Zscaler Private Access (ZPA) and Zscaler Internet Access (ZIA) complement each other to secure Virtual Desktop Infrastructure (VDI) solutions. Like peanut butter and chocolate: Two great things that are great together.
A common question: Where should we replace our VDI with ZPA, and where should we leverage the combined solution? Peanut butter and chocolate might taste good when paired, but you can’t substitute one for the other. (Chocolate syrup on spring rolls? No. Just, no. Well, maybe chocolate mole sauce?) Analogously, VDI replacement makes sense in some ZPA scenarios, but doesn’t in others.
The answer lies in understanding why you use VDI in the first place. Do your current use cases and applications really still require VDI? Do all users use VDI or just a subset? Asking why and exploring the scope can help to move beyond the assumptions that flow from the traditional on-premise / on-network mindset.
Generally, organizations leverage VDI for one or more of the following reasons:
- Access granularity: Restricting users to only authorized applications
- Data residency restrictions: Ensuring data a) stays within the corporate boundary, and/or b) is never stored on the end-user’s device
- Traffic localization: Minimizing latency for heavyweight client-server interactions (e.g., database calls)
- Desktop management or reduction: Maintaining a clean desktop experience and ensuring a persistent desktop that users can access from multiple devices
- Software license reduction: Deploying software to a limited pool of virtual desktops, rather than all user devices
- Legacy application support: Enabling access to applications that require older OSes
- Traffic inspection: Using VDI to force all traffic through on-premise security stacks
If you’re considering option #1, ZPA can replace VDI and provide granular, least-privilege access for authorized users to specific applications. In addition, deploying ZPA with Private Service Edge can address option #2a, ensuring that both the control plane and data plane stay entirely within your security boundary for private traffic. (And Zscaler’s upcoming integration of Cloud Browser Isolation with ZPA will start to address option #2b, as well.) For all of the other options, you can add Zscaler to your existing VDI environment to augment the benefits described above.
Whether your VDI environment is on-premise (e.g., Citrix XenDesktop, VMware Horizon) or Desktop-as-a-Service (e.g., Amazon WorkSpaces, Windows Virtual Desktop), Zscaler lets you layer granular, cloud-native zero trust access over virtual desktop offerings. In this great-tastes-that-go-better-together scenario, Zscaler provides centralized visibility and control for users accessing resources from VDI environments. Installing the Zscaler Client Connector on virtual desktop instances gives visibility and centralized control over what the user can access from there.
We have real-world examples of Zscaler customers deploying Zscaler Client Connector in their DaaS environments to protect external and SaaS traffic, via Zscaler Internet Access (ZIA), as well as traffic to private applications via Zscaler Private Access (ZPA). This combined solution offers many benefits: centralized visibility and control, single access control policy config for VDI as well as other forms of access, and consistent user experience—with the caveat that you must have dedicated single-user VDI instances (i.e., what Amazon calls Windows BYOL).
An example where this approach makes sense is enabling employees to access private applications directly from their own devices, while restricting third parties to VDI-only access. You can extend ZPA’s centralized visibility and control to both user communities, as illustrated below in Figure 1.
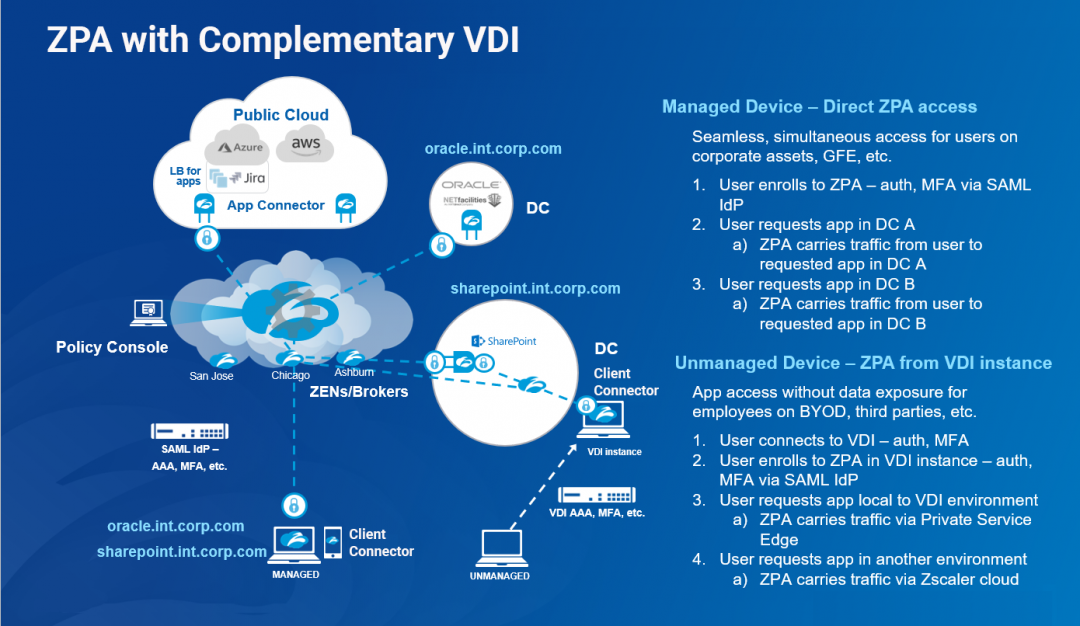
Figure 1. How ZPA complements VDI deployments.
Even if we don’t replace VDI for all users, often we find that there are many user communities we can serve more simply with ZPA. For financial advisors and insurance agents, many firms have moved to web-based apps (DocuSign, etc.). So there may no longer be a hard requirement for those thousands of users to have VDI. This often requires going beyond the boundaries of the network and security teams and engaging enterprise architects, application owners, etc.
ZPA and VDI go great together
Replacing or augmenting VDI with ZPA requires a deeper understanding of why you use VDI, and whether it is still a necessary part of your environment. Often, Zscaler’s Zero Trust Exchange trust can remove the necessity for VDI by providing direct access to internal and cloud apps, even if the user is accessing from outside the perimeter.
Dig into your assumptions. Replace where you can, combine where it makes more sense. And let me know if you think mole sauce goes well with spring rolls.
For additional resources, please visit our Work-from-Anywhere Content Hub.





