[Update - July 13, 2015]
- CVE-2015-5122: valueOf use after free vulnerability during the assignment to freed TextBox
Two in-the-wild samples reported here
- CVE-2015-5123: valueOf use after free vulnerability during the assignment to freed Bitmap
Introduction
Exploits, Remote Control System, and more
- Flash 0-day exploit with Proof-Of-Concept (POC) [CVE-2015-5119] - Confirmed 0day for the latest version of Adobe Flash Player, running on Windows XP and Windows 7. The exploit did not succeed on Windows 8.1. We also saw support for targeting OS X. This is a Use-After-free vulnerability in Adobe Flash player's built-in ByteArray class that can lead to crash or remote code execution by the attacker.
Affected applications:
- The majority of the popular browsers including Chrome, FireFox, Internet Explorer and Safari with Flash Player installed are vulnerable to this issue.
- Microsoft Office 2007/2010/2013 - where the attack scenario will involve an office document with the malicious SWF file embedded in it. The document may arrive via an e-mail or as a drive-by download on the target system.
Adobe released a patch today to address this vulnerability.
- Microsoft Windows Kernel code injection vulnerability exploit that can be leveraged to perform privilege escalation on the target system to bypass various security mechanisms
- Support for iOS devices - They are leveraging the popular iOS Jailbreak application Cydia for iOS devices to further install malicious payloads on the target device.
- Support for Android Devices - There is a separate module for Android OS (Android Webkit) that is leveraging a probable 0day exploit [we are still working on confirming this] in the Android browser and running various known root-access exploits like exynos, gingerbreak, levitator, etc. to root the target devices and further install malicious payloads.
- Support for Windows & Blackberry devices - We also saw source code for supposed exploits that will target Windows Phone 8 as well as Blackberry devices.
- MacOS Rooting exploit to enable online and offline installation of untrusted applications.
- A Remote Control System (RCS) Dropper module that is capable of creating both mobile and computer system payloads for Windows and Macintosh.
- A multi-stage JAVA exploit module that contains a weaponized version as well as a two stage version with features to by pass Microsoft Security Essentials and an example Trojanized Putty.exe payload.
- Multiple driver files that may contain Rootkit functionality to hide the malicious process and evade detection.
- Source code of the core Remote Control System module where we can see the in-depth list of features supported by it.
core-win32:
1.) Monitoring modules for Instant messengers, Web Browsers, PC cameras & microphones, etc.
2.) Monitoring social media activities over Yahoo, Gmail, Twitter, and Facebook
3.) Hooking Outlook and getting email and contact details.
4.) Relaying infected system information including time, battery status, processor, memory, OS, user etc..
5.) Advanced keylogging capabilities
We also observed support for 64-bit operating system target.
- There are also multiple anti-VM, anti-Sandbox, and anti-AV evasion modules present in the source code archive.
Loader configuration server
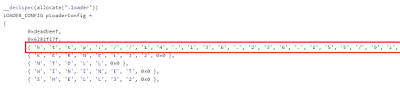 |
| Hardcoded configuration file location |
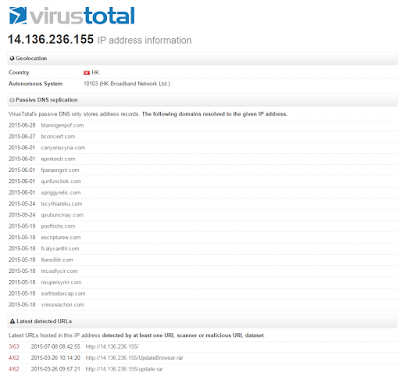 |
| VirusTotal report for the Configuration Server |





