Malvertising
Malvertising involves using malicious online advertisements as a means to serve malware payloads to unsuspecting users. Cybercriminals leverage compromised advertising networks to serve malicious advertisements on legitimate websites which subsequently infect the visitors. This has become one of the most successful vectors of malware delivery for cybercriminals. Malvertising campaigns in most cases will involve a malicious advertisement redirecting the user to an Exploit Kit (EK) landing page.
Exploit Kits
Exploit Kits are web-based frameworks that attempt to exploit browser application plugins for known vulnerabilities. Upon successful exploitation, the EK will silently download and install a malware payload on the victim machine. The entire exploit cycle is completely hidden from the end user.
The Exploit Kit infection cycle typically moves through three distinct stages:
Stage 1 - Loading stage: This stage involves the initial delivery mechanism which causes the user to visit a compromised website or advertisement. This compromised website then leads the user to the actual Exploit Kit landing page which may involve a series of web redirects.
The initial delivery vector can be any of the following:
- Spam & phishing e-mail
- Social Networking sites
- SEO poisoning
- Compromised website
- Malvertising on legitimate sites
Stage 2 - Landing Stage: During this stage, the victim machine visits the actual EK hosting site and the exploit cycle is started. The EK code will attempt to exploit the identified vulnerable plugins by downloading the relevant exploit payloads.
Upon successful exploitation, the EK will lead to the download of the malware payload as configured by the EK operator. The entire exploit cycle may not require any user intervention in most cases, which greatly increases the success rates.
Stage 3 - Malware Payload Delivery: This is the final stage of the Exlpoit Kit infection cycle where the malware executable is downloaded and installed on the victim machine. This is usually achieved, after successful exploitation, by one of the EK payloads that was served during the landing stage.
The EK operators strive to ensure that the EK code, exploit payloads and the end malware payloads have very low to zero antivirus detection. Over the past few years, EK authors have implemented multiple new features to improve the effectiveness & infection success rates:
- Anti-VM and Anti-Analysis features
- Detection of known antivirus drivers
- Multiple levels of highly obfuscated JavaScript code
- Dynamic construction of exploit payload URLs only when a vulnerable plugin is found
- Short lived exploit payload URLs often restricted to one visit per IP address
- Obfuscated and repackaged exploit payloads
- Repackaged malware payloads
After last year’s infamous “Kyle & Stan” malvertising campaign that affected Google, Yahoo, YouTube and multiple other popular websites, this year has been no different. We have seen a malvertising campaign leading to a zero day Flash Exploit payload via the Angler EK to start of the year, followed by a Malvertising campaign targeting European Transit users. There have been numerous other instances of Malvertising which involved popular sites like huffingtonpost.com, yahoo.com, zillow.com and we only expect this trend to continue throughout the year.
 |
| Malvertising attempts blocked [Last 7 days] |
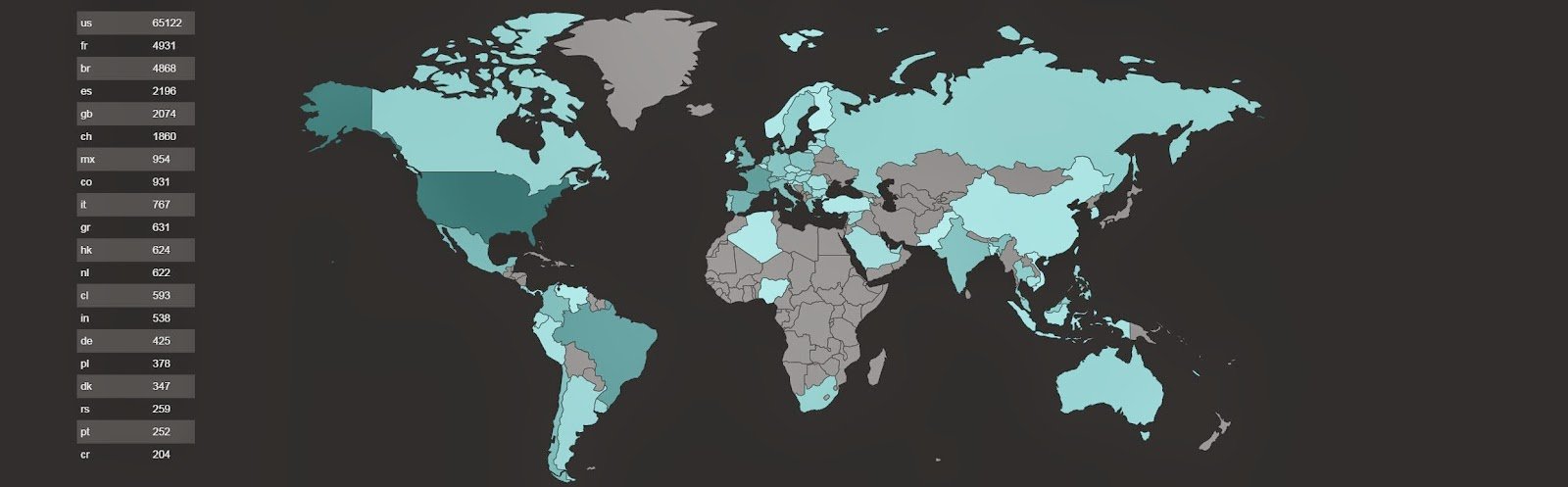 |
| Users targeted globally by Malvertising [Last 7 days] |
Advanced techniques to evade detection
We have also noticed some new techniques being introduced in the Malvertising & EK exploit chain this year to further evade detection by URL reputation & network scanners:
- 302 cushioning, or a 'cushion attack', is used to redirect victims to malicious sites via simple HTTP 302 redirects rather than traditional techniques like iframes or JavaScript redirects which are easy to detect by network IDS/IPS devices.
- Domain Shadowing, involves compromising the parent domain and creating multiple sub-domains that point to malicious code.
Please refer to our most recent write-up describing it in more detail.
A typical Malvertising infection cycle would involve following stages:
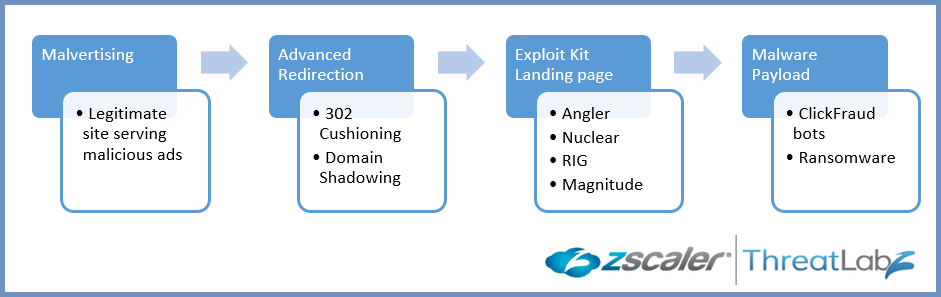 |
| Malvertising infection cycle |
Cybercrime Infrastructure & Business Model
Threat actors involved at different stages of the infection cycles are part of a thriving Cybercrime infrastructure & business model that is all interconnected as seen below:
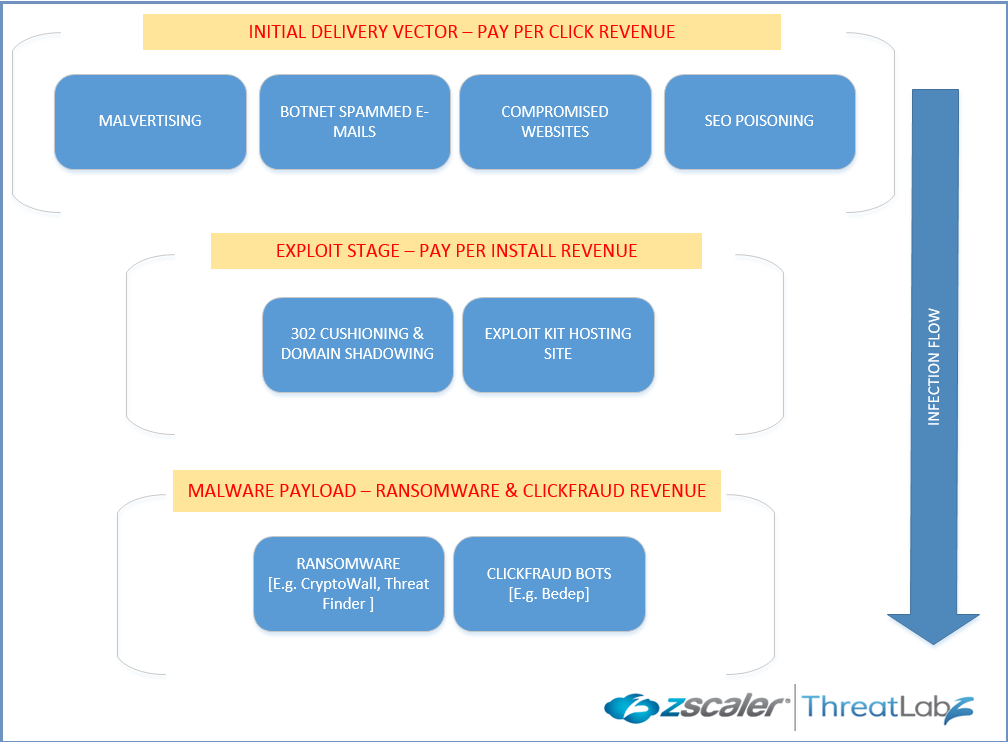 |
| Cybercrime Infrastructure & Business Model |
The top Exploit Kits that we have seen involved in various Malvertising campaigns in 2015 are:
- Angler
- Nuclear
- Magnitude
- RIG
/l86dvw7qfp.php
/62ynh7h2e9.php
/ukvugw2mct.php
/govern_wickets_insulator/1305714616
/pews-bathrobe-understatement/2333676765
/pions_fingertips_rebuff/8057907058341
/pounces-garrotted-bedfellow-mingling/387249683138585374
/3R6sqI6COwSVqj-FeU2X7WK5qWYlpQskmTr-ivR7ZSZuIbap/9Oj96BjEJ7Rpe-CuvXMl_DVaDQFeQV53vYrJekoio1vi9dIc/eS9vXVpGOZhiD1CflWv8J9AeWGa_auetZVWzsTeBZqZTSXlR/VZsq9DV0HzNyc0_HxSiYUpc4_NiyZW729YthGRWUQOssgshN/JQqtNNYjlHsJNYAFZDsQEJIFAF227hht8nMx0qCyo6HRXuO8
sstmxixcdr.serveftp[.]com/xqpjvl5oabhksk1fqq1bwl1afxdcs09xxxbjf1pdva.htmlUsing new subdomains of compromised sites enables Nuclear to evade older, domain-based blocking and allows for rapid rotation or one-time use of subdomains to hinder analysis by security researchers. In addition, before actually serving the exploit kit's landing page, potential victims are sent through an intermediary hop via 302-redirection; the victim is either 302-redirected to the landing page if this is a new victim, or sent to the desired non-malicious page.
fu7bncm7xzjwu6hcfhuwwgg.90saniye[.]com/xvsobfbfaayaaxcou1gfcfvbs1wrefrrulaoebvovlfixfjkufgphacxulkl.html
azwbm2qdqs276gxw9qj82fg.akildakalici[.]net/rkklfaaacu1yh0aexaniauyvawypak8rcebtxquavh9ydl4kvvbsbfspulgxc1is.html
Another interesting feature of Nuclear is that various fields are Base64-encoded and passed to the malicious domain:
ce79suqo5euujfchllkmwwf.alumni-year-book[.]com/index.php?a=cmtpbWJwZ2Q9cWEmdGltZT0xNTA0MTUwNjU0NjExNjY2ODgyJnNyYz0zMjImc3VybD1vbmVoYWxseXUuY29tJnNwb3J0PTgwJmtleT0xOUZGM0EwJnN1cmk9L3RvcGljLzQ0NzU0LSUyNUUyJTI1OTklMjVBNS10aGUtb2ZmaWNpYWwtJTI1RTIlMjU5OSUyNUE1LW5hbXNvbmctY291cGxlLSUyNUUyJTI1OTklMjVBNS10aHJlYWQtJTI1RTIlMjU5OSUyNUE1Lw==Similar to Angler, the landing page contains sections of highly obfuscated JavaScript in between chunks of text; however, unlike Angler, Nuclear uses totally randomized text, which makes landing pages more difficult to detect using traditional signatures.
--base64 decoded--
rkimbpgd=qa&time=1504150654611666882&src=322&surl=onehallyu.com&sport=80&key=19FF3A0&suri=/topic/44754-%25E2%2599%25A5-the-official-%25E2%2599%25A5-namsong-couple-%25E2%2599%25A5-thread-%25E2%2599%25A5/
The majority of the recent Nuclear EK infections were serving Teslacrypt Ransomware.
QMx sKWhYGWu eZJGyZ aFnKgWwC xfgcc KmTs rOETlec oBWPHKZ yVrHkWnM AXkEQvfe oPeaHHcdWk kYVRPcClQO GmV gQl
fQgQqXM gvllOkaC HknmN qvPFFFKKja TRNMxyHikW JYAb QOWuNSKTX mhzDYzV
 |
| Nuclear EK instances blocked |
 |
| Nuclear EK server locations |
Magnitude Exploit Kit
55e3a.76ec.b9.d9a6a.b863cb4.01962.4abd.c0s7894l6e3.basicmagic[.]pw/?17657271617e787b766376796376637e3974787a
ba5.861fa24.4f.f40.e0c1.f51.afb.47340.7a.o7faf55lqj.workerscertain[.]in/?2b594e4d5d4244474a5f4a455f4a5f4205484446
domain.tld/search
domain.tld/search.php
far[.]capacitorsfordownhole[.]com
min[.]closinglawyer[.]net
deal[.]customdetonatorcapacitor[.]com
road[.]detonationcapacitor[.]com
home[.]autoqueen[.]net
calls[.]hightempcaps[.]com
add[.]hightempceramiccaps[.]com
top[.]highfrequencycapacitors[.]com
take[.]buriedbroadbandcapacitors[.]com
pro[.]customdetonatorcapacitor[.]com
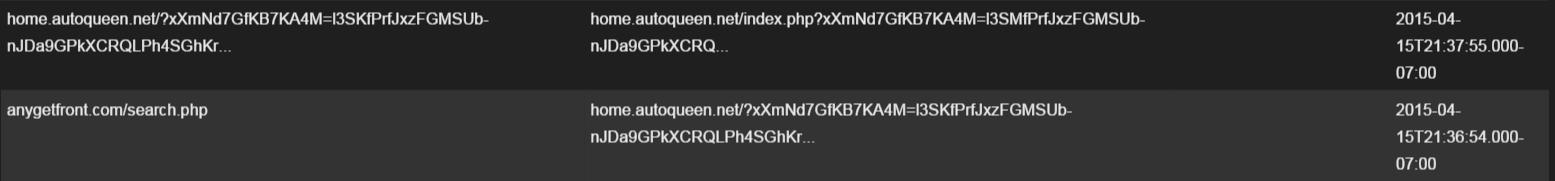 |
| Two-stage landing page |
l3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWKrBLZZl9B_ZqXHOJqjl-gzeQSdpovwBbQuGhVxL4ZVUgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioXX9RyJNA5A_8CUQrY80Vz0ybYWJMslzxCE7GMBzeMdVkgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWB9RWMZQJArcHEHbYy3A_3neJGdJl0lUKA4TQFxbtPVUgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWLqBXeMgoQrZOVE7k-31-nnLNHI8lywhfUvGJQmu5IVUgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWE9RyKZQhBq5KQErIz2FSmnOUVeM11wUXU4TUDz7kYVEgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWE9RyKZQhBq5KQErIz2FSmnOUVeM11wUXU4TUDz7kYVEgbrAl3SKfPrfJxzFGMSUb-nJDa9GPkXCRQLPh4SGhKrXCJ-ofSih17OIFxzsmTu2KV_OpqxveN0SZFT_zR3AaQ4ilotXQB5MrPzwnEqWwxWeioWK9BPcNAsT-MHBR-Bp3Vv1zbJBJJgllROB7mJXzLhLVEgbrA
 |
| RIG EK instances blocked |
 |
| RIG EK server locations |
Malware Payload: ClickFraud & Ransomware
Exploit kits can serve a variety of different payloads, from Backdoors and Ransomware, to generic Downloaders. We’ve noted that the ultimate goal of many exploit kits is to monetize the infected system as much as possible, most commonly via Adfraud/ClickFraud. To support this goal, a very common payload for exploit kits is the Trojan Bedep, which can download additional malware and is used to perpetrate advertising fraud. In order to evade detection, Bedep is usually downloaded in an encrypted form and decrypted in memory as part of the infection process. Once decrypted, Bedep uses a domain generation algorithm (DGA) to communicate with its command and control servers. This communication is over normal HTTP, but messages are encrypted and then Base64 encoded, making analysis and detection more difficult.
When used for advertising fraud, Bedep creates a hidden desktop (a desktop instance not visible to the end user), shown below, that is not normally accessible in Windows, then begins displaying loading web pages and advertisements to commit advertising fraud.
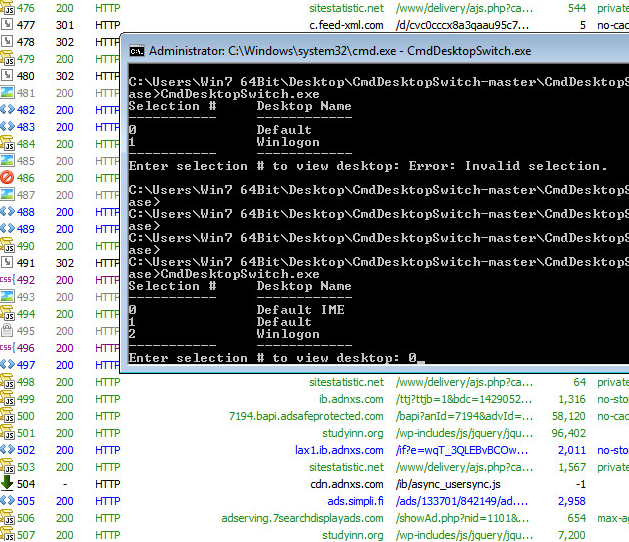 |
| Bedep Adfraud traffic & hidden desktop used to display Ads |
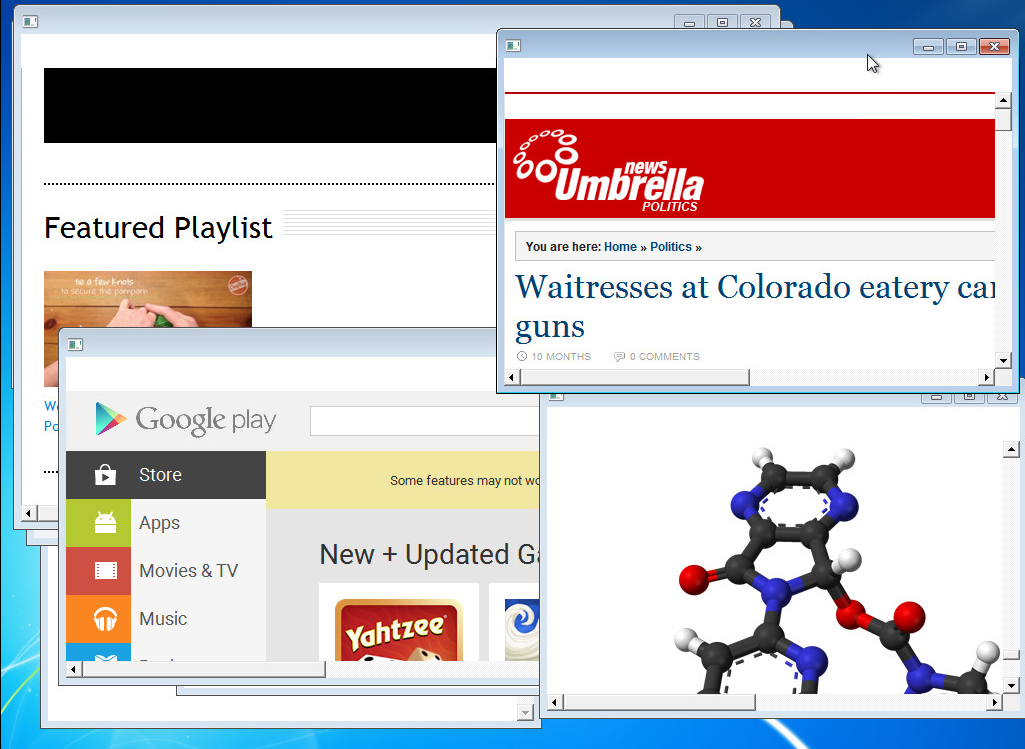 |
| Bedep displaying multiple Ads on hidden desktop |
Pages are quickly cycled to make as much money from the Ads as possible. In general, Bedep’s Adfraud traffic takes the form of ‘/r.php?key=’ or ‘/ads.php?sid=’ followed by a 32-character alphanumeric string, for example:
keppertoolsmaster[.]com/r.php?key=722445fbcd3e90f18f451c1344bdcc85Another popular payload for exploit kits is ransomware, such as CryptoLocker and CryptoWall. This type of ransomware encrypts files on an infected system, and then demands payment to decrypt the files. CryptoLocker was first discovered in 2013 and quickly became popular due to the use of asymmetric encryption to hold user’s files for ransom, which is expected to be paid in Bitcoins. Additionally, recent samples contact a command and control infrastructure hosted on TOR hidden servers via TOR proxy gateways, such as tor2web.org. ThreatLabZ recently analyzed a sample of CryptoWall 3.0, a derivative clone of CryptoLocker, and found the binaries were hosted with a “.jpg” extension to avoid raising suspicion. Some of the other features of this CryptoWall sample include:
- Decryption service hosted on TOR
- CAPTCHA on decryption service
- High ransom amount (700 USD, increasing to over 1400 USD)
- Multiple payment options accepted besides Bitcoin
Multi-tasking example from a recent infection
A recent development we’ve observed is using Bedep to install ransomware as well as committing advertising fraud. In the observed sample, Angler EK first installed Bedep on the compromised system, which immediately downloaded a piece of ransomware called “Threat Finder v2.4.” Like other popular ransomware, Threat Finder displays a “HELP_DECRYPT” message which instructs users to send 300 USD of Bitcoins to a Bitcoin wallet in order to decrypt files. The screenshot below shows both the Threat Finder ransom window and advertising fraud sessions captured by Fiddler. Installing both ransomware and committing advertising fraud potentially generates even more money for the perpetrators.
 |
| Threat Finder v2.4, Bedep, dual infection |
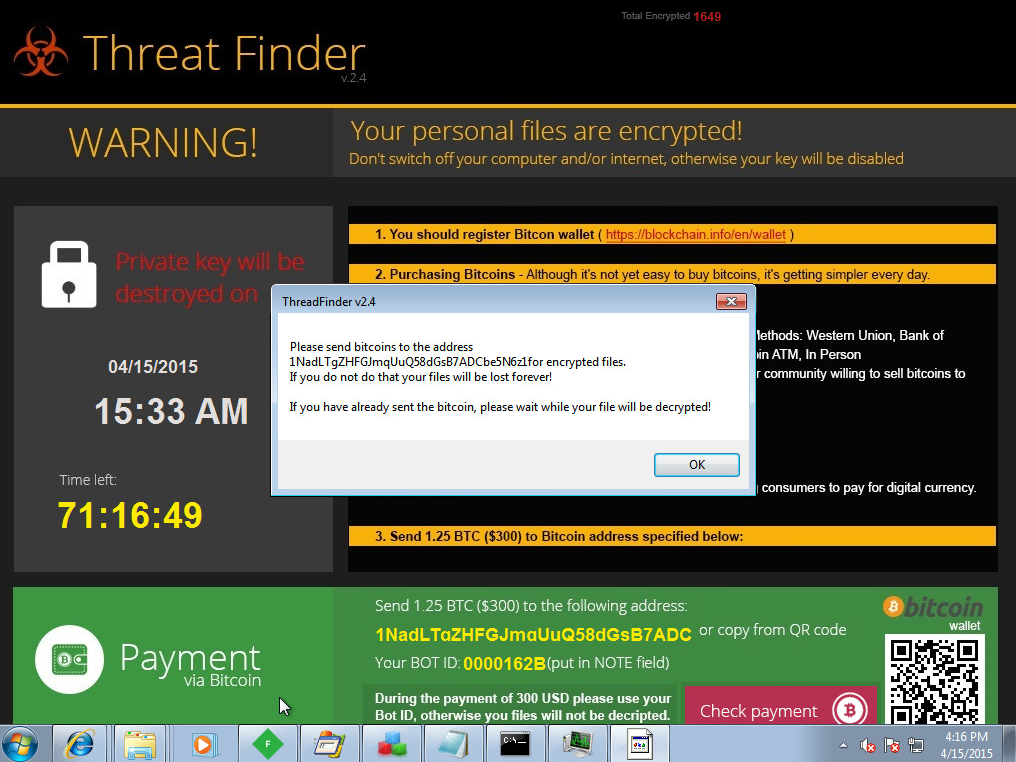 |
| Trust us, we'll decrypt your files.... but only if you pay! |
Malvertising campaigns have seen a significant uptick in 2015 and continue to be the most lucrative initial delivery mechanism for Exploit Kits. The fact that the legitimate websites becoming target of these campaigns have very little to no control for preventing such attacks makes this a very dangerous vector and a popular choice for cybercriminals.
The users should ensure that all the Browser application plugins are always patched with latest updates and disable the plugins that are not used. We also highly recommend using click-to-play feature available in many browser for Java & Flash plugins.
Analysis by: Deepen Desai, John Mancuso, Ed Miles, Chris Mannon









