I won't make a new blog post every time I update the Search Engine Security add-on for Firefox, but there have been several changes since the last post.
Notification
This feature was introduced in version 1.0.4. A notification is shown on Bing, Yahoo, and Google to let users know whether the SES protection is enabled for this search engine. The notification is shown under the search input.
 |
| Search Engine Security notification in Google search |
 |
| Search Engine Security notification in Bing search |
User-Agent modification
Most spam pages look at the Referrer value to decide whether or not to redirect users to a malicious page. However, in some cases like the Hot Video pages, only the User-Agent value is used. One common check is to look for "slurp" in the user-agent string to flag the request as coming form the Yahoo crawler. If you check the "Modify User-Agent" checkbox in the options, the string "slurp" is added to the User-Agent header when you leave Google/Bing/Yahoo in addition to overriding the Referrer header.
This option provides additional protection against malicious spam SEO.
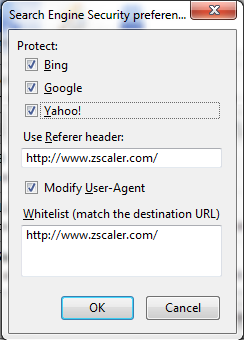 |
| New option to modify the User-Agent header |
Fix for Google Instant
Google now make new searches as you type, without reloading the page, with Google Instant. Since the plug-in was listening on new page load to add the notification under the search input, it was showing only for the first search. Version 1.0.8 ensure the notification is always shown.
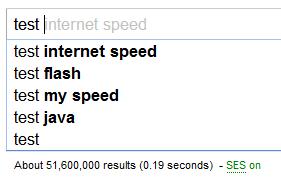 |
| Search Engine Security notification with Google Instant |
French translation
The extension has been translated in French.
If you have an older version of the plug-in installed, go to Tools > Add-Ons > Find Updates to get the latest version.
-- Julien






