There are apps for everything, including spying. Users often download such apps for little to no cost and for innocent reasons, such as monitoring their children’s activity on mobile devices. However, what happens when the app is malicious and instead spies on the original user and the environments that user is in? In the BYOD enterprise environment, this can spell trouble for corporate networks.
During the course of daily malicious app tracking activity, the Zscaler ThreatlabZ team came across multiple commercial Android spyware programs. These malicious apps were proactively flagged by Zscaler cloud sandbox as seen below:
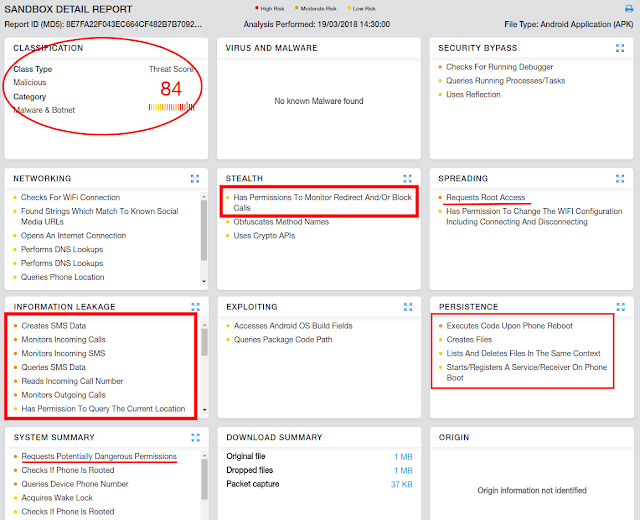 |
| Fig 1: Zscaler Sandbox |
Technical Details:
Name : NeoSpy
Package : nam.atapp.module
MD5 : 8e7fa22f043ec664cf482b7b7092b3d9
Upon installation, the spyware displays its icon, named NeoSpy Mobile, which, upon clicking, asks the user to register or login.
| Fig 2: App Installation & Registration |
For a new registration, it asks for login name, login email, and password. These details were being sent to the server in plain text over HTTP, as can be seen in the screenshot below. Anyone sniffing the network can get these details, which opens another attack vector—but that's a completely different story.
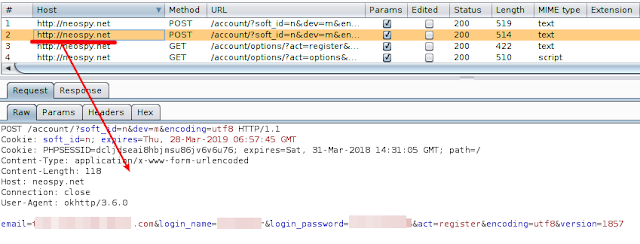 |
| Fig 3: Registration Request |
Once registration is successful, the spyware asks for features to be enabled/disabled on the victim's device. Features include:
- Intercepting SMS
- Intercepting calls
- Enabling keylogger (To steal anything typed by victim, especially passwords)
- Stealing GPS coordinates of victim
- Online status of victim
- Stealing photos
- Frequency for sending GPS coordinates (5 minutes/1 hour/never)
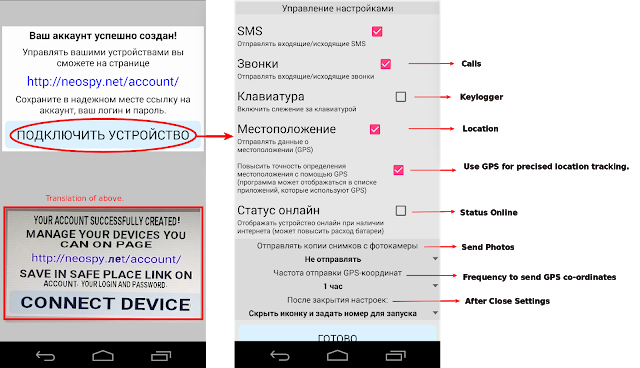 |
| Fig 4: Enabling spying features |
As soon as basic setup is done, the app icon is immediately hidden from the mobile device. Soon after, the server responds with the location where victim's data will be sent. The screenshot below shows the request/response:
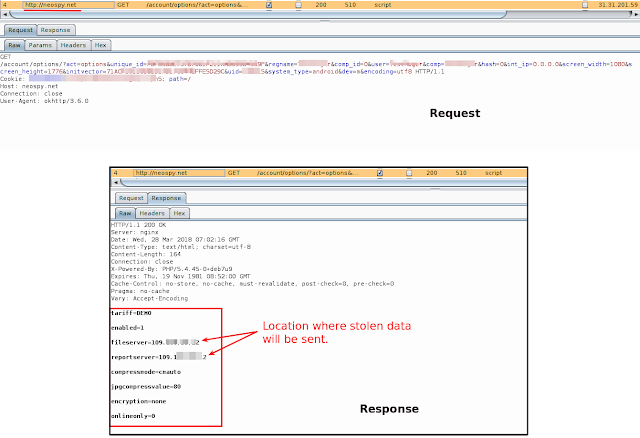 |
| Fig 5: Server response with destination IP |
As soon as the destination address is received, NeoSpy starts its services and continuously hunts for incoming SMS messages and phone calls, and sends them over to the IP address specified by NeoSpy server. Over the course of the spyware life cycle, the victim remains totally unaware. The screenshot below shows stolen data being sent.
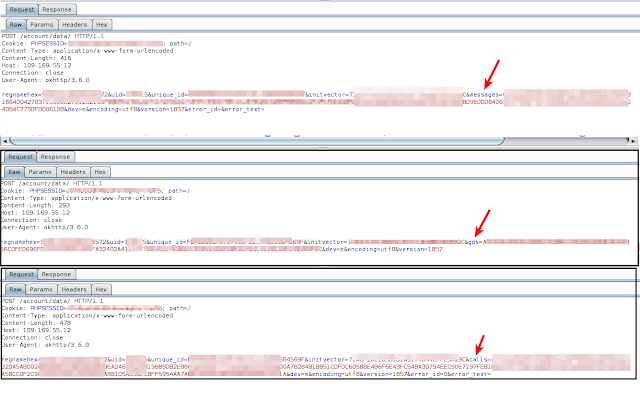 |
| Fig 6: Stolen data sent to attacker |
On the other side, the attacker simply needs to log in to the NeoSpy dashboard, which displays the number of devices infected, as shown in the below screenshot:
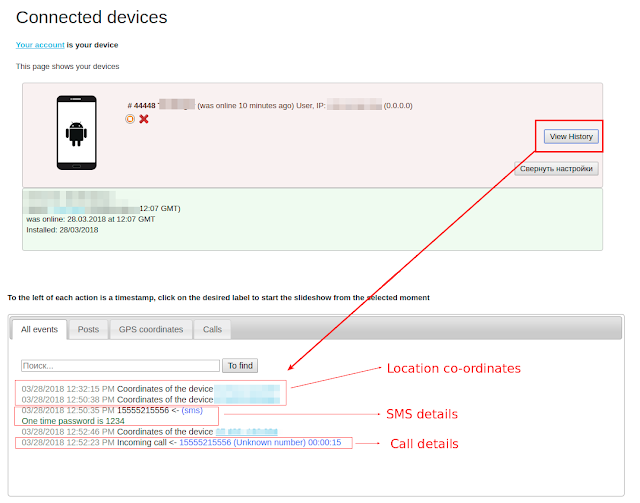 |
| Fig 7: Attacker's dashboard |
We ran the spyware in a controlled environment where the virtual Android device was made to receive an SMS message and call. The spyware successfully intercepted the data and relayed it to the server. Both the details along with location of the device are visible on the dashboard, as shown in the above screenshot.
During our analysis, we also found a variant of this spyware available on Google Play Store with installs between 10,000 and 50,000. Zscaler ThreatlabZ contacted Google’s android security team and the app was promptly removed from the Google Play Store. Such spyware uses false/misleading advertising tactics to lure Google Play Store users. SMS spyware programs portray themselves as parental control apps, and location stealers portray themselves as phone tracking devices. In this case, NeoSpy portrayed itself as an anti-theft app with a description as follows:
"This is an effective phone monitoring module that allows you to find a lost phone or tablet using the geographical coordinates sent to your account. Also you will be able to monitor your child, check where he is, and with whom he communicates, protect him from unwanted acquaintances. All data sent to your personal account is securely protected (AES-128 encryption)."
The screenshot below shows this spyware app on Google Play Store before it was removed:
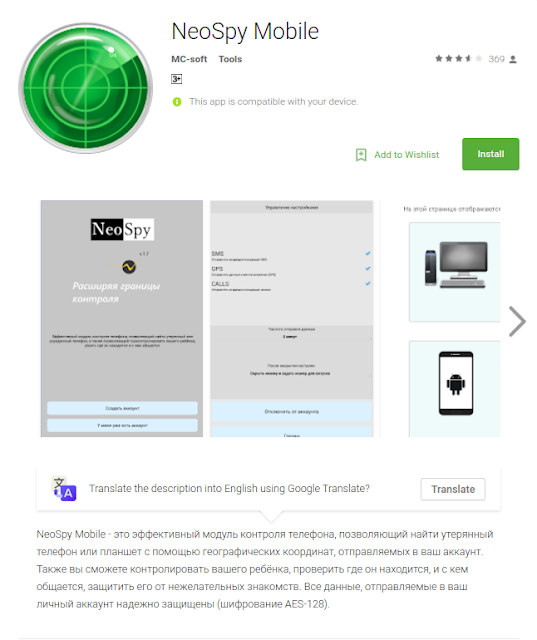 |
|
Fig 8: NeoSpy on Google Play Store |
Conclusion:
The use of Android spyware apps has become fairly common, but with corporate BYOD (Bring-Your-Own-Device) policies, their use can become devastating as employees bring devices loaded with the spyware and connect them to the company's network. It's possible that an infected device on a corporate network could leak sensitive information to an attacker. Or, imagine the presence of a spyware app on a government and defense personnel’s mobile device that could then leak not only private call details, but also locations and photos that may contain highly sensitive information.
In most cases, an attacker needs physical access to the device to set up such spyware properly. It is therefore advisable to deploy password-protected measures like pattern lock or pin lock on mobile devices.
While further examining the Zscaler cloud, we found an increased presence of spyware in enterprise networks over the past two months (see details in Appendix A). Zscaler identified this threat as Android.Gen.Spyware.
Appendix A
| App Name | MD5 | Spyware Variant |
| MobileTracker App | 53ec451d2746f35ea2183fed71b792d4 | Mobile-Tracker-Free (MTF) |
| brasil.apk | 639d2383c4267884a390d8d2f2463a0d | iSpyoo |
| neospy.apk | 8e7fa22f043ec664cf482b7b7092b3d9 | NeoSpy |
| MobileTracker App | 875ea463d7f40709f53b5eb9fbdb231f | Mobile-Tracker-Free (MTF) |
| MobileTracker App | fbd72f310c9efcdf48e7d69c02ac0219 | Mobile-Tracker-Free (MTF) |
| TheTruthSpy.apk | 2f149f3890ac1fb31afbcf8b5c2a917e | TruthSpy |
| TheTruthSpy.apk | b208d4203b7b3675106aff62f840b81b | TruthSpy |
| TheTruthSpy.apk | 6b954360ef997a3d551f4437bc1aeb72 | TruthSpy |
| MobileTracker App | efb56ceea844ddffc97b3c5ba973f39f | Mobile-Tracker-Free (MTF) |
| TheTruthSpy.apk | 4ec7b793f0664e4321e2369ccc077e17 | TruthSpy |
| TheTruthSpy.apk | 11878010fd3bffeb64bd8f0a80648d95 | TruthSpy |
| MobileTracker App | 19fd7f77c8431df87593ce9468a90c7e | Mobile-Tracker-Free (MTF) |
| TheTruthSpy.apk | c349e6446b22f7daa137a45605cee25e | TruthSpy |





