Introduction
An aggressive phishing campaign went viral earlier today that impacted multiple Google Mail users, including those in enterprise Google deployments. The campaign involved unsuspecting users receiving an email with a Google Doc link from one of their known contacts. If a user clicks on the link and further grants access, that user's contacts would be leveraged to send the same phishing email with a link from the impacted user account.
The attack involved squatted domains that were recently registered and hosting the malicious web app. Google permitted this app to request access to a user’s email and contacts leveraging the Google authentication service. As such, many users believed that they were responding to a request from Google, not a third party, and clicked on it.
Campaign details
We saw the Mailinator service being leveraged to receive the spam emails with Google Doc links to harvest email addresses of the victims who fell for the campaign. Below is a screenshot of one of the inboxes used in this campaign:
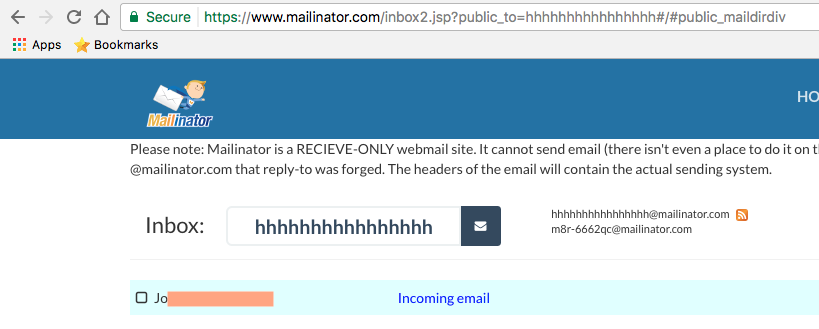
Figure 1: Mailinator inbox leveraged in one of the spam emails
Here is a sample email that the target user would receive from this campaign:
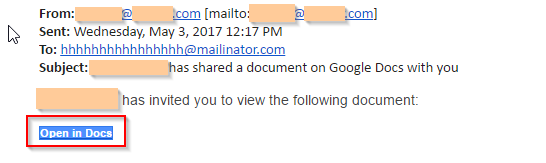
Figure 2: Google phishing email with link
If the "Open the Docs" link is clicked, the user will be redirected to Google’s OAuth to select the Google account:
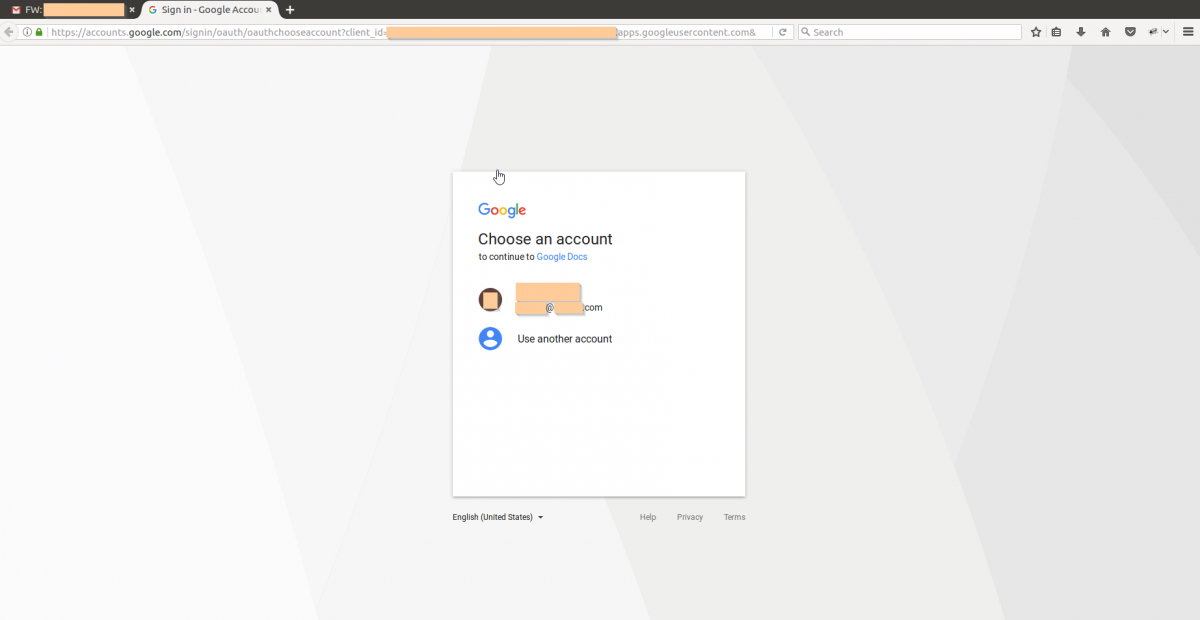
Figure 3: Google's OAuth redirection
Once the user selects the Google account, the malicious app will request the following permissions; to the user, the requests looks like it has come from Google Docs:
- Read, send, delete, and manage your emails
- Manage your contacts
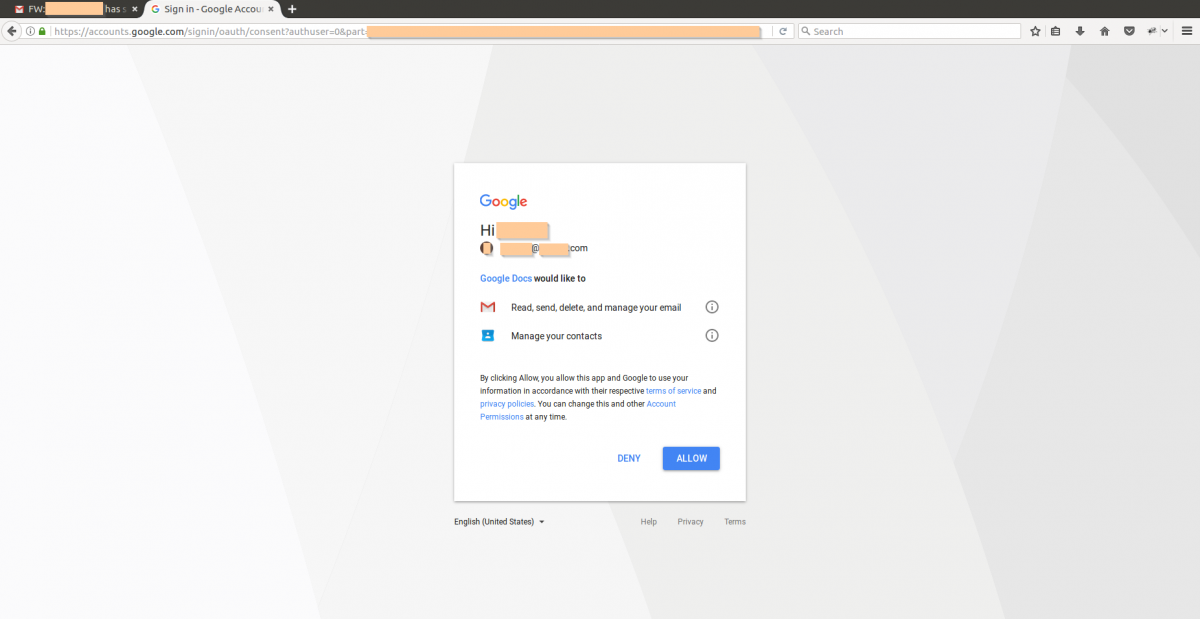
Figure 4: Google OAuth permission for accessing email and contacts
If access was allowed, the user will be redirected to a site hosting a malicious web app. We noticed 10 unique, recently registered domains that were being leveraged for this activity. Each of these domains was registered on the same day: April 22, 2017. We saw more than 10,000 hits in two hours earlier today for these squatted domains.
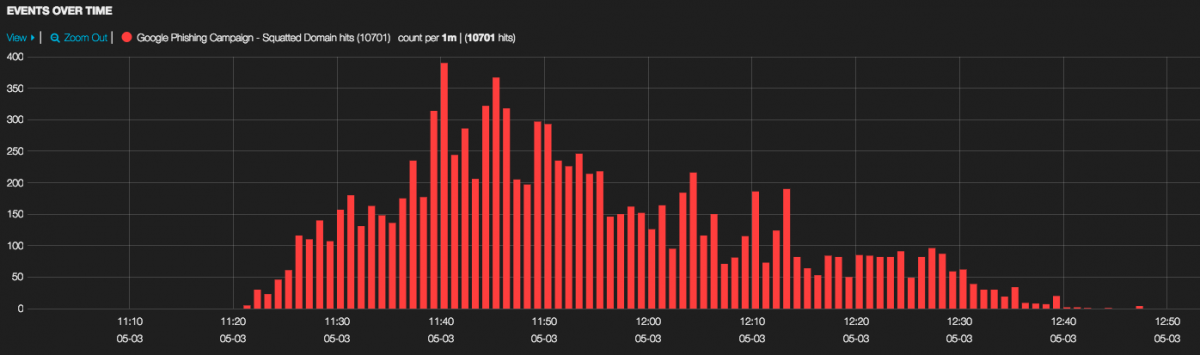
Figure 5: Hits to squatted domains involved in Google phishing campaign
Conclusion
The attacker leveraged the tried-and-true method of social engineering to make this phishing campaign successful. The campaign became viral within minutes, because the majority of these spam emails were sent from legitimate Google user accounts to their known contacts, making detection difficult.
Google was quick to resolve this issue and provided regular updates on its Twitter handle (@googledocs). Zscaler implemented blocks for multiple domains tied to this campaign within minutes of the initial reports, ensuring protection for customers. Customers leveraging strict Suspicious destination-based policies were proactively protected from this campaign.
IOCs
g-cloud[.]pro
g-cloud[.]win
gdocs[.]download
docscloud[.]download
docscloud[.]info
gdocs[.]win
g-docs[.]pro
docscloud[.]win
gdocs[.]pro
g-docs[.]win





