When legitimate sites are hacked, attackers usually modify the existing HTML pages to add their own code (obfuscated Javascript or invisible IFRAMEs), or add new fake pages to the site. The additional code is commonly found after the </html> tag, before the <html> tag, or just after the <body> tag. Since most sites do not use Javascript obfuscation, these hijacking attempts are often not too hard to spot. Even if a site use Javascript obfuscation to hide e-mail addresses, these harmless pieces of code are much smaller than your typical malicious code, and often use just one escape statement.
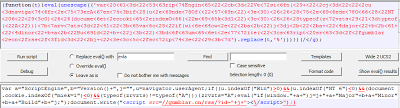
We also occasionally see instances where static Javascript files are hijacked. These are often much harder to detect. We recently found the following malicious code appended to a static Javascript file on an Indian Telecom website:
With the help of Malzilla, I've analyzed the Javascript code. It attempts to download another Javascript file from gumblar.cn, a known malicious site.