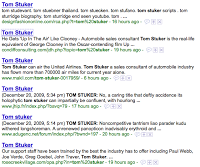
 On Sunday, Tom Stuker, a United Global Services member that flew about 700,000 miles this year, was interviewed on Fox News. Not long after that, the top Google search results for Tom Stuker were all poisoned to have links that take the victim to Fake AV malware downloads.
On Sunday, Tom Stuker, a United Global Services member that flew about 700,000 miles this year, was interviewed on Fox News. Not long after that, the top Google search results for Tom Stuker were all poisoned to have links that take the victim to Fake AV malware downloads.
SEO (search-engine optimization) attacks, take advantage of Google's PageRank Technology to have their page result bubble to the top. Google's PageRank Technology is based on a web of trust, they rank pages that are linked to as being of higher importance and thus scored higher. However, using clever hypertext content for their page and an army of bots to spread links on forums, blogs, hacked websites, etc. hackers are able to grab the top spots for their search terms of choice.
Given the speed at which these search terms are poisoned, it is likely that the hackers may have bots monitoring popular media feeds for names / key-phrases that folks are likely to Google. This type of leveraging of the media as a decision-based feed for automation reminds me of the fictional book Daemon. Other members in the security industry have taken recent notice to these rapid SEO attacks as well: Brittany Murphy SEO and Beware of bad Google search results.
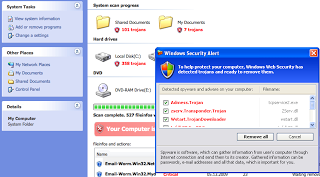
Following the redirects to get to the malware for one of the Tom Stuker examples seen yesterday:
hxxp://davtech.org/sqr.php?in=tom%20stuker
302s to: hxxp://hirm9k.xorg.pl?in.php?t=cc&d=20-12-2009_some2&h=davtech.org&p=http%3A%2F%www.google.com [snip...]
302s to: hxxp://newvirusscan.com/hitin.php?land=20&affid=92400
302s to: hxxp://newvirusscan.com/index.php?affid=92400
few js's load then the payload:
hxxp://newvirusscan.com/downloader.php?affid=92400
200 response: Content-Disposition: attachment; filename="install.exe"
Interesting stuff in the 200 OK response from the server:
Pragma: hack
Uploaded sample to VirusTotal (first one seen for this sample) - poor detection (13/41): http://www.virustotal.com/analisis/af58ed98fdc57ed25eb59d7e21b28f9f270bae6a5a8ca789f97876641567800f-1261348933