Zscaler Blog
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Fortify Your Future: How Zscaler Drives a Modern Defensible Architecture for Supercharged Cyber Resilience
In today's hyper-connected world, cyber threats are not just a possibility, they're a relentless reality. From sophisticated nation-state actors to organised criminal groups, the adversaries are more advanced and persistent than ever. Traditional perimeter based security is simply inadequate, leaving organisations with an increased attack surface and vulnerable to breaches.
This escalating complexity demands a fundamental shift in how we approach cybersecurity. Enter the Australian Cyber Security Centre Foundations for Modern Defensible Architecture (MDA), a critical framework offering a strategic, layered blueprint for building contemporary cyber resilience. The MDA champions three core pillars: a Layered Architecture, comprehensive Zero Trust, and Secure-by-Design methodologies. At its core, Zscaler's Zero Trust Exchange was developed to support the implementation of these vital principles.
The MDA Blueprint: Beyond the Perimeter
The Modern Defensible Architecture isn't just about replacing existing perimeter controls with new stronger perimeter controls; it's about building a fortress from the inside out. It acknowledges that breaches are inevitable and focuses on minimising impact, containing threats, and ensuring business continuity.
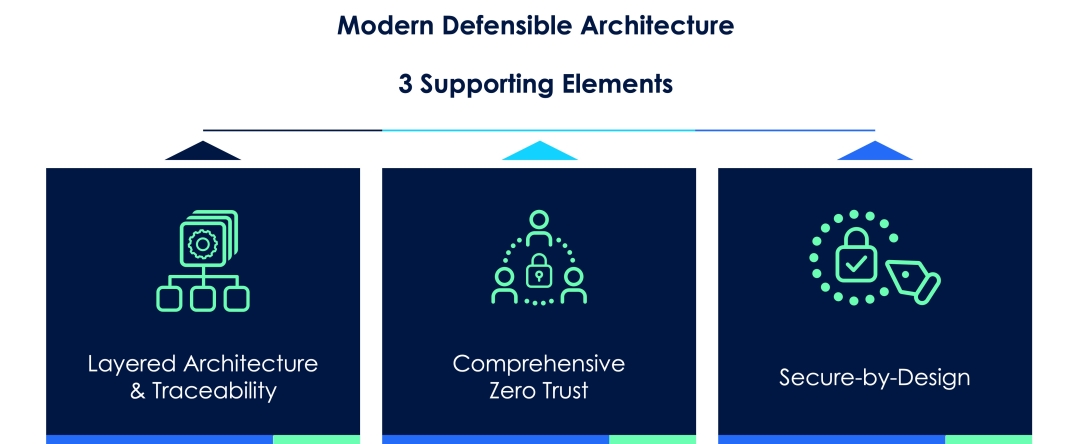
Its three pillars are:
- Layered Architecture and Traceability: Ensuring security controls are directly linked to business objectives and provide deep visibility.
- Comprehensive Zero Trust: Embracing "never trust, always verify", "assume breach", and "verify explicitly" principles for every interaction.
- Secure-by-Design: Integrating security from the outset of all development and operational processes, making it an inherent quality, not an afterthought.
These pillars are further supported by ten foundational capabilities, designed to create an environment of continuous security validation and adaptation.
Zscaler's Zero Trust Exchange: The Engine of MDA
Zscaler's cloud-native Zero Trust Exchange platform is uniquely positioned to help organisations achieve the MDA vision. It shifts traditional network security by connecting users directly to applications, not the network. This "never trust, always verify" model transforms security from a static perimeter defense to continuous verification of every user, device, and application interaction.
Here's how Zscaler provides the necessary components to build a robust and defensible architecture:
- Zscaler Internet Access (ZIA): For secure internet and SaaS access, inspecting all outbound traffic for threats and policy violations.
- Zscaler Private Access (ZPA): Providing zero trust access to internal private applications, making them "dark" to the public internet.
- Zscaler Digital Experience (ZDX): Offering end-to-end monitoring of user experience and application performance.
- Zscaler Client Connector (ZCC): The intelligent agent on endpoints that enforces policies and gathers crucial device posture.
- Zscaler Security Operations - Providing external attack surface management and continual risk, vulnerability and control context.
- Red Canary a Zscaler company: Provides 24x7 continuous security monitoring.
Powering MDA: Zscaler in Action
Let's look at how Zscaler directly contributes to some of the MDA's most critical foundations:
High Confidence Authentication (MDA Foundation 2)
Phishing-resistant and cryptographically bound authentication is crucial. Zscaler integrates seamlessly with your existing IdP, enforcing strong MFA for all user authentications. Beyond the user, the ZCC provides a critical layer of device authentication, establishing a secure, device-bound tunnel to the Zscaler cloud. This dual-layered approach ensures access is granted only to an authenticated user from an authenticated and compliant device.
Contextual Authorisation (MDA Foundation 3)
The MDA demands dynamic, real-time validation for every access request, factoring in user identity, device posture, location, and threat intelligence. Zscaler's platform excels here. Its policy engine acts as the central Policy Decision Point (PDP), aggregating "confidence signals" from your Identity Provider (IdP), the ZCC (device health), and real-time threat intelligence. This allows Zscaler to enforce granular, adaptive policies, adjusting access privileges based on the evolving risk profile, truly "never trust, always verify."
Reliable Asset Inventory (MDA Foundation 4)
Having a reliable asset inventory drives better management, visibility and decision making. A number of Zscaler modules provide near real time asset inventory information and/or the scanning of external assets to supplement existing approaches to CMDB management. This provides more accurate information regarding assets deployed within the organisation.
Reduced Attack Surface (MDA Foundation 6)
The MDA emphasises minimising exploitable entry points. ZPA dramatically shrinks your attack surface by making private applications invisible to the internet. Instead of exposing services via inbound firewall ports, ZPA establishes secure, outbound-initiated microtunnels, preventing reconnaissance and direct attacks. ZIA complements this by securing all internet-bound traffic, blocking malicious sites and preventing exploitation at the web gateway. Universal vulnerability management provides up to date context to support vulnerability and patching processes.
Continuous and Actionable Monitoring (MDA Foundation 10)
All Zscaler components provide detailed logging which can feed into an organisation's security analytics systems. Zscaler also has a 24x7 security monitoring service provided by Red Canary, a Zscaler company.
Zscaler's capabilities extend across all ten MDA foundations, from supporting Centrally Managed Enterprise Identities and Reliable Asset Inventory to enabling Resilient Networks, promoting Secure-by-Design practices, and facilitating Comprehensive Validation and Continuous and Actionable Monitoring. Its inline, cloud-native architecture generates a wealth of high-fidelity logs, seamlessly integrating with SIEM/SOAR platforms to provide unparalleled visibility and rapid response capabilities.
Beyond Security: The Zscaler Advantage
Adopting Zscaler for your Modern Defensible Architecture offers a cascade of benefits:
- Reduction of risk via the implementation of controls which align to the MDA principles
- Accelerated Zero Trust Adoption: Rapidly deploy "never trust, always verify" principles without complex network overhauls
- Enhanced Threat Prevention and Data Protection: Inline inspection, advanced threat detection, and robust Data Loss Prevention (DLP) stop sophisticated attacks in their tracks
- Improved User Experience: Direct-to-app connections mean faster, more seamless access for users, regardless of their location
- Operational Simplicity and Scalability: As a cloud-native platform, Zscaler removes the burden of managing security hardware, simplifying operations and scaling globally on demand
- Unrivaled Visibility and Auditability: Granular insights into every user activity and security event empower compliance, incident response, and continuous security validation
Beyond an IT project, the journey to a truly Modern Defensible Architecture is a strategic imperative for every organisation. Zscaler doesn't just check the boxes for MDA requirements; it embodies them. By shifting security to a cloud-native, Zero Trust model, Zscaler empowers you to build a future-proof, resilient security posture that can withstand and mitigate the cyber challenges of today and tomorrow.
Ready to transform your security from reactive defense to proactive resilience? Contact us to explore how Zscaler can be the foundational enabler for your Modern Defensible Architecture. Stay tuned for Zscaler’s whitepaper covering in depth how Zscaler maps to the MDA foundations.
War dieser Beitrag nützlich?
Haftungsausschluss: Dieser Blog-Beitrag wurde von Zscaler ausschließlich zu Informationszwecken erstellt und wird ohne jegliche Garantie für Richtigkeit, Vollständigkeit oder Zuverlässigkeit zur Verfügung gestellt. Zscaler übernimmt keine Verantwortung für etwaige Fehler oder Auslassungen oder für Handlungen, die auf der Grundlage der bereitgestellten Informationen vorgenommen werden. Alle in diesem Blog-Beitrag verlinkten Websites oder Ressourcen Dritter werden nur zu Ihrer Information zur Verfügung gestellt, und Zscaler ist nicht für deren Inhalte oder Datenschutzmaßnahmen verantwortlich. Alle Inhalte können ohne vorherige Ankündigung geändert werden. Mit dem Zugriff auf diesen Blog-Beitrag erklären Sie sich mit diesen Bedingungen einverstanden und nehmen zur Kenntnis, dass es in Ihrer Verantwortung liegt, die Informationen zu überprüfen und in einer Ihren Bedürfnissen angemessenen Weise zu nutzen.
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Mit dem Absenden des Formulars stimmen Sie unserer Datenschutzrichtlinie zu.




