Vue d’ensemble
• Le CASB est un composant essentiel de la sécurité cloud moderne, qui offre visibilité, contrôle et protection des données et des applications cloud.
• Le CASB permet aux entreprises de prévenir les fuites de données, d’assurer la conformité, d’atténuer les menaces et d’identifier l’informatique fantôme.
• Sans CASB, les entreprises s’exposent à des risques accrus liés à l’utilisation du cloud, aux erreurs de configuration et aux activités malveillantes.
• La solution CASB idéale est multimode, combinant des contrôles inline et via API pour une protection complète des données et contre les menaces.
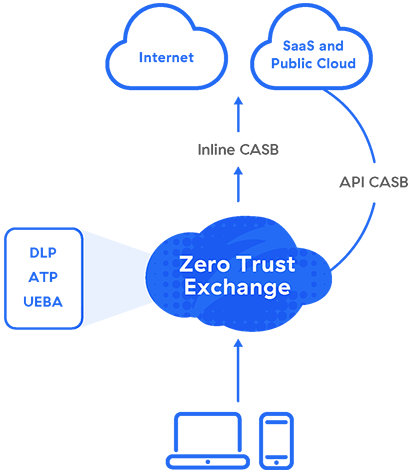
• Zscaler CASB intègre des capacités de sécurité avancées dans une architecture Zero Trust afin d’offrir une protection cloud unifiée et évolutive.
Pourquoi un CASB est-il nécessaire aujourd’hui ?
Face à la généralisation du cloud, les CASB se sont imposés comme un élément central de la sécurité des entreprises, assurant des fonctions de cybersécurité, de contrôle des accès et de protection des données. Ils vous redonnent le contrôle des données de l’entreprise, en transit comme au repos, au sein des plateformes et applications cloud. Les CASB sont essentiels, car :
- La croissance des plateformes et des applications cloud (par exemple, Microsoft 365, Salesforce) a considérablement réduit l’efficacité des outils de sécurité réseau traditionnels, tels que les pare-feu des data centers.
- Les équipes informatiques ne disposent plus du contrôle qu’elles avaient autrefois. Presque tout le monde peut choisir et utiliser une nouvelle application cloud, et le service informatique ne peut pas gérer manuellement les contrôles d’accès granulaires des utilisateurs à cette échelle.
- Ils peuvent appliquer des politiques pour contrôler l’informatique fantôme, assurer la protection contre la perte de données (DLP), la gestion de la posture de sécurité des données (DSPM) et la protection contre les menaces avancées.
Rôle des CASB pour les entreprises
En offrant une visibilité sur les activités, l’application des politiques de sécurité, la détection des menaces et la protection des données, les CASB permettent aux entreprises d’adopter le cloud en toute sérénité tout en conservant le contrôle et en respectant les exigences réglementaires. Examinons de plus près quelques avantages concrets d’un CASB.
Avantages du CASB
Une solution CASB efficace apporte des bénéfices clés dans le cadre d’une stratégie globale de sécurité cloud :
Visibilité sur l’informatique fantôme et les risques
Face à l’essor du télétravail et du BYOD, les entreprises ont besoin d’une visibilité claire sur les utilisateurs, les appareils et les applications SaaS qui accèdent à leurs environnements cloud. Simultanément, le risque d’accès non autorisé monte en flèche. Un CASB identifie l’utilisation des applications cloud de votre entreprise, génère des rapports sur les dépenses cloud et évalue les risques pour vous aider à créer et à maintenir des politiques d’accès appropriées.
Gestion de l’utilisation du cloud
L’utilisation du cloud peut être soumise à divers mandats de conformité, en particulier dans les secteurs fortement réglementés tels que les services financiers, la santé et le secteur public. Un CASB peut identifier les principaux facteurs de risque de votre secteur et définir des politiques strictes de protection des données pour assurer et maintenir la conformité au sein de votre entreprise.
Sécurité des données et DLP
Le volume des données mondiales double tous les deux ans, et le risque lié aux données augmente en conséquence. Associer un CASB à une DLP cloud permet à la fois d’identifier et de corriger les risques potentiels. En disposant d’une visibilité sur les contenus sensibles qui transitent vers, depuis ou entre les environnements cloud, vous êtes mieux à même d’identifier les incidents, d’appliquer les politiques et de protéger les données.
Prévention des menaces
Dans l’écosystème informatique actuel, les ressources cloud sont généralement les plus vulnérables. Grâce aux analyses comportementales et aux renseignements sur les menaces, vous pouvez rapidement détecter et corriger les activités suspectes, protéger les applications et les données cloud, et renforcer la posture globale de sécurité de votre entreprise.
Comment mettre en œuvre un CASB
Au plus haut niveau, la mise en œuvre d’un CASB consiste à évaluer vos besoins, à les adapter au bon produit, à le configurer de la manière qui convient le mieux à vos systèmes et à effectuer une surveillance et des audits continus. Vous pouvez considérer la mise en œuvre en cinq étapes :
- Analysez votre environnement et établissez un plan. Faites l’inventaire des services et applications cloud utilisés, des risques associés et de vos exigences de sécurité et de conformité.
- Choisissez la solution CASB la mieux adaptée à vos besoins. Trouver le bon fournisseur est tout aussi important que choisir le bon produit — privilégiez un partenaire en qui vous pouvez avoir confiance.
- Intégrez le CASB à vos services cloud et à vos annuaires d’utilisateurs. Utilisez le SSO pour un accès utilisateur sécurisé et une authentification transparente.
- Configurez des politiques d’accès, de partage de données, de DLP et de sécurité. Selon votre secteur, vos politiques de chiffrement peuvent demander des précautions spécifiques.
- Activez la surveillance en temps réel et la détection des menaces. Vous devrez également revoir et actualiser régulièrement vos politiques à mesure que les besoins de votre entreprise évoluent.
Comment fonctionnent les CASB ?
Les solutions CASB peuvent être déployées sur site sous forme logicielle ou matérielle, mais elles sont plus efficaces en mode cloud, offrant une meilleure évolutivité, des coûts réduits et une gestion simplifiée. Quel que soit le modèle de déploiement, les CASB peuvent fonctionner en mode proxy (direct ou inverse), via API, ou combiner les deux — on parle alors de CASB multimode.
Proxy
Parce qu’il s’insère directement dans le flux de données, le CASB idéal repose sur une architecture proxy cloud. Les proxys directs sont plus souvent utilisés avec les CASB, garantissant la confidentialité et la sécurité des utilisateurs du côté client.
Un proxy direct intercepte les demandes de services cloud sur le chemin vers leur destination. Ensuite, en fonction de votre politique, le CASB applique le mappage des informations d’identification et l’authentification unique (SSO), le profilage de la posture de l’appareil, la journalisation, les alertes, la détection des malwares, le chiffrement et la tokenisation.
API
Si un proxy inline intercepte les données en transit, les données au repos dans le cloud nécessitent une protection hors bande, fournie par les intégrations API des fournisseurs CASB avec les services cloud.
Qu’est-ce qu’un CASB multimode ?
En mode proxy, les CASB appliquent les politiques de sécurité inline qui bloquent en temps réel les fuites de données et les malwares. Ils peuvent également s’intégrer aux API pour analyser le contenu des applications SaaS, afin d’identifier les motifs de données sensibles et de réagir aux menaces telles que les ransomwares. Plus récemment, les intégrations API ont été utilisées pour le DSPM, permettant aux CASB de corriger les erreurs de configuration des applications.
Les CASB qui proposent à la fois les modes proxy et API sont appelés CASB multimodes. Au-delà de la sécurisation des SaaS, ils peuvent protéger les IaaS tels que Microsoft Azure et AWS S3. Et plutôt que de déployer un CASB comme un autre produit ponctuel, vous pouvez le déployer dans le cadre d’une plateforme SSE pour garantir une sécurité cohérente, de meilleures performances et une administration regroupée.
Que dit Gartner à propos du CASB ?
Gartner a défini le « CASB » pour la première fois en 2012, lorsque les entreprises utilisaient principalement cette technologie pour contrôler l’informatique fantôme.
À mesure que ses capacités ont convergé avec celles des passerelles web sécurisées (SWG), Gartner a défini en 2019 le concept de Secure Access Service Edge (SASE), un ensemble de services cloud combinant des fonctions WAN complètes et des capacités avancées de sécurité réseau (SWG, CASB, FWaaSet ZTNA) pour répondre aux besoins d’accès sécurisé dynamiques des entreprises numériques.
En 2021, Gartner a isolé la composante sécurité du SASE sous le nom de Security Service Edge (SSE), reflétant les efforts croissants visant à simplifier des architectures de sécurité complexes et fragmentées.
CASB et SASE
Les fonctions CASB et SASE se complètent, le CASB sécurisant les interactions et les flux de données dans le cloud, tandis que le SASE intègre plus largement la sécurité, la mise en réseau et le contrôle d’accès dans le cloud. Le SASE inclut le CASB par définition, permettant aux entreprises d’appliquer leurs politiques et de sécuriser les données dans le cadre de leur architecture réseau.
Zscaler est un leader du Gartner Magic Quadrant pour le Security Service Edge (SSE).
Principaux cas d’utilisation de CASB
1. Identifier et contrôler l’informatique fantôme
Lorsque vos utilisateurs stockent et partagent des fichiers et des données d’entreprise dans des applications cloud non approuvées, la sécurité de vos données est impactée. Pour contrer ce phénomène, vous devez comprendre et sécuriser l’utilisation du cloud au sein de votre entreprise.
Zscaler CASB identifie automatiquement l’informatique fantôme, dévoilant les applications à risque que visitent vos utilisateurs. Des politiques automatisées et facilement configurables permettent ensuite d’appliquer diverses mesures (par exemple, autoriser ou bloquer, empêcher le téléchargement, restreindre l’utilisation) à des applications individuelles ou à des catégories d’applications.
2. Sécuriser les entités SaaS non professionnelles
Les utilisateurs peuvent utiliser des instances autorisées et non autorisées d’applications telles que Google
Drive. Les approches généralistes, qui autorisent ou bloquent entièrement l’application, peuvent respectivement encourager les partages inappropriés ou nuire à la productivité.
Zscaler CASB peut faire la distinction entre les entités SaaS autorisées et les instances non autorisées, en appliquant sur chacune d’elle une politique appropriée. Les contrôles préconfigurés des locataires SaaS permettent une correction automatisée et en temps réel.
3. Contrôler le partage risqué de fichiers
Les applications cloud permettent un partage et une collaboration sans précédent. Par conséquent, vos équipes de sécurité doivent savoir qui partage quoi dans les applications autorisées, pour éviter que des individus malveillants ne s’emparent de vos données.
La gestion de la collaboration est une fonctionnalité essentielle de tout CASB efficace. Zscaler CASB parcourt rapidement et de manière récurrente les fichiers de vos locataires SaaS afin d’identifier les données sensibles, de vérifier les utilisateurs avec lesquels les fichiers sont partagés et de réagir automatiquement aux partages à risque si nécessaire.
4. Remédier aux erreurs de configurations SaaS
Lors du déploiement et de la gestion d’une application cloud, une configuration précise est essentielle pour garantir le bon fonctionnement et la sécurité de l’application. Les erreurs de configuration nuisent à votre hygiène de sécurité et peuvent rapidement exposer des données sensibles.
Zscaler DSPM s’intègre à vos environnements SaaS via API afin de détecter les erreurs de configuration susceptibles de compromettre la conformité réglementaire.
5. Prévenir les fuites de données
Outre les erreurs de configuration des ressources cloud susceptibles de générer des violations et des fuites de données, vous devez identifier et contrôler les modèles de données sensibles dans le cloud. Un grand nombre de ces données sont réglementées par des cadres tels que HIPAA, PCI DSS, RGPD, et bien d’autres.
La plateforme de sécurité cloud native de Zscaler assure une protection unifiée des données grâce aux capacités Cloud DLP et CASB. Elle garantit une configuration sécurisée des applications cloud afin de prévenir les fuites de données et la non-conformité, en s’appuyant sur des techniques avancées de classification pour identifier et protéger les données sensibles où qu’elles transitent.
6. Prévenir les attaques réussies
Une fois qu’un fichier infecté a contourné la sécurité de votre entreprise et atteint l’une de vos applications cloud autorisées, il peut rapidement se propager aux applications et aux appareils connectés d’autres utilisateurs. C’est pourquoi vous devez disposer d’un moyen de vous défendre contre les menaces en temps réel, tant au moment du chargement qu’au repos.
Zscaler CASB bloque la progression des malwares grâce à des capacités de protection contre les menaces avancées, notamment :
- un proxy en temps réel pour empêcher le chargement de fichiers malveillants sur le cloud ;
- une analyse hors bande pour identifier les fichiers au repos et corriger les menaces ;
- Sandboxing cloudpour identifier les malwares, même zero-day
- Isolation du navigateur cloudsans agent pour sécuriser l’accès depuis des terminaux non gérés
Zscaler CASB
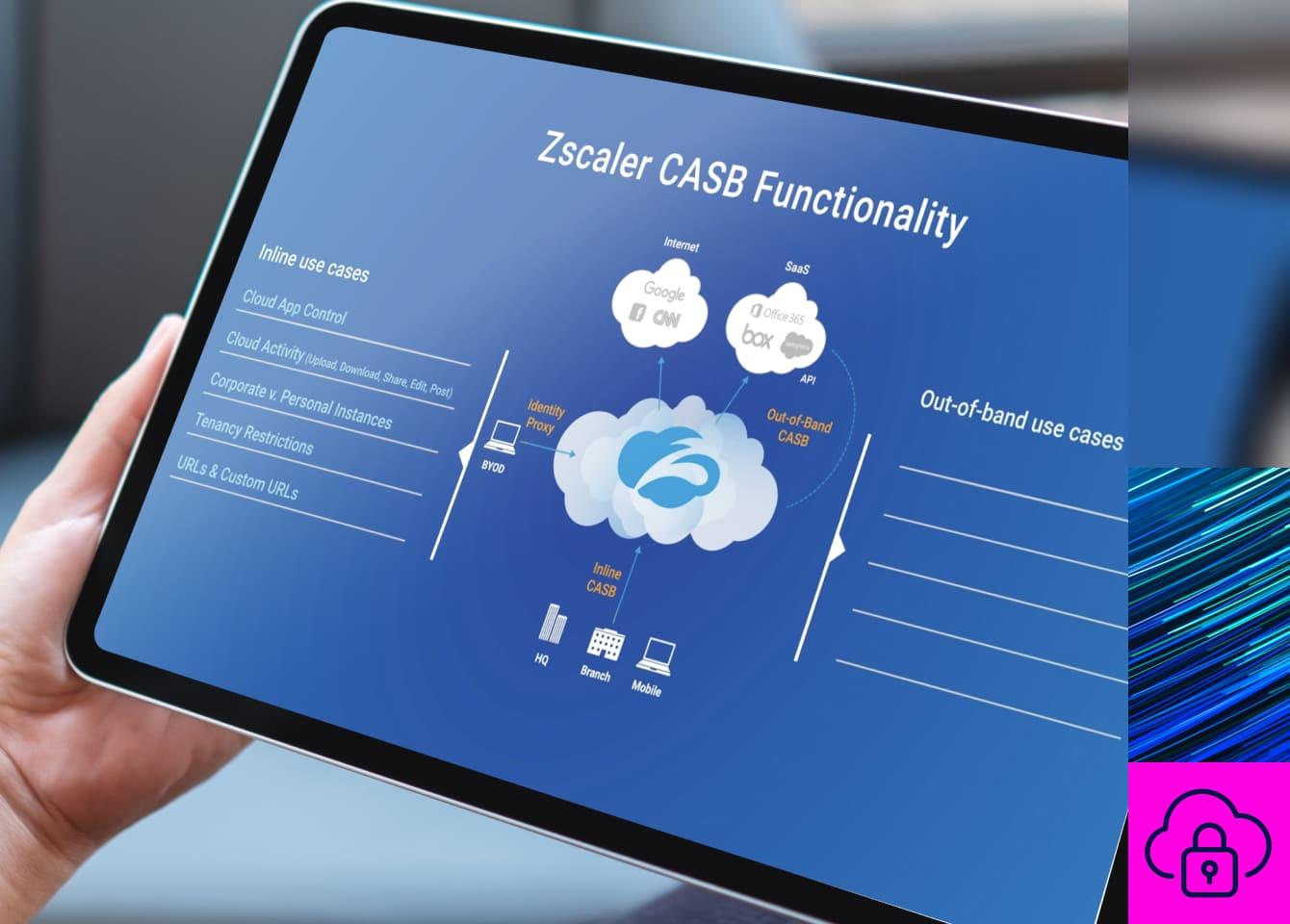
Zscaler fournit un CASB multimode en tant que service avec SWG, ZTNA, et plus encore dans le cadre de notre plateforme globale Zscaler Zero Trust Exchange™ afin de vous permettre de supprimer les produits ponctuels, de réduire la complexité informatique et d’inspecter le trafic en un seul passage. Les administrateurs n’ont qu’à configurer une politique automatisée pour garantir une sécurité cohérente sur tous les canaux de données dans le cloud.
Sécurité inline pour les données cloud en mouvement
Le proxy direct de haute performance et l’inspection SSL procurent une protection critique en temps réel :
- La détection de l’informatique fantôme et le contrôle des applications cloud identifient et sécurisent les applications non approuvées, sans nécessiter de journaux des périphériques réseau.
- Les mesures de DLP empêchent le chargement de données sensibles vers des applications approuvées et non approuvées.
- La protection contre les menaces avancées arrête les programmes malveillants connus et inconnus en temps réel grâce au sandboxing cloud optimisé par l’apprentissage automatique.
- L’isolation du navigateur diffuse les sessions sous forme de pixels pour le BYOD afin de prévenir toute fuite de données sans recourir à un proxy inverse.
Sécurité hors bande pour les données au repos
L’analyse basée sur les API des applications SaaS, des plateformes cloud et de leur contenu renforce automatiquement votre sécurité :
- Des dictionnaires de DLP prédéfinis et personnalisables identifient les données sensibles dans les applications SaaS et les clouds publics.
- La fonctionnalité de gestion de la collaboration recherche dans les applications les partages de fichiers à risque et les révoque conformément à la politique.
- Le cloud sandboxing analyse les données au repos afin d’identifier les malwares de type zero-day et les ransomwares, et d’agir contre ces derniers.
- La DSPM détecte et classe automatiquement les actifs de données sensibles ou à risque dans les environnements SaaS, PaaS, cloud public, sur site et LLM.
Renforcez la sécurité de vos applications SaaS avec Zscaler CASB.
Ressources suggérées
FAQ
Les solutions CASB sont indispensables pour les entreprises de toutes tailles qui s’appuient sur le cloud pour stocker des données sensibles, collaborer via des applications SaaS ou gérer leurs ressources cloud. Des secteurs comme la santé, la finance ou le secteur public en tirent un bénéfice particulier en raison d’exigences réglementaires strictes, mais les CASB sont tout aussi essentiels pour les entreprises qui adoptent le télétravail, le BYOD ou sont confrontées aux risques liés à l’informatique fantôme.
Le CASB (cloud access security broker) est une solution de sécurité qui applique des politiques entre les utilisateurs et les services cloud. Il aide les entreprises à protéger leurs données cloud, prévenir les fuites et réduire les menaces de sécurité. Les CASB offrent des fonctionnalités essentielles telles que la prévention de la perte de données (DLP), la découverte de l’informatique fantôme, l’application des exigences de conformité et une intégration transparente avec les plateformes SaaS et IaaS.
Pour choisir le CASB le mieux adapté, évaluez les besoins de votre entreprise en matière de sécurité du cloud, les risques actuels et les exigences de conformité. Recherchez des capacités telles que le déploiement multimode (proxy et intégrations API), la surveillance des données en temps réel, la DLP avancée, la prévention des menaces et le contrôle de l’informatique fantôme. Appuyez-vous sur un fournisseur de confiance qui offre évolutivité, simplicité de déploiement et intégration aux plateformes Security Service Edge (SSE).
Bien que les CASB assurent des fonctions essentielles de sécurité cloud, ils sont plus efficaces lorsqu’ils s’intègrent dans une stratégie de sécurité globale. Ils s’intègrent naturellement à des solutions telles que SWG (passerelles web sécurisées), ZTNA (accès réseau Zero Trust) et DSPM (gestion de la posture de sécurité des données) pour appliquer une protection unifiée. Déployer un CASB dans des architectures étendues telles que SASE ou SSE permet d’assurer une couverture de sécurité plus complète du cloud et du réseau.
Les CASB sont essentiels pour la visibilité sur l’informatique fantôme, car ils détectent automatiquement les applications utilisées sans l’approbation du service informatique. Ils aident ainsi les entreprises à contrôler les partages de fichiers à risque, appliquer des politiques d’accès appropriées, réduire les vulnérabilités et limiter l’exposition globale aux risques cloud.
Les solutions CASB multimodes combinent une protection inline (via proxy) et une analyse hors bande (via intégrations API). Cette double approche permet une application en temps réel des politiques afin de prévenir les fuites de données et les malwares, tout en offrant une visibilité sur les données au repos afin de détecter les erreurs de configuration et de gérer la conformité. Les CASB multimodes permettent aux entreprises de sécuriser les environnements SaaS et de cloud public.
Les CASB contribuent à assurer la conformité en identifiant les données sensibles soumises au RGPD ou à d’autres cadres réglementaires, puis en appliquant des politiques strictes à leur stockage, leur transmission et leur utilisation. Des fonctionnalités avancées comme le cloud DLP analysent les motifs de données réglementées, bloquent les accès non autorisés et traitent les comportements de fichiers à risque afin de respecter les exigences de conformité.
Les CASB renforcent la DLP en analysant de manière proactive les données sensibles qui circulent dans les applications cloud approuvées et non approuvées. Les capacités de proxy inline appliquent des politiques en temps réel sur les téléversements, les téléchargements et le partage de données, tandis que les intégrations API sécurisent les données au repos. Ensemble, ces fonctionnalités empêchent les fuites et les accès non autorisés aux données sensibles, et renforcent l’efficacité de la DLP cloud.