When I was analyzed the PHP scripts used for the "Hot Video" pages, I had to find a way to deobfuscate the PHP code. There are many tools and online services to obfuscate PHP, but very few to deobfuscate it.
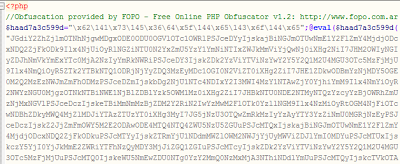 |
| Obfuscated PHP code: one big eval() |
PHP obfuscation is generally done with:
- Base64 encoding
- Encoding strings into hexadecimal and octal values
- Assigning functions to variables
- Multiple calls to eval()
Evalhook
This code can be deobfuscated by hand, but it takes multiple iterations and can be time-consuming. Fortunately, Steffan Esser wrote evalhook to make deobfuscation easier. His article about the tool describes how it works. Basically, it is a library used with PHP to render code that is executed by the eval() function.
There are no instructions for compiling the source code, so it took me a little bit of time to understand all the necessary steps to use the code on CentOS5. Here are basic instructions to compile the code.
First, you need:
- PHP >= v5.2
- php-devel
- PHP Zend Optimizer
CentOS5 comes with PHP 5.1, so you will need to obtain a newer version from another YUM repository. I used AtomicCorp to install the new PHP version and Zend.
Then, run these commands:
tar xvfz evalhook-0.1.tar.gz cd evalhook phpize ./configure make sudo make install
Now, you can use the evahlhook library to deobfuscate PHP files.
$ php -d extension=evalhook.so encoded_script.php
The only inconvenience I had to deal with when using evalhook, was that the resulting code still has strings encoded with hexadecimal and octal. So I wrote a small (and ugly!) Perl script to parse these strings into ASCII. Download strings.pl if you're interested in using it.
perl strings.pl source.php target.php
-- Julien




