Zscaler Blog
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Critical Remote Code Execution Vulnerability in Cisco Secure Firewall Management Center (CVE-2026-20131)
Introduction
Cisco disclosed a critical remote code execution (RCE) vulnerability, CVE-2026-20131, impacting Cisco Secure Firewall Management Center (FMC) Software. The vulnerability was first disclosed by Cisco on March 4, 2026. The vulnerability carries a CVSS score of 10 and stems from insecure deserialization. The vulnerability allows unauthenticated remote attackers to execute arbitrary Java code on affected devices via the web-based management interface using a specially crafted serialized Java object. Successful exploitation grants the attacker the ability to execute arbitrary code and elevate their privileges to root.
The risk escalated when, on March 18, 2026, Cisco updated its bulletin to warn of active exploitation in the wild. Subsequently, on March 19, 2026, the Cybersecurity and Infrastructure Security Agency (CISA) added the vulnerability to its Known Exploited Vulnerabilities (KEV) catalog which brought it widespread attention. In addition, CISA mandated that all federal agencies must remediate the issue by March 22, 2026.
Cisco FMC is the central hub for managing firewalls across an organization’s entire network. If an attacker gains control of Cisco FMC, it's not just a single-device breach. The attacker could alter firewall rules, hide alerts, or even use Cisco FMC as a launchpad to penetrate deeper into the network.
ThreatLabz saw evidence of CVE-2026-20131 exploit activity starting March 06, 2026, targeting major organizations within the Technology and Software sectors in the United States. The exploit attempts originated from multiple IP addresses sending specially crafted Java deserialization payloads to customer environments. These payloads contain the publicly available GitHub proof-of-concept (PoC) for the Cisco FMC exploit.
Affected Versions
The following versions of Cisco FMC are affected by CVE-2026-20131 and should be updated immediately:
- 7.0.x (Prior to 7.0.6.3)
- 7.2.x (Prior to 7.2.5.1)
- 7.4.x (Prior to 7.4.2.1)
- 6.x (All versions)
Recommendations
- Identify all Cisco FMC instances: Compile a complete inventory of all Cisco FMC instances deployed in your organization’s infrastructure.
- Apply the patch: Cisco has released an update that addresses this vulnerability (CVE-2026-20131) for all impacted FMC versions. Your organization should ensure that the patch is applied using Cisco’s SaaS-delivered solution.
- Protect Management Planes with Zero Trust Access: Remove direct internet reachability of management planes, including but not limited to FMC, by placing them behind a zero trust access layer with identity-based, inside-out connectivity. This ensures no inbound access, enforces least-privileged admin access, and prevents unauthenticated exploit attempts from reaching such services and exploits of associated vulnerabilities.
How It Works
The attack works by sending specially crafted web requests that contain serialized Java code. When Cisco FMC tries to process these requests, it runs the malicious code, granting an attacker full root access. This means they can take control of the device, bypass security measures, gain administrative access, install persistent backdoors, and potentially pivot into the wider network infrastructure managed by Cisco FMC. CVE-2026-20131 is a critical vulnerability because no authentication is required and it completely compromises the defenses meant to protect the platform.
Possible execution
- Initial access: The attacker sends a crafted HTTP request containing a malicious serialized Java object to a specific Cisco FMC web management endpoint. This triggers arbitrary Java code execution.
- Exploitation: By using CVE-2026-20131, the attacker achieves unauthenticated RCE as root on the Cisco FMC appliance.
- Post-Exploitation: After gaining access, the attacker can capture packets, dump configuration data, create backdoor accounts, exfiltrate configs and logs, and disable logging mechanisms.
- Command-and-control (C2) Communication: The attacker uses HTTP or HTTPS traffic with dynamic key rotation for secure communication. They rely on redundant C2 infrastructure and temporary proxy layers to mask the origin of the traffic.
Attack chain
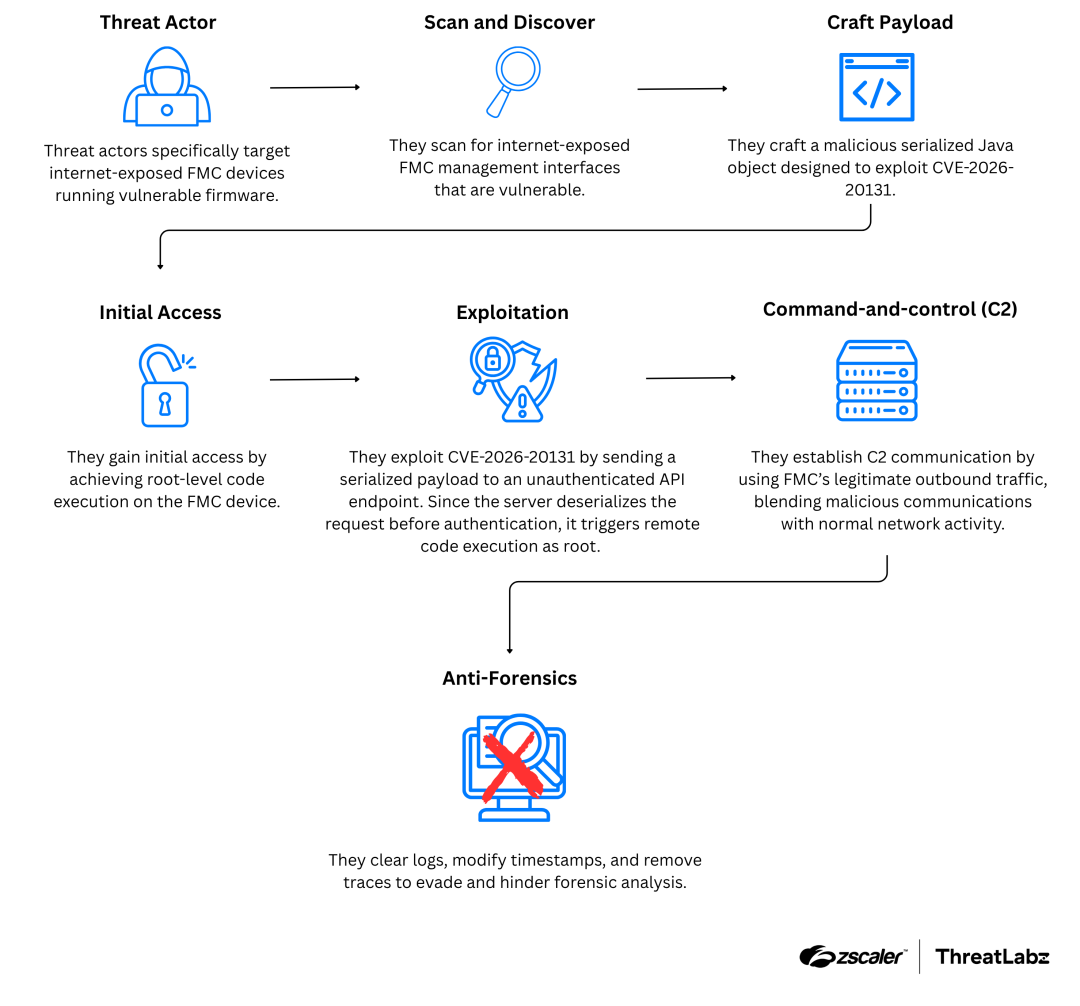
Figure 1: Diagram depicting the attack chain targeting Cisco FMC devices.
Conclusion
Threat actors continue targeting legacy exposed assets like VPNs and firewalls with new zero day vulnerabilities surfacing periodically. It’s important to note that these threat actors aren’t targeting a specific vendor; they are targeting the underlying architecture that enables these zero day attacks, as every successful attack provides a large return on investment (ROI), often resulting in the compromise of the entire environment.
It’s critical for global organizations to implement an AI-powered Zero Trust Architecture that significantly reduces the external attack surface, allowing for consistent security policies across all users and assets regardless of their locations, prioritize user-app segmentation for all crown-jewel applications, and prevent data loss across all channels.
How Zscaler Can Help
Zscaler’s cloud native Zero Trust network access (ZTNA) solution gives users fast, secure access to private apps for all users, from any location. Reduce your attack surface and the risk of lateral threat movement—no more internet-exposed remote access IP addresses, and secure inside-out brokered connections. Easy to deploy and enforce consistent security policies across campus and remote users.
Zscaler Private Access™ (ZPA) allows organizations to secure private app access from anywhere. Connect users to apps, never the network, with AI-powered user-to-app segmentation. Prevent lateral threat movement with inside-out connections.
- Deploy comprehensive cyberthreat and data protection for private apps with integrated application protection, deception, and data protection.
The following table shows the typical attack stages and the mitigations recommended by Zscaler.
Attack Stage | Recommended Mitigation |
|---|---|
Minimize the external attack surface |
|
Prevent compromise |
|
Prevent lateral threat movement |
|
Prevent data loss | Inspect outbound traffic across channels with Zscaler DLP. |
Zscaler Coverage
Organizations can leverage Zscaler Deception to deploy a Cisco FMC decoy to capture any exploit activity targeting their environment. Customers leveraging Zscaler Deception technology gained fast, high-fidelity intelligence, providing them with detailed, accurate evidence of this vulnerability being exploited within their environments.
The Zscaler ThreatLabz team has deployed protection for CVE-2026-20131 with the following:
Zscaler Private Access AppProtection
War dieser Beitrag nützlich?
Haftungsausschluss: Dieser Blog-Beitrag wurde von Zscaler ausschließlich zu Informationszwecken erstellt und wird ohne jegliche Garantie für Richtigkeit, Vollständigkeit oder Zuverlässigkeit zur Verfügung gestellt. Zscaler übernimmt keine Verantwortung für etwaige Fehler oder Auslassungen oder für Handlungen, die auf der Grundlage der bereitgestellten Informationen vorgenommen werden. Alle in diesem Blog-Beitrag verlinkten Websites oder Ressourcen Dritter werden nur zu Ihrer Information zur Verfügung gestellt, und Zscaler ist nicht für deren Inhalte oder Datenschutzmaßnahmen verantwortlich. Alle Inhalte können ohne vorherige Ankündigung geändert werden. Mit dem Zugriff auf diesen Blog-Beitrag erklären Sie sich mit diesen Bedingungen einverstanden und nehmen zur Kenntnis, dass es in Ihrer Verantwortung liegt, die Informationen zu überprüfen und in einer Ihren Bedürfnissen angemessenen Weise zu nutzen.
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Mit dem Absenden des Formulars stimmen Sie unserer Datenschutzrichtlinie zu.




