 |
| Link to Google Play Store for the fake app |
[UPDATE #2 - July 9, 2015] Google Android security team confirmed that the fake application was uploaded to the Google Play Developer Console by the miscreants.
Google Play Developer Console enables developers to easily publish and distribute their applications directly to users of Android-compatible phones
However, as per Google's Android team the fake app did not make it to the official Google Play Store as Google's security system flagged the fake app during scanning.
Malware authors tend to follow one of the following two methods for malware development:
- Create a malware app from scratch.
- Compromise a legit app by embedding malicious modules into it.
Spoofed Functionality and Ads:
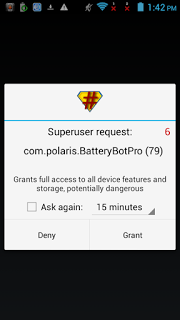
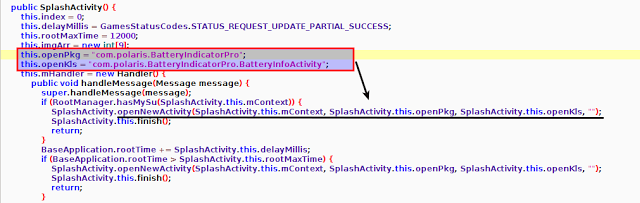
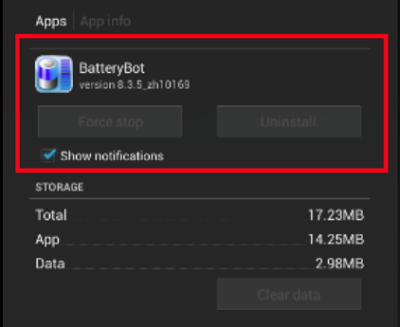
We came across a malicious app recently that followed this path. This time the spoofed app was a copy of a legit app named BatteryBot Pro. The spoofed app had the package name of 'com.polaris.BatteryIndicatorPro' and was removed from the Play Store as soon as Google became aware of it's malicious intent.
We also saw a spoofed version of BatteryBot Pro available for free during our research. The actual price of BatteryBotPro on official Play Store is Rs.179.99. The legit BatteryBotPro app demanded for minimal permissions as shown below:
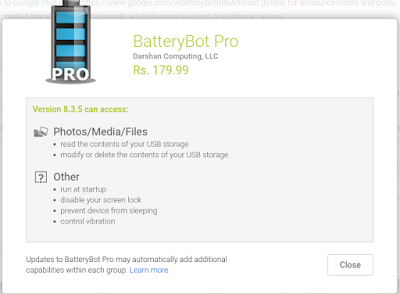 |
| Legit app permissions |
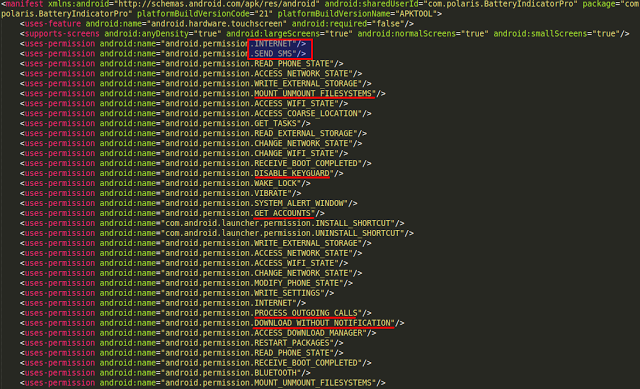 |
| Permission requested by Malware |
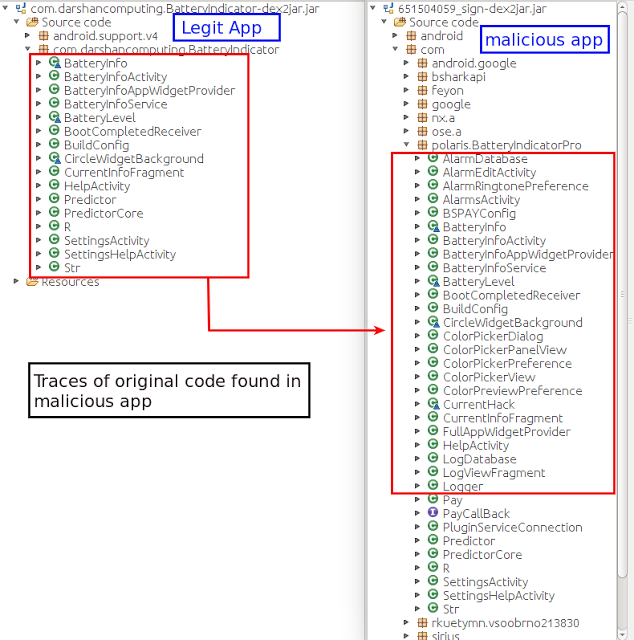 |
| legit app vs fake app |
 |
| Request for Administrator access |
 |
| opening BatteryPro screen |
ClickFraud and AdFraud activity
Though the app seems to be working normally, at the back-end it tried to load various ad libraries, ultimately delivering a click fraud campaign.
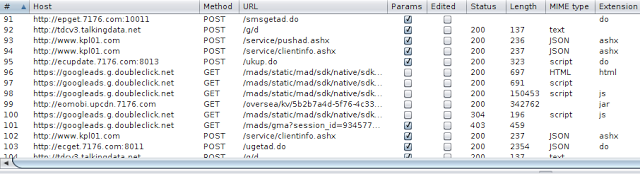 |
| Requests sent in back-end |
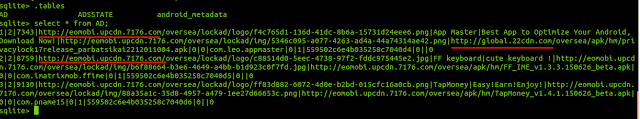 |
| Hard-coded URLs in database |
-Memory available in deviceThe following screenshot shows the data being collected.
-IMEI
-Phone Operator
-Location
-Langauge
-Phone Model
-Sim Card availability
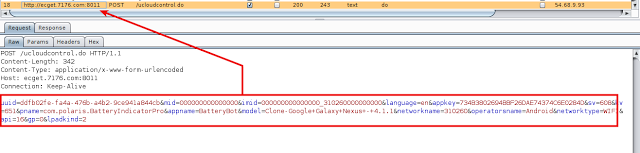 |
| Parameters sent to server |
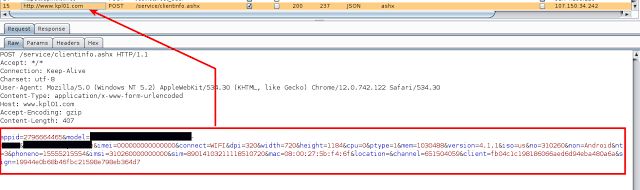 |
| Parameters sent to server |
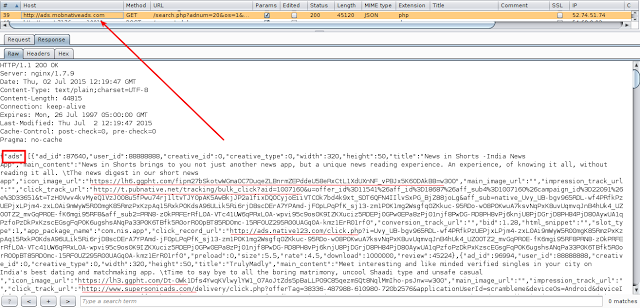 |
| Response from server containing ad URL |
The malicious app then downloads and installs additional malicious APKs without the user's consent:
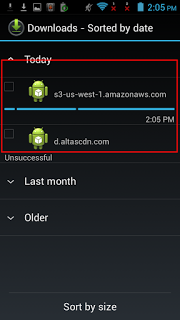 |
| Downloaded Apps by malware |
 |
| Pop up Ads |
This malware was not only built with the purpose of displaying ads, it was also designed with more evil intentions.
Sending SMS messages:
The main Activity Screen is identical to original app but when the user clicks on "View Battery Use", the malware sends a few requests to its Command & Control server to retrieve short codes. These short codes were premium rate SMS numbers where a message was sent. This will result in financial loss to the affected user.
Requests sent to server can be seen below:
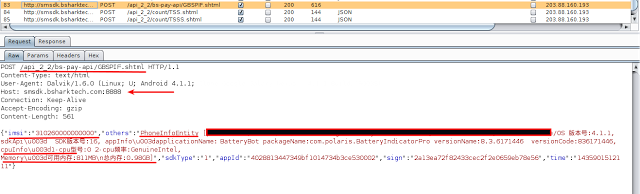 |
| Device info sent in request |
Though the content was encoded, we did not have to work hard to determine what was sent as the malware developer forgot to remove the logs. The server responds with short codes that are used for sending messages. The following screenshot shows a premium SMS response received from the server.
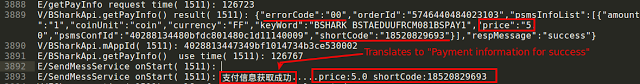 |
| Logs showing server response |
 |
| Uninstall not possible |
While in some of the scenarios we were able to manually delete the app, the malware authors have taken care of ensure persistence. The malware silently installs an app with a package name of com.nb.superuser, which runs as a different thread and resides on the device even if the app is forcefully deleted.
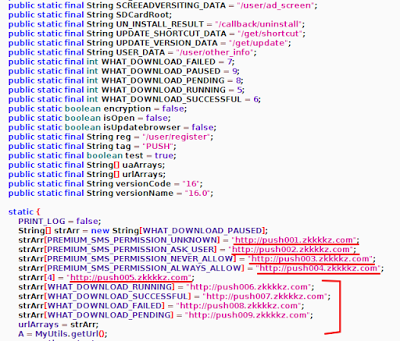
This acts as a service and sends requests to hard-coded URLs found in the app.
The screenshot below shows the hard coded URLs.
 |
| Hard-coded URLs |
Conclusion:
The Malware we saw in this blog was designed with multiple evil intentions including ClickFraud, AdFraud, Premium rate SMS fraud and the download & installation of additional malicious APKs.
The ThreatLabZ team will continue monitoring new mobile malware threats and ensure protection for Zscaler customers.







