One of the question I often get asked is "What is the most prevalent threat on the Internet for the enterprises?". In terms of the total number of transactions, botnets are the biggest security risk. Once a host gets infected, the botnet usually spreads quickly within an enterprise. It also generates a significant amount of traffic to the command and control server, to download additional malware or perform other actions. For the last 30 days, botnets account for almost 80% of the security blocks at Zscaler.
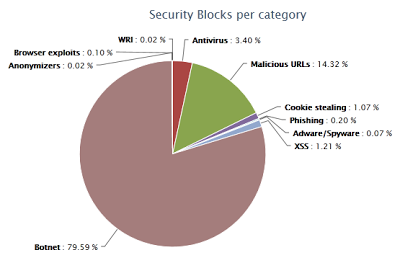 |
| Security blocks for the last 30 days |
When it comes to individual variants of malware, botnets, or other threats, there is no single piece of malware that dominates. Some threats appear one day, and disappear just as quickly. Others are seen daily for months, with random peaks. For example, Blackhole exploits and Zeus have been active for months.
 |
| One of the Blackhole exploits |
 | |
| Zeus traffic |
Mass infections of legitimate sites can still be seen months after the infection initially occurred and the vulnerable application has been patched. For example, our customers are still hitting websites infected with Lizamoon which was first reported in May 2011 and reached it's peak in September.
 |
| Legitimate sites infected by mass LizaMoon SQL Injection attacks |
The security landscape is very wide. Although botnets, as a category, represent the majority of overall malicious web traffic, there are a huge number of different threats seen daily by enterprise users. This means that security solutions must be able to detect and block a wide variety of traffic by looking at all components: URLs, HTTP header and content on both the client and server side.




