Scammers and spammers are known to capitalize on user's news hungry interests. In the past year, they've tricked users into clicking on malicious links in e-mails, blog comments and social media posts on anything from the Royal Baby to the U.S Government shutdown. The end result of these attacks varies from scam to scam, but the tactic remains the same. Provide just enough intrigue and official looking graphics or text to peak the user's curiosity and take advantage of less savvy users. This time they seem focused on exploiting victim's interest in health care plans offered by the National health Information Center (NHIC), a US government run health information referral service.
 |
| Stock image which leads to a false enrollment form |
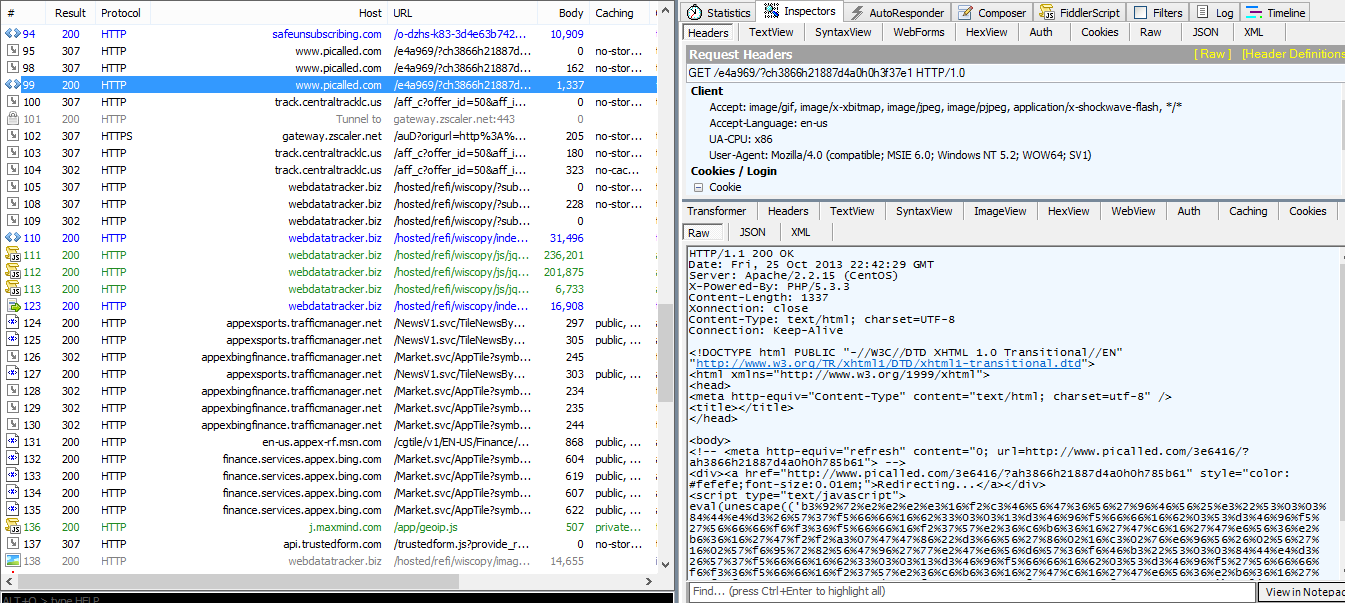
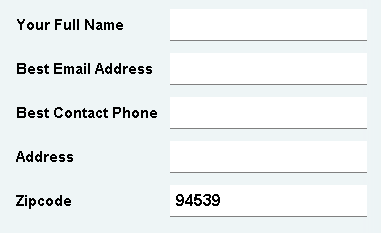
This e-mail has been through circulation for awhile now and shows no signs of letting up. This usually marks the success of a spam campaign. Victims will be disappointed to find that they are not actually signing up for preventive health treatment, but are actually signing themselves up to be victims of Personally Identifiable Information (PII) theft. Clicking through to this link will actually execute an obfuscated JavaScript snippet which will lead the user to a contact information request form.
Less savvy users may think this is part of the process to apply to the NHIC, but this is actually an elaborate fraud to convince users to willingly provide their PII so that it can be sold or used in further attacks later on.
User's should take extra care when it comes to handling their e-mail attachments and links. No matter how official a site looks, there should always be a degree of caution when handing out your PII over the internet.