I was fortunate enough to find a hijacked site which was being used to host fake "Hot video" pages, which I've blogged about before. However, this time around, the site had directory listings enabled. As such, I could view all the files used in the attack, including source code of the php files which display the fake video page and redirect users to a malicious pages. This provided insight into how the attack actually works.
Here is the list of interesting files in the /images/ directory:
- error_log - somebody tried to cover their tracks?
- news.dot - template for the Hot video page
- sitemap.php - displays a list of spam pages from other domains
- sites.txt - list of spam pages from other domains
- key.txt - a list of popular Google searches
- news.txt - log of crawler visits
- .news/ - folder containing thousands of spam pages
- .cch/ - folder containing thousands of spam pages
- g------.php (censored) and a few similar pages - execute external commands and upload files
- .sys.php - execute any PHP code and upload file
- page.php - displays the "Hot Video" page
- news.php - display the "Hot Video" page
- style.css - style sheet used on fake video page
- load.swf - Flash file which redirects the user to the malicious page
- player.gif - image of the fake Youtube video
Here are some information about some of the files.
error_log
This file shows a series of PHP errors. On the website, it contained a list of rmdir (remove a local folder) commands that had failed. It appears that somebody had attempted to delete the folders which contain the spam pages, which may have resulted from a failed attempt to clean a site by the webmaster, or perhaps a failed attempt to cover the hijacking by the attacker.
| Failed attempt to remove the folder containing the spam pages. |
sitemap.php, sites.txt key.txt
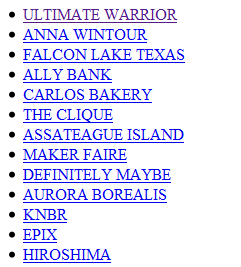
key.txt contains the list of popular searches from Google Hot Trends. A spam page is created for each of the searches.
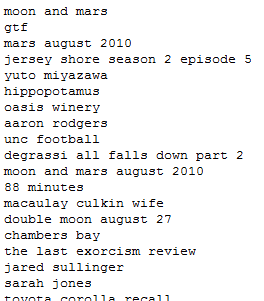 |
| List of popular searches |
The file reviewed, contained 8,000 popular searches.
sites.txt contains a list of hijacked sites which host spam pages. There are 139 domains listed.
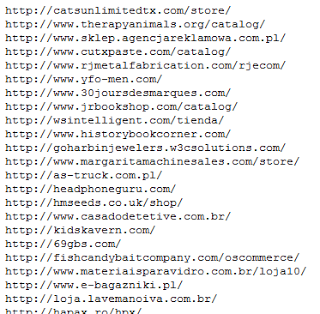 |
| List of hijacked sites hosting spam pages |
These 2 text files are used by sitemap.php to generate HTML pages with links to a total of 1,112,000 (8,000 x 139) spam pages.
 |
| HTML links to spam pages |
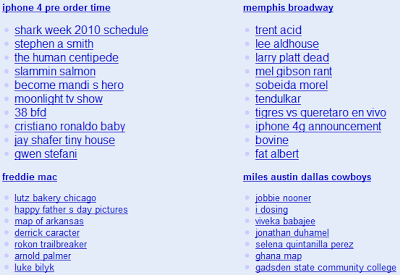
sitemap.php generates different lists each time the page is accessed and shows a few hundred links each time.
 |
| Part of the sitemap.php PHP source code |
The source shows that the same script, news.php, is used on all the 139 domains to display the fake video pages.
news.txt
news.txt contains the logs from search engine crawlers that have accessed the spam page news.php.
 |
| Information about crawlers accessing he spam pages |
The log file contained 29,983 lines. Google started to crawl the spam pages on August 15th. Here is the breakdown of crawler access:
- Google: 29,402
- Yahoo!: 580
- MSN: 1
98% of the crawler access to this page was done by Google, so it is not surprising that Google search results contained more spam links than Yahoo! or Bing.
Bing visited the spam page on September 6th, and Yahoo! for the first time on August 27th, 12 days after Google. This plays well with what I've described before: Yahoo! is late to add spam pages to its search results, and Bing does not seem to contain any.
.news/
This folder contains about 25,000 pages.
 |
| Spam pages |
The file name is based on the popular searches. For each search, there is a -new.html file, a -key.html file, and a .html file.
The -new.html and -key.html pages look similar. The -new.html files contain links to the malicious "Hot Video" page on other domains, whereas -key.html files contain links to the fake pages on the same domain, for example news.php?page=tour+de+francecheck=f7b972cf78d306834a08b9655bff1822
 |
| Links to "Hot Video" pages |
The 3rd file contains a spam page, the same type we've seen for other blackhat spam SEO attacks.
 |
| Spam page |
The content of these 3 files is combined to create the overall "Hot Video" spam page.
news.dot
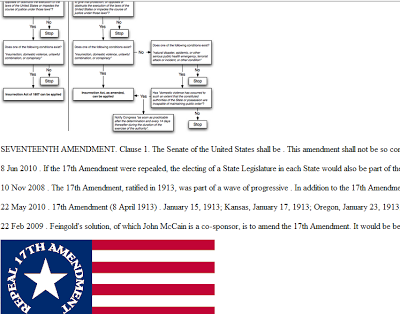
This is the template for the "Hot Video" spam page.There are 4 main sections in the template:
- the fake Youtube page, with the flash file load.swf to redirect users to the malicious site, player.gif for the picture of the fake Video player and style.css for the style sheet
- a list of links to "Hot Video" pages on other domains
- a list of links to "Hot Video" pages on the same domain
- spam content for a specific search
 |
| HTML template |
news.php
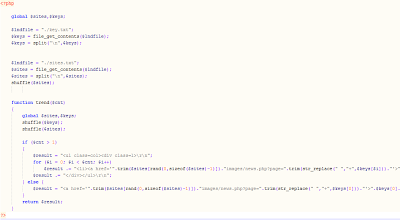
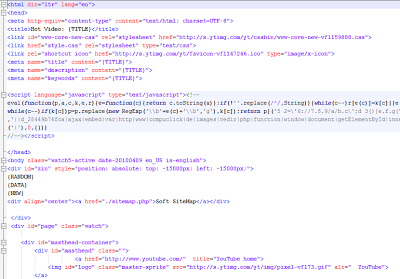
This PHP script is obfuscated with "FOPO - Free Online PHP Obfuscator v1.2: http://www.fopo.com.ar".
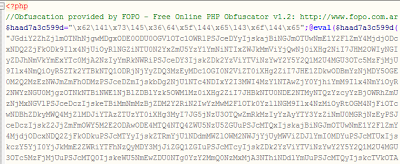 |
| Obfuscated PHP code |
Once de-obfuscated, the code is pretty simple.The script does two main actions:
- display the spam page
- create spam content
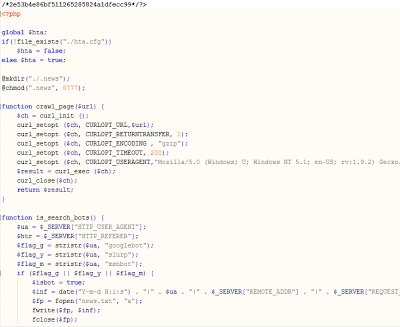 |
| De-ofuscated code for news.php |
The script displays the same page to crawlers and regular users. If the script detects a crawler, it also logs information about the crawl in news.txt. The detection is based on the user agent only - if the string slurp is found, it is the Yahoo crawler, GoogleBot is detected by the string googlebot, and Bing is detected with msnbot.
Requests to news.php are involve a query string which contains 2 parameters:
- the search term
- a hash
The search term is used to fill out the news.dot template with the corresponding spam content and links to other "Hot Video" pages. The hash is used to make sure the request is legitimate, and it is done against the search term and an internal key. This prevents researchers, for example, from accessing the page with random query strings.
Surprisingly, there is some "dead code". Checks are done for the presence of a file, or the value of an HTTP request, but nothing is then done with it.
If a new search term is used, and the corresponding files are not found in the news/ directory, the script generates it's own spam content. It does so by requesting the first 100 results of the search term from www.google.ru. It then uses the summary of each search result given by Google to build the page. Images are added to the page as well, but they come from a Bing image search for the given search terms. The links to other "Hot Video" pages is built from the files key.txt and sites.txt.
The "Hot Video" page does not require any command and control server. It can generate new spam pages automatically.
The redirection to the malicious site is ultimately done by another hijacked site, compuclick.de. Pages on this domain still redirect to fake AV pages, and they are not blocked by Google Safe browsing: www1.repulseguard10.co.cc, www1.repulseguard3.co.cc, etc.
I will detail the other files in later blog posts. Stay tuned!
-- Julien




