Spyware or legitimate monitoring application? You decide. In this blog we'll discuss a 'legitimate' app that can be purchased in Google Play known as SMS Tracker. Now it's legitimate as it advertises exactly what it does, but based how this same application is packaged and distributed in other markets, it's clear that the vendor is also targeting another, less altruistic audience with this same application. The app also illustrates the powerful access permissions that an application can gain so long as the end user agrees to it, either explictly or otherwise.
Details about the application:
Name: SMS Tracker.
Installs: 10,000-15,000.
As per the description on the application’s Google Play page, the application is able to do the following:
- SMS Tracking – Intercepts text messages. Read all inbound and outbound text messages. Details include time and date, phone number, contact name and location of the target phone. Complete Text message tracking and logging.
- MMS tracking - Intercepts MMS multimedia messages. Read and view all inbound and outbound MMS messages. See what photos are sent to and from the target phone. Details include photo, time and date, phone number, contact name and location of the target phone.
- Browser Tracking – monitors all web browser activity on the target phone. Know which websites were visited, which pages were viewed and when.
- GPS Tracking – Logs GPS location information wich can later be viewed on a map. Know when and where the phone was located at all times. Breadcrumbs to record location information allowing parents to locate their children at frequent intervals. GPS logging occurs at a user defined rate (default interval is 5 minutes). Remote GPS logging and viewing give you the ability to see the location of your child’s phone, from any web browser. The breadcumb trail offers powerful GPS Tracking.
- Call Logging – Monitors all inbound, outbound and missed calls. Identifies the phone number, contact name, call duration, and location of the phone for every call.
- If you want to know where your kids are, just send them a text message. The location of the phone is
- recorded every time it sends or receives a text message.
- Tracking of System Events, including Device Powered On/Off, Device Attached / Removed to/from the charger, Apps installed/removed/updated.
- Silently monitor all inbound and outbound SMS messages.
How the app can be used?
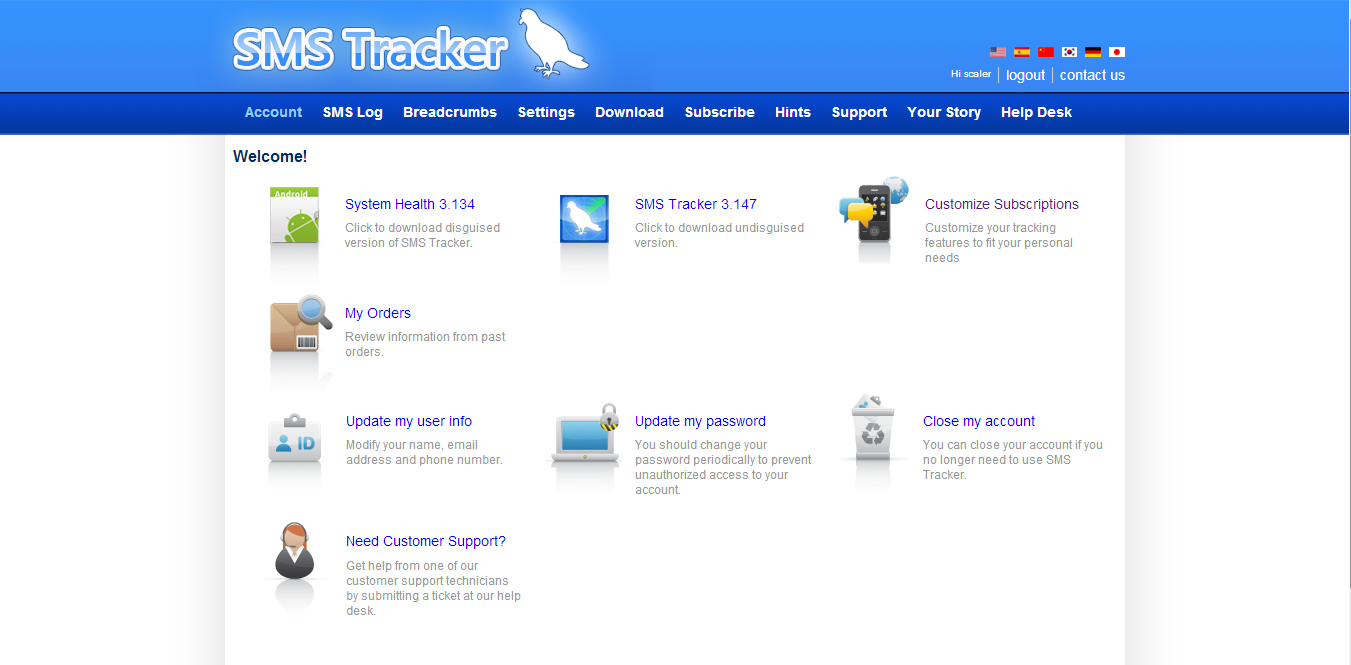
First you need to download the application and install it on the device on which you want to spy. After installing an application you need to register it. Next, you need to go to http://smstracker.com, where you will be asked for your login name and password ,which was registered at a time of installing the application.
This screenshot shows the dashboard after login.
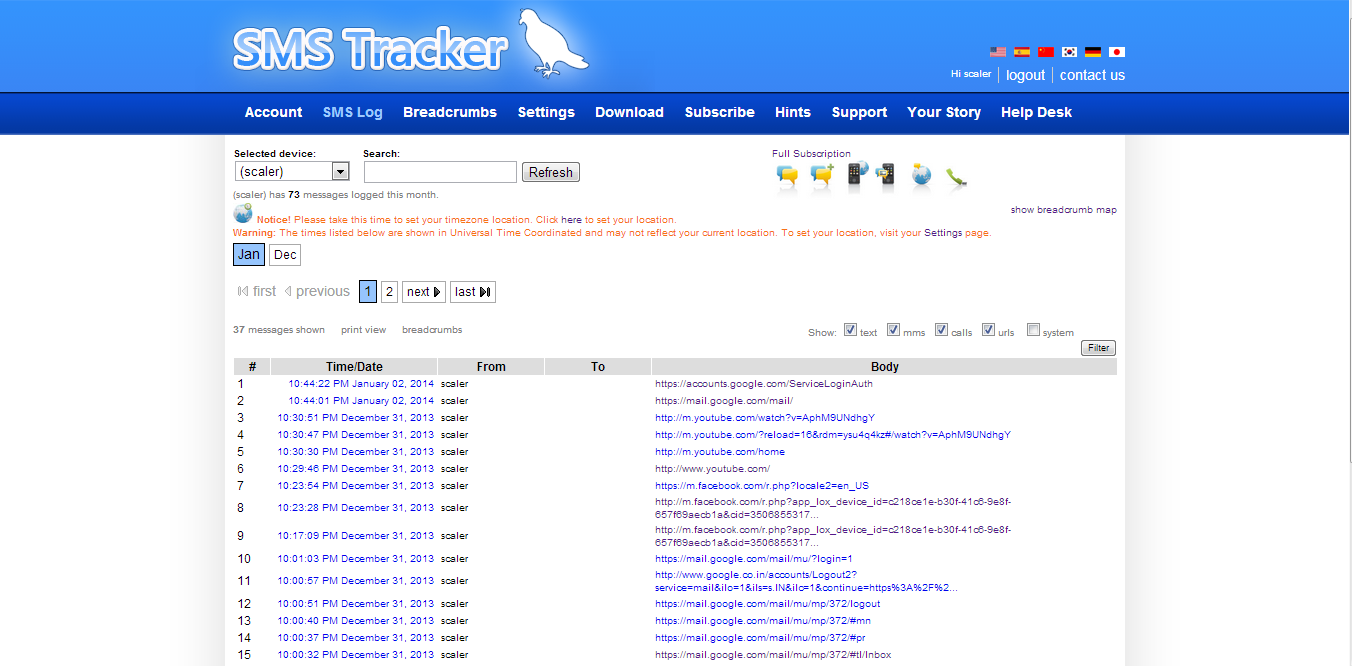
This screenshot shows the page where you can see logging from the device. It covers SMS, device information, call logs, network traffic, location details, etc.
Zscaler’s concerns:
In any other context, an application with these capabilities would clearly be labelled as spyware. At the vendor's (
https://smstrackerweb.com/download.php) they are selling a repackaged version of this app which has the same functionality but does not leave an icon on the device, thus making it more stealthy and harder to detect following installation. This version also does not contain the notification icon or privacy policy screen. Why the transparency? What audience is this version targeting?
This same application could also serve generic template for other spyware projects by being wrapped with other code to provide the core functionality needed to create another malicious app.
This type of app clearly shows the powerful level of access that can be granted to Android apps, so long as users grant permission. An app can access SMS, call logs, network traffic, hardware details, screen details etc. Always carefully read the permissions requested by an application before installing it on your device.
The vendor is promoting this application as a tool for monitoring the mobile activities of your children. However, this same app would be a very effective tool for spying on someone once installed on their phone. You just need to install the app on the device which you want to spy and you are done. All the information about the device and all call and SMS logs can then be remotely monitored.
Moreover, all of the user's private data is stored on the vendor's server. What guarantees are in place that the private data will remain private? In the increasingly common enterprise world of “Bring Your Own Device” (BYOD), such applications could be leveraged to expose corporate contact lists, email, browsing information and collect private data from corporate apps in the workplace. Enterprises often block access to 'non-official' app stores to prevent the installation of such apps, but this illustrates that such a restriction is no guaruntee that spyware can't be installed from an official source.
Virustotal scan results:
The application available from the vendor site (smstracker.com):
The Google Play store’s version:
Interestingly, despite virtually the same functionality, far fewer AV vendors flag the Google Play version as malicious.
- Viral