Next-gen firewall appliances have been used for years to secure the network perimeter, allowing admins to set policies that determine who can access the network. Identity provider (IDP) services provision users and make it easier to manage passwords and authorize access based on contextual controls. By focusing on identity, they play an integral role in providing all employees, contractors, and partners with access to the information and apps appropriate to their functions.
But, with all the buzz around zero trust security, given the adoption of hybrid and multi-cloud environments, it’s important to understand that enterprises, to achieve zero trust security, must actually decouple application access from network access altogether.
This means that firewalls that take a network-centric approach are no longer effective, and IDP providers that focus solely on identity must be combined with other solutions. Instead, teams should look to redefine private application access with a software-defined perimeter (SDP) service—technology that Gartner calls zero trust network access (ZTNA).
The concept of zero trust security was first created eight years ago by Forrester Research and it was about embracing a new model for application access—one that treats all users and networks as untrusted. Zero trust requires IT to rethink network security, shifting from a network perimeter–based mentality to a more user- and application-centric one. Unfortunately, some analysts and vendors today are describing zero trust the way it was done eight years ago: placing users on the network, allowing for inbound connectivity to apps, and, thus, exposing app IP addresses to the internet.
What’s needed to make zero trust security a reality?
Given that internal apps are moving to cloud and users are accessing them from outside the LAN, the need for zero trust has never been greater. To achieve it, there are five factors that IT must now consider in addition to password security via IDP.
-
Never allow inbound connections to internal apps: Exposing app IP addresses to the open internet leaves them vulnerable to DDoS and internet-based external attacks. Zero trust ensures that apps are completely invisible to the internet and involves creating an isolated environment around each and every internal application.
-
Segmented access at the app level: Also referred to as microsegmentation, this requires the use of secure and encrypted micro-tunnels that are spun up on demand and on a per-session basis. Micro-segmentation is a modern alternative to the unnecessary and complex layers of network segmentation done in the past.
-
Never place users on-net: Access to applications should no longer require access to the network. By decoupling apps from the network, the internet can be used as the new corporate network, providing a more secure, perimeter-less approach to application access.
- Monitor suspicious activity and stream to SIEM: IT must have a way to view user activity—in real time—to reduce the potential for security exposure. The ability to automatically stream logs to a SIEM allows teams to leverage the power of their SOC immediately, instead of relying on batch cron jobs with limited visibility (IP and port-centric only) that are sent from legacy tools like VPNs.
- Discover unknown apps: Zero trust should not only apply to known applications, but to unknown applications as well. This is why it is critical for teams to be able to discover previously unknown applications and apply the same zero trust access policies to them as they do to all known apps.
The zero trust ecosystem
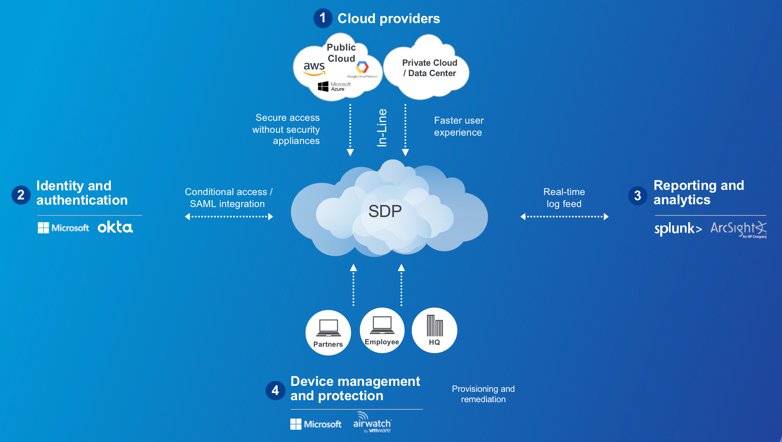
The zero trust model requires an integrated ecosystem of modern security technologies. At the heart of this ecosystem is a software-defined perimeter (SDP) solution. This term, now known by Gartner as ZTNA, describes cloud-based technologies that securely connect users to internal apps via the internet instead of network firewalls and appliances. Here is a look at some of the other zero trust security ecosystem players:
- Identity providers (such as Azure AD, Okta, Ping, Centrify): These password and authentication providers integrate with SDPs and are used to centralize identities, simplify management, and provide authorized access to apps by creating and passing SAML attributes.
- Mobile device management (such as Intune, AirWatch, MobileIron, Good Technology): These solutions can be used to silently deploy SDP software onto endpoints so that all connectivity from iOS, Android, Windows, and Mac devices is based on zero trust.
- SIEM providers (such as Splunk, LogRhythm, EventTracker): A key technology within the enterprise SOC, SIEM is used to provide visibility into user activity and consume audit logs coming from the SDP to identify suspicious activity.
- IaaS platforms: Platforms such as Azure, AWS, and Google Cloud Platform (to which many internal apps are now migrating) do have some high-level security features of their own, such as the AWS Security Groups. But, teams can combine these with a purpose-built SDP solution to provide secure access to cloud apps across hybrid and multi-cloud environments.
When looking to adopt a zero trust model, remember to keep the ecosystem—and its heart, the software-defined perimeter—in mind. Don’t misconstrue zero trust for what it was eight years ago. What you need, instead, is a model like Gartner's zero trust network access.
Learn how National Oilwell Varco, Perdue Farms, and MAN Energy Solutions have all made zero trust possible through software-defined access with Zscaler. Videos are available at https://www.zscaler.com/products/zscaler-private-access.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Christopher Hines is head of product marketing for Zscaler Private Access and Zscaler App





