| Snort Signature |
| alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"ET CURRENT_EVENTS Probable malicious download from e-mail link /1.php"; flow:established,to_server; urilen:8; content:"/1.php?r"; http_uri; content:!"Referer|3a 20|"; http_header; flowbits:set,et.exploitkitlanding; classtype:bad-unknown; sid:2019894; rev:1;) |
Below are the compromised websites observed, which have been found to be serving multiple malware families.
| Compromised wordpress websites |
| airlessspraysupplies[.]com/wp-includes/1[.]php?r |
| altero[.]be/1[.]php?r |
| alzina[.]cat/1[.]php?r |
| angeladoesfood[.]com/wp-admin/1[.]php?r |
| apsmiles[.]com/wp-content/themes/rfx/1[.]php?r |
| architecture[.]web[.]auth[.]gr/1[.]php?r |
| augustgifford[.]com/wp-admin/1[.]php?r |
| bankruptcy-software[.]com/wp-content/themes/classic/1[.]php?r |
| bernie[.]jshall[.]net/wp-content/themes/twentytwelve/1[.]php?r |
| beta[.]pescariusports[.]ro/images/1[.]php?r |
| blackwellanddenton[.]com/components/com_contact/1[.]php?r |
| blog[,]longboardsicecream[.]com/wp-content/plugins/1[.]php?r |
| blog[.]ridici-jednotky[.]cz/wp-content/plugins/simple4us/1[.]php?r |
| blog[.]topdealslondon[.]com/wp-content/uploads/1[.]php?r |
| cartorioalbuquerque[.]com[.]br/images/1[.]php?r |
| climatechange[.]mobi/images/1[.]php?r |
| core[.]is/1[.]php?r |
| couponshare[.]me/1[.]php?r |
| dannygill[.]co[.]uk/wp-content/plugins/simple4us/1[.]php?r |
| dlaciebie[.]org/wp-admin/1[.]php?r |
| geototal[.]az/en/ru/engine/editor/scripts/common/codemirror/mode/xml/1[.]php?r |
| kba1f9684c70[.]nazwa[.]pl/images/1[.]php?r |
| linkleads[.]vn/1[.]php?r |
| lionel[.]my/wp-content/plugins/akismet/1[.]php?r |
| livedoor[.]eu/1[.]php?r |
| ludovicharollais[.]org/wp-admin/1[.]php?r |
| m11[.]mobi/images/1[.]php?r |
| matthewkarant[.]com/wp-content/themes/twentynine/1[.]php?r |
| mcymbethel[.]com[.]ar/modules/mod_ariimageslider/1[.]php?r |
| merklab[.]eu/1[.]php?r |
| mitoyotaseagarrota[.]com/components/com_banners/1[.]php?r |
| mlmassagetherapy[.]com[.]au/wp-content/uploads/1[.]php?r |
| monitoring[.]sensomedia[.]hu/1[.]php?r |
| newwww[.]r11mis[.]be/images/1[.]php?r |
| odelia-coaching[.]co[.]il/wp-content/plugins/google-sitemap-generator/1[.]php?r |
| odelia-coaching[.]co[.]il/wp-content/plugins/google-sitemap-generator/1[.]php?r |
| osp[.]ruszow[.]liu[.]pl/images/1[.]php?r |
| pms[.]isovn[.]net/images/1[.]php?r |
| prodvizhenie-sajta[.]com/images/1[.]php?r |
| redmine[.]sensomedia[.]hu/1[.]php?r |
| salihajszalon[.]hu/1[.]php?r |
| sonicboommusic[.]com[.]au/components/com_banners/1[.]php?r |
| sparkledesign[.]ro/1[.]php?r |
| thebestcookbooks[.]co[.]uk/wp-content/plugins/1[.]php?r |
| thefoodstudio[.]co[.]nz/wp-content/themes/food-cook/1[.]php?r |
| thietkekientruca4[.]vn/1[.]php?r |
| treasurething[.]com/wp-includes/pomo/1[.]php?r |
| tsv-penzberg[.]de/wp-admin/1[.]php?r |
| turbomarketingteam[.]com/1[.]php?r |
| tusengangerstarkare[.]ingelaclarin[.]se/wp-admin/1[.]php?r |
| twobyones[.]com/1[.]php?r |
| xhmeiastokyma[.]gr/1[.]php?r |
| youreverlastingmemories[.]co[.]uk/1[.]php?r |
These compromised WordPress sites may have been used by Exploit Kit (EK) authors as drop sites for serving malware. Another potential attack vector could involve email spam.
| ZIP MD5 | ZIPFILE NAME |
| 2f225283c66032c9f7dcb44f42697246 | fax_20141204_385.pdf.zip |
| 6696527bfda97b1473d1047117ded8d6 | invoice.pdf.zip |
| 93babef06bfd93bcbb5065c445fb57d4 | label_08122014_23.pdf.zip |
| bea9be813bb7df579d5be3e4543dc6a4 | payment_details9427923.pdf.zip |
| 1159fe7ec4d0b2cfde57dfb28b98f0c9 | ePackage_12092014_42.pdf.zip |
| 038710b2029046c39ca4082e2c34f9b3 | wav_voice20141208.zip |
| ec35acdbe331c73e5e6883ebc08f896d | payment_invoice_182734.pdf.zip |
| 8f00cfdf067b01462670212ba5874cdb | pdf_efax_9823612397.zip |
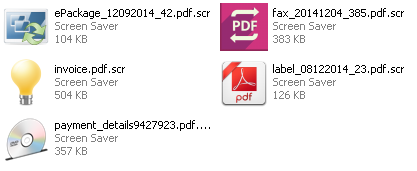
Lets take a look at the files after unzipping them. All of the files are Windows screen savers and include fake icons of legitimate software packages, to persuade the victims to click on them.
Downloaded files:
For this post we've chosen to focus on the Hencitor malware. Hencitor’s typical behavior is to download additional malware onto the victim’s machine and execute it.
MD5: 6bb3b23ff3e736d499775120aa8d6ae2
VT Score: 9/56 (At the time of analysis)
Lets take a look at some important things noted while conducting dynamic analysis of this malware.
- Copies itself to
- "C:\Users\Win7 64Bit\AppData\Roaming\Windows\winlogin.exe”
- Creates autostart registry key entry
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run
- "winlogin” = "C:\Users\Win7 64Bit\AppData\Roaming\Windows\winlogin.exe”
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run
- Uses ping.exe to check the status of other devices and networks.
- cmd /D /R ping -n 10 localhost && del C:\payment_invoice_182734.pdf.scr.exe && start /B C:\Users\Win7 64Bit\AppData\Roaming\Windows\winlogin.exe && exit
- Creates a thread in following existing process on the system.
- C:\Windows\explorer.exe
- C:\Windows\System32\sppsvc.exe
- C:\Windows\System32\wbem\WmiPrvSE.exe
- C:\Windows\System32\conhost.exe
- Deletes itself after installation
- c:\payment_invoice_182734.pdf.scr.exe
- Malware seen to resolve couple of suspicious tor sites.
- o3qz25zwu4or5mak.tor2web[.]org
- o3qz25zwu4or5mak.tor2web[.]ru
-Stay Safe