The Google Buzz sign-up is being advertised to users when logging into Gmail, and is a fairly transparent process to users with an existing Gmail account.
The Google Buzz sign-up is being advertised to users when logging into Gmail, and is a fairly transparent process to users with an existing Gmail account.
Clicking on “Sweet! Check out Buzz” brings you to your initial follower/follow back network of friends:

And as the privacy statement suggested, it automatically determined people who have communicated with me over Gmail and that joined Buzz to follow me. Similarly Buzz made suggestions on whom I should follow. From the Buzz privacy statement:
For me, the default web apps connected to Buzz were my public facing Picasa and Google Reader:
By default, (as stated in the Google Privacy statement) the list of people that I am following and the people following me will be publicly displayed on my profile.
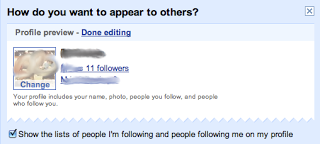
As numerous folks have blogged about (e.g., CNET), this could be a privacy concern for users who do not want to share their social network with the world. As with other social networks, this could be used to gather intelligence on individuals, the corporations/organizations/groups they belong to, and could be used in targeted spear phishing or impersonation attacks. To the general user on the web however, many of the benefits of social networking out-weigh the risks.
In addition to these concerns, there are also a few other items that Google Buzz brings to the table for an attacker. One item in particular is email validation. I clicked on one of my co-worker's that was following me from his default setup for his Buzz profile … I was able to then see the people that he is following and those following him (again, default setting). The people in his social network that I had emailed in the past from my Gmail account have their email address exposed, those that I had not emailed in the past did not have this exposed.