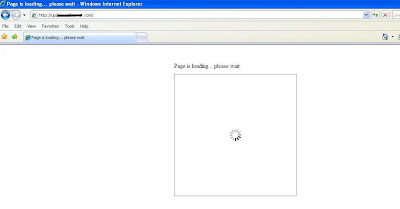
Web access is a critical activity for virtually all jobs, but how many employees recognize the risks that can be encountered simply by viewing a web page? How many times have you encountered web pages with a title such as “Page is loading… Please wait”? I’ve already talked about the threats posed by Phishing and ActiveX vulnerabilities in previous blogs. Another significant threat on the web is the increasingly popular drive-by download attack. In this attack, malicious software is downloaded without user knowledge by exploiting known/unknown web browser or opreating system vulnerabilities. Recently, we came across an interesting website hosting malicious animated page. The page shows animation that will entice the victim to wait patiently while content is supposedly being loaded on the page. Below is a screen capture of the page in question.
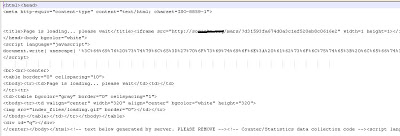
When someone visits this web page, it will continually play the ‘page is loading…’ animation and nothing will ever be displayed on the page. The victim will undoubtedly grow impatient and eventually close the page and continue surfing. But wait; did the victim notice what else was being loaded? Of course not as the malicious content was loaded in the background. Yes, the page actually contains a couple of malicious iframes,
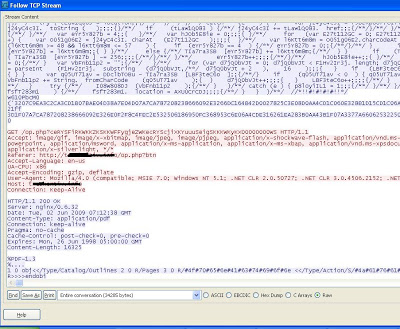
Looking at the above code, there are two hidden malicious iframes, one is clearly shown in text format and other is obfuscated. Those hidden iframes actually point to malicious websites hosting the “LuckySploit” attack toolkit. This is another type of exploit toolkit, which takes the advantage of different types of critical vulnerabilities to download additional malware. This toolkit is more advanced than the older Mpack, Icepack, etc. toolkits. Finjan’s blog has provided detail on this new attack toolkit. After visiting the above page, the malicious website sends obfuscated JavaScript which exploits vulnerabilities, if present and downloads additional malicious binaries. The packet capture for obfuscated JavaScript is shown below,
The attacker has done his job behind the page by downloading malicious binaries without the user noticing. These attack toolkits spread by injecting malicious hidden iframes into otherwise legitimate sites. Once the victim visits those sites, they are redirected to attacker’s website. Social engineering can also be employed to convince victims to directly visit malicious sites controlled by the attakers. The frightening part of these attacks is that the victim does not have to do anything. They simply visit the malicious page and everything runs in the background. Such malicious sites are increasing every day with advanced techniques and with the help of different novel ways to spread malware. Browser patch management is critical for those enterprises seeking to defend against such attacks.
We have observed that number of websites that are infected by hidden malicious iframes and the latest ones include attacks carried out LuckySploit and Gumblar. We recommend you to keep your antivirus updated and keep your eye on such suspicious websites while surfing.
Happy surfing!!!
Umesh