day in November when we saw a surge in phishing activity was the sixth, the U.S. election day).
Three things you can do right now to protect yourself from phishing:
- Check the authenticity of the URL or website address before clicking on a link; make sure the address matches the site you're visiting
- Ensure online retailers and banking sites use secure connections; the URL should start with HTTPS
- Inspect the source of emails with enticing shopping deals; be wary of all links and attachments
More resources:
Read the ThreatLabZ Phishing Roundup blog for an analysis of current phishing trends
Download the infographic:






