Some numbers
70% of malicious links were found on hijacked websites in 2011 (Sophos, page 39). In 2012, Google is finding 9,500 newly malicious websites every day, mostly hijacked sites (Google, 2012). The Blackhole exploit kit alone is estimated to be present on several million websites per year (AVG, weekly count).
Nikkju, a web based worm that used SQL injection to spread, has infected about 200,000 websites. Lizamoon, which started propagating in 2010, infected about 1.5 million websites via SQL injection.
High profile victims
Since the hijacking of websites is mostly automated, websites of all types are getting compromised. Here are some of the high-profile websites that have been hijacked:
- 2012: French budget minister, Cleartrip (India), Computer World Mexico, and most of the top-1,000 websites blocked by Google, like blog.com (#649), fatakat.com (#699), ziddu.com (#802)
- 2011: MySQL, Geek.com, USPS, Lenovo India, etc.
Vulnerable software
The attack surface of website is quite large, an attacker can target the CMS, its plugins, administration tools (PHPMyAdmin, Plesk, cPanel - tools which should not be publicly accessible), the web server, the FTP server, the DNS server, etc.
I looked at the number of CVEs issued in 2012 for the most popular software platforms in these areas:
- WordPress: 14 CVEs for the core, 42 for extensions, including security extensions that are supposed to make WordPress safer.
- Joomla: 7 in core
- Drupal: 20+ in core
- PHPMyAdmin: 5 - Gemenenet, a security company, was compromised through a vulnerability in PHPMyAdmin
- cPanel: 50,000 compromised through one attack
- Plesk: 1 CVE, but 50,000 websites compromised through it
- Apache: 30+ CVE (core and modules)
- BIND: 6 CVEs
- etc.
In your mail box
If you want some examples of hijacked websites redirecting users to malicious pages, you can take a look at your inbox. Just this morning, I received four similar messages about a fictitious payment sent to me through Intuit:
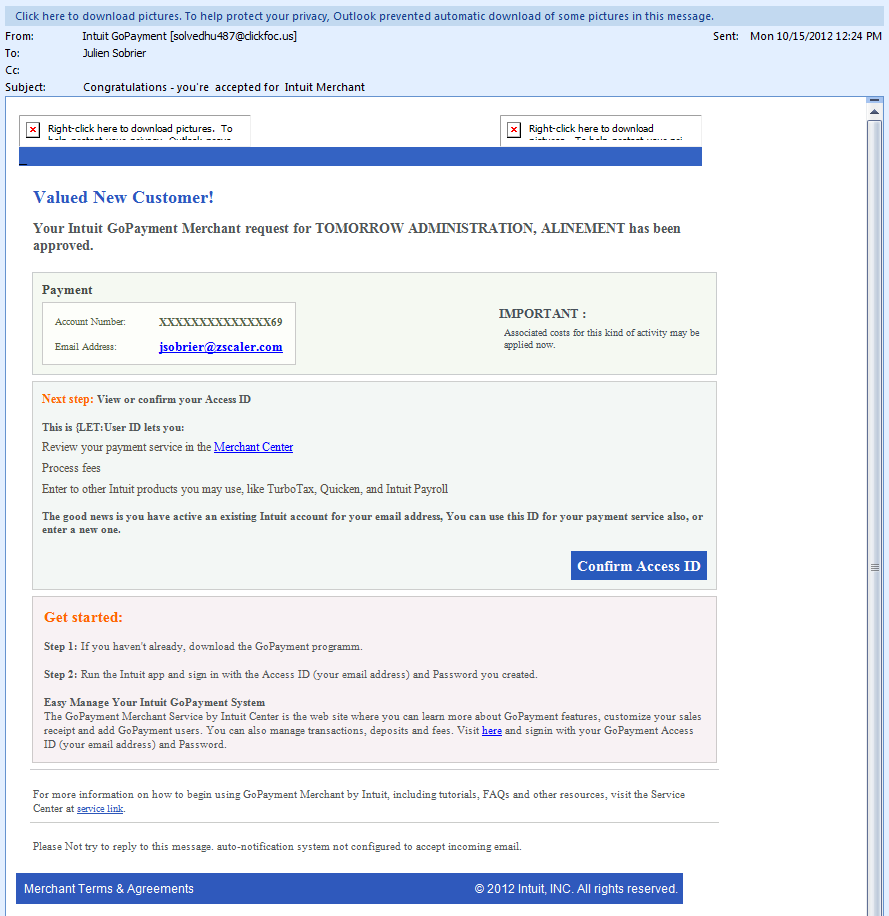 |
| Malicious e-mail |
- www.eyslerimaging.com/blog/wp-content/plugins/flickr-widget/iprprocsd.html (photography blog)
- www.odiseya.net/wp-content/themes/twentyten/bewpinfr.html
- user3.inet.vn/wp-content/plugins/iprprocsd.html
This is just one of the many spam campaigns that lead visitors to a malicious site.




